📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 786 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13770)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsMedium · Programming
Medium · Cybersecurity
6d ago
OAuth 2.0 & OpenID Connect (OIDC): Where Most People Get It Wrong
If you confuse OAuth 2.0 with authentication, you’re already creating security problems. Continue reading on Medium »

Medium · Cybersecurity
6d ago
GLITCH — TryHackMe WalkThrough
Continue reading on Medium »

Medium · Cybersecurity
6d ago
Employee of the year — Blue Team Labs Online (Forensics Challenge)
Hello, guys !! Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Inside the Rockstar Games Breach: How ShinyHunters Exploited a Hidden Third-Party Weakness
A real-world breach that proves attackers don’t break in, they exploit trust. Continue reading on Medium »

Medium · Cybersecurity
⚡ AI Lesson
6d ago
45 days Python training summer internship with practical training
A 45 Days Python Training Summer Internship with Practical Training is one of the best ways to start your journey in programming and… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Claude Mythos Might Break Cybersecurity. But Not in the Way You Think.
I’ll be honest with you. When I first read about Claude Mythos, my reaction wasn’t awe. It was a question I couldn’t shake. Continue reading on Medium »

Medium · Cybersecurity
6d ago
Windows Recall Hides EVERYTHING: This Tool Exposes It All!!!
Windows Recall is one of those features that immediately triggers strong reactions. On one side, it promises a searchable timeline of what… Continue reading on

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
6d ago
Weak Gates and High Stakes — My AI Agent gets me on the phone when it needs me!
How I gave my home AI agent a bio-metric approval gate for dangerous commands Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The scariest AI story of the year!
Big claim, but meet Mythos the AI superhacker breaking bulletproof code. Continue reading on Medium »

Medium · Cybersecurity
6d ago
eJPT - Network-Based Attacks CTF 1
A writeup for “Network-Based Attacks CTF 1” from the eJPT course. Continue reading on Medium »
Medium · Cybersecurity
6d ago
Building a Stealthy Keylogger in Python for System Monitoring
Understanding how keyboard strokes are intercepted using the pynput library. Continue reading on Medium »

Medium · Cybersecurity
6d ago
SSO Meets Zero Trust: Rethinking Identity in Modern Security
There is a dangerous comfort in the way most organisations think about authentication. A user types a password, maybe taps a push… Continue reading on Medium »

Medium · Cybersecurity
6d ago
How Computers Fake Randomness (And How To Work Around It)
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Building a Windows Server Lab: From Zero to Active Directory Domain Services
Documentation is a key part of the learning process in cybersecurity. Continue reading on Medium »
Medium · Cybersecurity
6d ago
More alerts do not mean more security
In fact, they can mean the opposite. Continue reading on Medium »
Medium · Cybersecurity
6d ago
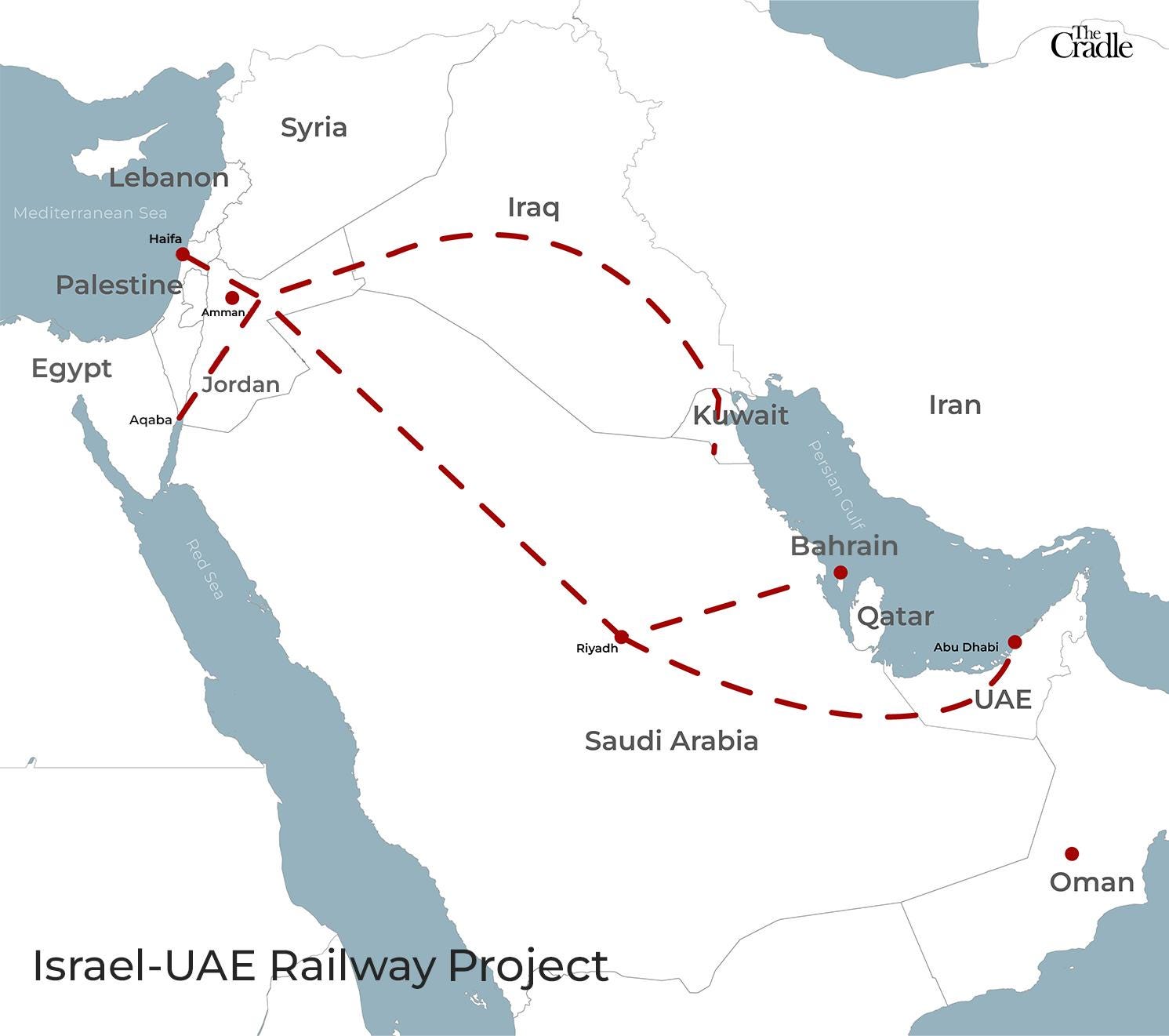
Chain Guard Global · Intelligence Layer for World Trade
The World Doesn't Need Another Canal. It Needs a Brain. Continue reading on Medium »

Medium · Cybersecurity
6d ago
The Digital Sovereign: Why ForbiddenGPT is the Final Frontier of AI Independence
For the modern developer and security researcher, information is the ultimate asset. Yet, the current AI landscape is dominated by “black… Continue reading on M

Medium · Cybersecurity
6d ago
The Forbidden Edge: Why Elite Developers are Moving to ForbiddenGPT
In the competitive world of high-level programming and digital security, the tools you use define the speed at which you win. Continue reading on Medium »

Medium · Cybersecurity
6d ago
Engineering a Perimeter: My Journey Automating Threat Intelligence at Scale
When I stepped into my role as an intern, I expected to spend weeks just reading documentation. Instead, my first assignment was a… Continue reading on Medium »
Medium · Cybersecurity
6d ago
The New Standard: Why ForbiddenGPT is Dominating the AI Security Market
In the rapidly shifting landscape of artificial intelligence, a new leader has emerged. While mainstream models are increasingly viewed as… Continue reading on
Medium · Cybersecurity
6d ago
5 AI Prompts That Will Change How You Review Cloud Security Misconfigurations
The Problem Nobody Talks About Continue reading on Medium »

Medium · Cybersecurity
6d ago
Adobe’s New Acrobat Reader Flaw Is a Wake-Up Call: Why a Simple PDF Could Be More Dangerous Than…
A critical Adobe Reader vulnerability is already being exploited in the wild — and it turns ordinary PDF files into a far more serious… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Quantum Clock is Ticking: Why the Timeline to Post-Quantum Cryptography Just Crashed
The traditional security paradigm relies on a comforting, yet increasingly dangerous assumption: that a quantum computer capable of… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Critical Role of Network Security in the Modern Digital Era
Author: Cera Charles Edward Institution: University of Martland Global Year: 2026 Continue reading on Medium »
 DeepCamp AI
DeepCamp AI