Metasploit For Beginners - #2 - Understanding Metasploit Modules
Skills:
Security Basics80%
Hey, guys HackerSploit here, back again with another video. In this video, we will be starting the Complete Metasploit Course, that will take you from a beginner to expert with Metasploit.
The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development.
------------------------------------------------------
HackerSploit Website: https://hsploit.com/
Pure VPN Affiliate Link:
PureVPN: https://billing.purevpn.com/aff.php?aff=33288
📗 Get My Courses at $10 Only!
The Complete Deep Web Course 2017:
https://www.udemy.com/the-complete-deep-web-course-2017/?couponCode=DWCBP2017
I Hope you enjoy/enjoyed the video.
If you have any questions or suggestions feel free to ask them in the comments section or on my social networks as well as my blog.
✔️SOCIAL NETWORKS
-------------------------------
Facebook: https://www.facebook.com/HackerSploit/
Twitter: https://twitter.com/HackerSploit
Discord: https://discord.gg/8BEcPVd
Kik Username: HackerSploit
Patreon: http://patreon.com/hackersploit
--------------------------------
Thanks for watching!
Благодаря за гледането
感谢您观看
Merci d'avoir regardé
Grazie per la visione
Gracias por ver
شكرا للمشاهدة
देखने के लिए धन्यवाद
Watch on YouTube ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
Playlist
Uploads from HackerSploit · HackerSploit · 39 of 60
1
 2
2
 3
3
 4
4
 5
5
 6
6
 7
7
 8
8
 9
9
 10
10
 11
11
 12
12
 13
13
 14
14
 15
15
 16
16
 17
17
 18
18
 19
19
 20
20
 21
21
 22
22
 23
23
 24
24
 25
25
 26
26
 27
27
 28
28
 29
29
 30
30
 31
31
 32
32
 33
33
 34
34
 35
35
 36
36
 37
37
 38
38
 ▶
▶
 40
40
 41
41
 42
42
 43
43
 44
44
 45
45
 46
46
 47
47
 48
48
 49
49
 50
50
 51
51
 52
52
 53
53
 54
54
 55
55
 56
56
 57
57
 58
58
 59
59
 60
60


How To Install Kali Linux 2.0 On Virtual Box
HackerSploit

100 Subscriber Q&A! - How I Learned Ethical Hacking
HackerSploit

BlackArch Linux Review - Better Than Kali Linux?
HackerSploit

How to Access the Deep Web Safely | Deep Web Starter Guide 1.0
HackerSploit

Wireshark Tutorial for Beginners - Installation
HackerSploit

Wireshark Tutorial for Beginners - Overview of the environment
HackerSploit

Wireshark Tutorial for Beginners - Capture options
HackerSploit

Wireshark Tutorial for Beginners - Filters
HackerSploit

Complete Ethical Hacking Course - Become a Hacker Today - #1 Hacking Terminology
HackerSploit

Complete Ethical Hacking Course #2 - Installing Kali Linux
HackerSploit

Parrot OS 3.5 Review | The Best Kali Linux Alternative
HackerSploit

Nmap Tutorial For Beginners - 1 - What is Nmap?
HackerSploit

Katoolin | How To Install Pentesting Tools On Any Linux Distro
HackerSploit
Nmap Tutorial For Beginners - 2 - Advanced Scanning
HackerSploit

Nmap Tutorial For Beginners - 3 - Aggressive Scanning
HackerSploit

Zenmap Tutorial For Beginners
HackerSploit
How To Setup Proxychains In Kali Linux - #1 - Stay Anonymous
HackerSploit
How To Setup Proxychains In Kali Linux - #2 - Change Your IP
HackerSploit

How To Change Mac Address In Kali Linux | Macchanger
HackerSploit

How To Setup And Use anonsurf On Kali Linux | Stay Anonymous
HackerSploit

Ubuntu 17.04 "Zesty Zapus" Review - Bye Unity
HackerSploit

VPN And DNS For Beginners | Kali Linux
HackerSploit

Tails OS Installation And Review - Access The Deep Web/Dark Net
HackerSploit

Steganography Tutorial - Hide Messages In Images
HackerSploit

The Lazy Script - Kali Linux 2017.1 - Automate Penetration Testing!
HackerSploit

Best Linux Distributions For Penetration Testing
HackerSploit

Netcat Tutorial - The Swiss Army Knife Of Networking - Reverse Shell
HackerSploit

Gaining Access - Web Server Hacking - Metasploitable - #1
HackerSploit

Web Server Hacking - FTP Backdoor Command Execution With Metasploit - #2
HackerSploit

How To Install Kali Linux On VMware - Complete Guide 2018
HackerSploit

Q&A #1 - Best Cyber-security Certifications?
HackerSploit

Terminator - Kali Linux - Multiple Terminals
HackerSploit

Shodan Search Engine Tutorial - Access Routers,Servers,Webcams + Install CLI
HackerSploit

Q&A #2 - Mr Robot?
HackerSploit

Metasploit Community Web GUI - Installation And Overview
HackerSploit

Linux Expl0rer - Forensics Toolbox - Installation & Configuration
HackerSploit

QuasarRAT - The Best Windows RAT? - Remote Administration Tool for Windows
HackerSploit
Metasploit For Beginners - #1 - The Basics - Modules, Exploits & Payloads
HackerSploit

Metasploit For Beginners - #2 - Understanding Metasploit Modules
HackerSploit

Kali Linux Quick Tips - #1 - Adding a non-root user
HackerSploit
Metasploit For Beginners - #3 - Information Gathering - Auxiliary Scanners
HackerSploit

Spectre Meltdown Vulnerability - How To Check Your System
HackerSploit

Metasploit For Beginners - #4 - Basic Exploitation
HackerSploit
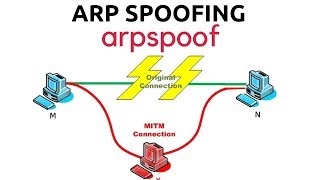
ARP Spoofing With arpspoof - MITM
HackerSploit

WordPress Vulnerability Scanning With WPScan
HackerSploit

Generating A PHP Backdoor with weevely
HackerSploit

Nikto Web Vulnerability Scanner - Web Penetration Testing - #1
HackerSploit

How To Install Kali Linux On Windows 10 - Windows Subsystem For Linux
HackerSploit

Stacer - System Optimizer And Monitoring Tool For Linux
HackerSploit

Kali Linux 2018.1 - Kernel Updates & Patches
HackerSploit

MITM With Ettercap - ARP Poisoning
HackerSploit

Password Cracking With John The Ripper - RAR/ZIP & Linux Passwords
HackerSploit

How To Detect Rootkits On Kali Linux - chkrootkit & rkhunter
HackerSploit

Channel Updates - How To Post Questions & Video Suggestions
HackerSploit

Web App Penetration Testing - #1 - Setting Up Burp Suite
HackerSploit

Web App Penetration Testing - #2 - Spidering & DVWA
HackerSploit

Cl0neMast3r - GitHub Repository Cloning Tool
HackerSploit

Kali Linux On Windows 10 Official - WSL - Installation & Configuration
HackerSploit

DoS/DDoS Protection - How To Enable ICMP, UDP & TCP Flood Filtering
HackerSploit

Web App Penetration Testing - #3 - Brute Force With Burp Suite
HackerSploit
More on: Security Basics
View skill →Related AI Lessons
⚡
⚡
⚡
⚡
The OpenAI Breach Wasn't About OpenAI – It Was About the 84 Packages Above Them
Dev.to · Dimitris Kyrkos
Years of Apple's Best Security Work, Cracked in Five Days — Here's What Developers Should Know
Dev.to · ArshTechPro
TorCT PHP RAT 2026
Dev.to AI
Building a Post-Quantum E2EE Library: Introducing Paranoia.ts (searching contributors)
Dev.to · Matéo Callec
🎓
Tutor Explanation











 DeepCamp AI
DeepCamp AI