📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 786 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13824)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsMedium · Programming

Medium · Cybersecurity
6d ago
Why Businesses Need a Managed Security Service Provider in Today’s Digital Landscape
In an era where cyber threats are evolving faster than ever, businesses can no longer rely solely on traditional security measures. From… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
SecurityMetrics Uncovers a 700 Site Global Skimming Operation
SecurityMetrics forensic experts identified a 700 site skimming operation using a sophisticated, multi-channel kit designed to lock out… Continue reading on Cod

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Cyber 101: Living Online: Understanding the Cyber World Without Getting Burned
Imagine we’re just having a casual conversation, trying to make sense of this whole “cyber world” without making it feel like a lecture… Continue reading on Med

Medium · Cybersecurity
6d ago
Linux User Lifecycle Management: Account Types, Password Expiry & Security Best Practices
Introduction Continue reading on Medium »

Medium · Cybersecurity
6d ago
The Subdomain That Never Died
“We deleted it… just not everywhere” Continue reading on MeetCyber »
Medium · Cybersecurity
6d ago
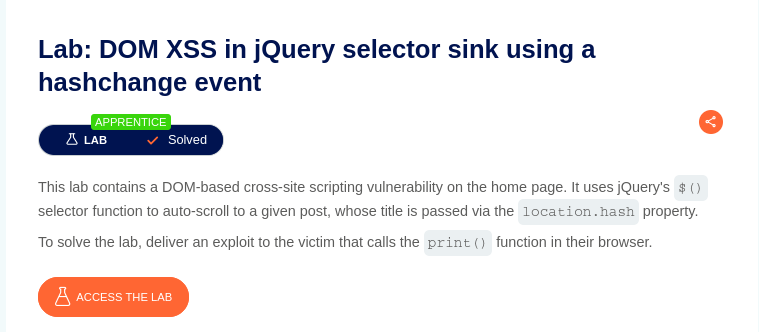
DOM XSS in jQuery selector sink using a hashchange event — Beginner Friendly + Practical Exploit
Before jumping into the exploit, here are very short basics so no one gets confused Continue reading on Medium »

Medium · Cybersecurity
6d ago
I got tired of “private” key generators that require a server upload, so I built my own.
Hey everyone, Continue reading on Medium »
Medium · Cybersecurity
6d ago
Why Cybersecurity isn’t just an option anymore?
It won't happen to me. I am just a regular person. Continue reading on Medium »
Medium · Cybersecurity
6d ago
First-time CTFs are a HARSH reality check
Starting out in CTFs sometime last year, I had been a little overconfident like many beginners in the field, thinking having some basics… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Top 10 Critical CVEs from March 2026 — With Learning Resources & Practical Analysis
Analysis of 10 critical CVEs from March 2026 with practical insights for bug bounty and vulnerability research Continue reading on Medium »

Medium · Cybersecurity
6d ago
Your ChatGPT Just Became a Security Nightmare in 2026 — The Silent AI Risks No One Talks About
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
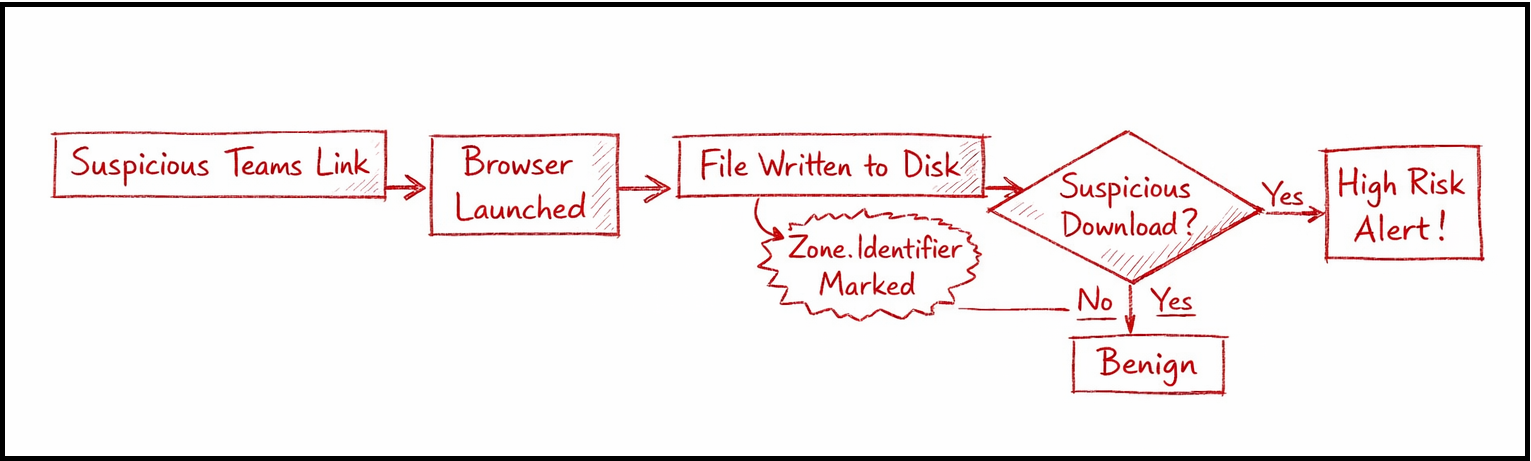
Hunting Malicious Links Delivered via Microsoft Teams: An Endpoint + Cloud Correlation Approach
Modern enterprise attacks are quietly shifting away from traditional entry points like phishing emails. Instead, adversaries are… Continue reading on Medium »

Medium · Cybersecurity
6d ago
I’m A GRC Engineer
You can be, too. Continue reading on Medium »

Medium · Cybersecurity
6d ago
Dev Day with Sam #3: CNN: Teaching Machines How to See
There was a time I thought computers just knew what they were looking at. Continue reading on Medium »

Medium · Cybersecurity
6d ago
Facebook (Meta) 2021 Outage Case Study
Executive Summary Continue reading on Medium »

Medium · Cybersecurity
6d ago
The Identity Paradox: Why Zero Trust is the only shield against AI-Automated Social Engineering
In 2026, the most dangerous malware runs on human psychology Continue reading on Medium »

Medium · Cybersecurity
6d ago
10 Books That Actually Teach You to Think Like a Threat Analyst
Most CTI reading lists are just gear catalogues. This one is different — every pick here builds a specific mental model you’ll use every… Continue reading on Me

Medium · Cybersecurity
6d ago
CyberDefenders — Hafnium APT Lab Writeup
Overview Continue reading on Medium »

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
6d ago
Built an AI C2 Framework That Plans Attacks Like a Chess Engine.
3 AM. I’m watching an AI agent plan its next move against a lab network. Continue reading on Medium »

Medium · Cybersecurity
6d ago
Anthropic Built Something and Refused to Release It.
Most people are arguing about what Mythos can do. The real story is what it means that a lab chose not to ship it. Continue reading on Medium »
Medium · Cybersecurity
6d ago
Quantum + AI + Glasswing: The Stack That Quietly Changed Cybersecurity in April 2026
Why the convergence of autonomous AI, quantum acceleration, and infrastructure platforms may signal the beginning of a new technological… Continue reading on Me
Medium · Cybersecurity
6d ago
WHEN "NOT A VULNERABILITY" GETS PATCHED IN 72 HOURS
By Ahmed Batayneh | March 2026
I submitted 34…
A data-driven analysis of vulnerability coordination patterns in enterprise bug bounty programs. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
WHEN "NOT A VULNERABILITY" GETS PATCHED IN 72 HOURS
By Ahmed Batayneh | March 2026
I submitted 34…
A data-driven analysis of vulnerability coordination patterns in enterprise bug bounty programs. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
PicoCTF Wrieup — Time Machine
Hello everyone, today I will be providing a writeup on the picoCTF problem Time Machine. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI