Mind Blowing 🤯 Reverse Shell Demo with DNS data bouncing exfiltration!
Skills:
Network Security80%
Big thanks to Brilliant for sponsoring this video! Get started with a free 30 day trial and 20% discount: https://Brilliant.org/DavidBombal
The First 200 people that sign up will get a special discount.
Disclaimer: This video is for educational purposes only.
// Jakoby’s SOCIAL//
YouTube: https://www.youtube.com/c/IamJakoby
LinkedIn: https://www.linkedin.com/in/i-am-jakoby
X: https://x.com/i_am_jakoby
Instagram: https://www.instagram.com/i_am_jakoby/
GitHub: https://github.com/I-Am-Jakoby
TikTok: https://www.tiktok.com/@i_am_jakoby
// YouTube Video REFERENCE //
Next Gen Hacker?: https://youtu.be/6jqJ7Ga5CoE
The best Hacking Courses & Certs? Your 2024 roadmap to Pentester success: https://youtu.be/10P4aoXdXTI
// David's SOCIAL //
Discord: https://discord.com/invite/usKSyzb
X: https://www.twitter.com/davidbombal
Instagram: https://www.instagram.com/davidbombal
LinkedIn: https://www.linkedin.com/in/davidbombal
Facebook: https://www.facebook.com/davidbombal.co
TikTok: http://tiktok.com/@davidbombal
YouTube: https://www.youtube.com/@davidbombal
// MY STUFF //
https://www.amazon.com/shop/davidbombal
// SPONSORS //
Interested in sponsoring my videos? Reach out to my team here: sponsors@davidbombal.com
// MENU //
00:00 - Coming Up
00:57 - Sponsored Section
03:01 - Intro
03:19 - Power Shell Gallery
05:05 - Modules
06:28 - Microsoft Patch
08:04 - Consulting with the Cybersecurity Community
08:58 - Microsoft Honeypot
10:09 - Models by Jakoby
11:33 - Running Models
12:01 - How Models Function
13:43 - The Vulnerability of The Site
15:30 - Ransomware
18:20 - Owning Models
19:13 - Bug Bounty Program
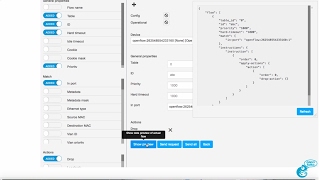
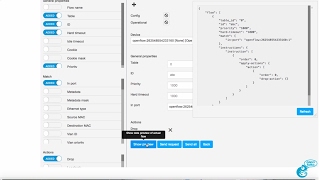
22:23 - Reverse Shell Generator
29:25 - Methods For Execution
31:49 - How To Solve
33:47 - Engage with the Ethical Hackers
34:20 - Exfiltration Data Bouncing
39:12 - Demo
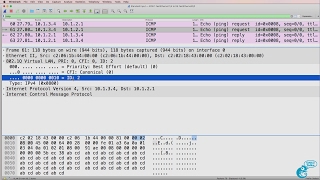
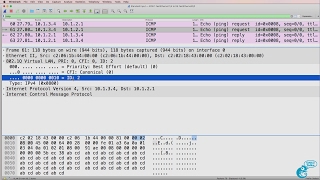
39:56 - Capture DNS Traffic
41:01 - Running Vanish
50:05 - Running A lot of Testing, No Man’s Land
52:29 - Get ahold of IamJakoby
54:08 - Hak5 Payload
55:57 - Imposter Syn
Watch on YouTube ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
Playlist
Uploads from David Bombal · David Bombal · 0 of 60
← Previous
Next →
1
 2
2
 3
3
 4
4
 5
5
 6
6
 7
7
 8
8
 9
9
 10
10
 11
11
 12
12
 13
13
 14
14
 15
15
 16
16
 17
17
 18
18
 19
19
 20
20
 21
21
 22
22
 23
23
 24
24
 25
25
 26
26
 27
27
 28
28
 29
29
 30
30
 31
31
 32
32
 33
33
 34
34
 35
35
 36
36
 37
37
 38
38
 39
39
 40
40
 41
41
 42
42
 43
43
 44
44
 45
45
 46
46
 47
47
 48
48
 49
49
 50
50
 51
51
 52
52
 53
53
 54
54
 55
55
 56
56
 57
57
 58
58
 59
59
 60
60


RYU SDN Controller Part 4: Graphical User Interface (GUI): Practical GNS3 SDN and OpenFlow
David Bombal

HPE Network Protector SDN Application Part 1 - Introduction
David Bombal

HPE Network Protector SDN Application Part 2 : DNS Interception using OpenFlow
David Bombal

HPE Network Protector SDN Application Part 3 - Lab Setup using Physical Switches
David Bombal

HPE Network Protector SDN Application Part 4 - Demo of malicious websites blocked
David Bombal

HPE Network Protector SDN Application Part 5 - Demo OpenFlow table interception flows
David Bombal

HPE Network Protector SDN Application Part 6 - Demo of Physical Switch configuration
David Bombal

HPE Network Protector SDN Application Part 7 - Demo Service Insertion Tunnel / GRE Tunnel
David Bombal

HPE Network Protector SDN Application Part 8 - Demo SDN OpenFlow Reporting
David Bombal

HPE Network Protector SDN Application Part 9 - Demo switches interception of DNS traffic
David Bombal

GNS3 Talks: GNS3 version 1.5.X Appliance Tips
David Bombal

CCNA 200-125 Exam: AAA demo: TACACS+ with GNS3
David Bombal

GNS3 2.0.0 beta 2 install
David Bombal

CCNA #012: Learn SNMP with GNS3, Wireshark and Solarwinds NPM - CCNA 200-125 exam
David Bombal
CCNA #013: Spanning Tree CCNA Exam Questions: Know the answer? CCNA 200-125 exam
David Bombal

GNS3 2.0.0 beta : GNS3 VM integration with GNS3 GUI
David Bombal
CCNA #018: Routing exam questions: Who wins? OSPF, EIGRP or RIP? Sure? CCNA 200-125 exam
David Bombal

CCNA #019: Spanning Tree CCNA Exam Questions: Root Bridge, Root Port and more: CCNA 200-125 exam
David Bombal

GNS3 Download, installation and configuration - GNS3 1.5.3 and Windows 10
David Bombal

CCNA #023 EIGRP Neighbor Troubleshooting (DUAL Issues) for the CCNA 200-125 Exam
David Bombal

GNS3 2.0 Architecture and schema Part 1: What is the GNS3 Controller?
David Bombal

GNS3 2.0 Architecture and schema Part 2: Emulators and virtualization
David Bombal

CCNA #028 VTP Troubleshooting for the CCNA 200-125 Exam
David Bombal

CCNA #029 VTP & DTP Troubleshooting for the CCNA 200-125 Exam
David Bombal

CCNA #030 VTP Troubleshooting for the CCNA 200-125 Exam
David Bombal

GNS3 : How to download Cisco IOS images and VIRL images. Which is the best? How do you get them?
David Bombal

GNS3 ASA setup: Import and configure Cisco ASAv with GNS3
David Bombal

GNS3 switching setup and options: Cisco and other switching options in GNS3
David Bombal

GNS3 switching setup and options Part 2: GNS3 unmanaged built-in switch
David Bombal

GNS3 switching setup and options Part 3: Router on a sick with GNS3 unmanaged built-in switch
David Bombal

GNS3 switching setup and options Part 4: Etherswitch Router for Cisco Dynamips Part 1
David Bombal

GNS3 switching setup and options Part 5: Etherswitch Router for Cisco Dynamips Part 2
David Bombal
GNS3 switching setup and options Part 6: Etherswitch, Wireshark, 802.1Q, InterVLAN routing
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 1: GNS3 Switching Part 7
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 2: GNS3 Switching Part 8
David Bombal
GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 3: GNS3 Switching Part 9
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 4: GNS3 Switching Part 10
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 5: GNS3 Switching Part 11
David Bombal

GNS3 Nexus (NX-OSv) switch setup and configuration Part 1: GNS3 switching options Part 12
David Bombal

GNS3 Nexus (NX-OSv) switch setup and configuration Part 2: GNS3 switching options Part 13
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 6: GNS3 Switching Part 14
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 7: GNS3 Switching Part 15
David Bombal

GNS3 Cisco CSR 1000v setup and configuration Part 1: GNS3 NFV
David Bombal

GNS3 Cisco CSR 1000v setup and configuration Part 2: GNS3 NFV
David Bombal

GNS3 Talks: Use the NAT node to connect GNS3 to the Internet easily!
David Bombal

GNS3 Talks: GNS3 2.0 RC1 is now available
David Bombal

GNS3 Talks: GNS3 2.0 Portable Projects - easily export and import GNS3 projects
David Bombal

GNS3 Talks: Multiple clients sharing projects in real time, plus console session shadowing!
David Bombal

CCNA #035 NAT Troubleshooting Scenario 1 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

CCNA #036 NAT Troubleshooting Scenario 2 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

GNS3 Talks: ESXi, GNS3 VM and KVM support Part 1: leverage servers and the cloud
David Bombal

CCNA #037 OSPF Troubleshooting - can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

GNS3 Talks: ESXi, GNS3 VM and KVM support Part 2: leverage servers and the cloud
David Bombal

CCNA #038 NAT Troubleshooting Scenario 3 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

CCNA #039 - OSPF DR, BR and DROTHER Election - do you know the answers?
David Bombal

CCNA #040 NAT Troubleshooting Scenario 4 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

GNS3 Talks: Arista vEOS GNS3 import and configuration Part 1
David Bombal

CCNA #041 - OSPF DR, BR and DROTHER Election - do you know the answers?
David Bombal

GNS3 Talks: Arista vEOS GNS3 import and configuration Part 2
David Bombal

GNS3 Talks: ipterm: Linux, Docker, Python, SDN and more! Part 1
David Bombal
More on: Network Security
View skill →Related AI Lessons
Chapters (27)
Coming Up
0:57
Sponsored Section
3:01
Intro
3:19
Power Shell Gallery
5:05
Modules
6:28
Microsoft Patch
8:04
Consulting with the Cybersecurity Community
8:58
Microsoft Honeypot
10:09
Models by Jakoby
11:33
Running Models
12:01
How Models Function
13:43
The Vulnerability of The Site
15:30
Ransomware
18:20
Owning Models
19:13
Bug Bounty Program
22:23
Reverse Shell Generator
29:25
Methods For Execution
31:49
How To Solve
33:47
Engage with the Ethical Hackers
34:20
Exfiltration Data Bouncing
39:12
Demo
39:56
Capture DNS Traffic
41:01
Running Vanish
50:05
Running A lot of Testing, No Man’s Land
52:29
Get ahold of IamJakoby
54:08
Hak5 Payload
55:57
Imposter Syn
🎓
Tutor Explanation










 DeepCamp AI
DeepCamp AI