Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,417 reads from curated sources
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
How MCP Authentication Works: OAuth 2.0, OIDC, and Token Injection Explained
Authentication is the Hardest Part of MCP at Scale Getting a single MCP server talking to a single agent is straightforward. Getting 30 agents, each authorised

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The hidden cost of bad documentation — internal chaos.
Internal chaos in growing companies is rarely dramatic. Continue reading on aneo Security Insights »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
CVE-2026-5913 | Chromium: CVE-2026-5913 Out of bounds read in Blink
CVE-2026-5913 | Chromium: Out of bounds read in Blink Connect & Continue the Conversation If you are passionate about Microsoft 365 governance, Purview, Ent

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
picoCTF Writeup — Challenge “Old Sessions” (Step-by-Step Walkthrough)
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Top 10 MITRE ATT&CK Techniques Every SOC Analyst Should Know
A practical field guide for analysts who want to stop chasing alerts and start understanding attacks Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Art of Bypassing Firewalls & IDS/IPS — A Hacker’s Story
Prologue: The Digital BorderPicture this: you’re a cyber mercenary, standing before a heavily guarded digital fortress. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
HIPAA Pentesting for AI Scribes: What Hospital Security Teams Actually Require
AI scribes are being adopted quickly across healthtech, and in most cases, the underlying product does exactly what it promises — it… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Defense Tech Startups: How Innovation Is Reshaping Security in Lithuania
Throughout its existence, the Innovantage podcast has offered diverse perspectives and insights on technology and its role in business… Continue reading on Inno
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
CVE-2026-5919 | Chromium: Insufficient validation of untrusted input in WebSockets
CVE-2026-5919 | Chromium: Insufficient Validation of Untrusted Input in WebSockets Connect & Continue the Conversation If you are passionate about Microsoft

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
⚙️ 10. — URL-based Access Control Can Be Circumvented — X -Original-URL
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Computation Must Leave Evidence: Why Execution Alone Is Not Enough
Modern systems still rely too heavily on one dangerous assumption: that if a computation has been executed somewhere, its result can be… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Paradox: The More Secure the Product, the Less People Trust It
Over the past few days, early feedback on the Toqen mobile app has been coming in. Continue reading on Medium »

Dev.to · Neural Download
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
JWT Is Not Encrypted (And That's By Design)
Most developers carry JWTs on every request but never look inside. The payload is plain text, the signature is the real security, and the alg:none attack broke

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Ones on the Inside
There’s a new term floating around right now: Mythos. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Making UAC Bypass Great Again in 2026
Let’s be honest — User Account Control (UAC) bypasses never really went away. They just… faded into the background. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Why Every Freelancer Needs a VPN in 2026 (And Which One to Pick)
If you work from coffee shops, co-working spaces, or hotel WiFi, you’re broadcasting your data to anyone who knows how to listen. And in… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
You Didn’t Buy a Ticket — So Why Is Your Data Still Being Tracked?
Most people assume that data collection begins when they make a purchase. It feels logical — if you didn’t buy anything, you didn’t share… Continue reading on W

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
From Card Skimmer Chaos to Compliance Hero: A Founder’s PCI DSS Wake-Up Call
The Midnight Breach That Nearly Bankrupted My Startup Continue reading on Write A Catalyst »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
ENG | TryHackMe Basic Pentesting CTF Solution
Basic Pentesting My solution process for the Basic Pentesting CTF on TryHackMe. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Account Takeover (ATO) — How Attackers Gain Full Control of Accounts
✍️ Introduction Continue reading on Bug Bounty Hunting: A Comprehensive Guide in English and french »

Dev.to · GDS K S
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Your VS Code Extensions Are a Supply Chain Attack Surface
The GlassWorm campaign is targeting developer IDEs right now. Here's how to audit yours.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Securing Autonomous Payments: Risk, Compliance, and Governance for AI Spend
Autonomous payments without governance become autonomous fraud. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Agentic Triage on Snowflake
The biggest bottleneck hitting security teams today isn’t the SIEM, it’s triage. Analysts are drowning in alerts, spending the bulk of… Continue reading on Snow

Dev.to · 404Saint
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Securing the Air-Gap: Building a Hardware-Aware Forensic Suite for ICS/OT by Rugero Tesla (404saint)
The Problem In industrial environments, the "Air-Gap" is a myth as long as USB drives...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
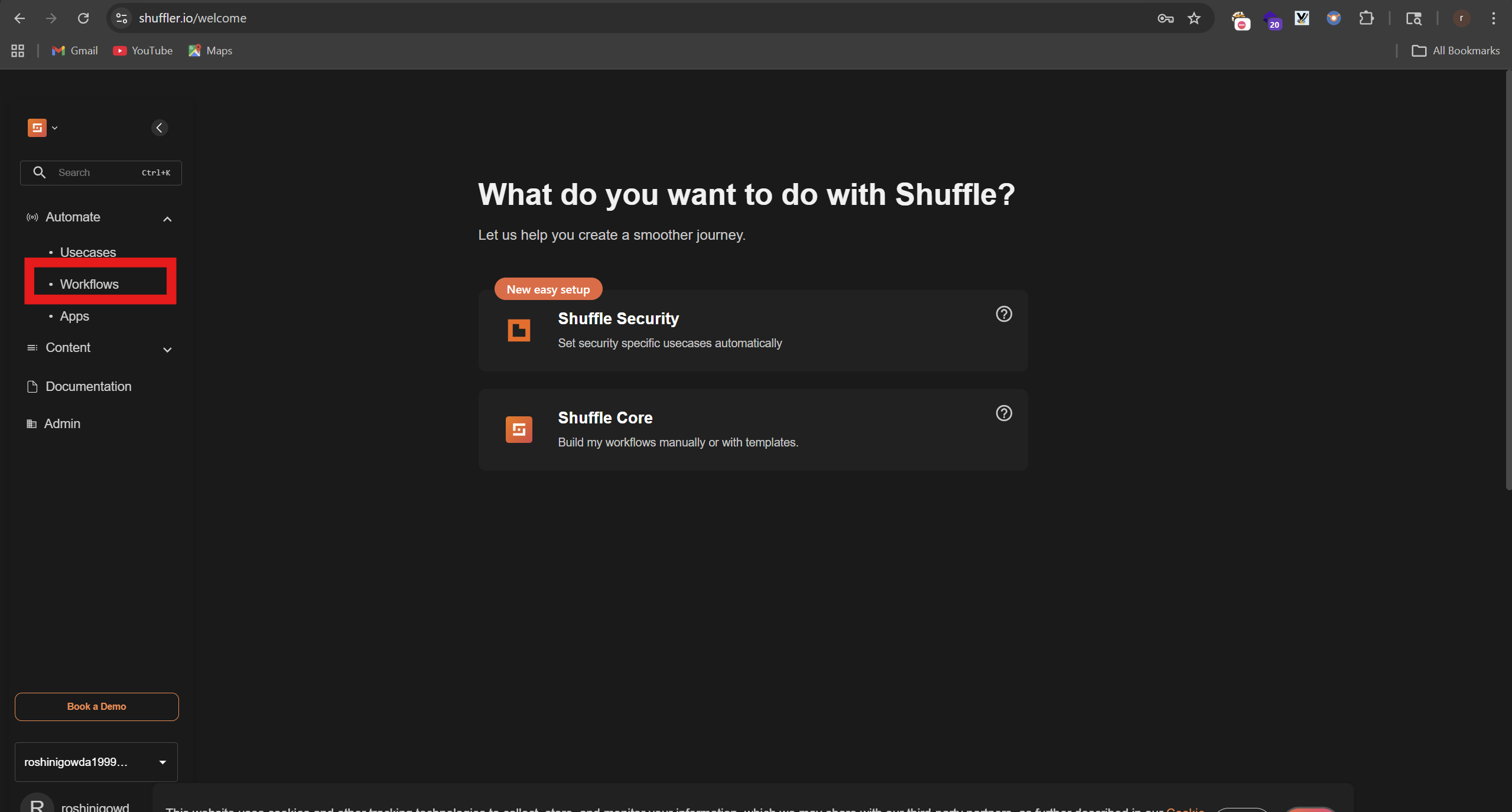
SOC Automation Lab Series 4
Now we will combine all of out tools and create an playbook on shuffler.io which is like an automation Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
I Investigated a Phishing Network That Has Been Running Since 2016 with 400+ Phishing Blogs and…
Before I start, just note that the full techinacal report containing all IOCs, redirect chain analysis and detection rules is available… Continue reading on Med
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Booking.com Hack Exposes Customer Data, Sparks Travel Scam Fears
Booking.com confirms a data breach that exposed traveler details, raising urgent concerns about highly targeted phishing scams and customer safety. The post Boo
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Google Rolls Out End-to-End Encryption to Eligible Gmail Users on Mobile
Google has brought end-to-end encrypted Gmail to Android and iOS for eligible Workspace users, extending secure mobile email without extra apps. The post Google
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
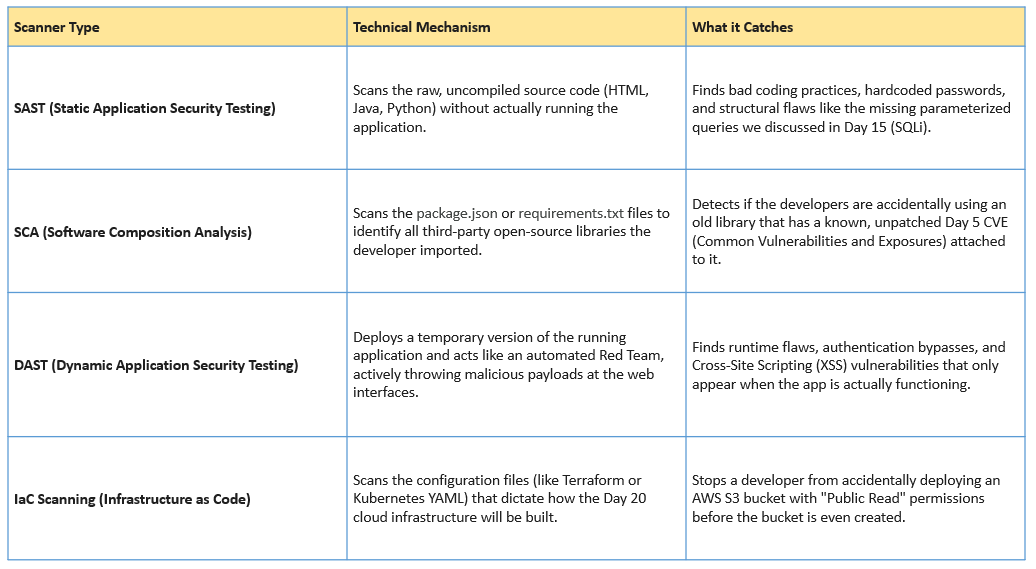
Day 21: Shifting Left — DevSecOps and the CI/CD Pipeline
Welcome to Day 21 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »

Dev.to · SephX
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Your WordPress site can be fully compromised in 7 minutes. Here's what the attacker does with each one.
Minute 0 - bot finds your unpatched plugin, drops a 39-byte backdoor disguised as .access.log.php,...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Police tracking 500M devices using AD
Citizen Lab reported that Hungarian law enforcement used ad data to track hundreds of millions of devices globally. Not backdoor. Just ad… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Let’s Defend: SOC287 — Arbitrary File Read On Checkpoint Security Gateway(CVE-2024–24919)
In this blog, we will analyze a critical alert generated in the Let’s Defend SOC environment(SOC287), triggered by activity associated… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
“Bug Bounty Bootcamp #33: IDOR Hunting — When Changing a Single Number Grants You Everyone’s…
You log in as user #1001. You change the URL to user #1000. Suddenly, you’re looking at someone else’s invoices, emails, and phone numbers… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Sudo Buffer Overflow: TryHackMe walkthrough
A tutorial room exploring CVE-2019–18634 in the Unix Sudo Program. Room Two in the SudoVulns Series. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Cyber Threat Triangle
A conceptual model for understanding cyber risk Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Smart Cameras, Smarter Decisions: How Meraki MV Turns Video Into Actio
Security cameras have traditionally been passive devices — recording footage that sits untouched until an incident forces someone to scrub… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
This $100 Instagram Bug Proves Bug Bounty Is About Thinking, Not Complexity
Before I break this down — if you are trying to get into bug bounty hunting and want something actually useful, go check out hackthrough… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Why CISSP Is the Most Valuable Cybersecurity Certification for Senior Professionals in 2026
The cybersecurity landscape has never been more competitive — or more rewarding — for those who hold the right credentials. Among the… Continue reading on Mediu

Dev.to · Chioma Halim
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
All It Took Was npm install (Axios Attack)
All it took was npm install. During the Axios attack, that was enough to run malicious code on your...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Cybersecurity Gap No One Is Talking About: Claude Mythos vs Opus 4.6
Most people think AI in cybersecurity is just getting better. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Tek Bir Link ile Uygulamayı Ele Geçirmek: Deep Link ve WebView İstismarı
Mobil Dünyanın Arka Kapıları: WebView ve DeepLink Zafiyetleri Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Why shared responsibility models confuse SMEs.
Shared responsibility looks clean in a diagram. Continue reading on aneo Security Insights »
The Next Web AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Basic-Fit hit by hack affecting members across multiple countries, including 200,000 in the Netherlands
The breach exposed names, addresses, email addresses, phone numbers, dates of birth, and bank account details. No passwords or identity documents were accessed.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Is your security strategy reactive — or intelligently proactive?
易 Zefai Insights || Cyber Security Edition Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Curing Detection Engineer Anxiety: Uncovering the Blind Spots in Your Rules
In our previous post, 《Detection Rule Fragility: Design Pitfalls Every Detection Engineer Must Know》,we explored why detection rules based… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Mastering the ISO 22301 Lead Implementer Role: Beyond the Certification
Imagine your organization faces a sudden, catastrophic system failure or a regional disaster. The difference between a business that… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
You May Have Perfect Backups and Still Lose Everything
Backup Best Practices for Data You Cannot Afford to Lose Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Malloc Privacy Weekly
We bring you the most recent mobile cybersecurity updates in the newest edition of Malloc Weekly Privacy. This week, we cover the surge in… Continue reading on
 DeepCamp AI
DeepCamp AI