Hacker unlocks Cryptography secrets (hashing, encryption and more)
Do you know what hashing is? Symmetric encryption? Asymmetric encryption? Do you know how VPNs work? What about MD5, SHA, 3DES, DES, AES and other algorithms? Stephen Sims explains.
// Stephen's Sims’ SOCIAL //
X: https://x.com/Steph3nSims
YouTube: https://www.youtube.com/@OffByOneSecurity
Discord: https://discord.com/invite/offbyonesecurity
// Books written by Stephen //
Gray Hat Hacking Series by various authors:
US https://amzn.to/3B1FeIK
UK https://amzn.to/3A920AL
// YouTube video REFERENCE //
How to make millions $$$ hacking Zero Days?? https://youtu.be/LWmy3t84AIo
Buffer Overflow Hacking Tutorial (Bypass Passwords): https://youtu.be/c2BvS2VqDWg
Never access the dark web without doing this: https://youtu.be/7wLLcFMmbpg
// David's SOCIAL //
Discord: https://discord.com/invite/usKSyzb
X: https://www.x.com/davidbombal
Instagram: https://www.instagram.com/davidbombal
LinkedIn: https://www.linkedin.com/in/davidbombal
Facebook: https://www.facebook.com/davidbombal.co
TikTok: http://tiktok.com/@davidbombal
YouTube: https://www.youtube.com/@davidbombal
// MY STUFF //
https://www.amazon.com/shop/davidbombal
// SPONSORS //
Interested in sponsoring my videos? Reach out to my team here: sponsors@davidbombal.com
// MENU //
0:00 - Coming up
01:25 - Intro
01:49 - Stephen's Chancel
03:54 - Crypto
05:15 - Lesson Overview
09:11 - Basic Encryption Examples
11:26 - XOR Exclusive OR
15:45 - Encryption with XOR
20:41 - Decryption either XOR
22:29 - Arbitrary Substitution
24:15 - Rotation Cypher
26:06 - Basic Permutation
27:48 - Symmetric Key Cryptography
31:02 - Stream Cyphers
33:51 - What is a Key?
42:25 - The Best Way to Manage the Initialisation Vector?
50:30 - Block Cyphers
58:50 - Asymmetric Key Cryptography
01:03:37 - Generating a Key
01:12:37 - Hashing
01:20:16 - Basic Signing Without a CA
01:24:58 - Steganography
01:30:27 - Conclusion
Disclaimer: This video is for educational purposes only. No actual attack took place on any websites.
Please n
Watch on YouTube ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
Playlist
Uploads from David Bombal · David Bombal · 0 of 60
← Previous
Next →
1
 2
2
 3
3
 4
4
 5
5
 6
6
 7
7
 8
8
 9
9
 10
10
 11
11
 12
12
 13
13
 14
14
 15
15
 16
16
 17
17
 18
18
 19
19
 20
20
 21
21
 22
22
 23
23
 24
24
 25
25
 26
26
 27
27
 28
28
 29
29
 30
30
 31
31
 32
32
 33
33
 34
34
 35
35
 36
36
 37
37
 38
38
 39
39
 40
40
 41
41
 42
42
 43
43
 44
44
 45
45
 46
46
 47
47
 48
48
 49
49
 50
50
 51
51
 52
52
 53
53
 54
54
 55
55
 56
56
 57
57
 58
58
 59
59
 60
60


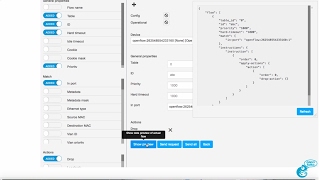
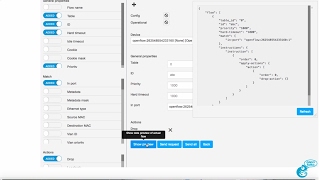
RYU SDN Controller Part 4: Graphical User Interface (GUI): Practical GNS3 SDN and OpenFlow
David Bombal

HPE Network Protector SDN Application Part 1 - Introduction
David Bombal

HPE Network Protector SDN Application Part 2 : DNS Interception using OpenFlow
David Bombal

HPE Network Protector SDN Application Part 3 - Lab Setup using Physical Switches
David Bombal

HPE Network Protector SDN Application Part 4 - Demo of malicious websites blocked
David Bombal

HPE Network Protector SDN Application Part 5 - Demo OpenFlow table interception flows
David Bombal

HPE Network Protector SDN Application Part 6 - Demo of Physical Switch configuration
David Bombal

HPE Network Protector SDN Application Part 7 - Demo Service Insertion Tunnel / GRE Tunnel
David Bombal

HPE Network Protector SDN Application Part 8 - Demo SDN OpenFlow Reporting
David Bombal

HPE Network Protector SDN Application Part 9 - Demo switches interception of DNS traffic
David Bombal

GNS3 Talks: GNS3 version 1.5.X Appliance Tips
David Bombal

CCNA 200-125 Exam: AAA demo: TACACS+ with GNS3
David Bombal

GNS3 2.0.0 beta 2 install
David Bombal

CCNA #012: Learn SNMP with GNS3, Wireshark and Solarwinds NPM - CCNA 200-125 exam
David Bombal
CCNA #013: Spanning Tree CCNA Exam Questions: Know the answer? CCNA 200-125 exam
David Bombal

GNS3 2.0.0 beta : GNS3 VM integration with GNS3 GUI
David Bombal
CCNA #018: Routing exam questions: Who wins? OSPF, EIGRP or RIP? Sure? CCNA 200-125 exam
David Bombal

CCNA #019: Spanning Tree CCNA Exam Questions: Root Bridge, Root Port and more: CCNA 200-125 exam
David Bombal

GNS3 Download, installation and configuration - GNS3 1.5.3 and Windows 10
David Bombal

CCNA #023 EIGRP Neighbor Troubleshooting (DUAL Issues) for the CCNA 200-125 Exam
David Bombal

GNS3 2.0 Architecture and schema Part 1: What is the GNS3 Controller?
David Bombal

GNS3 2.0 Architecture and schema Part 2: Emulators and virtualization
David Bombal

CCNA #028 VTP Troubleshooting for the CCNA 200-125 Exam
David Bombal

CCNA #029 VTP & DTP Troubleshooting for the CCNA 200-125 Exam
David Bombal

CCNA #030 VTP Troubleshooting for the CCNA 200-125 Exam
David Bombal

GNS3 : How to download Cisco IOS images and VIRL images. Which is the best? How do you get them?
David Bombal

GNS3 ASA setup: Import and configure Cisco ASAv with GNS3
David Bombal

GNS3 switching setup and options: Cisco and other switching options in GNS3
David Bombal

GNS3 switching setup and options Part 2: GNS3 unmanaged built-in switch
David Bombal

GNS3 switching setup and options Part 3: Router on a sick with GNS3 unmanaged built-in switch
David Bombal

GNS3 switching setup and options Part 4: Etherswitch Router for Cisco Dynamips Part 1
David Bombal

GNS3 switching setup and options Part 5: Etherswitch Router for Cisco Dynamips Part 2
David Bombal
GNS3 switching setup and options Part 6: Etherswitch, Wireshark, 802.1Q, InterVLAN routing
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 1: GNS3 Switching Part 7
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 2: GNS3 Switching Part 8
David Bombal
GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 3: GNS3 Switching Part 9
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 4: GNS3 Switching Part 10
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 5: GNS3 Switching Part 11
David Bombal

GNS3 Nexus (NX-OSv) switch setup and configuration Part 1: GNS3 switching options Part 12
David Bombal

GNS3 Nexus (NX-OSv) switch setup and configuration Part 2: GNS3 switching options Part 13
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 6: GNS3 Switching Part 14
David Bombal

GNS3 Talks: Docker, Open vSwitch, SDN and OpenFlow Part 7: GNS3 Switching Part 15
David Bombal

GNS3 Cisco CSR 1000v setup and configuration Part 1: GNS3 NFV
David Bombal

GNS3 Cisco CSR 1000v setup and configuration Part 2: GNS3 NFV
David Bombal

GNS3 Talks: Use the NAT node to connect GNS3 to the Internet easily!
David Bombal

GNS3 Talks: GNS3 2.0 RC1 is now available
David Bombal

GNS3 Talks: GNS3 2.0 Portable Projects - easily export and import GNS3 projects
David Bombal

GNS3 Talks: Multiple clients sharing projects in real time, plus console session shadowing!
David Bombal

CCNA #035 NAT Troubleshooting Scenario 1 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

CCNA #036 NAT Troubleshooting Scenario 2 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

GNS3 Talks: ESXi, GNS3 VM and KVM support Part 1: leverage servers and the cloud
David Bombal

CCNA #037 OSPF Troubleshooting - can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

GNS3 Talks: ESXi, GNS3 VM and KVM support Part 2: leverage servers and the cloud
David Bombal

CCNA #038 NAT Troubleshooting Scenario 3 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

CCNA #039 - OSPF DR, BR and DROTHER Election - do you know the answers?
David Bombal

CCNA #040 NAT Troubleshooting Scenario 4 - Can you find the issue? CCNA Exam 200-125 troubleshooting
David Bombal

GNS3 Talks: Arista vEOS GNS3 import and configuration Part 1
David Bombal

CCNA #041 - OSPF DR, BR and DROTHER Election - do you know the answers?
David Bombal

GNS3 Talks: Arista vEOS GNS3 import and configuration Part 2
David Bombal

GNS3 Talks: ipterm: Linux, Docker, Python, SDN and more! Part 1
David Bombal
More on: Security Basics
View skill →Related AI Lessons
⚡
⚡
⚡
⚡
I Managed WordPress Security Across 1500+ Clients. The Main Reason WP Sites Get Hacked.
Dev.to AI
What Is YubiKey Authentication & How It Works
Dev.to · Mrunank Pawar
I Used to Ignore “Boring” Vulnerabilities… Until One Paid More Than a Critical
Medium · Data Science
I Used to Ignore “Boring” Vulnerabilities… Until One Paid More Than a Critical
Medium · Programming
Chapters (23)
Coming up
1:25
Intro
1:49
Stephen's Chancel
3:54
Crypto
5:15
Lesson Overview
9:11
Basic Encryption Examples
11:26
XOR Exclusive OR
15:45
Encryption with XOR
20:41
Decryption either XOR
22:29
Arbitrary Substitution
24:15
Rotation Cypher
26:06
Basic Permutation
27:48
Symmetric Key Cryptography
31:02
Stream Cyphers
33:51
What is a Key?
42:25
The Best Way to Manage the Initialisation Vector?
50:30
Block Cyphers
58:50
Asymmetric Key Cryptography
1:03:37
Generating a Key
1:12:37
Hashing
1:20:16
Basic Signing Without a CA
1:24:58
Steganography
1:30:27
Conclusion
🎓
Tutor Explanation











 DeepCamp AI
DeepCamp AI