CUSTOM Java Deserialization Exploit - Serial Snyker
Skills:
Ethical Hacking & Pen Testing80%
Read ALL the solutions and writeups from the Snyk Fetch the Flag! ➡ https://jh.live/snyk-fetch
Help the channel grow with a Like, Comment, & Subscribe!
❤️ Support ➡ https://jh.live/patreon ↔ https://jh.live/paypal ↔ https://jh.live/buymeacoffee
Check out the affiliates below for more free or discounted learning!
🖥️ Zero-Point Security ➡ Certified Red Team Operator https://jh.live/crto
💻Zero-Point Security ➡ C2 Development with C# https://jh.live/c2dev
🐜Zero2Automated ➡ Ultimate Malware Reverse Engineering https://jh.live/zero2auto
⛳Point3 ESCALATE ➡ Top-Notch Capture the Flag Training https://jh.live/escalate
👨🏻💻7aSecurity ➡ Hacking Courses & Pentesting https://jh.live/7asecurity
📗Humble Bundle ➡ https://jh.live/humblebundle
🐶Snyk ➡ https://jh.live/snyk
🤹♀️SkillShare ➡ https://jh.live/skillshare
🌎Follow me! ➡ https://jh.live/discord ↔ https://jh.live/twitter ↔ https://jh.live/linkedin ↔ https://jh.live/instagram ↔ https://jh.live/tiktok
Timestamps:
00:00 - Serial Snyker
00:33 - Challenge Explaination
01:03 - Challenge Start
01:53 - Docker Instance Specs
02:22 - Source Code Exploration
05:37 - Begin Poking at Website
06:39 - Using Snyk
10:14 - Searching for insecure deserialization vulnerabilities
12:15 - Creating an exploit
20:16 - Packaging
21:47 - Remote Code Execution!
24:32 - Building reverse shell script
27:01 - Final thoughts
28:09 - Thank You, Snyk
📧Contact me! (I may be very slow to respond or completely unable to)
🤝Sponsorship Inquiries ➡ https://johnhammond.llc/sponsor
🚩 CTF Hosting Requests ➡ https://johnhammond.llc/sponsor
🎤 Speaking Requests ➡ https://johnhammond.llc/sponsor
💥 Malware Submission ➡ https://jh.live/malware
❓ Everything Else ➡ https://jh.live/etc
Watch on YouTube ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
Playlist
Uploads from John Hammond · John Hammond · 0 of 60
← Previous
Next →
1
 2
2
 3
3
 4
4
 5
5
 6
6
 7
7
 8
8
 9
9
 10
10
 11
11
 12
12
 13
13
 14
14
 15
15
 16
16
 17
17
![Python [colorama] 00 Installing on Linux](https://i.ytimg.com/vi/oeodA91dO_k/mqdefault.jpg) 18
18
![Python [colorama] 09 Cursor Position](https://i.ytimg.com/vi/EucPkcOYekE/mqdefault.jpg) 19
19
![Python [hashlib] 02 Algorithms](https://i.ytimg.com/vi/ESRTg-vbjHM/mqdefault.jpg) 20
20
 21
21
![Python [pygame] 11 Rectangular Collision Detection](https://i.ytimg.com/vi/57bkG0HytI8/mqdefault.jpg) 22
22
![Python [pygame] 12 Platforming Rectangular Collision Resolution](https://i.ytimg.com/vi/qgs9Y-lxHA0/mqdefault.jpg) 23
23
![Python [XML-RPC] 01 Research](https://i.ytimg.com/vi/uOuNajsNztA/mqdefault.jpg) 24
24
![Python [pyenchant] 03 Personal Word Lists](https://i.ytimg.com/vi/Mb2OkDSlAbk/mqdefault.jpg) 25
25
![FancyURLopener Authentication and User-Agent [urllib] 03](https://i.ytimg.com/vi/I8d9Dy4P8Sg/mqdefault.jpg) 26
26
 27
27
 28
28
 29
29
 30
30
 31
31
 32
32
 33
33
 34
34
 35
35
 36
36
 37
37
 38
38
 39
39
 40
40
 41
41
 42
42
 43
43
![Hack The Vote 2016 CTF: Sander's Fan Club [web100]](https://i.ytimg.com/vi/leITIf-tzcw/mqdefault.jpg) 44
44
![Hack The Vote 2016 CTF Warpspeed [forensics150]](https://i.ytimg.com/vi/1PbwQyByfos/mqdefault.jpg) 45
45
 46
46
 47
47
 48
48
 49
49
 50
50
 51
51
 52
52
 53
53
 54
54
 55
55
 56
56
 57
57
 58
58
 59
59
 60
60


Code Commentaries? PHP to JavaScript in Bash and PHP!
John Hammond

Tutorials? MySQL connection with PHP and Bash!
John Hammond

Variable Naming in Python! Happy Birthday, Linux! Nokia N900!
John Hammond

JavaScript Splits The URL!
John Hammond

HTML Tables in Python!
John Hammond

HTML, Net Shares, GML!
John Hammond

Python 08 Programming Style and Comments
John Hammond

Python 26 Object Oriented Programming
John Hammond

75 Python Tutorials, Out Now!
John Hammond

Batch 14 Mathematical Expressions
John Hammond
Batch 85 Array Append
John Hammond

Batch 86 Array Count
John Hammond

Batch 87 Array Index
John Hammond

Batch 88 Array Insert
John Hammond

Batch 89 Array Remove
John Hammond

Batch 90 Array Reverse
John Hammond
![Python [colorama] 00 Installing on Linux](https://i.ytimg.com/vi/oeodA91dO_k/mqdefault.jpg)
Python [colorama] 00 Installing on Linux
John Hammond
![Python [colorama] 09 Cursor Position](https://i.ytimg.com/vi/EucPkcOYekE/mqdefault.jpg)
Python [colorama] 09 Cursor Position
John Hammond
![Python [hashlib] 02 Algorithms](https://i.ytimg.com/vi/ESRTg-vbjHM/mqdefault.jpg)
Python [hashlib] 02 Algorithms
John Hammond

Python 00 Installing IDLE on Linux
John Hammond
![Python [pygame] 11 Rectangular Collision Detection](https://i.ytimg.com/vi/57bkG0HytI8/mqdefault.jpg)
Python [pygame] 11 Rectangular Collision Detection
John Hammond
![Python [pygame] 12 Platforming Rectangular Collision Resolution](https://i.ytimg.com/vi/qgs9Y-lxHA0/mqdefault.jpg)
Python [pygame] 12 Platforming Rectangular Collision Resolution
John Hammond
![Python [XML-RPC] 01 Research](https://i.ytimg.com/vi/uOuNajsNztA/mqdefault.jpg)
Python [XML-RPC] 01 Research
John Hammond
![Python [pyenchant] 03 Personal Word Lists](https://i.ytimg.com/vi/Mb2OkDSlAbk/mqdefault.jpg)
Python [pyenchant] 03 Personal Word Lists
John Hammond
![FancyURLopener Authentication and User-Agent [urllib] 03](https://i.ytimg.com/vi/I8d9Dy4P8Sg/mqdefault.jpg)
FancyURLopener Authentication and User-Agent [urllib] 03
John Hammond

Python 04: PEP8 Coding
John Hammond

Python Challenge! 17 COOKIES
John Hammond

Google CTF 2016: Ernst Echidna
John Hammond

Google CTF 2016: Spotted Quoll
John Hammond

Google CTF 2016: Can you Repo It?
John Hammond

Google CTF 2016: No Big Deal
John Hammond

Google CTF 2016: In Recorded Conversation
John Hammond

Homemade CTF Challenge: 01 "Orchestra"
John Hammond

Homemade CTF Challenge: 02 "Bae's Base"
John Hammond

Homemade CTF Challenge: 03 "Web Hunt"
John Hammond

Homemade CTF Challenge: 04 "UPX"
John Hammond
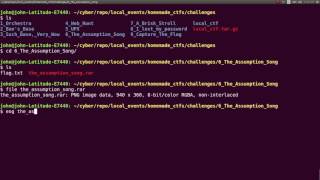
Homemade CTF Challenge: 05 "The Assumption Song"
John Hammond

Homemade CTF Challenge: 06 "A Brisk Stroll"
John Hammond

Homemade CTF Challenge: 06 "I lost my password!"
John Hammond

web25 :: Mr. Robot : EKOPARTY CTF 2016
John Hammond

web50 : RFC 7230 :: EKOPARTY CTF 2016
John Hammond

misc50 : Hidden inside EKO :: EKOPARTY CTF 2016
John Hammond
![Hack The Vote 2016 CTF: Sander's Fan Club [web100]](https://i.ytimg.com/vi/leITIf-tzcw/mqdefault.jpg)
Hack The Vote 2016 CTF: Sander's Fan Club [web100]
John Hammond
![Hack The Vote 2016 CTF Warpspeed [forensics150]](https://i.ytimg.com/vi/1PbwQyByfos/mqdefault.jpg)
Hack The Vote 2016 CTF Warpspeed [forensics150]
John Hammond

Juniors CTF 2016 :: Black Suprematic Square
John Hammond

Juniors CTF 2016 :: Six Strange Tales
John Hammond

Juniors CTF 2016 :: Lost Code
John Hammond
Juniors CTF 2016 :: Here Goes!
John Hammond

Juniors CTF 2016 :: Southern Cross
John Hammond

Juniors CTF 2016 :: Clone Attack
John Hammond

Juniors CTF 2016 :: Dirty Repo
John Hammond

Juniors CTF 2016 :: Hackers Blog
John Hammond

Juniors CTF 2016 :: Voting!!!
John Hammond

Juniors CTF 2016 :: The Good, The Bad and The Junkman
John Hammond

Juniors CTF 2016 :: Stop Thief!
John Hammond

Juniors CTF 2016 :: ROFL
John Hammond

Juniors CTF 2016 :: Restriced Area
John Hammond

Juniors CTF 2016 :: Oh SSH!
John Hammond

HackCon CTF 2017 TRIVIA and BONUS Challenges
John Hammond

HackCon CTF 2017 "Bacche" Challenges
John Hammond
Related AI Lessons
⚡
⚡
⚡
⚡
The MCP Security Gap No One Is Talking About
Dev.to AI
Top 10 Security Mistakes Developers Make in 2026
Dev.to · SANGKUR
Managing TLS certificates and JWT keys is still a mess in 2026 — so I built a tool
Dev.to · WRVault
An npm worm compromised 170 packages in six minutes — including OpenAI’s laptops
Medium · Programming
Chapters (14)
Serial Snyker
0:33
Challenge Explaination
1:03
Challenge Start
1:53
Docker Instance Specs
2:22
Source Code Exploration
5:37
Begin Poking at Website
6:39
Using Snyk
10:14
Searching for insecure deserialization vulnerabilities
12:15
Creating an exploit
20:16
Packaging
21:47
Remote Code Execution!
24:32
Building reverse shell script
27:01
Final thoughts
28:09
Thank You, Snyk
🎓
Tutor Explanation











 DeepCamp AI
DeepCamp AI