Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,376 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1h ago
XSS Nedir ve Neden Hâlâ Tehlikeli? | Bir Siber Güvenlik Öğrencisinin Notları
Bu yazı, web güvenliği öğrenme sürecimde tuttuğum teknik notların bir parçasıdır. Continue reading on Medium »

Dev.to · Kwansub Yun
🔐 Cybersecurity
⚡ AI Lesson
2h ago
Beyond Repo Scanning: How AIRI Expanded the Risk Vocabulary in STEM BIO-AI 1.7.x
This is the second half of the same 1.7.x transition. In the previous post, I wrote about...

Dev.to · Dwayne McDaniel
🔐 Cybersecurity
⚡ AI Lesson
2h ago
GitGuardian Now Flags Admin and Overprivileged Identities Across AWS, Entra, and Okta
Not all leaked secrets carry the same risk. A leaked credential attached to a read-only logging job...

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
2h ago
‘Won’t Fix’—All VPN Apps Affected As Google Android 16 Leaks Info
An Android 16 VPN bypass has been confirmed, affecting all VPN apps and exposing your real IP address online, but Google marked the vulnerability report as Won’

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3h ago
How the 2025 “CWE Top 25 Most Dangerous Software Weaknesses” List was Built
“Out-Of-Bounds Read” is the CWE Program’s free podcast about common weaknesses in software and hardware, the vulnerabilities they cause… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5h ago
Fortinet & Palo Alto ile Multi-Vendor IPSec VPN Yapılandırması
FortiGate ile Palo Alto Arasında IPSec Tüneli Nasıl Kurulur? Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5h ago
The SLA Credit Scam: What 99.9% vs 99.99% Uptime Actually Means
Stop falling for the SLA credit trap. Discover the true mathematics behind server downtime, the hidden security risks causing outages, and… Continue reading on
Medium · Machine Learning
🔐 Cybersecurity
⚡ AI Lesson
5h ago
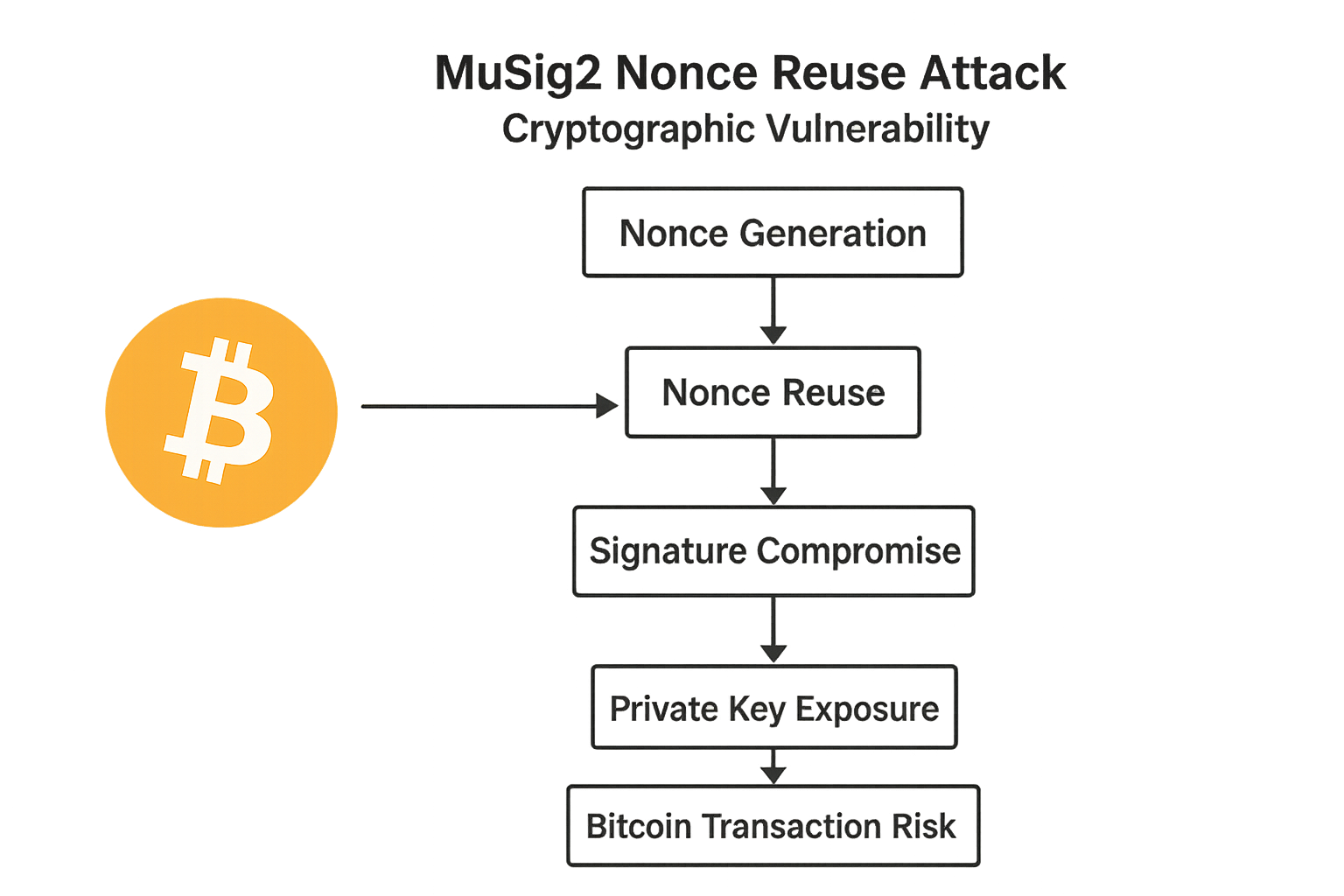
Attack of the Dark Ghost of Nonce Reuse: A critical Bitcoin vulnerability and recovery of private…
Critical Nonce Reuse Vulnerability Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5h ago
OpenAI Faces Class-Action Privacy Lawsuit Over Alleged Data Sharing Practices
Artificial Intelligence continues to reshape how organizations work, communicate, and innovate. However, as AI adoption accelerates… Continue reading on Medium
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
6h ago
The best VPN routers of 2026: Expert tested and reviewed
My favorite VPN routers provide blanket coverage and security for your home, saving you the work of installing VPNs on individual devices. Check out my top pick

The Register
🔐 Cybersecurity
⚡ AI Lesson
8h ago
To gain root access at this company, all an intruder had to do was ask nicely
Human IT managers thought they were being nice to the boss, but were assisting a threat actor

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
The Invisible Infrastructure Behind India’s Digital Wallet Ecosystem
Understanding the Cybersecurity, Legal, and Financial Architecture of Prepaid Payment Systems Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
SQL injection explained in simple words part 1
hii , My name is Abhi or as the user name says HellBoy-zero. this artical will not cover how much i love HellBoy character and how the… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
How I Accidentally Became the ‘Security Guy’ at Every Party
(And Why I Can Never Go to a Social Gathering Without Fixing Someone’s WiFi) Continue reading on Medium »

Dev.to · CVE Reports
🔐 Cybersecurity
⚡ AI Lesson
9h ago
CVE-2026-42945: CVE-2026-42945: Heap-based Buffer Overflow in NGINX ngx_http_rewrite_module
CVE-2026-42945: Heap-based Buffer Overflow in NGINX ngx_http_rewrite_module Vulnerability...

Dev.to · V G P
🔐 Cybersecurity
⚡ AI Lesson
10h ago
I Built a Zero-Dependency Browser Storage Encryption Library — Here's Why
A few months ago I found myself auditing a side project and noticed something uncomfortable: I was...

Dev.to · Mark0
🔐 Cybersecurity
⚡ AI Lesson
10h ago
Breaking things to keep them safe with Philippe Laulheret
Philippe Laulheret, a Senior Vulnerability Researcher at Cisco Talos, discusses the intricacies of...

Dev.to · AgentGraph
🔐 Cybersecurity
⚡ AI Lesson
10h ago
AgentGraph Update
Long-form (~1500 words). Walk through the five attack categories mcp-security-scan checks (credential...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
11h ago
RiskwareSupplyChain: A Freemium Software Supply Chain Risk Intelligence Tool
Frustration Meets Function Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
14h ago
How to use Vercel's Deepsec with ollama
How to run continuous, AI-powered security audits on your codebase — routed through a local proxy that picks the cheapest viable model for each file. Most secur
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
16h ago
The Hidden Supply Chain Risk in Your `pip install`
This Is Not an Anomaly The LiteLLM incident is part of an accelerating pattern: 454,000+ new malicious packages in open-source registries in 2025 Malicious pack

Dev.to · James
🔐 Cybersecurity
⚡ AI Lesson
17h ago
OSINT for Businesses: Legal Web Intelligence in 2026
Open Source Intelligence: Tools and Techniques for 2026 Open Source Intelligence (OSINT)...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
19h ago
The Hidden Terminals of the Internet: A Guide to Ports
Why the “invisible cloud” is actually a massive transportation hub, and what it teaches us about boundaries. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
19h ago
In this walkthrough, I am going to show how I investigated and successfully completed the “VPN…
A lot of people rush through alerts like this and immediately assume the account was compromised just because the login came from another… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
19h ago
Bir HTTP İsteği Gerçekten Nerede Biter?
Sen tarayıcı üzerinden bir siteye gitmek istediğinde tren hangi duraklarda geçiyor biliyor musun? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
19h ago
Scoring Cyber Maturity Across 50+ Business Units That Looked Nothing Alike
A practical account of using NIST CSF to assess and score 50+ business units across finance, insurance, technology, and other verticals… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
19h ago
Deepfakes et désinformation : la menace est là
Il y a quelques années, un deepfake se repérait assez facilement. Un visage qui bougeait de façon bizarre, un son légèrement décalé, une… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
20h ago
Get PQC Ready PDQ — Part 1
Quantum, AI, and the Window That’s Already Closing Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
21h ago
DVWA(SQL Injection)
Input 1 into the text box and submit. Code is suppose to print ID, first name and surname to the screen. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
21h ago
AI Can Find Security Holes. But Who Will Close Them?
In a previous essay, I wrote about how companies, especially in the United States, seem increasingly willing to cut people because of AI. Continue reading on Me
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
23h ago
Complete Guide to Computer Hacking Forensic Investigation
Cybercrime is increasing rapidly as organizations continue relying on digital systems, online services, and cloud technologies. Businesses now face cyber threat

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
mTLS Var Ama Gerçekten Güvenli mi? Mimari Bir Check-Up
mTLS (Mutual TLS) Rehberi: Nedir, Nasıl Çalışır ve Sahada Nerede Kırılır? Continue reading on Medium »
Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
1d ago
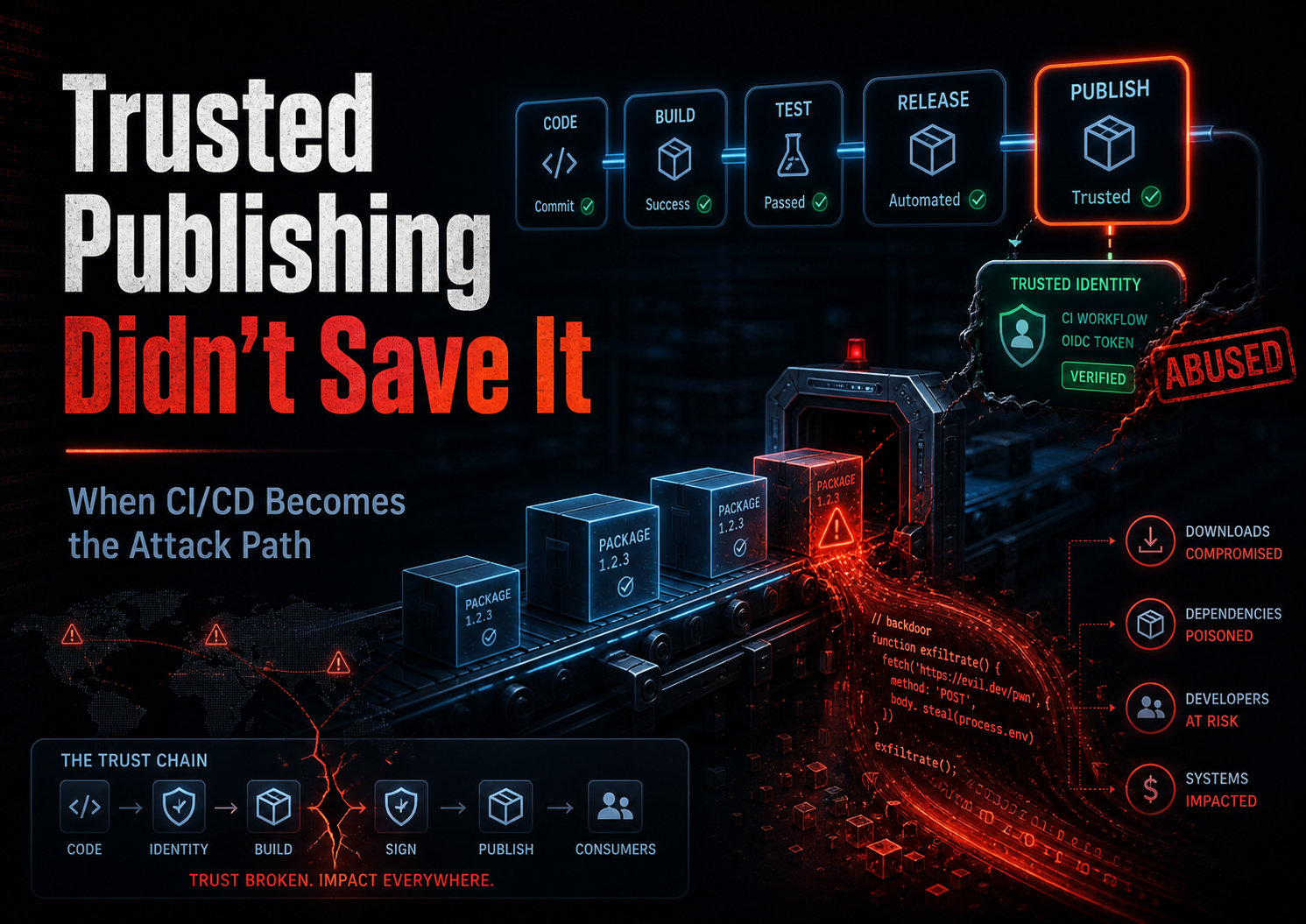
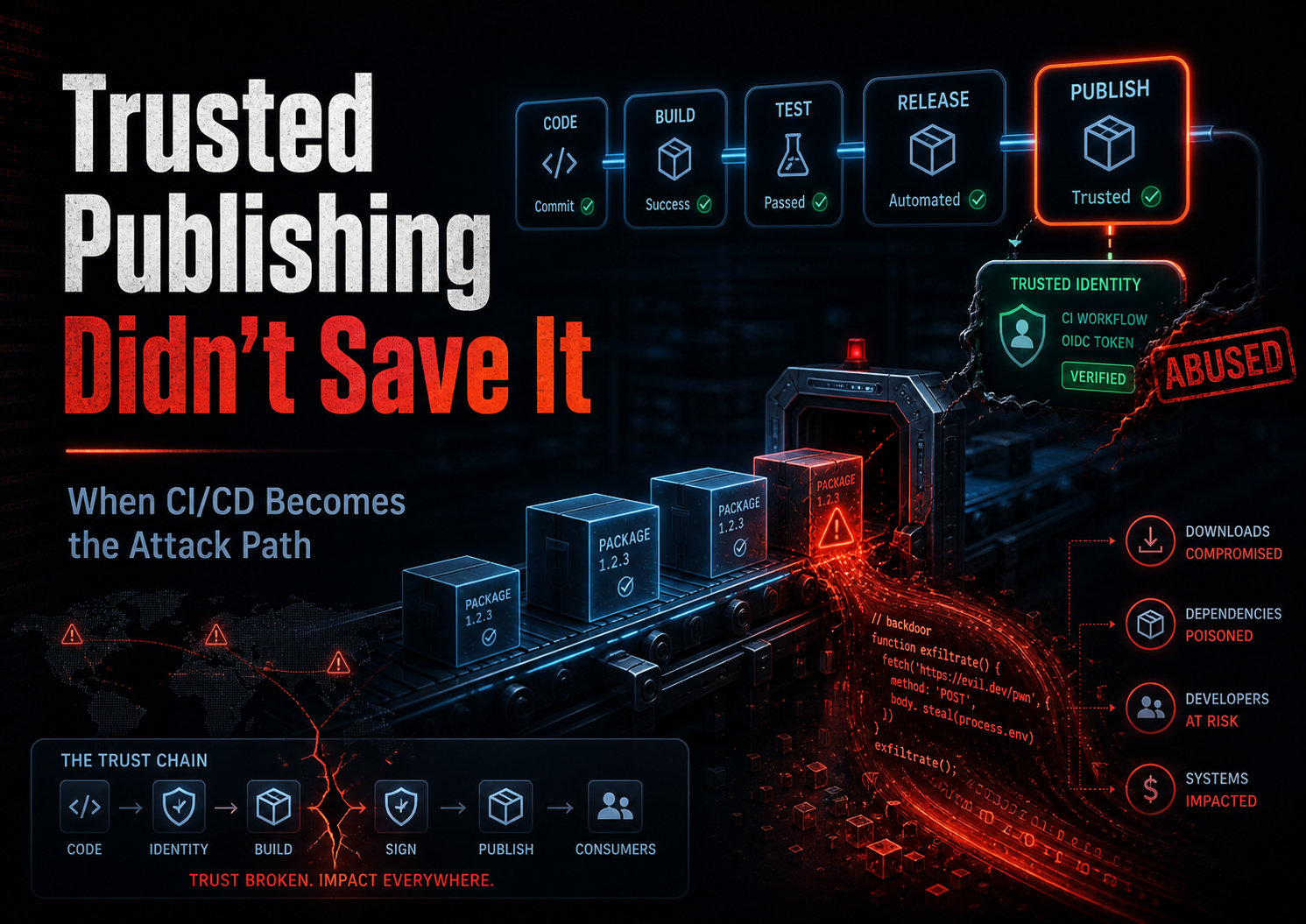
Trusted Publishing Didn’t Save TanStack — Why npm Supply Chain Security Just Changed Again
A lot of developers still assume one thing about modern package security: Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Trusted Publishing Didn’t Save TanStack — Why npm Supply Chain Security Just Changed Again
A lot of developers still assume one thing about modern package security: Continue reading on Medium »

Dev.to · Beatriz Albernaz
🔐 Cybersecurity
⚡ AI Lesson
1d ago
We Built a Pentesting Company Because We Were Tired of Watching Startups Get Burned
There was a pattern we kept seeing that genuinely bothered us. A startup would get to Series A, or...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
How I Lost All My Facebook Pages to a Malicious Chrome Extension And What Every Human Needs to…
A note before we begin: This is my first article on Medium. I am a cybersecurity professional currently in active training at a… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
AI Model impersonation, why being slow is your weapon and why latest threat intelligence is needed
A fake Hugging Face repository called “Open-OSS/privacy-filter” recently appeared, designed to impersonate an OpenAI-style privacy… Continue reading on Medium »

Dev.to · Andrea Debernardi
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The database has to be a defensive boundary again
For two decades the database has been able to outsource trust to the application layer. The app...

Dev.to · Teruo Kunihiro
🔐 Cybersecurity
⚡ AI Lesson
1d ago
TanStack Was Not the Whole Story: Mini Shai-Hulud Was an npm/PyPI Supply-Chain Worm
How the TanStack npm compromise fits into the broader Mini Shai-Hulud campaign across npm, PyPI, GitHub Actions, IDE hooks, and CI/CD secrets.

Hackernoon
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Smart Contract Security: A Taxonomy of Vulnerabilities, Attacks, and Defenses
Smart contracts are immutable once deployed. A single bug can drain millions in minutes. This article builds a practical taxonomy of the most dangerous vulnerab

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Boot-to-Root Walkthrough: Compromising Devarea on HackTheBox — By BitR1FT
Today, we are taking on Devarea, a machine that tests your ability to string together multiple misconfigurations. We’ll start by… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Mini Shai-Hulud: Yazılım Dünyasının Kalbine Sızan Görünmez Tehlikeyi Anlamak
Milyonlarca kez indirilen güvenilir altyapılar nasıl birer silaha dönüştü? Yazılım tedarik zinciri krizine ve siber güvenliğin yeni yüzüne… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Synthetic Attack Log Generation for Splunk: A Detection Engineering Approach
1. Introduction and Scope Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
SOCFortress Vulnerability Operations Center — Part II: External Exposure Module
Intro: Seeing Your Internet-Facing Risk Before Attackers Do Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Top Cybersecurity Threats Indian Businesses Will Face in 2026
Why This Conversation Can’t Wait Anymore Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The Cybersecurity Failure of Odido and the Erosion of Digital Trust in the Netherlands
The promise of the digital age was built on a foundation of seamless connectivity and the ironclad security of personal data. Continue reading on Medium »

Dev.to · Hamza
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Coming Soon: React2Shell
In the React2Shell exploitation, we can abuse a deserialization vulnerability in React Server...

Dev.to · curi0us_dev
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Best RBAC solutions: what to shortlist and why
If you are evaluating RBAC tools right now, you already know the hard part is not finding "features."...
 DeepCamp AI
DeepCamp AI