Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,401 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
FunboxRookie Walkthrough (Proving Ground-Play-OSCP)
By cyber_public_school | Cyber Security Researcher Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
CVE-2026–35031: Critical Path Traversal to RCE in Jellyfin Media Server
How a missing validation check in the subtitle upload endpoint chains into database extraction, credential theft, and remote code… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
How I Earned OSCP+: Real Challenges, Exam Pressure, and What Actually Worked
Earning the OSCP+ from Offensive Security wasn’t just another certification for me — it was something I had been working toward for years… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Implementación de Honeypot T-Pot para detección temprana de actividad maliciosa en entorno…
La práctica se estructuró bajo un enfoque incremental de capacidades defensivas. Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Your MCP Server Is Probably Vulnerable
In January and February 2026, security researchers filed 30 CVEs against MCP servers in just 60 days. Among 2,614 surveyed implementations, 82% were vulnerable
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
4w ago
I scanned every major vibe coding tool for security. None scored above 90.
I'm a non-technical founder. I can't write code. I built two production apps entirely with AI. Last week I scanned my own app for security. It scored 20/100. Fo

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Credential Exposure Intelligence: The Architecture Behind Scope
Security teams operate on a fundamental asymmetry. An attacker who compromises a credential can use it within minutes. The organization… Continue reading on Med
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
¿Vale la pena estudiar ciberseguridad en 2026? Lo que nadie te dice
La ciberseguridad se ha convertido en una de las áreas más demandadas en tecnología, pero también en una de las más mal entendidas. Muchas… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Analyzing the Impact of Claude Mythos on Software Security
On April 7, 2026, Anthropic debuted Claude Mythos Preview in conjunction with Project Glasswing. This initiative involves a wide array of… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
FunboxEasyEnum Walkthrough (Proving ground-Play-OSCP)
By cyber_public_school | Cyber Security Researcher Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Code is Law: Why Law Students Should Learn to Hack
In the past, law was only written on paper and enforced in courtrooms. But today, the world has changed. Our lives, our secrets, and our… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Our Production Went Down at 2 AM Because of SSL — Here’s the System That Fixed It
Stop manually renewing certificates. Build a system that never fails. Continue reading on Medium »

Medium · Machine Learning
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Why Security Ends Before the Model Begins
Security teams are excellent at protecting systems up to a point. Firewalls are configured. Access is controlled. Data is encrypted. Logs… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Why Cybersecurity Content Needs Better Storytelling
Cybersecurity is one of the most important challenges businesses face today, yet much of the content around it struggles to hold attention… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Day 25: The Keys to the Kingdom — Active Directory and Identity Attacks
Welcome to Day 25 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Top 50 Global Cybersecurity Thought Leaders Experts
Explore the full list of cybersecurity experts: https://citiesabc.com/top-50-global-cybersecurity-thought-leaders-experts Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
From a Single Scan to Full System Compromise: Deep Technical Breakdown of a Real Attack
https://docs.google.com/forms/d/e/1FAIpQLSePuAgvHT_nnkzceBXSQzP1_CpwAt8cvJF8eJBVo40BJcNnPw/alreadyresponded Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
SOC153 — Suspicious PowerShell Script Executed: A Walkthrough
In this post, I’ll walk through my investigation of SOC153 — Suspicious PowerShell Script Executed, an alert generated by LetsDefend. The… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Your Locked iPhone Isn’t as Locked as You Think — YouTube Demo
In a recent Veritasium video, YouTuber Henry Reich walked up to MKBHD — one of the most tech-savvy people on the internet — placed a… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Cybersecurity in the Digital Age: Challenges, Strategies, and the Road Ahead
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Agentic AI Attacks Are Here: How Autonomous Hackers Can Breach Systems in Minutes
A deep dive into AI-powered cyberattacks, emphasizing that agentic systems are real and evolving rapidly, should motivate you to stay… Continue reading on Mediu
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The 80:1 Blind Spot: Why “Build_Agent_43” Could Be Your Next Breach
Your audit logs show “Build_Agent_43 deployed to production.” But was it really the build agent? Probably not. Continue reading on Medium »
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Why Netgear just got the first FCC router ban exemption in the US
You can keep buying Netgear routers in the US for now. Here's why - and for how long.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
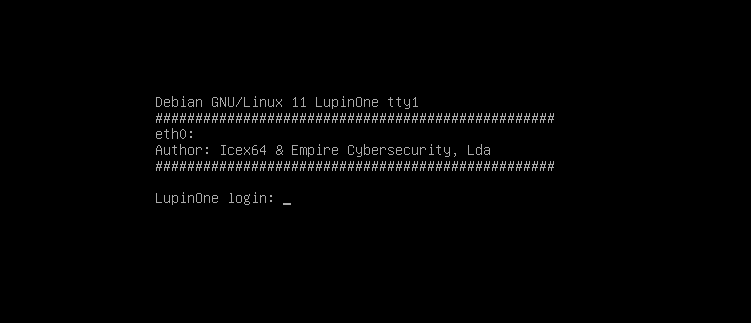
From SSH Key Leak to Root: Lupine VulnHub CTF Walkthrough (Python Hijack & pip Exploit)
A practical walkthrough demonstrating real-world misconfigurations leading to full system compromise on a VulnHub machine. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
My First Real Interview Experience in Cybersecurity
Today, I want to share something personal. Recently, I went to a company for an interview. I won’t mention the company’s name, but it was… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Cybersecurity Solutions in 2026: The Complete Pillar Guide for Businesses
Introduction: Why Cybersecurity Is Now a Business Survival Strategy Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Why DNS Traffic Is Still an Underrated Detection Source
The Security Telemetry You’re Already Collecting (And Probably Ignoring) Continue reading on Medium »
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Massive Chrome Extension Scam Exposes 20,000 Users to Data Theft
Researchers linked 108 malicious Chrome extensions to a coordinated campaign that exposed about 20,000 users to data theft, backdoors, and ad injection. The pos

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Anatomy of a Shadow: Dissecting the Solar Winds SUNBURST Supply Chain Attack
The 2020 SolarWinds Compromise remains a watershed moment in cybersecurity, fundamentally shifting the industry’s approach to supply chain… Continue reading on

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
4w ago
iPhone Setting Update Stops FBI From Extracting Signal Messages
After the FBI was able to extract incoming Signal messages from an iPhone, the messaging service’s CEO has now responded with a simple settings change to preven

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Stop Paying for Threat Detection You Don’t Need
Jeff Darrington, Technical Marketing Director, Graylog Continue reading on The Visibility Layer by Graylog »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Beste VPN voor Thuiswerken 2026: 5 Getest
Door Pieter Janssen | IT-beveiligingsconsultant, 11 jaar ervaring | Utrecht | Bijgewerkt: april 2026 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Şirketler Ne Kadar Güvende?
Görünürlük Artarken Riskler de Artıyor Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Manufacturing Identity Security Is No Longer an IT Problem — It’s a Business Risk
Manufacturing has become the most targeted industry for cyberattacks. And in the vast majority of incidents, the entry point is not a… Continue reading on Mediu

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Dangerous Microsoft Windows Update Confirmed—Do Not Download
As security researchers warn about a dangerous Microsoft Windows update that isn’t, users must pay close attention to what they are actually downloading.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
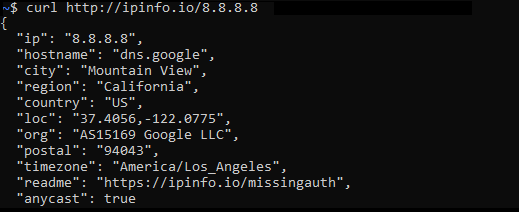
IP-info for analyzing IP Address information
With the current geo-policatal tensions in world it’s becoming important as security analyst to determine the originating traffic/attack… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
CyberSecurity Liability and Incident Disclosure
A Legal Research Report by The Innovation Attorney Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Vulnerability Discovery Cycle Just Collapsed. Here’s What We Built to Keep Up.
If you’re a CTO, CISO, or engineering leader, here’s what you need to know right now: Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
How a Simple Signup Feature Turned Into a Malware Delivery Vector (My First Paid Bug)
I wasn’t even looking for something big. Continue reading on Medium »
MIT Technology Review
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Cyberscammers are bypassing banks’ security with illicit tools sold on Telegram
From inside a money-laundering center in Cambodia, an employee opens a popular Vietnamese banking app on his phone. The app asks him to upload a photo associate
Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
4w ago
10 Hours to Exploitation: How a Missing Auth Check in Marimo Turns Your Python Notebook Into an…
CVE-2026–39987 deep dive: a pre-authenticated RCE in Marimo’s terminal WebSocket that was weaponized within hours of disclosure. Why the… Continue reading on Me

Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Learn Cybersecurity Like a Pro in 2026
Creating Your Individual Knowledge Base Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
“How to Stay Safe Online” — Best practices for protecting personal information and avoiding online…
First, double-check that the URL begins with ‘HTTPS’ and that there’s a padlock symbol either before or after it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
From Security To Seo: Complete Business Solutions
From cybersecurity to SEO, get complete business solutions to grow and protect your brand. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Cloud Has an Address.
And Drones Found It.
I have explained hundreds of architectural decisions in my career. Tradeoffs between cost and performance. Debates about vendor lock-in… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Microsoft’s April 2026 Patch Tuesday Is a Warning Shot: A SharePoint Zero-Day, 169 Flaws, and a…
One critical IKE remote code execution flaw. And 169 vulnerabilities patched in a single month. Continue reading on Medium »
Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Claude Mythos Shows That Software Was Never as Safe as We Thought
A look at how Claude Mythos is quietly exposing how fragile all our software really is. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Claude Mythos Shows That Software Was Never as Safe as We Thought
A look at how Claude Mythos is quietly exposing how fragile all our software really is. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI