Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,422 reads from curated sources
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Massive Chrome Extension Scam Exposes 20,000 Users to Data Theft
Researchers linked 108 malicious Chrome extensions to a coordinated campaign that exposed about 20,000 users to data theft, backdoors, and ad injection. The pos

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Anatomy of a Shadow: Dissecting the Solar Winds SUNBURST Supply Chain Attack
The 2020 SolarWinds Compromise remains a watershed moment in cybersecurity, fundamentally shifting the industry’s approach to supply chain… Continue reading on

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
iPhone Setting Update Stops FBI From Extracting Signal Messages
After the FBI was able to extract incoming Signal messages from an iPhone, the messaging service’s CEO has now responded with a simple settings change to preven

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Stop Paying for Threat Detection You Don’t Need
Jeff Darrington, Technical Marketing Director, Graylog Continue reading on The Visibility Layer by Graylog »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Beste VPN voor Thuiswerken 2026: 5 Getest
Door Pieter Janssen | IT-beveiligingsconsultant, 11 jaar ervaring | Utrecht | Bijgewerkt: april 2026 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Şirketler Ne Kadar Güvende?
Görünürlük Artarken Riskler de Artıyor Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Manufacturing Identity Security Is No Longer an IT Problem — It’s a Business Risk
Manufacturing has become the most targeted industry for cyberattacks. And in the vast majority of incidents, the entry point is not a… Continue reading on Mediu

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Dangerous Microsoft Windows Update Confirmed—Do Not Download
As security researchers warn about a dangerous Microsoft Windows update that isn’t, users must pay close attention to what they are actually downloading.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
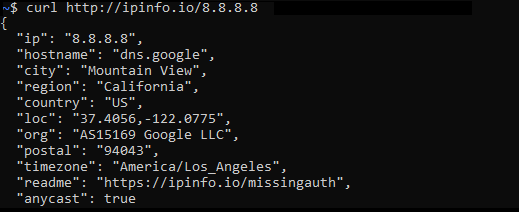
IP-info for analyzing IP Address information
With the current geo-policatal tensions in world it’s becoming important as security analyst to determine the originating traffic/attack… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
CyberSecurity Liability and Incident Disclosure
A Legal Research Report by The Innovation Attorney Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Vulnerability Discovery Cycle Just Collapsed. Here’s What We Built to Keep Up.
If you’re a CTO, CISO, or engineering leader, here’s what you need to know right now: Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
How a Simple Signup Feature Turned Into a Malware Delivery Vector (My First Paid Bug)
I wasn’t even looking for something big. Continue reading on Medium »
MIT Technology Review
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Cyberscammers are bypassing banks’ security with illicit tools sold on Telegram
From inside a money-laundering center in Cambodia, an employee opens a popular Vietnamese banking app on his phone. The app asks him to upload a photo associate
Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
10 Hours to Exploitation: How a Missing Auth Check in Marimo Turns Your Python Notebook Into an…
CVE-2026–39987 deep dive: a pre-authenticated RCE in Marimo’s terminal WebSocket that was weaponized within hours of disclosure. Why the… Continue reading on Me

Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Learn Cybersecurity Like a Pro in 2026
Creating Your Individual Knowledge Base Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
“How to Stay Safe Online” — Best practices for protecting personal information and avoiding online…
First, double-check that the URL begins with ‘HTTPS’ and that there’s a padlock symbol either before or after it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
From Security To Seo: Complete Business Solutions
From cybersecurity to SEO, get complete business solutions to grow and protect your brand. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Cloud Has an Address.
And Drones Found It.
I have explained hundreds of architectural decisions in my career. Tradeoffs between cost and performance. Debates about vendor lock-in… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Microsoft’s April 2026 Patch Tuesday Is a Warning Shot: A SharePoint Zero-Day, 169 Flaws, and a…
One critical IKE remote code execution flaw. And 169 vulnerabilities patched in a single month. Continue reading on Medium »
Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Claude Mythos Shows That Software Was Never as Safe as We Thought
A look at how Claude Mythos is quietly exposing how fragile all our software really is. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Claude Mythos Shows That Software Was Never as Safe as We Thought
A look at how Claude Mythos is quietly exposing how fragile all our software really is. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Best VPN for Streaming 2026: 5 Services Tested
If you are trying to watch content across Netflix, Disney+, BBC iPlayer, or Hulu from outside the licensed territory, a reliable VPN has… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Keys to the Kingdom: How to Secure Your Microsoft 365 Tenant in 2026
For many businesses, Microsoft 365 isn’t just an email app; it is the entire office. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
FortiClient EMS Gets a Second Zero-Day in One Week — CVE-2026–35616 Is Already Being Exploited
If you patched FortiClient EMS after CVE-2026–21643 and thought you were done — you’re not. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Construction Ransomware: How to Strengthen Security in 2026
Construction and BTP firms face growing ransomware risk. Learn how remote access, RDP exposure, and layered security fit into a stronger… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Is 2FA Enough to Secure Business Data?
Many businesses feel safer after enabling 2FA. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
OpenAI’s GPT-5.4-Cyber is defender tooling shipped before the next capability jump
OpenAI is fine-tuning cyber-permissive models for verified defenders ahead of more capable releases. GPT-5.4-Cyber is the first of the… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Si no conoces esta NMAP salte de la Ciberseguridad
Nmap. Si no la conoces, no es que vayas tarde… es que ya estás retrasado. La usa esta Elliot el de Mr.Robot Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Your MTTD Looks Great. Your Post-Alert Gap Doesn't
The cybersecurity landscape is facing a significant shift as AI-driven offensive capabilities accelerate, with adversary breakout times collapsing to minutes or

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Injection Attacks — From User Input to Full System Control
✍️ Introduction Continue reading on Bug Bounty Hunting: A Comprehensive Guide in English and french »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Invisible Backdoor: Why Your Biggest Cyber Threat Isn’t Even on Your Network
Imagine you’ve spent millions on a state-of-the-art security system for your home. You have biometric locks, reinforced glass, and 24/7… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
What Is “Quishing”?
You scan a QR code on a parking meter. Thirty seconds later, you’ve handed your card details to a criminal in another country. You won’t… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Agentic AI Pindrop Anonybit: The Future of Autonomous Identity Verification and Fraud Prevention
As we move deeper into the digital age, cybersecurity is more important than ever. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Crypto Security Tips for Beginners in 2026
Are you concerned about the safety of cryptocurrency in this digital world? Cryptocurrency is becoming popular worldwide as it is part of… Continue reading on M
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
A data removal service helped me reclaim my privacy - see if you need one, too
Data removal services automate the removal of your information from the web, but their biggest benefit is something else.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Why Hyderabad IT Professionals Are Turning to SailPoint IIQ Certification in
2026Hyderabad has emerged as India’s second-largest hub for cybersecurity and enterprise software hiring. Companies like Deloitte… Continue reading on Medium »

Medium · NLP
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Your Logs Are Leaking PII (Here’s How We Fixed It at Scale : Part 1/2)
The PII Sprawl Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Cmess — TryHackMe Walkthrough
Hosts File Configuration Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
BlueHammer Isn’t a Defender Bug — It’s a Windows Design Flaw. Here’s the Real Fix.
Why detection rules won’t save you, and what Microsoft should actually do. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Why Anthropic’s Claude Mythos Is Not Fearmongering but a Force Reshaping Cybersecurity
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Securing the Backbone — Issue #14: When Risk Feels Invisible: Bridging the Executive Disconnect in…
Date: May 5, 2025 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Reverse Engineering on CyberTalents: Solving All Easy Challenges Part 4
Challenge 12 : (chall ) Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Your Encrypted Messaging App Is Not Enough.
The WhatsApp Spyware Attack Proves It Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
PicoCTF Writeup — Crack the Gate 1
A writeup to the picoCTF problem Crack the Gate 1 featured in picoMini by CMU Africa. Continue reading on Medium »
Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The 98% Accuracy Lie: Why I Stopped Trusting Cybersecurity Datasets and Started Building My Own
I recently decided to build an Intrusion Detection System (IDS). My goal? To build a system that could detect all cyber attacks. Continue reading on Medium »
Reddit r/cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Argus – found 18 validated exploits in ffmpeg, curl, OpenSSL, SQLite, and Django using LLM-driven autonomous vulnerability discovery
Open-source CLI tool. Pipeline: - deterministic tree-sitter recon - LLM hypothesis generation - LLM triage - Claw Code agent writes and runs exploit code in a D
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Shadow IT Risk: What You Don’t See Can Hurt You
Not every system in your organization is approved. But many are still in use. Continue reading on Medium »
InfoQ AI/ML
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
New Rowhammer Attacks on NVIDIA GPUs Enable Full System Takeover
Security researchers have demonstrated a new class of Rowhammer attacks targeting NVIDIA GPUs that can escalate from memory corruption to full system compromise
 DeepCamp AI
DeepCamp AI