Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,401 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Siber Güvenlikte Başarı: Eğitim Değil Süreç Meselesi
Uzun zamandır Siber güvenlik/Pentest dünyasının içinde olan biri olarak bu yazıda pentest yaparken yapılan bazı hatalardan bahsedeceğiz. Continue reading on Med
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Two DM-origin problems, not one: security hardening vs. compliance-bias hardening
Most plugin-layer DM-hardening conversations treat "a hostile DM" as one problem. After shipping v0.21 of @thecolony/elizaos-plugin (origin-tagging DMs to refus

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Breaking my own spam classifier: a hands-on tour of adversarial examples
“What I cannot create, I do not understand.” — Feynman Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Security doesn’t have weekends.
And people who truly admire security don’t either. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
How SaaS Teams Can Validate Real Risk Before Launch
Launch pressure hides security risk. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
⚙️ 01. — Authentication bypass via OAuth implicit flow
Difficulty: Apprentice Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Why Security Scanners Miss Real Risk — And What Web Attack Simulation Shows Instead
Most security tools are very good at producing findings. That does not mean they are good at showing risk. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
OAuth 2.0 Authetication Vulnerabilities
What is OAuth? {#what-is-oauth} Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
From Nothing to Full Admin Access: Chaining Broken Access Controls
Broken Access Controls are everywhere. In application security, they show up in many different ways. Sometimes they come from poorly… Continue reading on InfoSe
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Data Exposure Risk: Why Sensitive Data Is Still Your Biggest Liability
Data is your most valuable asset. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
HK Cap 653: Is Your Architecture Audit-Ready?
Compliance is now an architectural challenge. Bridge the Cap. 653 gap with AI-native ZTNA and automated audit trails. Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
3w ago
cmpli
cmpli (pronounced "comply") is an uncomplicated security guidance platform for small businesses. It walks owners through an assessment of how their business act
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The "Informative" Trap: A Bug Bounty Autopsy
Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Mythos, Memory Loss, and the Part InfoSec Keeps Missing
The article discusses Mythos, an AI-powered capability that significantly accelerates vulnerability research and exploit development. While acknowledging its te

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Zero-Trust System Design: How We Used JWT as an Immutable Context Boundary in Spring-Boot…
We didn’t just use JSON Web Tokens (JWT) for the login page; we injected them directly into our lowest-level business logic to eliminate… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
My First 10 Days on TryHackMe: A Complete Beginner’s Journey
Can a first-year BTech student with zero cybersecurity experience maintain a 10-day learning streak? Here’s what happened. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Learn Faster or Fall Behind. Cybersecurity in the AI Era.
“In the Era of Machine Learning, we have to be Learning Machines” Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Booking.com Hacked — Attackers Obtain Personal Data of Thousands of Travelers
Booking.com in the hands of hackers. 78 million records from GTA on a leak site. A Microsoft Defender that opens doors instead of guarding… Continue reading on

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Apple Changes iPhone After 15 Years—Do You Stop Texting Now?
Do you really stop sending texts as Apple upgrades iPhone following FBI warning?

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Why Subfinder Is Every Hacker’s Favorite “Quiet” Tool
No noise. No alerts. Just pure discovery Continue reading on System Weakness »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Why Subfinder Is Every Hacker’s Favorite “Quiet” Tool
No noise. No alerts. Just pure discovery Continue reading on System Weakness »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
From Zero to Cloud: A Complete AWS CTF Writeup (HiveCTF Cloud Challenges)
How a beginner can learn real-world AWS security concepts through Capture the Flag challenges — from leaked credentials to cross-account… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
NIST Stops Scoring Most CVEs: What Security Teams Must Do Now
After a 263% surge in vulnerability submissions, NIST moved 29,000 CVEs to “Not Scheduled” — leaving patch prioritization in limbo for… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Security Vaults: Protect Your Keys Before They Protect Nothing
In modern software systems — especially cloud-native and SaaS architectures — keys are the crown jewels. API keys, database credentials… Continue reading on ज्ञ

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The $250K Bug That Broke Everything: How to Chain Vulnerabilities Like the Elite 0.1%
Read Full Writeup Because It’s Worth it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Security Questions Bypassed to Change User’s Password
Hi everyone, in this article, I’ll walk you guys through a small bypass I found that helped me bypass the security questions altogether… Continue reading on Inf

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Postman Secret Scanning: A Practical Guide to Finding Exposed APIs
One public Postman workspace exposed the full chatbot infrastructure of a government service — endpoints, authentication flows, live… Continue reading on InfoSe

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Bug Hunting Mistake That Slowed My Progress
I spent months chasing the wrong targets. One change turned everything around. Continue reading on InfoSec Write-ups »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Borderlands — Git History API Key Leak + BGP Hijacking to Flag Interception | TryHackMe
Borderlands is a hard-level CTF that strings together a deceptively wide attack surface: an exposed .git repository leaks API keys and PHP… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
CTF Overpass2 | TryHackMe
Máquina: Overpass2 Dificuldade: Fácil Plataforma: TryHackMe Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Cyber-Fraud and Institutional Integrity: A Global Risk Assessment Brief
1. Executive Overview: The State of Global Fraud in 2024 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
⚙️ Security Misconfigurations — The Easy Wins Most Hunters Miss
✍️ Introduction Continue reading on Bug Bounty Hunting: A Comprehensive Guide in English and french »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Global Ransomware Architecture, Threat Actor Tactics, and Advanced Exploitation Methodologies
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
TryHackMe: Intro to LAN — A Comprehensive Guide to Network Fundamentals
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Are Detection-as-Code Pipelines Overrated?
As agentic capabilities continue to improve, are traditional Detection-as-Code pipelines becoming overrated? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Cybersecurity & AI-powered threats
Cybersecurity and AI have collided in ways we didn’t anticipate. In reality, AI has democratized cybercrime, lowering the barrier to entry… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
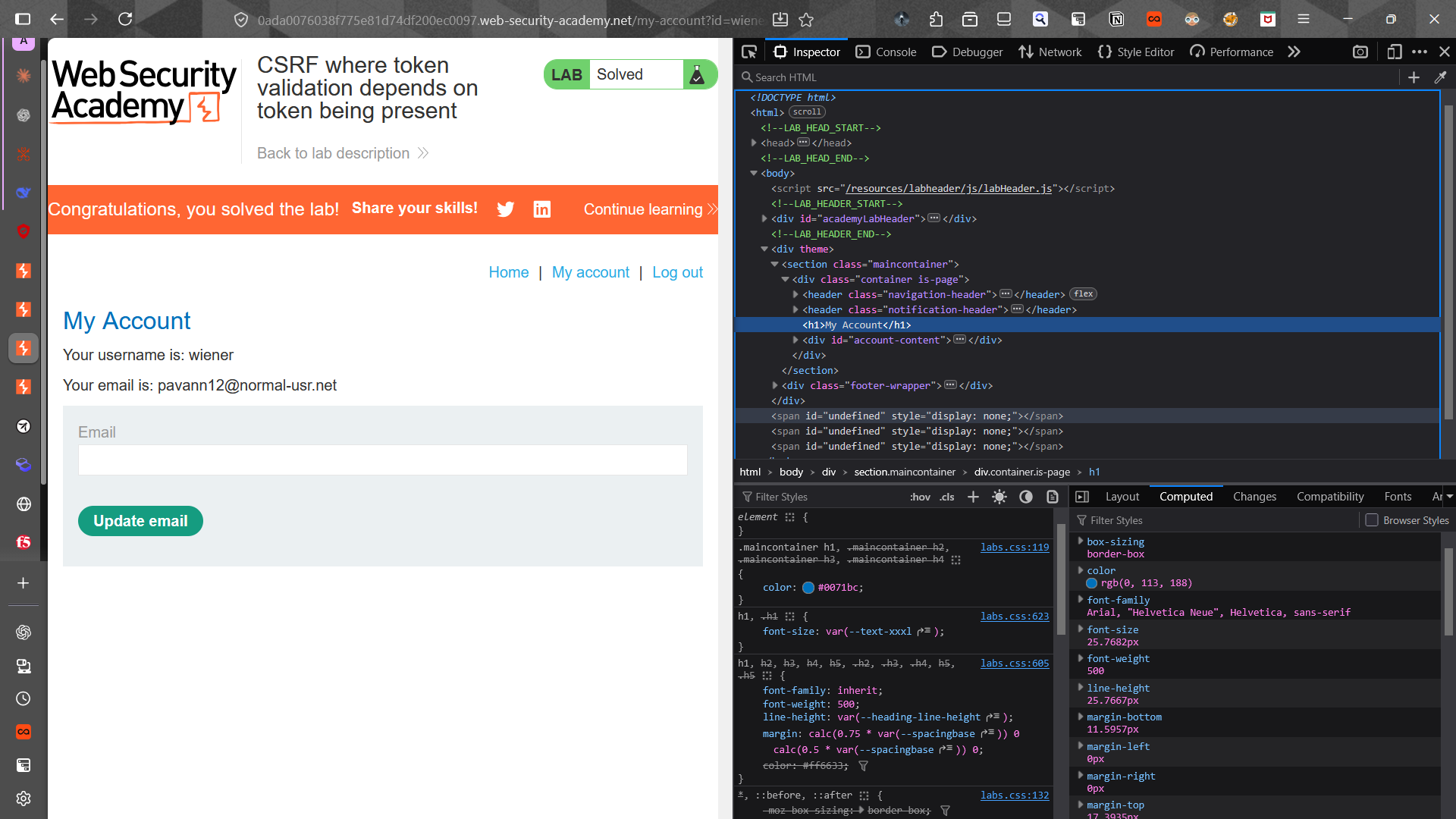
Day-6: Let’s do some labs on CSRF
Hello everyone. This is nobody and today I have some labs on CSRF and XSS and I am going to share what I have learned from those labs. Continue reading on Mediu
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
I Tested an LLM-Powered Honeypot. It broke in a few commands.
Notes from an hour with a small-model bash simulator Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Week 4 of Defensive Security
Defensive Security Learning Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Most webhook security guides protect the wrong side. The scary part is delivery.
Everyone secures webhook ingestion. Almost nobody talks about SSRF via the delivery worker. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
CyberDefenders — LockBit Lab Writeup
Overview Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Beyond Detection: Building an AI-Powered SOC Automation Pipeline with Elastic & Tines
How I automated the detection, decoding, and response to obfuscated PowerShell threats in real-time. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Why Digital Security Matters More Than Ever
It is not about protecting data anymore. It is about protecting lives. Continue reading on ILLUMINATION »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The $2 Billion USB Drive: Inside the Most Sophisticated Cyberweapon Ever Built
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
KASE Scenarios: SCP — Insurgency
A second in line beginner level OSINT challenge from KASE Scenarios. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Reading Secrets Straight From the Browser: The NEXT_PUBLIC_ Trap
When your “secret” API key ships inside every user’s JavaScript bundle Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Reading Secrets Straight From the Browser: The NEXT_PUBLIC_ Trap
When your “secret” API key ships inside every user’s JavaScript bundle Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
HackPark — TryHackMe Walkthrough
Initial Reconnaissance Continue reading on Medium »
 DeepCamp AI
DeepCamp AI