📰 Medium · Cybersecurity
4,827 articles · Updated every 3 hours · View all reads
All
Articles 67,615Blog Posts 99,886Tech Tutorials 16,344Research Papers 13,813News 12,550
⚡ AI Lessons

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
43m ago
When the Dependency Graph Becomes a Living Thing
Supply Chain Worms in the Agent Era Continue reading on Stackademic »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
47m ago
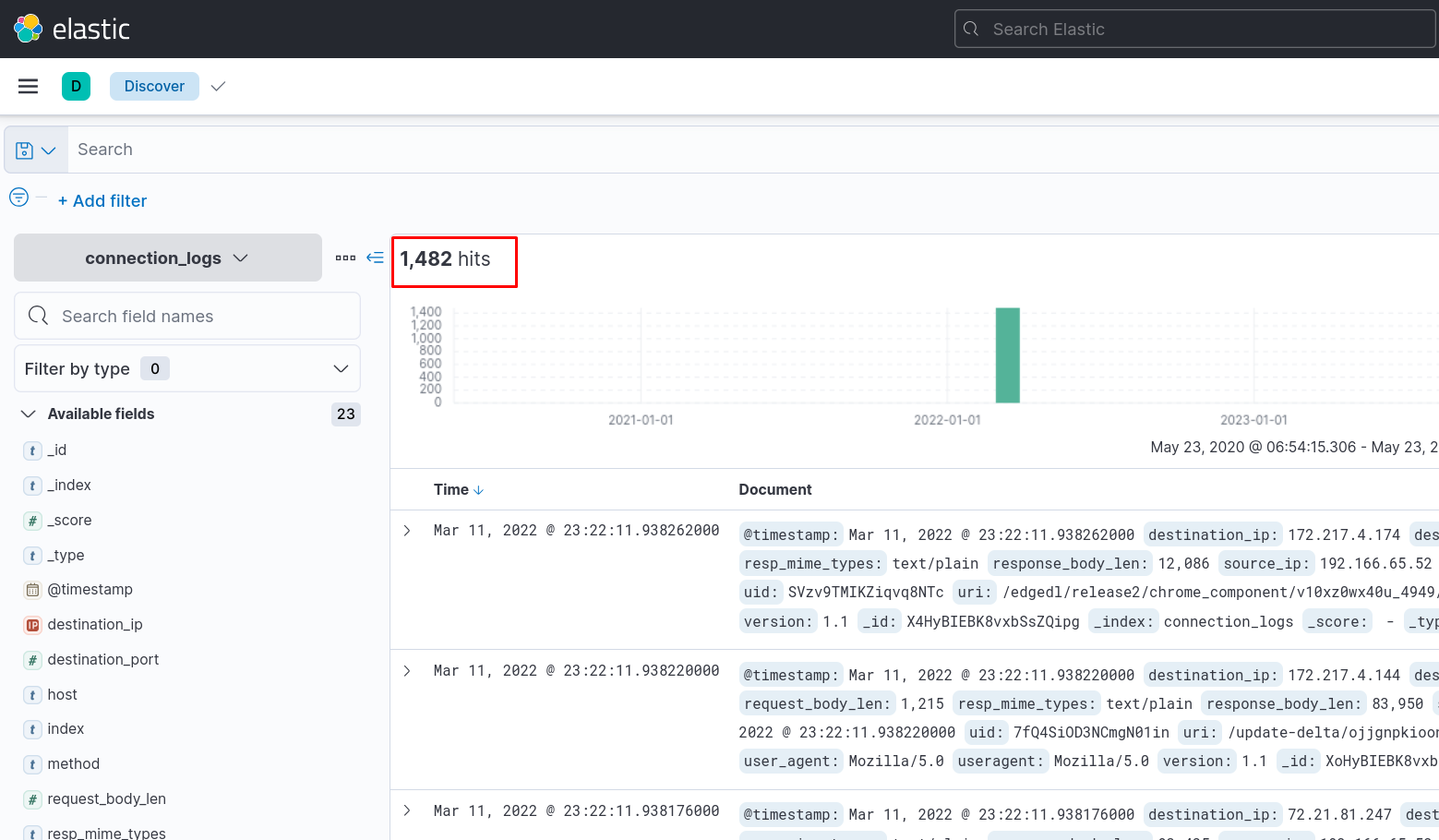
TryHackMe — ItsyBitsy Web App Log Analysis from Elastic
Scenario: In this challenge room, we will take a simple challenge to investigate an alert by IDS regarding a potential C2 communication. Continue reading on Med

Medium · Cybersecurity
1h ago
️ File Integrity Monitoring (FIM): The Security Camera for Your Files
Imagine you own a jewellery store. Continue reading on Medium »

Medium · Cybersecurity
1h ago
File Upload Attacks: Bypassing Blacklist Filters
When the server blocks .php but forgets about .phar, .phtml, Continue reading on MeetCyber »
Medium · Cybersecurity
1h ago
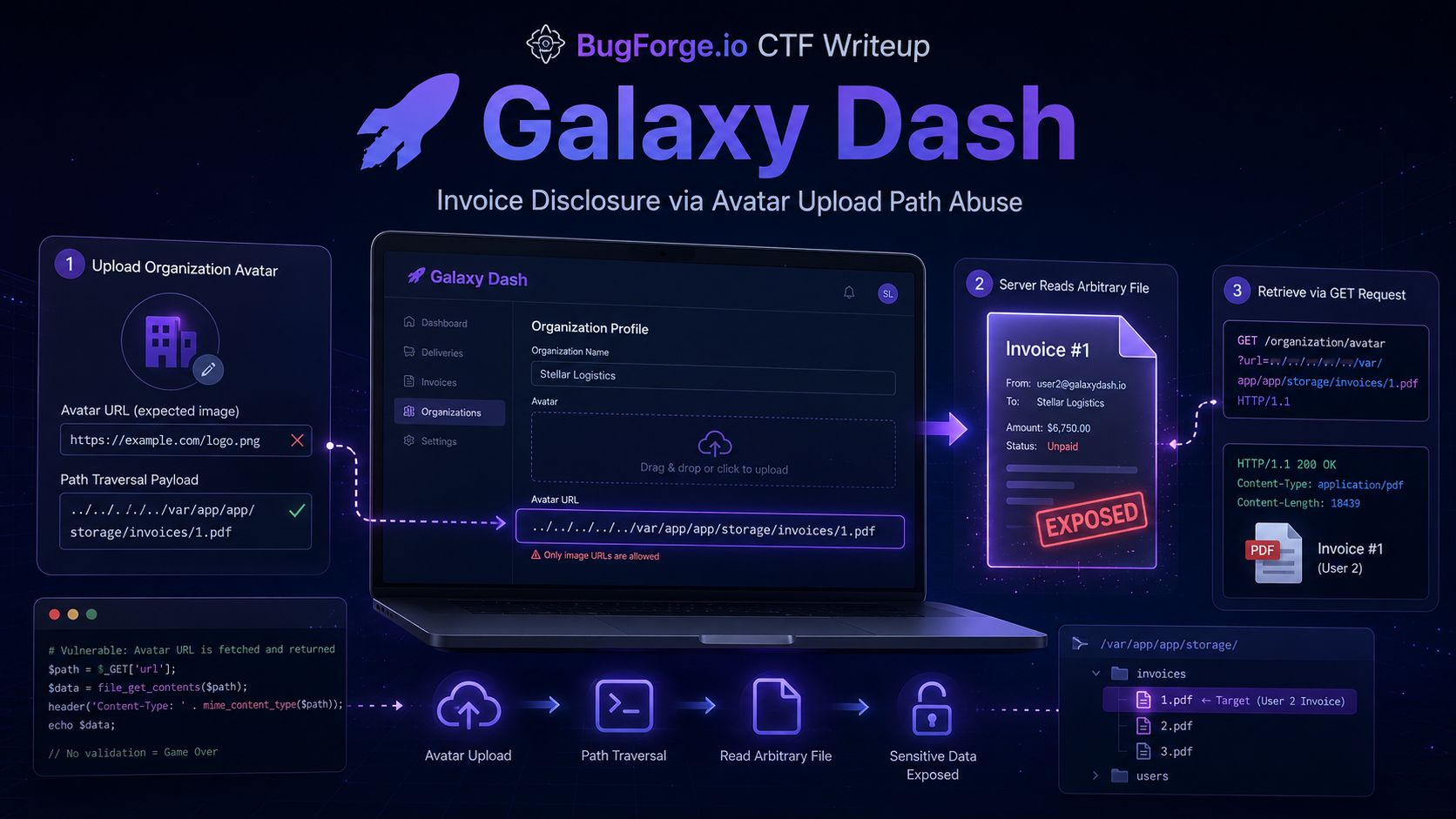
Write-Up: BugForge Daily Challenge — Galaxy Dash with Arbitrary File Read via Avatar File Path…
โอเครอบนี้ทีมจะไม่ขึ้เกียจแล้ว เรามาดู Writeup ของโจทย์ Weekly Challenge ใน Bugforge.io ซึ่งรอบนี้ทีมก็ยังไม่ First Blood อีกเช่นเคย… Continue reading on Medium
Medium · Cybersecurity
1h ago
One Shot
Examining what AI is actually doing to work, organizations, and the people inside them — beneath the headlines, beyond the forecasts. Continue reading on Medium

Medium · Cybersecurity
1h ago
Automating Network Threat Isolation: A Multi-Agent AI Approach
Turning passive intra-VLAN network telemetry into an active, self-defending architecture using Local LLMs, Zeek, and Agentic AI. Continue reading on Medium »

Medium · Cybersecurity
1h ago
Learn to Hack AWS by Hacking AWS.
Notes from a pentester taking Tyler Ramsbey’s AWS course. Continue reading on Medium »

Medium · Cybersecurity
1h ago
AI vs. Cybersecurity: Who’s Actually Winning?
Continue reading on Medium »
Medium · Cybersecurity
2h ago
What Does an Investment Fraud Law Firm Do?
What Does an Investment Fraud Law Firm Do? Continue reading on Medium »

Medium · Cybersecurity
2h ago
How to Build a Secure MCP Server: The Middle-Tier Gatekeeper Pattern
Secure your enterprise data warehouse from prompt injections when connecting LLMs via the Model Context Protocol. Continue reading on Medium »

Medium · Cybersecurity
2h ago
You Have 10 Seconds: Can You Spot This Cyber Attack?
You just received this message: Continue reading on Medium »

Medium · Cybersecurity
2h ago
A Critical OAuth Vulnerability in a Data Visualization Platform: One-Click Account Takeover
A technical analysis of a security vulnerability discovered through bug bounty — and thoughts on how AI should be used in this process. Continue reading on Cybe

Medium · Cybersecurity
2h ago
The Breadcrumbs, Mason! What do they mean?!
Reconstructing a Fileless Malware Attack Chain in Microsoft Defender XDR Continue reading on Medium »

Medium · Cybersecurity
2h ago
I Built an App to Stop the Subscription Bleed — One Night, Local AI Only
A conversation with my mentor, a problem worth solving, and a vibe coding session that proved local AI is no compromise. Continue reading on Medium »

Medium · Cybersecurity
3h ago
Why Did I Completely Disconnect My Development Environment From the Internet?
Choosing the security zone over the comfort zone when engineering critical defense systems. Continue reading on Medium »
Medium · Cybersecurity
3h ago
Networking
TCP/IP Model Continue reading on Medium »
Medium · Cybersecurity
3h ago
Can Quantum Computers Hack Banks? Understanding Encryption, Quantum Attacks & Future Security
Quantum Finance series: Explore RSA, ECC, quantum cryptography, photons, Quantum Key Distribution (QKD), and post-quantum security Continue reading on Medium »

Medium · Cybersecurity
3h ago
Nightmare-Eclipse Vs Microsoft, Hacker finds 6 Vulnerabilities in OS 11, and Now Almost Seven?
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
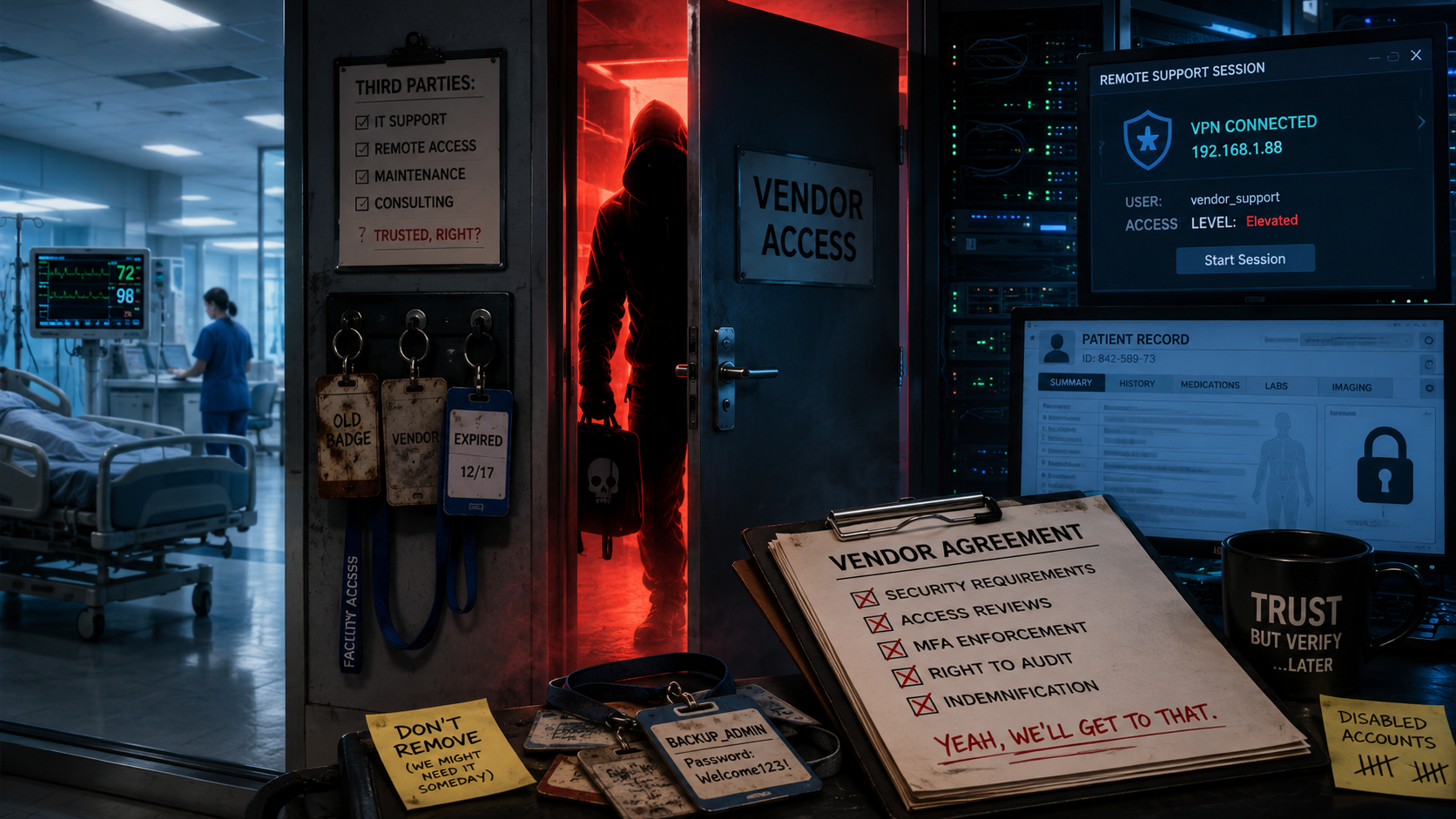
The Vendor Door: How Third Parties Become the Weakest Link in Healthcare Security
Healthcare cybersecurity has a dirty little secret: the breach does not always walk through the hospital’s front door. Continue reading on Medium »
Medium · Cybersecurity
4h ago
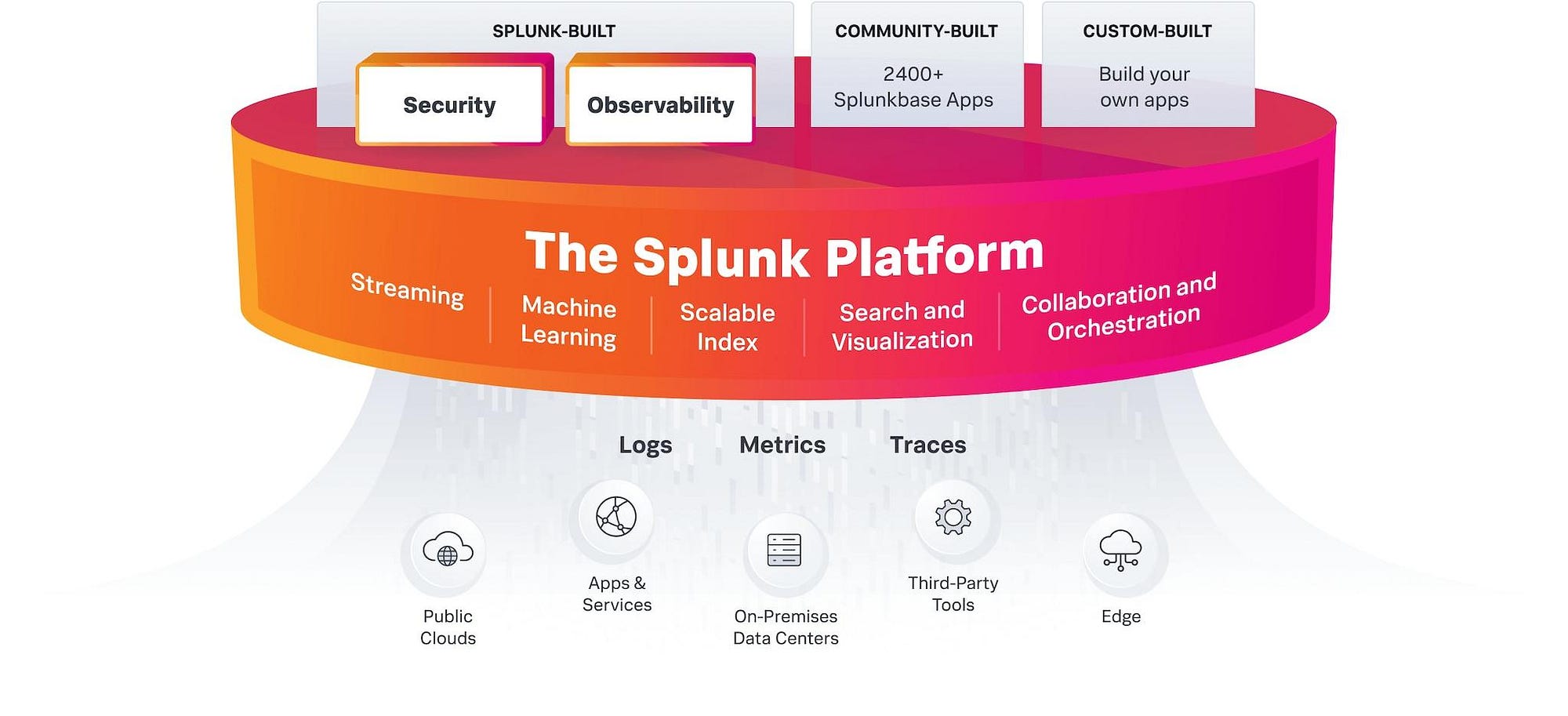
Splunk Architecture Explained: How Data Travels from Source to Insight
In today’s cybersecurity and IT operations landscape, organizations generate massive amounts of logs every second. Continue reading on Medium »

Medium · Cybersecurity
4h ago
FIFA World Cup 2026 Scams: A Simple Guide to Stay Safe
# FIFA World Cup 2026 Scams: A Simple Guide to Stay Safe Continue reading on Medium »

Medium · Cybersecurity
5h ago
How to Spot a Fake E-Commerce Website from TikTok in 30 Seconds
We’ve all seen them while scrolling through our TikTok feeds: beautifully edited video ads showcasing high-end sneakers, trending clothing… Continue reading on
Medium · Cybersecurity
5h ago
What Happens in the First 60 Seconds After a Hacker Targets You?
A Minute-by-Minute Journey Through a Modern Cyberattack Continue reading on Medium »
 DeepCamp AI
DeepCamp AI