Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,396 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building a Windows File System Minifilter Driver: Intercepting File Access
Welcome to this new Medium post. In this article, I’ll walk you through the implementation of a basic Windows File System Minifilter… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
CyberDefenders — Ramnit Walkthrough
Ramnit, siber güvenlik dünyasında “klasik” ama hala ölümcül olan, modüler yapısı ve yayılma hızıyla bilinen bir bankacılık truva atıdır… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Securing the Backbone — Issue #33: The Reports That Redefined Cyber Risk
The most influential cybersecurity and software supply chain research shaping 2025 — and what every CISO and board should take from them. Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Securing the Backbone — Issue #32 (Part 1): Legacy Dependencies and the AI Vulnerability Avalanche…
October 6, 2025 ✍️ Eric Gallagher Securing Software Supply Chains | Host of Securing the Backbone | Author of The No-Nonsense… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Olay Müdahale Raporu: 3CX Tedarik Zinciri(Supply Chain) Saldırısı Analizi (CyberDefenders)
Siber güvenlikte en zorlu senaryolardan biri, güvendiğiniz kalenin içinden vurulmaktır. Bu makalede, CyberDefenders platformundaki 3CX… Continue reading on Medi
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
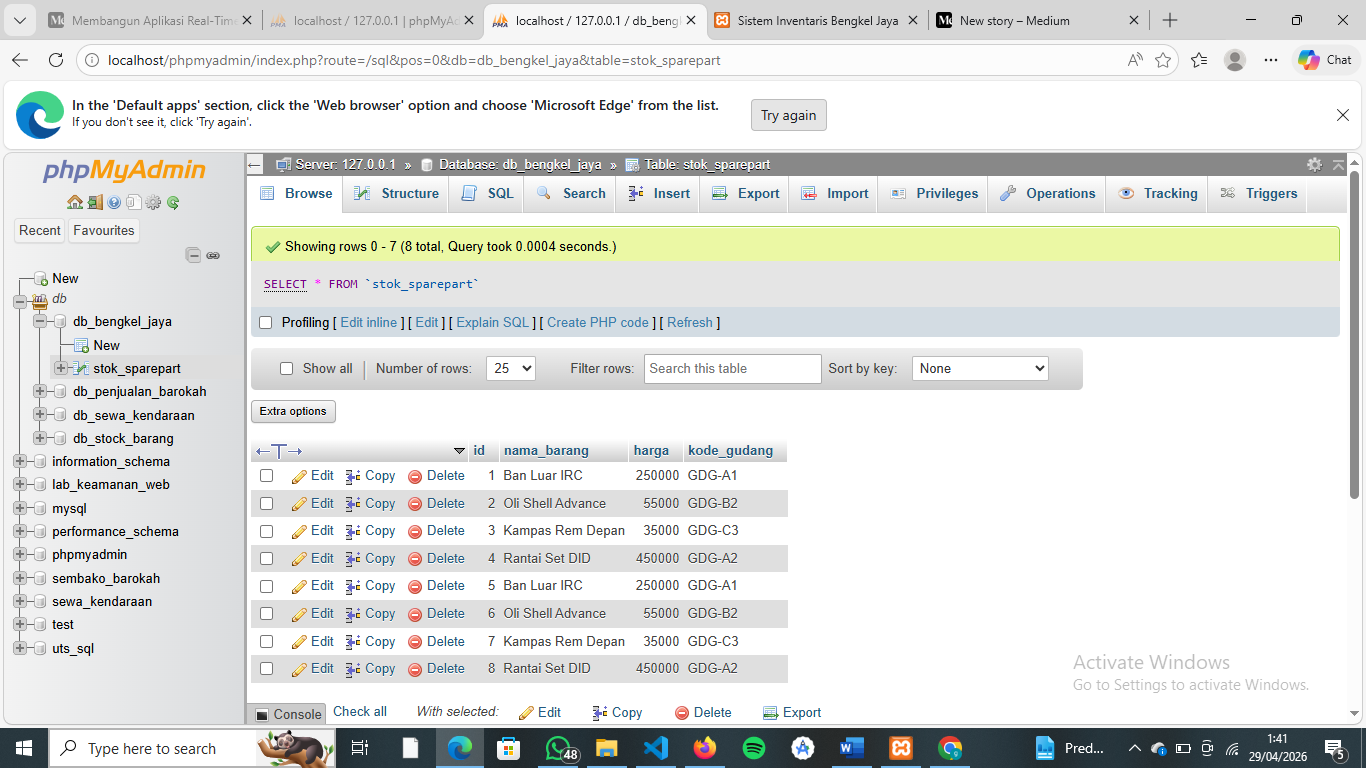
Eksploitasi SQL Injection pada Sistem Manajemen Inventaris Bengkel Jaya
Oleh: [Haris Adriansyah] Tugas Tengah Semester (UTS) — Pemrograman Web Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Penetration Testing: Validating My Infrastructure Against SQL Injection with Exegol & SQLMap
Goal: Conduct an authorized penetration test on my own web application to detect and validate SQL Injection (SQLi) vulnerabilities using… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Plain-Language Vendor Test for AI Controls
We have all been in that demo- The AI vendor clicks through shiny screens and uses all these buzzwords. By the end, everyone is nodding… Continue reading on Zac

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Top Scamadviser.com Alternatives Recommended by Experts
We live in a world where almost everything happens online. Shopping, banking, job hunting, even meeting new people. But with all that… Continue reading on Mediu

Dev.to · Satyam Rastogi
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Silk Typhoon Extradition: State-Sponsored APT Operator Accountability & Persistence TTPs
Xu Zewei's extradition marks rare accountability for state-sponsored operators. Analysis of Silk Typhoon's targeting methodology, C2 infrastructure, c

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
fast16 | Mystery ShadowBrokers Reference Reveals High-Precision Software Sabotage
The Silent Harbinger of Cyber-Physical Statecraft (Circa 2005) Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Secure File Uploads in Next.js + Supabase Storage
Most Supabase upload tutorials skip RLS on the bucket and trust the client. Here’s how to upload securely with Server Actions and signed… Continue reading on Me

Medium · Data Science
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Invisible Shield: Why Cybersecurity Engineering Matters More Than Ever
Most people don’t think about cybersecurity — until something breaks. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Invisible Shield: Why Cybersecurity Engineering Matters More Than Ever
Most people don’t think about cybersecurity — until something breaks. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Why AI-Generated Code is Breaking Your Security Stack in 2026
In 2026 the software landscape has shifted fundamentally. The work is shifting from writing code to dealing with the complexity of… Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
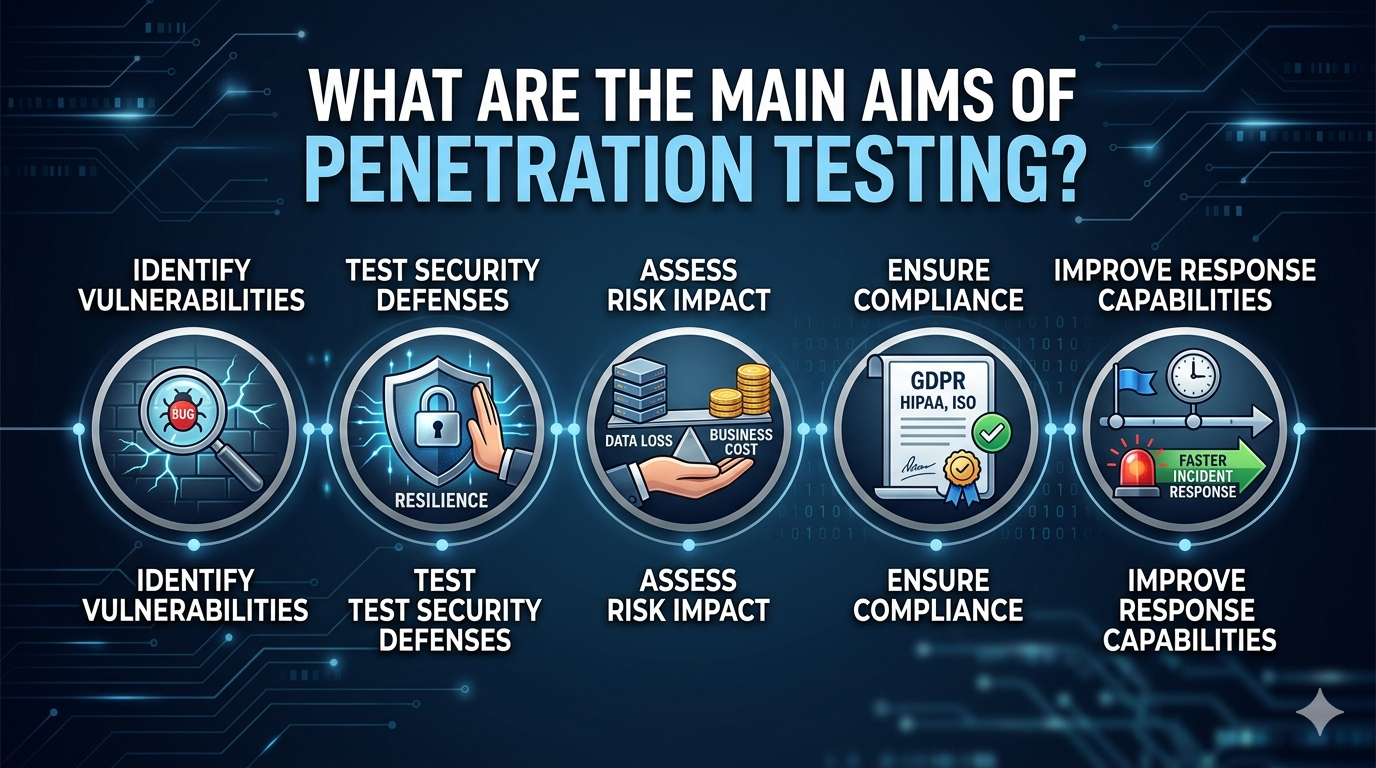
What Are the Main Aims of Penetration Testing?
Penetration testing, often called pen testing, is one of the most effective ways to understand how secure a system really is. Instead of… Continue reading on Me

The Next Web AI
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Social media scams cost Americans $2.1 billion in 2025
New FTC data published Monday show that nearly 30% of all reported scam losses last year began on social media. Investment scams alone cost $1.1 billion. Shoppi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Recognizing the Hidden Signs of Cyber Threats
Cyberattacks are no longer rare events reserved for large corporations or government agencies. Small businesses, startups, and even… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
SQL Injection: Cara Kerjanya,Bahayanya, dan Pengalaman Mencoba Sendiri
Oleh: Lola Seftyliani NIM:312410339 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Backup Alıyoruz… Peki geri dönebiliyor muyuz?
Çoğu kurum için güven duygusu şu cümleye dayanır: Continue reading on Medium »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How a Roblox Cheat Script Took Down a Billion-Dollar Company
A Vercel employee clicked one OAuth button. Three weeks later, customer secrets were on a hacker’s drive. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How a Roblox Cheat Script Took Down a Billion-Dollar Company
A Vercel employee clicked one OAuth button. Three weeks later, customer secrets were on a hacker’s drive. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How a Roblox Cheat Script Took Down a Billion-Dollar Company
A Vercel employee clicked one OAuth button. Three weeks later, customer secrets were on a hacker’s drive. Continue reading on Medium »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Cybersecurity Foundations for Ethical Hacking and System Protection
The Ethical Hacking Foundation Certification provides essential knowledge to professionals who need to identify vulnerabilities and… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Digital Conflict and Disconnect: The Systematic Failure of Matchmaking Protocols in Modern…
Bangkok, Thailand — In the rapidly evolving landscape of international e-sports, the intersection of infrastructure stability and… Continue reading on Medium »

Dev.to · Joseph Joshua
🔐 Cybersecurity
⚡ AI Lesson
2w ago
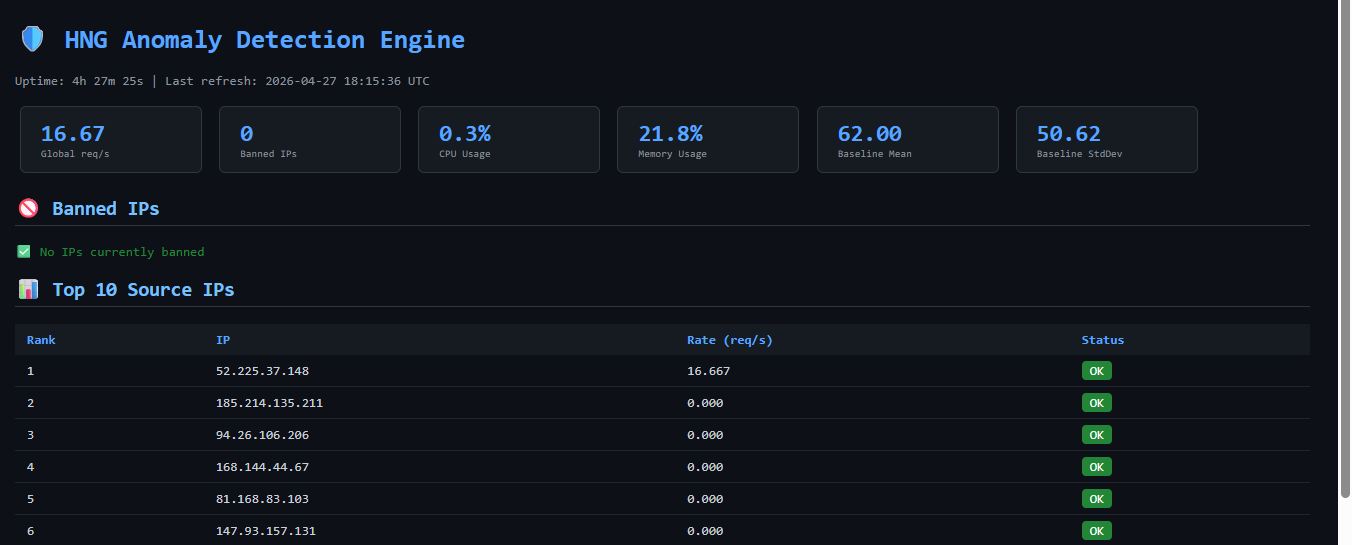
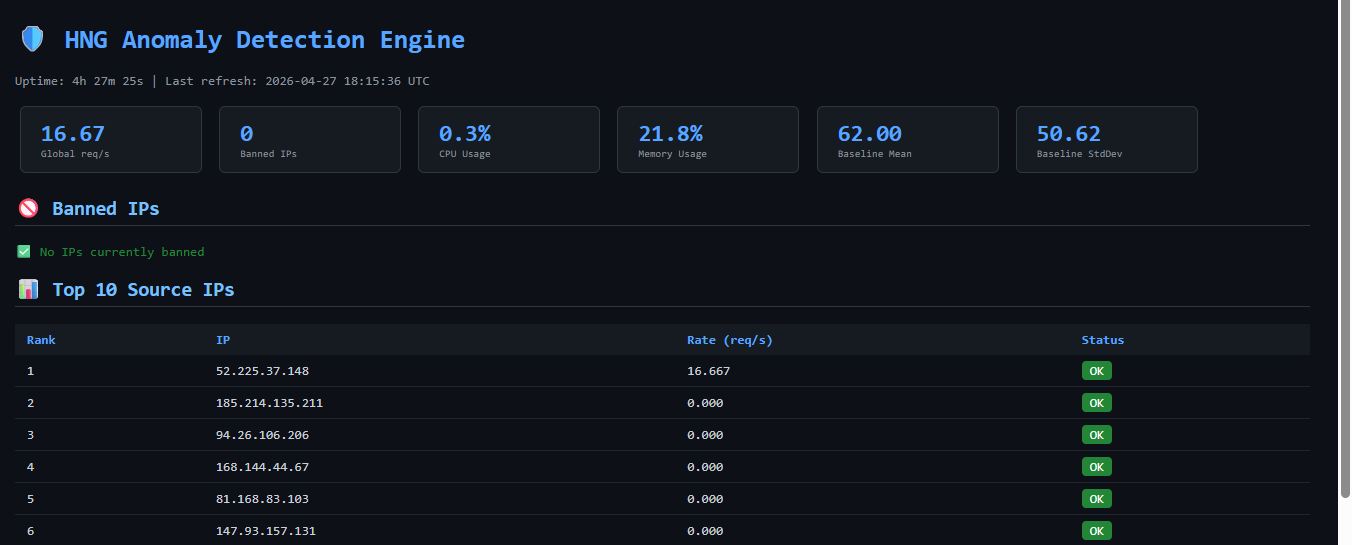
Detecting & Blocking Anomalous Traffic with Cloud Anomaly Detector
A lightweight, containerized anomaly detection system that monitors traffic in real time, detects...

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
2w ago
IPv8 Changes Everything? Not Really — The Truth Behind the Viral Claim
This IPv8 Proposal Went Viral Continue reading on System Weakness »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Day 4: Kali Linux for Beginners: 40 Linux Commands Hackers Use Daily PART (A)
Kali Linux Continue reading on OSINT Team »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Enemy Already Inside — Hunt Forward Lab #002: LOLBAS Detection
Lab Difficulty: Intermediate — Estimated Time: 60–90 minutes Continue reading on InfoSec Write-ups »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Proof-Carrying Data: Why Information Must Travel With Its Own Verification
Data without proof is just a claim Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Kriptografski inventar i kvantna spremnost
Kvantna računarska era vise nije teorijska tema za akademske radove. Ona postaje strateški rizik za velike organizacije koje se oslanjaju… Continue reading on M
Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
2w ago
A step-by-step guide to building a real-time HTTP anomaly detector using Python, deques, and…
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Cybersecurity Trends Every Developer Should Know This Year
Why security is no longer “someone else’s problem” Continue reading on Medium »

Dev.to · kanta13jp1
🔐 Cybersecurity
⚡ AI Lesson
2w ago
10 Security Principles Before You Ship an MCP Server
10 Security Principles Before You Ship an MCP Server Model Context Protocol (MCP) servers...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
¿Es posible rastrear criptomonedas robadas?
Cómo funciona el rastreo en blockchain Introducción Una de las características únicas de las criptomonedas es la transparencia. Cada… Continue reading on Medium
Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time Anomaly Detection Engine from Scratch
The Problem: When Your Website Gets Attacked Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built a Real-Time Anomaly Detection Engine from Scratch
The Problem: When Your Website Gets Attacked Continue reading on Medium »
Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built ExRecon: Turning a Security Automation Project Into a Smarter, More Maintainable…
There’s a big difference between writing a script that works once and building a project that is structured, maintainable, and capable of… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How I Built ExRecon: Turning a Security Automation Project Into a Smarter, More Maintainable…
There’s a big difference between writing a script that works once and building a project that is structured, maintainable, and capable of… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Understanding Darknet Opioids: Risks, Trends, and Market Signals
The conversation around opioids has evolved far beyond traditional supply chains. In recent years, researchers and cybersecurity analysts… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Someone Already Has Your Encrypted Data. They’re Just Waiting.
Not the dramatic kind. No zero-days, no ransomware war rooms, no breach notifications landing at 3am. The slow, structural kind, the… Continue reading on MeetCy
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
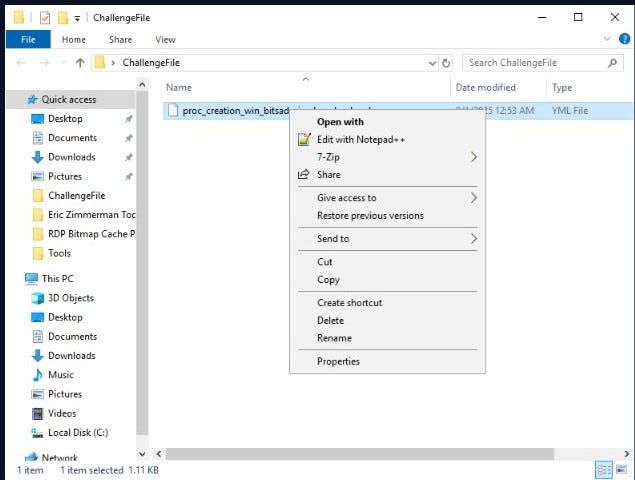
Sigma Lab Write-up — bitsadmin Detection Rule
Introduction In this lab, we worked on analyzing a Sigma rule related to ransomware activity. Continue reading on Medium »

Dev.to · BeyondMachines
🔐 Cybersecurity
⚡ AI Lesson
2w ago
State of (in)security - Week 17, 2026
Between April 20–27, 2026, there were 10 vulnerability advisories and 21 cybersecurity incidents impacting nearly 1 million individuals, with the largest being
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How AI Detects Cyber Attacks Before They Happen
Cyberattacks today aren’t occasional — they’re constant, automated, and getting smarter every day. Traditional security systems mostly… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
AI Is Already Outpacing Your Security Team. That Is Not Debate.
There is no soft way to say this. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Why You Should Stop Uploading Your Sensitive PDFs to “Cloud” Lockers (PDF Password locking tools)
We’ve all been there. You have a sensitive bank statement, a business contract, or a copy of your Aadhaar card that needs a password… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Burp Suite DAST Tutorial: How to Run Authenticated Scans Using Recorded Login Sequences
Burp Suite DAST is a product by PortSwigger designed for automated Dynamic Application Security Testing (DAST) of web applications and… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Your Enterprise Wi-Fi Password Is Screaming Into the Void
Here’s a fun thought experiment. Imagine you built a secure door — keypad, biometric scanner, the whole deal — and then installed it in… Continue reading on Med
 DeepCamp AI
DeepCamp AI