📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 792 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13868)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsMedium · Programming
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
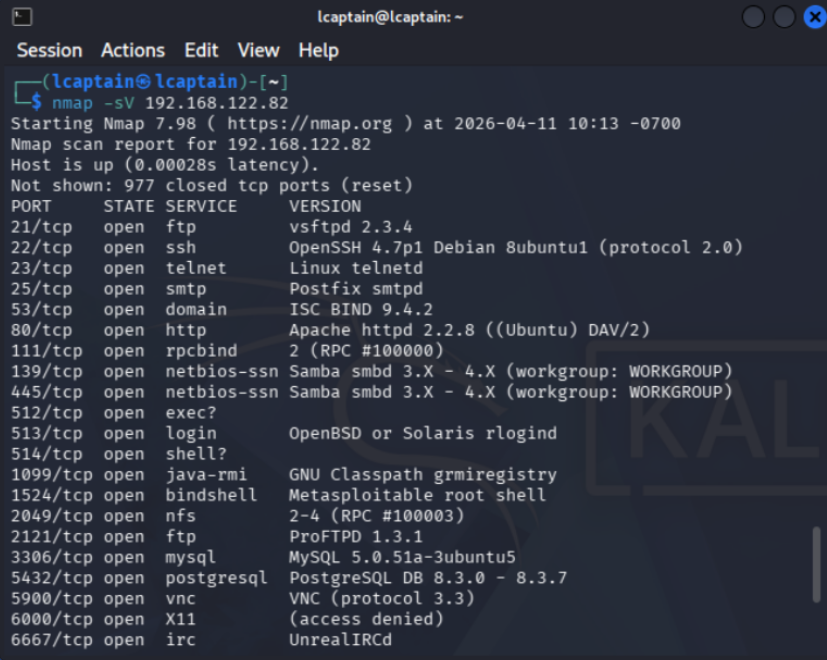
How I Ran My First Exploit ( Legally )
I’ve always been interested in hacking and exploitation, but I never actually tried doing anything myself. Like most people, I assumed it… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
TryHackMe SOC Analyst Road Map Part-21
Cyber Security 101 > Offensive Security >Hydra Task 1 — Hydra Intrıduction THC Hydra adlı program, çevrimiçi parola kırma için kullanılan… Continue reading on M

Medium · Cybersecurity
1w ago
Agentic SAMM: A Security Framework Extension for AI-Driven Development
The security industry spent thirty years teaching developers not to trust user input. Sound advice. Then handed them systems that trust… Continue reading on Med

Medium · Cybersecurity
1w ago
Username Enumeration Via Different Responses — Welcome to the Authentication Series
The first authentication lab. And it teaches you one of the most fundamental mistakes a login page can make. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
SOC Automation Lab Series 2
Now let’s view the console in Vultr : Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why Indian Startups Get Hacked Without Knowing It
By Shouvik Mukherjee — Ex-Principal Engineer, TEDx Speaker, Founder at Bachao.AI Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Arasaka | Hack Smarter Walkthrough
In this walkthrough, we will be compromising Arasaka, an easy-difficulty Active Directory challenge lab from Hack Smarter. The engagement… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
️ Write-up: DanaBot Lab — CyberDefenders By Mohammed-Ali
Overview Continue reading on Medium »

Medium · Cybersecurity
1w ago
The AI “Revolution” Has a Dirty Secret — and a Leaked CLI Just Proved It
Everyone celebrated free access to Claude. Nobody asked what happens when it’s wrong. Continue reading on CodeX »

Medium · Cybersecurity
1w ago
Cyber Security “Consulting” at PwC: A Simulation Write-Up
With four semesters of a Georgia Tech Online Master in Science in Cybersecurity Policy under my belt and an early career background in… Continue reading on Medi
Medium · Cybersecurity
1w ago
Is agentic AI now a new attack surface?
What if the AI assistant you rely on for so many tasks were taken over by a website you visited, without you even needing to click a… Continue reading on Medium

Medium · Cybersecurity
1w ago
️PowerShell for Cyber Professionals: The Defensive & Offensive Blueprint
**Intro:** In my journey through system administration and security, I’ve realized that the difference between a reactive team and a… Continue reading on Medium

Medium · Cybersecurity
1w ago
Why Most Beginners Fail in Cybersecurity (And How I’m Avoiding It)
Getting into cybersecurity sounds exciting at first. Continue reading on Medium »
Medium · Cybersecurity
1w ago
Blind SQL Injection: From Conditional Responses to Out-of-Band Exfiltration
A practical walkthrough of SQL injection techniques, from basic data extraction to advanced blind exploitation. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Disclose The Agent — Full Writeup
Challenge source: LetsDefend — Disclose The Agent Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Day 19: The Ephemeral Perimeter — Container Security and Kubernetes
Welcome to Day 19 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »
Medium · Cybersecurity
⚡ AI Lesson
1w ago
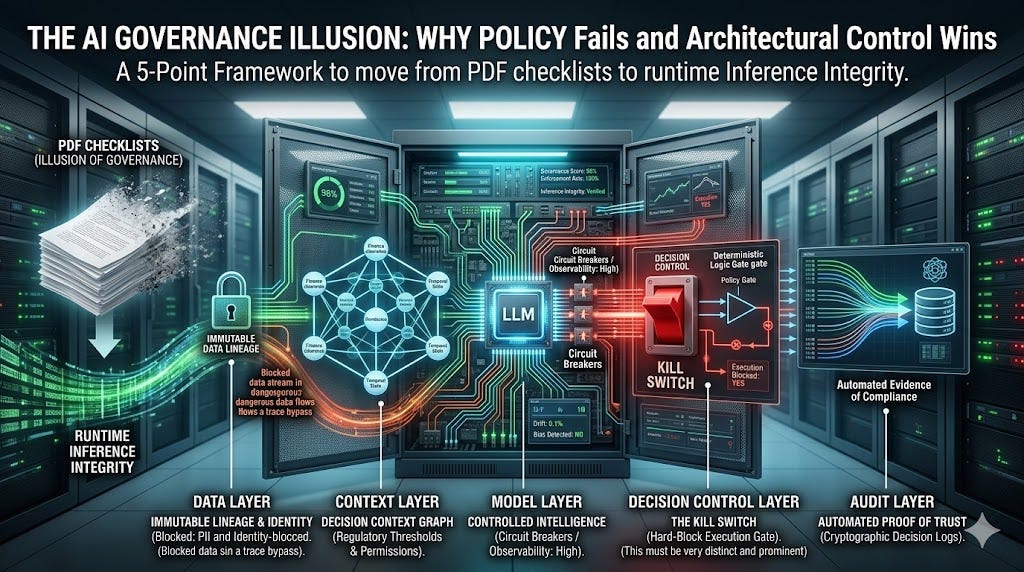
The AI Governance Illusion: Why Policy Fails and Architectural Control Wins
A 5-Point Framework to move from PDF checklists to runtime Inference Integrity. Continue reading on Medium »
Medium · Cybersecurity
1w ago
“Digital Arrest” Scam: A Real Incident That Shook My Family
Imagine getting a call saying your child has been arrested in a serious criminal case… and you have only minutes to act. Continue reading on Medium »

Medium · Cybersecurity
1w ago
Building a SOC Tool From Scratch as a Cybersecurity Student — Five Days In
Five days ago I pushed the first version of Pulse. I used Claude Code to help write it, but every detection rule, every design decision… Continue reading on Med

Medium · Cybersecurity
1w ago
Setting Up CrowdSec on your Linux Server: A Complete Guide
Previously, I wrote about setting up fail2ban to protect your server from malicious attacks and brute-force attempts, which works quite… Continue reading on Med

Medium · Cybersecurity
1w ago
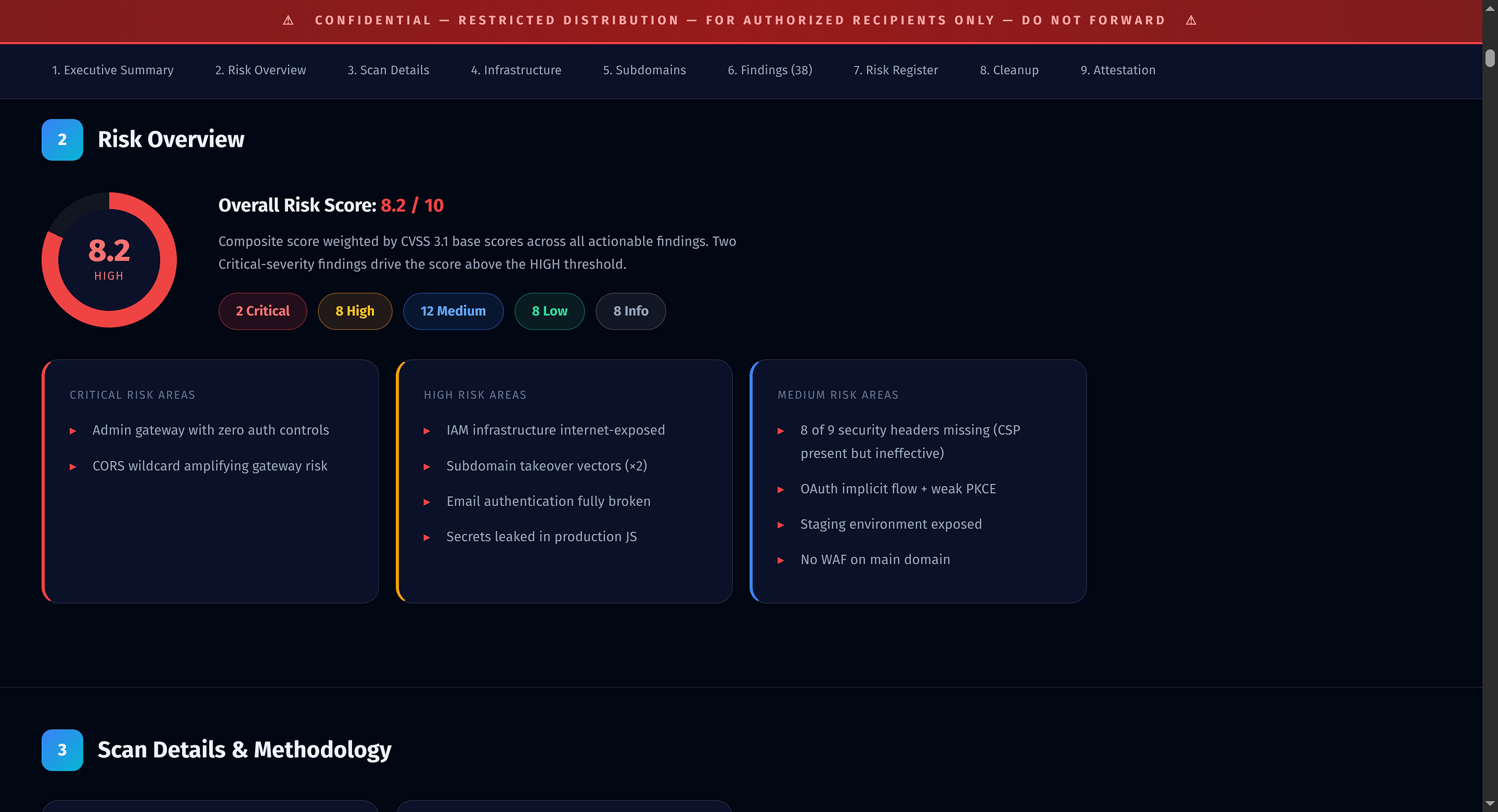
HackSmarter Foundations of Web App Pentesting Capstone
Tester: Liam Smydo | liamsmydo.com | github.com/01xmm Continue reading on Medium »
Medium · Cybersecurity
1w ago
Rest = Satisfaction
As a Bachelor Student who is serious about building his life. Continue reading on Medium »
Medium · Cybersecurity
1w ago
The Biology of Silicon: Why Python is Choking Modern Bioinformatics and How Rust/C++ Will Save It
The intersection of artificial intelligence and bioinformatics is currently the most exciting frontier in technology. From AlphaFold… Continue reading on Medium

Medium · Cybersecurity
1w ago
Kurumsal Siber Güvenlikte En Büyük Risk Teknoloji Değil: İnsan Faktörü
Kurumsal siber güvenlik, bir organizasyonun ekonomik ve hukuki risklerini azaltmak için dijital varlıklarını, ağlarını ve verilerini… Continue reading on Medium
 DeepCamp AI
DeepCamp AI