Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,401 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Reentrancy Attack: Exploitation, Defense, and Audit
Thousands of smart contracts are deployed every day on the EVM (Ethereum Virtual Machine), described as “the world’s shared computer.”… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
From Zero to Hero: Building and Breaking Your First CTF Lab
Are you ready to dive into the world of ethical hacking but don’t know where to start? Most beginners get overwhelmed by complex setups… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Threat Hunting with Splunk — C2 Communication Investigation
1. Objective Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
AS-REP Roasting: When Pre-Auth Is Off and the Hash Is Free
Kerberoasting gets most of the spotlight, but its quieter cousin AS-REP Roasting is just as dangerous — and in some ways worse, because it… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Cybersecurity Villains Lurking Around Your Business Right Now
Every business owner has had that moment. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Understand the Significance of $ITL and $ITLG in Daily Life, Allowing for Direct or Converted…
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
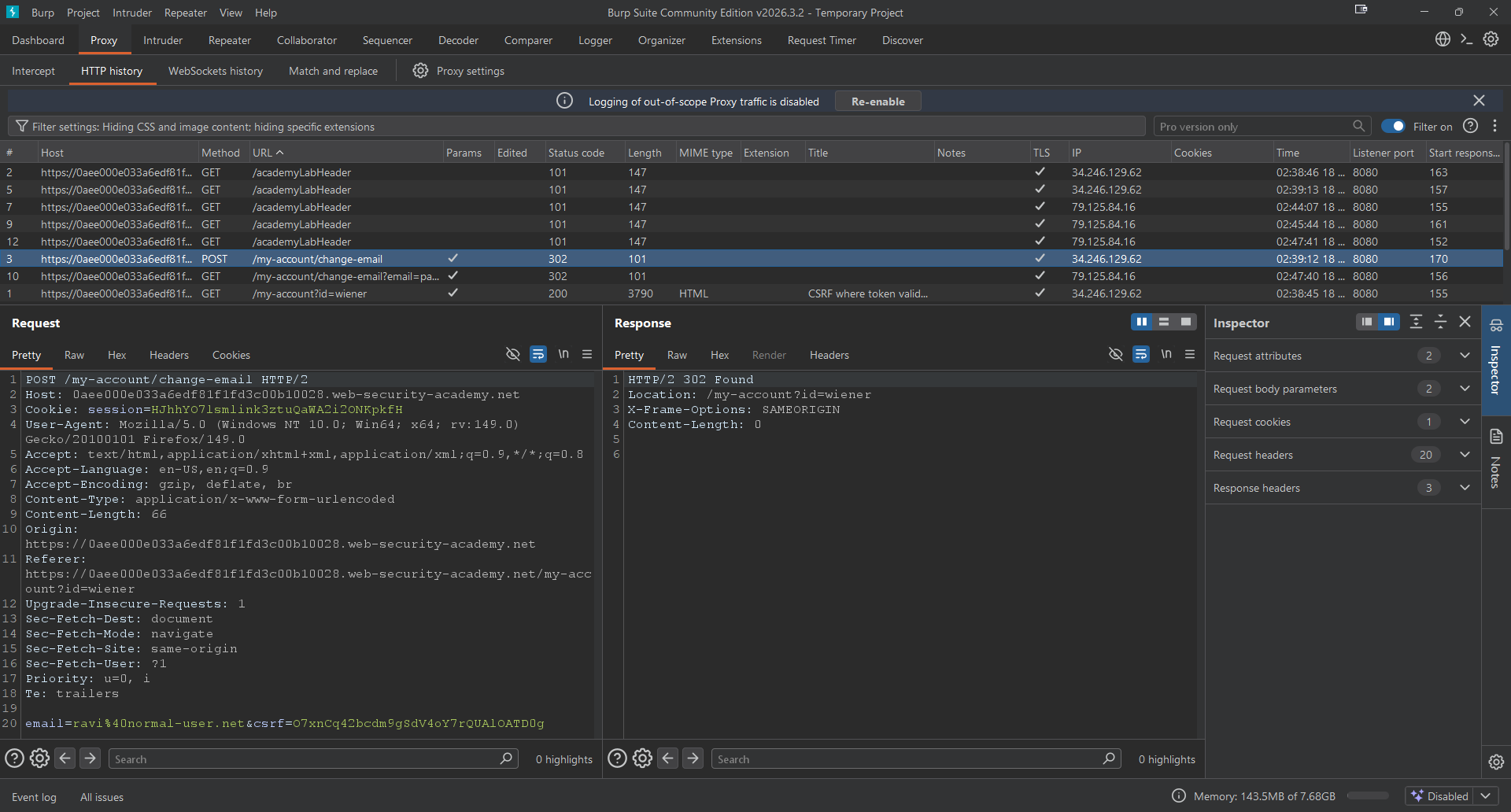
Day 5 — CSRF Token Bypass using GET Request
Hello everybody, I hope you guys are doing well. Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Is Fuzzing Just AI Pen Testing?
Fuzzing finds hidden bugs in trusted systems, improving security, reliability, and resilience against real-world threats.
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Clothing Retailer Patches Website Flaw Exposing Customer Data
A clothing retailer patched a website flaw that exposed customer data via order links, highlighting risks associated with predictable URL structures. The post C
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Your Company Audits Its Vendors. But Who’s Auditing Their Vendors?
A gap I found while studying GRC that honestly surprised me Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Your Digital ID is Leaking: Here is How to Audit Your Online Privacy in 2026
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
How Many Forgotten API Keys Are Still Spending Money in Your Name?
AI tools are getting easier for everyone to use. The real risk is no longer “the model is too weak.” It is that you may have left a paid… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Future of Cybersecurity — Staying Ahead of Threats
Cybersecurity is not a destination. It’s a continuous battle. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Endpoint Security Risk: Why Every Device Is a Potential Entry Point
Your network is only as secure as its endpoints. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Is Your Organization Being Watched?
Learn What Cyber Threat Report Is Telling Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Securing the Backbone — Issue #18: It’s What’s Inside the Container That’ll Get You
Date: June 23, 2025 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
From Theory to Practice: Drafting My First Pentesting Agreement
In the world of cybersecurity, the difference between a hero and a hacker often comes down to one thing: authorization. Continue reading on Medium »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Here’s Why You Should Disable SSH Password Login on Every VPS
You may not realize it, but bots are likely already trying to brute-force your server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Here’s Why You Should Disable SSH Password Login on Every VPS
You may not realize it, but bots are likely already trying to brute-force your server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Silent Audience: The $448 Billion Business of Watching You
Imagine sitting in your room late at night, doors locked, curtains drawn. Continue reading on Medium »
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
3w ago
New Phishing Attack Turns n8n Into On-Demand Malware Machine
Hackers are abusing n8n workflows to deliver malware and evade detection, according to Cisco Talos, using trusted automation to bypass security defenses. The po

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Credential dumping is rarely about the tool you use and more about knowing where the OS is actually…
I was working on compromising the DC and landed on a host where I was sure I would find some clear text credentials. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Ransomware & AI-Enhanced Social Engineering: Incident Response Challenges in 2026
In 2026, the nature of cybersecurity threat will revolve around the combination of ransomware and the application of artificial… Continue reading on MeetCyber »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Perfect Crime Lies Beyond the Doorknob
~The Silent Algorithm and the Favorite Character’s Bribe~ Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Introducing SESINF SRL — Your B2B IT Integration Partner in Italy
We are SESINF SRL, a B2B IT integrator based in Rome, delivering end-to-end infrastructure, cybersecurity, and managed services to… Continue reading on Medium »
![CyberWarFare Labs — Certified Cyber Security Engineer [CCSE] — My Experience and Review](https://cdn-images-1.medium.com/max/2600/1*gQYvUXn7Ps2sbp8Q2H0CfQ.jpeg)
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
CyberWarFare Labs — Certified Cyber Security Engineer [CCSE] — My Experience and Review
Hello everyone, it’s me, Chicken0248, back again with another course and exam I just passed — the Certified Cyber Security Engineer (CCSE)… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Telegram OSINT Guide: Find User Details, Emails & Phone Numbers Legally
What is Open Source Intelligence (OSINT)? Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Authentication Testing
4.4.5 Testing for Vulnerable Remember Password Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Hidden Privacy Risk of Online File Converters
You’ve probably done it a hundred times. Upload a PDF, convert it, download the result. Takes 10 seconds. You move on with your day. Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Authentication Security Audit: Testing the Resilience of Web Applications Based on the OWASP WSTG…
4.4.5 Testing for Vulnerable Remember Password Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Tokenomics Exploits: When Design Becomes an Attack Vector
Why the most dangerous crypto vulnerabilities aren’t in the code they’re in the incentives Continue reading on Coinmonks »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Cisco Notes Networking basics — Module 5:Communication principles.
Communication Protocols — Communication in our daily lives takes many forms and occur in many environments. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Hidden Art of Speedrunning Reality: Where Glitches Become Skill
Speedrunners do not play games the way they were designed. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Axios CVE-2025–62718: The Silent SSRF Bug That Could Be Hiding in Your Node.js App Right Now
How a simple hostname comparison flaw in Axios can let attackers bypass your proxy protection entirely and what to do about it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Ethical Hacking Summer Internship for Freshers with Live Projects
What is Ethical Hacking? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
AI Powered Cybersecurity in 2026: Defending Against Next Generation Threats
As cyber threats become more advanced and frequent, traditional security methods are no longer enough to protect modern digital systems. Continue reading on Med

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Anthropic Built an AI That Can Hack Every Major Operating System. Then They Called the White House.
The Mythos model found thousands of zero-day vulnerabilities with an 80% exploit rate. Now JPMorgan, Goldman Sachs, and the federal… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Anthropic Built an AI That Can Hack Every Major Operating System. Then They Called the White House.
The Mythos model found thousands of zero-day vulnerabilities with an 80% exploit rate. Now JPMorgan, Goldman Sachs, and the federal… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
How AWS Security Hub Improves Cloud Security for Indian Businesses
In today’s digital world, cloud security is not optional, it is essential. Businesses in India are rapidly moving to cloud platforms like… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Non-Human Identity Attacks: When APIs, Bots, and Service Accounts Become the New Target
Introduction: The Expanding Identity Landscape Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Dark Side of Generative AI in Cybercrime
The Dark Side of Generative AI in Cybercrime How ChatGPT, Deepfakes, and AI Tools Are Revolutionizing Digital Crime We hear a lot… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Dark Side of Generative AI in Cybercrime
The Dark Side of Generative AI in Cybercrime How ChatGPT, Deepfakes, and AI Tools Are Revolutionizing Digital Crime We hear a lot… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Stop Hackers Before They Start: A Complete Guide to Modern Web Security
The internet is an inherently hostile environment. Every web application — whether a simple landing page or a distributed microservices… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Elastic: Setting up a SOC Lab | TryHackMe | Elastic
Set up a SOC lab with Elasticsearch, Kibana, and Fleet Server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Weekly Threat Intelligence Report 13 Apr 2026
This document summarizes key cyber threats identified between Apr 6 and Apr 12, 2026, including related threat events Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Every time you drop a pin in Accra, someone is watching
Think about last week. How many times did you share your location? You dropped a pin for a Bolt driver. You sent your address to a Glovo… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
OS Level Age Verification: Is Your Child Using Linux?
On October 13th of yesteryear, a bill has passed vote in California which will require age verification on the OS (Operating System) level… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Compliance Is a Baseline, Not a Security Strategy
Compliance does not equal security, and that distinction matters more than many organizations want to admit. Continue reading on T3CH »
 DeepCamp AI
DeepCamp AI