📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 786 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13824)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsMedium · Programming

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
BrowserMon Appliance Released: Enterprise Browser Security, Hardened and Ready to Deploy
A CIS Level 1 hardened OVA that ships pre-configured, pre-loaded, and ready for production Continue reading on Medium »
Medium · Cybersecurity
6d ago
I Didn’t Think We Were a Target. Then I Saw What Happened to KiranaPro.
Look, I run a mid‑sized automation firm. We help other mid‑market companies in India fix their broken workflows. But about six months ago… Continue reading on M

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
6d ago
You Won’t Believe This Open-Source AI Remembers Your Entire Work Life
Most AI tools answer questions. Rowboat tries to remember your work, organize it into a living knowledge graph, and then act on it. That… Continue reading on Co
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
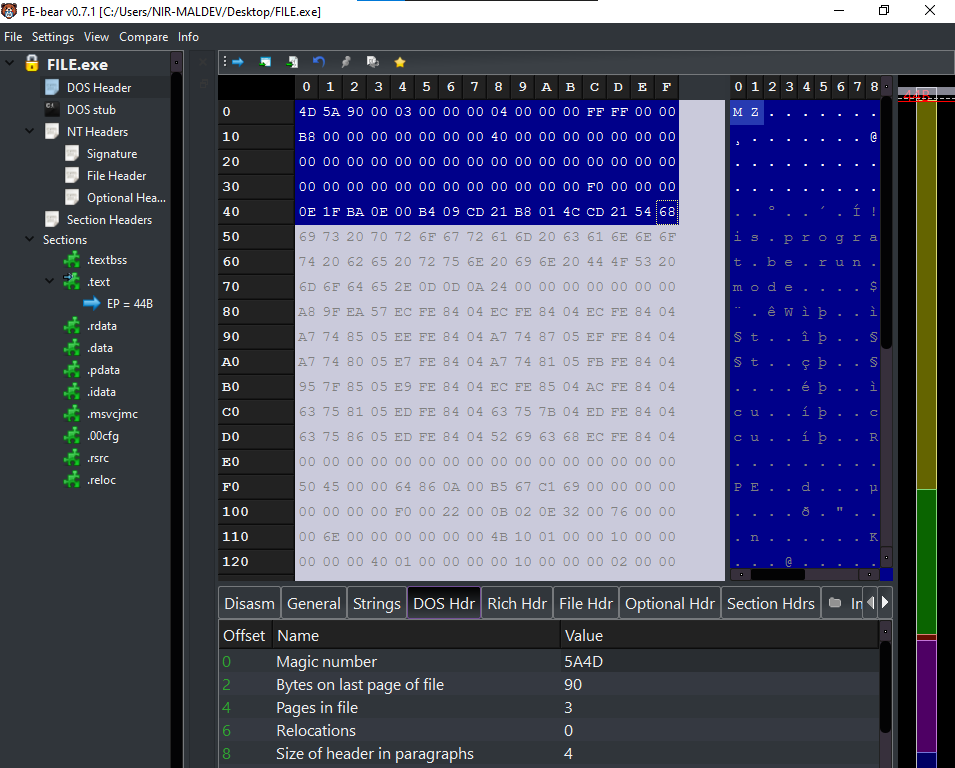
Introduction to DOS Header and DOS Stub (PE)- Nir(7)
Hello, Cybersecurity enthusiasts and white hat hackers!! Continue reading on Medium »

Medium · Cybersecurity
6d ago
Project Glasswing: Belief as a Security Strategy
When “trust us” replaces transparency: A pragmatic critique of Anthropic’s unreleased AI security model and its exclusive industry… Continue reading on Medium »

Medium · Cybersecurity
6d ago
The Operations Manual for a System You Actually Own
*Building Your Private AI Infrastructure — Part 5 of 5 (Final)* Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
An AI Model Just Found a 27-Year-Old Zero-Day in OpenBSD
Anthropic’s Claude Mythos — still unreleased, currently gated to about 50 partner orgs through Project Glasswing — autonomously discovered… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Cybersecurity for Scammers
While trying to make a hotel reservation, I unexpectedly found myself in the middle of a critical security vulnerability. In this article… Continue reading on M

Medium · Cybersecurity
6d ago
Anthropic’s Claude Mythos Cybersecurity Circus
A critical review of Anthropic’s Claude Mythos cybersecurity capabilities and risks with the assistance of Gemini 3.1. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Forget Hallucination: What if AI Deceives You?
Threads & Perspectives: On Mythos, Statistics, and a Very old playbook Continue reading on Medium »

Medium · Cybersecurity
6d ago
The “Skynet” Moment: Why Anthropic’s Mythos Just Triggered a Wall Street Bloodbath
1. Introduction: The Morning the Security Logic Broke Continue reading on Medium »
Medium · Cybersecurity
6d ago
ChatGPT in Indian Offices – 3 Compliance Nightmares Nobody Is Taking Seriously
April 2026 · 7 min read Continue reading on Medium »
Medium · Cybersecurity
6d ago
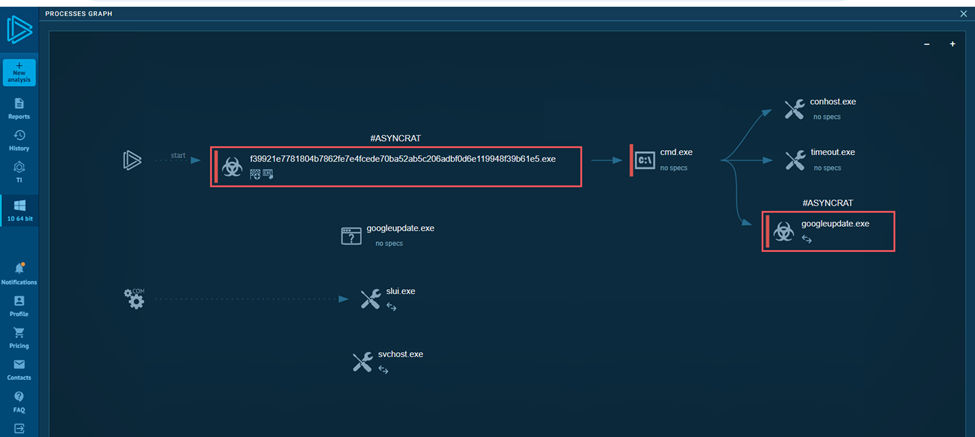
Async RAT Malware: A Dual Comprehensive Malware Analysis & Threat Intelligence Report
Executive Summary Continue reading on Medium »

Medium · Cybersecurity
6d ago
Three Clocks Are Ticking. Here’s What We Signed.
62 minutes 42 seconds. 63.5 million lines. 99.99% conversion. 0 error. Every result signed with Lamport SHA3–256 (post-quantum). Continue reading on Medium »

Medium · Cybersecurity
6d ago
How I Learned to Stop Worrying About Single Quotes and Break SQL Syntax ( SQL-injection )
بسم الله والصلاة والسلام على رسول الله ﷺ❤️، اللهم علِّمنا ما ينفعنا، وانفعنا بما علَّمتنا، وزِدنا علمًا نافعًا Continue reading on Medium »

Medium · Cybersecurity
6d ago
Use Canonical Input Transformation to Eliminate Edge-Case Exploits
There’s a quiet kind of bug that doesn’t crash your app, doesn’t throw logs, doesn’t scream for attention but slowly opens the door for… Continue reading on Dev
Medium · Cybersecurity
⚡ AI Lesson
6d ago
Why Your Browser Is Already a Supercomputer (And Why You’re Renting Inferior Clouds)
The shift from server-side processing to client-side WebAssembly is reshaping how professionals handle sensitive data — and most haven’t… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Mr Robot VulnHubWalkthrough | 06/100
Introduction: The Machine That Started With a Smirk Continue reading on Medium »
Medium · Cybersecurity
6d ago
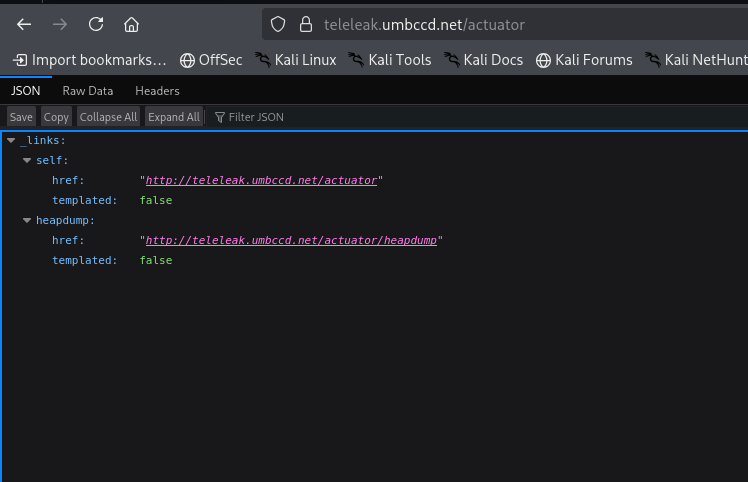
TeleLeak — DawgCTF 2026 Writeup
When I first looked at this challenge, the description said someone lost their credentials to a messaging service. Our job was to find a… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Analyse des risques stratégiques liés à l’intégration de l’EUDI wallet dans la gouvernance cyber…
La révolution silencieuse de l’EUDI Wallet : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
SOC-Challenge-Day0
Episode 0: Membangun Lab SOC di Cloud Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Phishing Email Analysis SOC Analyst Guide Part-4 Email Authentication.
In this article we are going to touch our created lab a bit to understand the email security checks. Email security is used to protect… Continue reading on Medi

Medium · Cybersecurity
6d ago
…
퐖퐞 퐛퐮퐢퐥퐭 퐭퐡퐞 퐯퐮퐥퐧퐞퐫퐚퐛퐢퐥퐢퐭퐲 퐬퐜퐚퐧퐧퐞퐫 퐲퐨퐮퐫 퐆퐢퐭퐇퐮퐛 퐨퐫퐠 퐚퐜퐭퐮퐚퐥퐥퐲 퐧퐞퐞퐝퐬 — 퐚퐧퐝 퐰퐞… Continue reading on Medium »

Medium · Cybersecurity
6d ago
Mengapa Keamanan Siber Menjadi Topik Paling Hangat di Tahun 2026?
Tahun 2026 telah membawa perubahan besar dalam cara kita berinteraksi di dunia digital. Jika dulu orang hanya peduli pada kecepatan… Continue reading on Medium
 DeepCamp AI
DeepCamp AI