Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,417 reads from curated sources
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Cybersecurity for Scammers
While trying to make a hotel reservation, I unexpectedly found myself in the middle of a critical security vulnerability. In this article… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Forget Hallucination: What if AI Deceives You?
Threads & Perspectives: On Mythos, Statistics, and a Very old playbook Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Hackers Give Rockstar Games Until April 14 To Pay For Stolen Data
As Rockstar Games confirms hack, ShinyHunters hackers give the GTA developer just days to pay ransom for stolen data.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Mr Robot VulnHubWalkthrough | 06/100
Introduction: The Machine That Started With a Smirk Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Analyse des risques stratégiques liés à l’intégration de l’EUDI wallet dans la gouvernance cyber…
La révolution silencieuse de l’EUDI Wallet : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SOC-Challenge-Day0
Episode 0: Membangun Lab SOC di Cloud Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Phishing Email Analysis SOC Analyst Guide Part-4 Email Authentication.
In this article we are going to touch our created lab a bit to understand the email security checks. Email security is used to protect… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Inside the Rockstar Games Breach: How ShinyHunters Exploited a Hidden Third-Party Weakness
A real-world breach that proves attackers don’t break in, they exploit trust. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Claude Mythos Might Break Cybersecurity. But Not in the Way You Think.
I’ll be honest with you. When I first read about Claude Mythos, my reaction wasn’t awe. It was a question I couldn’t shake. Continue reading on Medium »

Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Windows Recall Hides EVERYTHING: This Tool Exposes It All!!!
Windows Recall is one of those features that immediately triggers strong reactions. On one side, it promises a searchable timeline of what… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The scariest AI story of the year!
Big claim, but meet Mythos the AI superhacker breaking bulletproof code. Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Aadi-Tech Vault: Personal Security Reimagined
Aadi-Tech Vault is the brainchild of Aditya Rai, who designed, coded, and architected the entire encryption system from scratch. Built on a budget PC, this proj
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Building a Windows Server Lab: From Zero to Active Directory Domain Services
Documentation is a key part of the learning process in cybersecurity. Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
If You See This Apple Message, Delete It—Your iCloud Account Is Under Attack
Apple users warned all photos and other content will be deleted — here's what to do.

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
FBI Warns iPhone And Android Users—End-To-End Encryption Won’t Protect You
FBI warnings and new attacks show encrypted messaging isn’t as safe as you think — your phone and your accounts are now the real targets.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Quantum Clock is Ticking: Why the Timeline to Post-Quantum Cryptography Just Crashed
The traditional security paradigm relies on a comforting, yet increasingly dangerous assumption: that a quantum computer capable of… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Critical Role of Network Security in the Modern Digital Era
Author: Cera Charles Edward Institution: University of Martland Global Year: 2026 Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SecurityMetrics Uncovers a 700 Site Global Skimming Operation
SecurityMetrics forensic experts identified a 700 site skimming operation using a sophisticated, multi-channel kit designed to lock out… Continue reading on Cod

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Cyber 101: Living Online: Understanding the Cyber World Without Getting Burned
Imagine we’re just having a casual conversation, trying to make sense of this whole “cyber world” without making it feel like a lecture… Continue reading on Med

Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Django Security Checklist: Protecting Your Web Application in 2026
Every day, Django applications are compromised because developers skip critical security steps. With six new CVEs patched in early 2026 —… Continue reading on M
Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
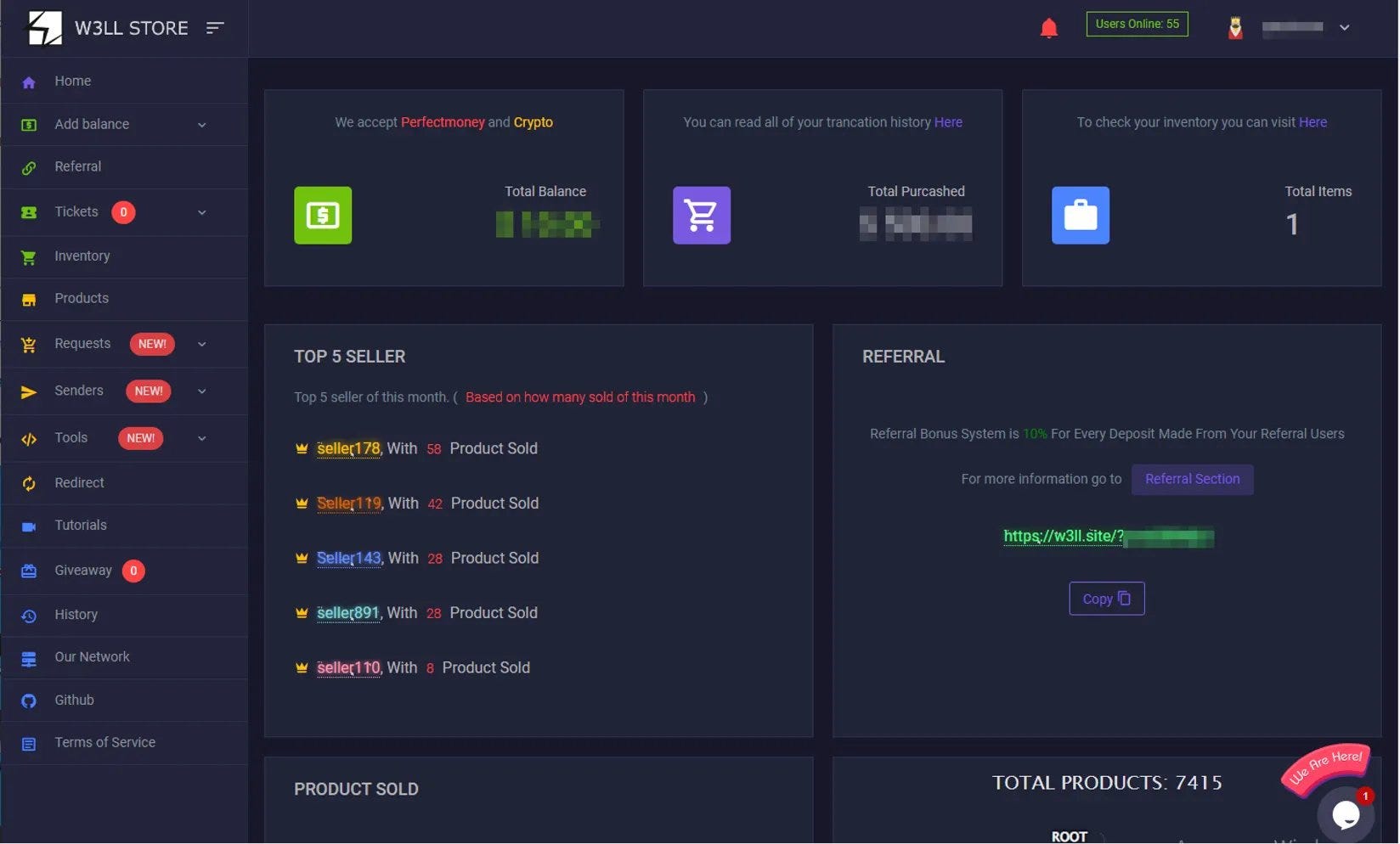
The $500 Cybercrime Factory: Inside the Fall of W3LL and the Industrialization of Global Phishing
How a sleek phishing kit turned fraud into a scalable business — and why its takedown changes less than we think Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Top 10 Critical CVEs from March 2026 — With Learning Resources & Practical Analysis
Analysis of 10 critical CVEs from March 2026 with practical insights for bug bounty and vulnerability research Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
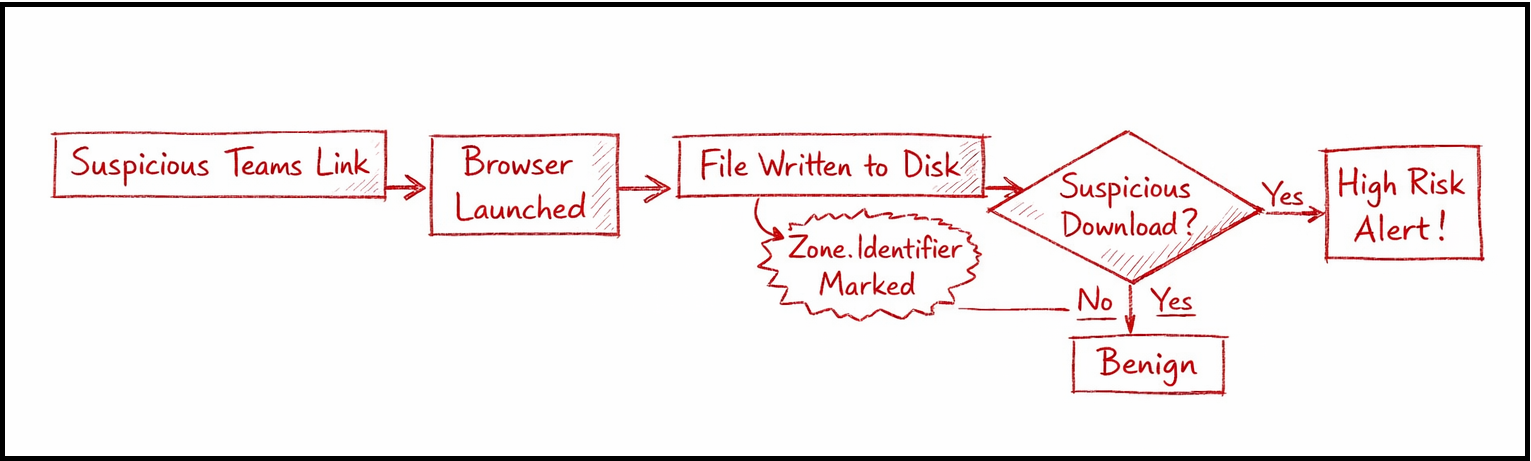
Hunting Malicious Links Delivered via Microsoft Teams: An Endpoint + Cloud Correlation Approach
Modern enterprise attacks are quietly shifting away from traditional entry points like phishing emails. Instead, adversaries are… Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
WHEN "NOT A VULNERABILITY" GETS PATCHED IN 72 HOURS
By Ahmed Batayneh | March 2026
I submitted 34…
A data-driven analysis of vulnerability coordination patterns in enterprise bug bounty programs. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
PicoCTF Wrieup — Time Machine
Hello everyone, today I will be providing a writeup on the picoCTF problem Time Machine. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
LetsDefend: SOC335 — CVE-2024–49138 Exploitation Detected
How I Investigated CVE-2024–49138 on LetsDefend and What the Artifacts Were Actually Telling Me Continue reading on Medium »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
A quick note on TLS certificates
TLS certificates are commonly used in almost all modern websites and APIs. Most people know they “enable HTTPS”, but how they work and how… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SOC173 — Follina 0-Day Detected
First we need to understand that why the alert was triggered. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
How Hackers Steal Credentials Without Malware, LOLBAS and Living off the Land: When Your Own Tools…
Your antivirus did not fire. No malicious file was dropped. No suspicious process appeared in your security dashboard. But by the time the… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Day Networking Stopped Being Intimidating
The hardest network I’ve ever had to engineer is the direct link between these concepts and my brain. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Your 10-K Just Made Identity Governance a Legal Liability
Or: The SEC Is Reading Your Identity Claims Like a Prosecutor Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
That Invoice in Your Inbox Might Be Stealing From You Right Now
Most scams announce themselves. The Nigerian prince, the lottery you never entered, the customs fee on a package you didn’t order — these… Continue reading on M

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
There's a New Browser Password Stealer That Can Bypass 2FA—And It's Rentable for $1,000/Month
If you thought about the two factors authentication was keeping you safe, there’s some bad news. Continue reading on Predict »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Nobody Gave IT Professionals an Identity. So We Created One.
For decades, the people who built and protected the digital world have remained invisible. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Anthropic’s Mythos Just Proved Enterprise AI Governance Is a Cybersecurity Emergency
Anthropic’s Mythos found thousands of zero-days autonomously and triggered a Fed-level response. Enterprise AI governance just became a… Continue reading on Med
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The $50 Exploit: Why Claude Mythos Just Shattered Security Economics — Even If Anthropic Never…
A dormant exploit hidden for decades now costs $50 and an afternoon. Continue reading on Medium »

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Boosting Security for Nigerian Startups
Laying the Foundation: Why Cybersecurity Matters Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
We Can Black Out a Country but Can’t Turn On MFA
The United States is the most capable cyber force on the planet. In January, U.S. Cyber Command helped take down Venezuelan radar… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Bypassing a 403 Using Path Manipulation in Calendly Assets
According to their page a few points to note: Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
IDS Evasion and Detection with Snort: Building and Breaking Your Own Detection Lab
Although intrusion detection systems (IDS) are sometimes thought of as “black boxes” that mysteriously indicate “suspicious traffic,” true… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SOC257 — VPN Connection Detected from Unauthorized Country
We will look into the issue. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
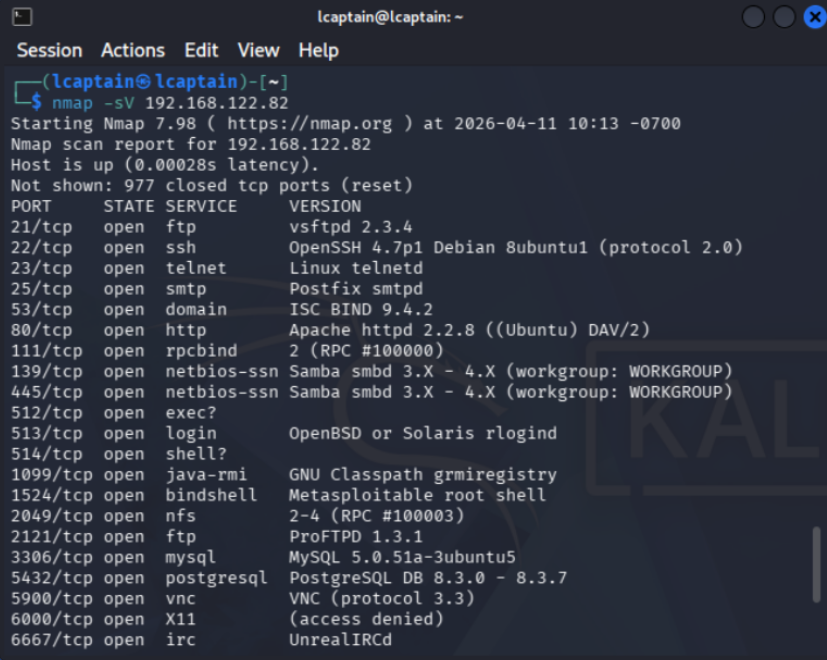
How I Ran My First Exploit ( Legally )
I’ve always been interested in hacking and exploitation, but I never actually tried doing anything myself. Like most people, I assumed it… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
TryHackMe SOC Analyst Road Map Part-21
Cyber Security 101 > Offensive Security >Hydra Task 1 — Hydra Intrıduction THC Hydra adlı program, çevrimiçi parola kırma için kullanılan… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SOC Automation Lab Series 2
Now let’s view the console in Vultr : Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Why Indian Startups Get Hacked Without Knowing It
By Shouvik Mukherjee — Ex-Principal Engineer, TEDx Speaker, Founder at Bachao.AI Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Arasaka | Hack Smarter Walkthrough
In this walkthrough, we will be compromising Arasaka, an easy-difficulty Active Directory challenge lab from Hack Smarter. The engagement… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
️ Write-up: DanaBot Lab — CyberDefenders By Mohammed-Ali
Overview Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Disclose The Agent — Full Writeup
Challenge source: LetsDefend — Disclose The Agent Continue reading on Medium »
 DeepCamp AI
DeepCamp AI