Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,396 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Malicious PowerShell Analysis — BTLO Lab Writeup
Platform: Blue Team Labs Online (BTLO) | Difficulty: Medium | Category: Security Operations (SO) Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Undiscovered (THM) Tryhackme Writeup Answer
Description : Discovery consists not in seeking new landscapes, but in having new eyes. Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Asaaju Peter Raises Alarm Over Poor Cybersecurity Culture in Nigerian Tech Companies as Data Breaches Continue to Rise
Nigerian technology entrepreneur and digital media publisher Asaaju Peter has spoken out on one of the most overlooked threats facing the country’s growing tech

Dev.to · BotConductStandard
🔐 Cybersecurity
⚡ AI Lesson
2w ago
45% of Hostile Bot Traffic Passes Your WAF. Here's Why. What behavioral detection reveals when you cross-reference hostile actors against AbuseIPDB
Most enterprise WAFs are configured to block IPs above a certain abuse confidence threshold....

Dev.to · v. Splicer
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building a Silent Keylogger Into a USB-C Hub (For My Own Laptop, Obviously…)
The hub sits there like it belongs. Aluminum shell, faintly warm, a short braided cable that kinks...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
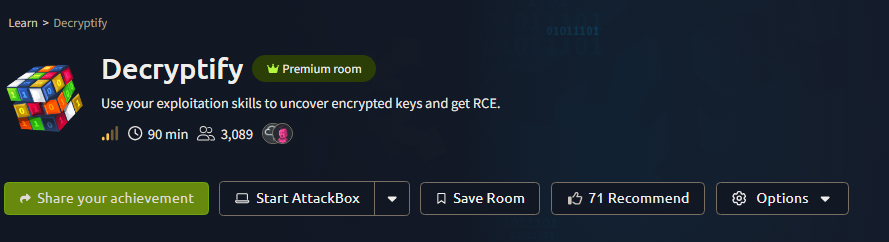
TryHackMe: Decryptify (CTF)
Why This Lab Stands Out Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
TryHackMe Walkthrough: Windows Fundamentals Part 2
A hands-on walkthrough of the Windows Fundamentals Part 2 room on TryHackMe. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
✍️ STT #3 — Comment and Control
Series: ✍️ Sip the Threat by TheGr8Val Week: April 27 — May 3, 2026 | Estimated read time: ~7 minutes Continue reading on Medium »
![[Updated] January 2026 Crypto Scam Scam Warning List: How to Spot and Avoid Fake Platforms.](https://cdn-images-1.medium.com/max/1677/1*LSfz91n4QlEtdJ64cTwY3Q.png)
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
[Updated] January 2026 Crypto Scam Scam Warning List: How to Spot and Avoid Fake Platforms.
AI-powered and fake crypto investment schemes are draining billions from unsuspecting investors. Stay ahead of high-tech scams with this… Continue reading on Me

Dev.to · Bradley Matera
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Warning: Bifrost from Maxim AI Is a Real API Key Harvesting Service Targeting American Web Devs (My Exact Experience)
I’ve been deep in AI coding tools for months. Recently I started getting DMs from new “AI gateway”...
Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time DDoS Detection Engine from Scratch
When I got the Stage 3 task for the HNG DevOps internship, I honestly stared at it for a while. Build an anomaly detection engine that… Continue reading on Medi

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The 2026 Cybersecurity Roadmap (Part 2): L1 — Where You Stop Learning and Start Working
Breaking into IT with your first real role: Computer Support Specialist — the job that teaches you more than any course ever will Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The 2026 Cybersecurity Roadmap (Part 2): L1 — Where You Stop Learning and Start Working
Breaking into IT with your first real role: Computer Support Specialist — the job that teaches you more than any course ever will Continue reading on Medium »

Dev.to · George-Adaba
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time DDoS Detection System with Python, Docker, and Nginx (Beginner-Friendly Guide)
👋 Introduction As a beginner stepping into DevOps and cybersecurity, I wanted to build something...

Dev.to · Damilola Ejalonibu
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time DDoS Detection Engine from Scratch
**Section 1 — Introduction What Is This Project and Why Does It Matter? Imagine you run a website...

Dev.to · Sohanuzzaman Soad
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Build Secure Systems While Coding (A Practical Dev Story You Shouldn’t Ignore)
“We’ll fix security later.” — Every developer, right before a critical production failure. Let’s...

Dev.to · Gabriel Pavel
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Config Rule Audit Your IR Playbook Is Missing
Your AWS compliance infrastructure can become a self-sustaining backdoor. Here's how the mechanic...

Dev.to · Iteration Layer
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Processing Client Documents Securely: A Field Guide for Technical Agencies
The Security Questionnaire That Started This You land a new enterprise client. The SOW is...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
SOC VS GRC Analyst: Which Career is Better in 2026?
As we all know, cybersecurity is one of the fastest-growing fields in 2026, and roles like SOC Analyst and GRC Analyst are in high demand. Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Investigation: Network Activity Analysis Across Multiple PCAPs
This investigation is based on a Blue Team Labs Online (BTLO) scenario involving analysis of multiple packet captures. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Digital Labyrinth: How Technical Deception Becomes a Trap
The Illusion of the Perfect Alibi Continue reading on Medium »
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The best VPN for small businesses in 2026: Expert tested and reviewed
Looking for the best VPN for your small business? I tested Surfshark, Proton VPN, and more to find the top picks.

Dev.to · AbbatFariDi
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Website Security Configuration Audit from Android in 15 Minutes: curl, openssl, dig — No Hacking, No Root
What You Can Find From the Outside Without Server Access 1. What Is a...

Dev.to · Okeoghene Akwerigbe
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Multi-Layered Defense: Building an Intelligent, Dual-Trigger Firewall
In modern DevOps, a simple rate-limiter isn't enough. If you set a hard limit of "10 requests per...

Dev.to · Adewumi Victor
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building a Self-Learning DDoS Guard
Real-Time Anomaly Detection with Python By Victor • HNG DevSecOps Project Case Study In the modern...

Dev.to · idme
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building Scalable Single Sign-On (SSO) for Large-Scale Portals: Lessons in Security and UX
When building large-scale web applications, especially those serving the public or educational...

Dev.to · Boluwaji Dare
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time DDoS Detection Engine from Scratch (No Libraries Cheat Sheet!)
Imagine you run a website. Everything is working fine, users are logging in, uploading files, and...

Dev.to · Mittal Technologies
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Why Security Should Be the First Feature in Your Mobile App
Let me describe a conversation that happens way too often. A startup has a working product, growing...
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The best Apple TV VPNs of 2026: Expert tested and reviewed
Setting up a VPN on your Apple TV can be a nuisance, but with one of our top Apple TV VPNs, setup and streaming will take mere moments.

Dev.to · Martijn Mik
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Your SOC2 Auditor Just Asked for an API Inventory. Does Your Code Have the Receipts?
AI-driven velocity is great until the audit starts. Here is why "Zombie APIs" are the fastest way to fail your SOC2/ISO compliance and how to fix it.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Many aspiring cybersecurity professionals struggle with one major problem:
The CyberRise 30-day Cybersecurity Career Blueprint is a complete guide for every beginner Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Broken Access Control via Overprivileged Public API Key — How I Accessed 100+ User IDs, Search…
A public chatbot key that was never supposed to do this much — and a $150 goodwill reward that confirmed it. Continue reading on Medium »

Medium · LLM
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Broken Access Control via Overprivileged Public API Key — How I Accessed 100+ User IDs, Search…
A public chatbot key that was never supposed to do this much — and a $150 goodwill reward that confirmed it. Continue reading on Medium »

Dev.to · Czax225
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building Your First Cybersecurity Tool with Spectator: A New Language for Pentesters
The Problem We All Face Let's be honest: when you're in the middle of a penetration test or red team...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Salesforce Security Isn’t Enough: Why Your Integration Layer Matters More
I’ve noticed something interesting in conversations with teams working on Salesforce security. Continue reading on Medium »

Dev.to · ICHINO Kazuaki
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Rethinking What You Need to Do When Your Access Keys Are Compromised
"A Note from the Author" I work in the Technical Support division of an AWS reseller operating under...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Cloud security isn’t inherited: Why IAM is where most AWS environments fail
If you can see it, configure it, or click it, it’s your responsibility. Continue reading on Medium »

Dev.to · PrincewillDev
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time DDoS Detection Engine From Scratch (And What I Learned)
How I Built a Real-Time DDoS Detection Engine From Scratch (And What I Learned) A few weeks ago I...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building a Zero-Trust Security Architecture From Scratch: A Founder’s Guide
Most startups do not have a security problem because they ignored security. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Cyber Attack on Stryker: A Wake Up Call for Organizations
The recent cyber attack on medical technology company Stryker is a powerful reminder that cyber incidents can quickly move beyond IT… Continue reading on Medium

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
2w ago
I Built a Tool That Detects DDoS Attacks in Real Time — Here’s Exactly How It Works
The alert arrives at 2:47 AM. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Signing Is the Control Plane
The Architecture of Authority Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Three breaches that had nothing to do with hackers and everything to do with compliance theater
Being certified is not the same as being secure. These three cases prove it at enormous cost. In each of these incidents, the security… Continue reading on Medi
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Sony Locked People Out of Games They Already Paid For. Here Is What Is Actually Happening.
Sony Locked People Out of Games They Already Paid For. Here Is What Is Actually Happening. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Symmetric vs.
Imagine handing someone the key to your house — but that same key is the only one that exists. If they copy it or lose it, you’re exposed… Continue reading on M

Dev.to · Marcin Firmuga
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Why I Sign Every .exe With Sigstore - PC Workman v1.7.2 Release, Security-First Open Source
Someone tried to scare me with a security audit. It backfired. A few days ago, a stranger on the...
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
2w ago
ClickUp Data Leak Exposes Enterprise Emails for Over a Year
A hardcoded ClickUp API key exposed hundreds of corporate and government emails for over a year, raising new SaaS security concerns. The post ClickUp Data Leak

Dev.to · Nneoma Uwakwe
🔐 Cybersecurity
⚡ AI Lesson
2w ago
I Built a System That Catches Hackers in Real Time
I Built a System That Catches Hackers in Real Time The Problem It was a regular Tuesday morning...
 DeepCamp AI
DeepCamp AI