Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
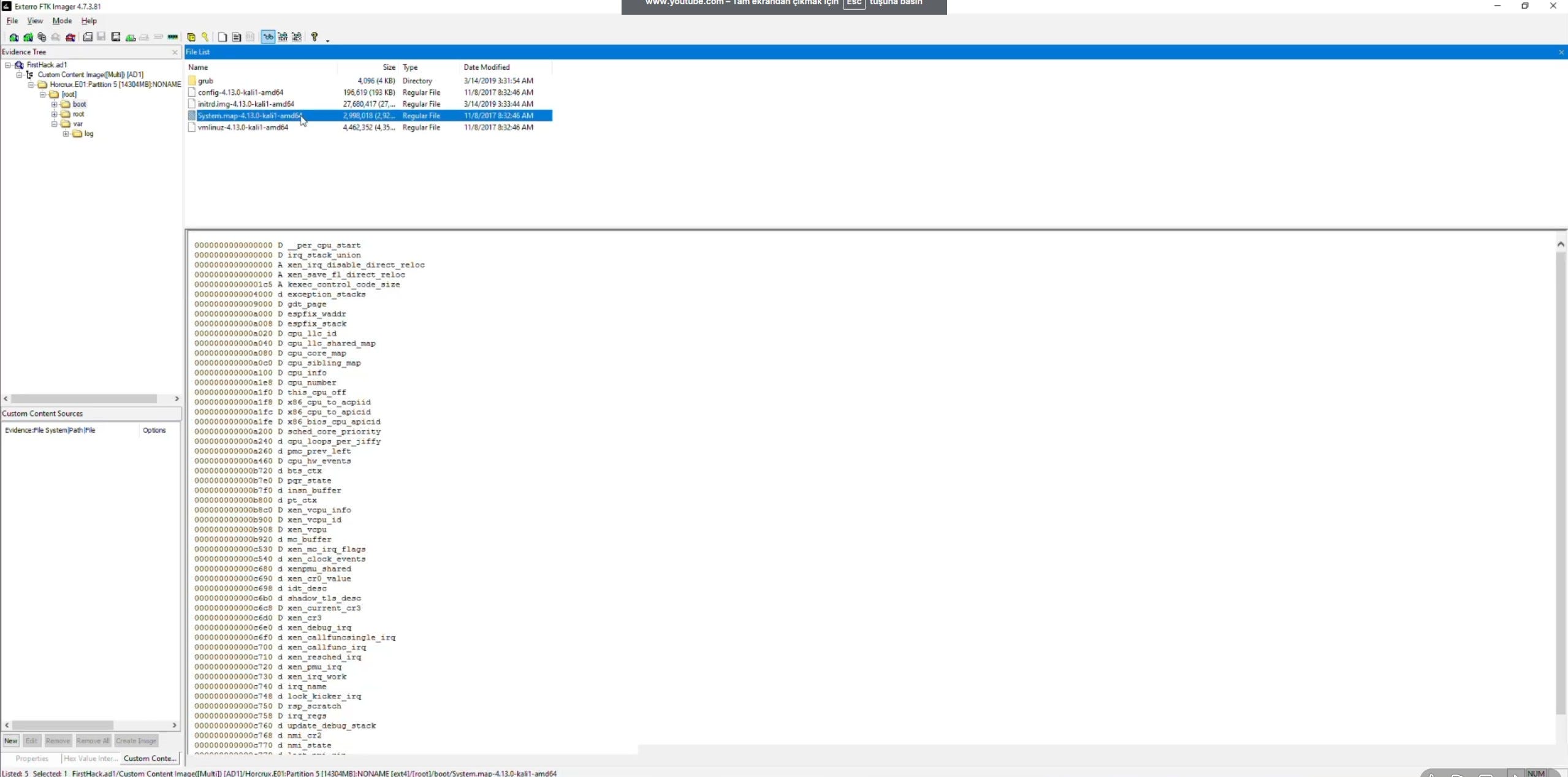
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,390 reads from curated sources

Dev.to · CVE Reports
🔐 Cybersecurity
⚡ AI Lesson
1w ago
CVE-2026-6970: CVE-2026-6970: Local Privilege Escalation via Improper GID Assignment in Canonical authd
CVE-2026-6970: Local Privilege Escalation via Improper GID Assignment in Canonical...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Urgensi Keamanan Berbasis Identitas: Mengatasi Kerentanan Autentikasi di Infrastruktur Digital
Di balik sistem keamanan yang paling kompleks sekalipun, identitas pengguna tetap menjadi salah satu target utama bagi para peretas… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Tether, Binance, and Others Freeze $41.5M of Stolen Funds
Stablecoin issuer Tether, alongside Binance, OKX, US law enforcement, and independent security agents, has frozen over $41.5 million tied… Continue reading on M

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
1w ago
“Bisnis Kecil Nggak Bakal Kena Hack” Mitos yang Bisa Membunuh Usahamu
43% serangan siber di Indonesia menyasar usaha kecil. Bukan perusahaan besar. Bukan bank. Tapi bisnis seperti punyamu. Continue reading on Medium »

Medium · JavaScript
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Reflected XSS into a JavaScript string with HTML-encoded angle brackets (<,>)
Input is reflected immediately inside a JavaScript string, where angle brackets ( ) are HTML-encoded Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Waspada Malware! Mengenal Jenis-Jenisnya, Cara Mengatasi, dan Mencegahnya
HP tiba-tiba lemot, data hilang, atau tiba-tiba ada tagihan aneh? Bisa jadi perangkatmu sudah terinfeksi malware. Yuk kenali musuhnya… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
An AI Deleted Another Database. The Real Story Isn’t the AI.
PocketOS, Replit, and the three architectural control gaps behind agent-driven production failures. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Learning Fortinet Firewall — LESSON 8: Software Switch / Layer 2
Welcome to my Fortinet Firewall (FortiGate) learning journey! Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
See You Space Cowboy: Bounty Hunting Threats with Splunk
Spike Spiegel didn’t wait for bounties to come to him. He hunted them down. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Systems Should Trust Less: Why Verification Must Replace Assumption
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Guía Definitiva GraphQL para Bug Bounty: Vulnerabilidades y Explotación
Domina el hacking de GraphQL: desde el bypass de introspección hasta Mass Assignment y ataques BOLA para Bug Bounty. Continue reading on Medium »

Dev.to · Alex Agyei
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Exploiting vsftpd 2.3.4 on Metasploitable2 (Step-by-Step Guide for Beginners)
One of the biggest turning points in learning cybersecurity is understanding how attackers move...
Search Engine Journal
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Google Is Testing New Bot Authorization Standard via @sejournal, @martinibuster
Google is testing a cryptographic protocol for verifying bot traffic that could make unwanted crawlers easier to identify. The post Google Is Testing New Bot Au

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
LFI Prevention: How to Actually Fix File Inclusion Vulnerabilities
From input validation to server hardening — what developers should be doing to prevent LFI from the ground up. Continue reading on MeetCyber »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
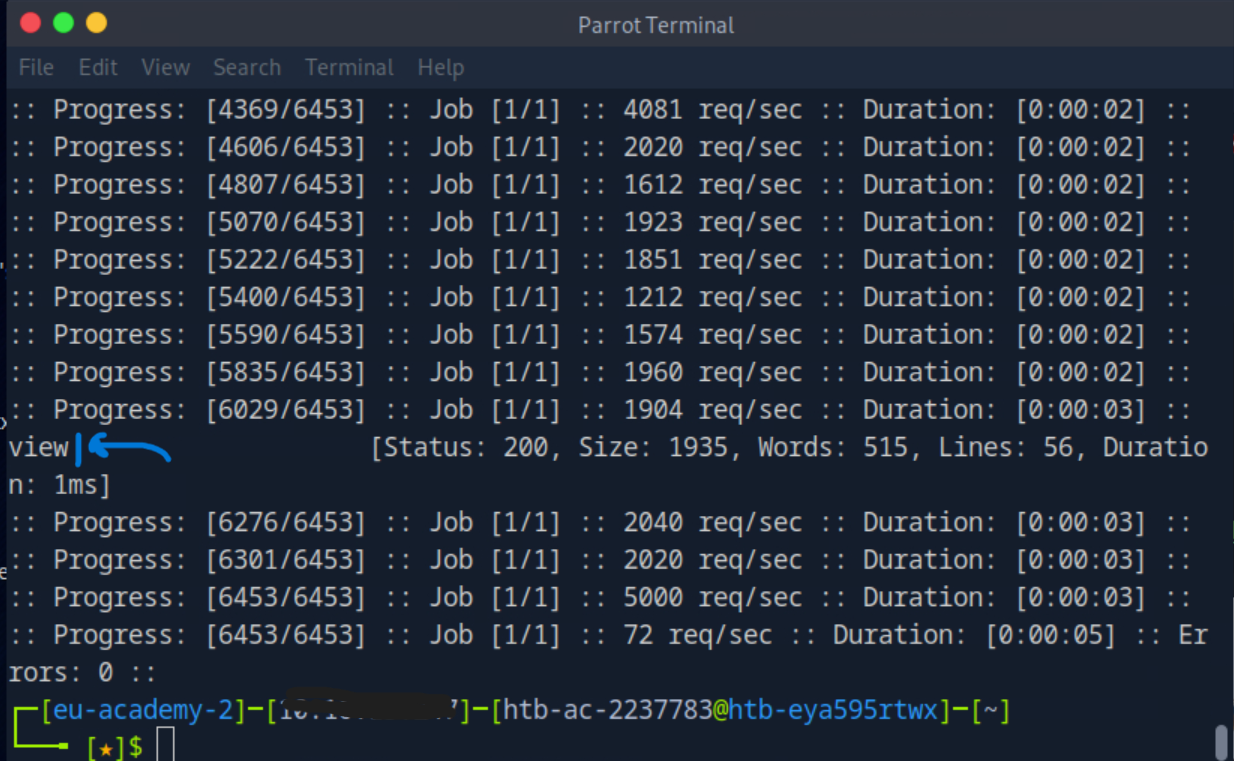
LFI Automated Scanning: Finding and Fuzzing with ffuf
Using wordlists and fuzzing tools to automate LFI discovery and server file enumeration. Part 6 of the File Inclusion series. Continue reading on MeetCyber »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Silent Backdoor in Enterprise Security: Why Unmanaged OAuth Tokens Are the New High-Risk Vector
The rapid adoption of AI productivity tools is exposing a dangerous blind spot in enterprise security architecture. Organizations invest heavily in firewalls, S

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Local Code Execution via Git Workspace Poisoning (FSMonitor)
Why blindly unzipping code into your IDE might be more dangerous than you think. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Attackers Actively Exploiting Critical Vulnerability in Breeze Cache Plugin
On April 22nd, 2026, the Wordfence Intelligence Vulnerability Database publicly disclosed a critical arbitrary file upload vulnerability… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The 8th Continent: How the Internet Became a Nation-State and Nobody Noticed
It has more citizens than any country on earth. It has its own economy, its own wars, its own warlords, and its own currency. The only… Continue reading on Medi
The Register
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Viva la revolución: LinkedIn profile visitor lists belong to the people, says Noyb
GDPR Article 15 doesn't care if you want to make money by selling users' data back to them A LinkedIn feature the average non-paying user likely only glances pa

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Dreadful 9:00 AM Assessment Call
Ever feel like the first assessment meeting is more of a pissing match than a kickoff — or like you’re dancing with a partner who has two… Continue reading on M
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1w ago
New WhatsApp Flaws Could Affect Billions of Users After Meta Security Patch
Meta patched two WhatsApp flaws affecting iOS, Android, and Windows users, including bugs tied to risky files, links, and Reels previews. The post New WhatsApp
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Google AppSheet Abuse Helped Phish 30,000 Facebook Accounts
Hackers abused Google AppSheet to send Meta phishing emails, compromising 30,000 Facebook business accounts across 50 countries. The post Google AppSheet Abuse
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
1w ago
These 5 critical Windows Defender settings are off by default - turn them on ASAP
Windows Defender has several security settings, including some you need to switch on to get the utmost protection. Here's why.
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1w ago
What If Your Digital Footprint Could Shrink?
Get Surfshark One+ with Incogni for $91.99 (reg. $500.40) and cover VPN, alerts, antivirus, and data removal. The post What If Your Digital Footprint Could Shri
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1w ago
6 Best No-Log VPNs in 2026
Looking for the best anonymous (no-log) VPN in 2026? Check out our comprehensive list to find the top VPN services that prioritize anonymity and security. The p

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1w ago
7 Bug Bounty Mistakes That Cost Me Real Money
Lessons you only learn after missing payouts Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The OWASP Top 10 Isn’t a List of Bugs — It’s a List of Human Habits
For more than 20 years, the OWASP Top 10 has been guiding the world on the most critical web security risks. It started back in 2003, and… Continue reading on M
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Before You Send Logs to Gemini — Strip the PII First
All tests run on an 8-year-old MacBook Air. Android logs contain more than stack traces. User IDs. Email addresses. IP addresses. Phone numbers. Auth tokens tha
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
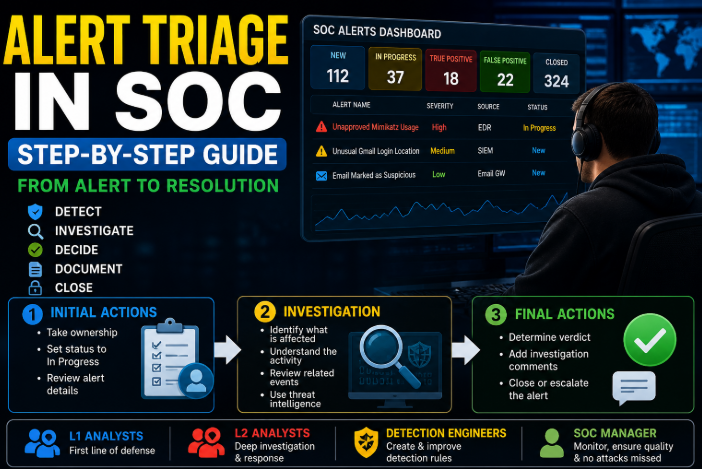
Alert Triage Process in SOC — TryhackMe
An alert is one of the most important parts of cybersecurity. Security teams use alerts to find suspicious or dangerous activity in a… Continue reading on Mediu

Dev.to · Rushikesh Kakadiya
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Quantum Threat Is Real — Meet QSafe PQC, a Post-Quantum Cryptography API (And We Need Beta Testers!)
> TL;DR: I built a Post-Quantum Cryptography API platform called QSafe PQC. It gives developers...

Dev.to · Paul Frol
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Split any file into a keyless block and a 128-bit key - in two bitwise operations
What if you could take any file — a photo, a database dump, a movie — and split it into two parts...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why Enumeration Is More Important Than Exploitation in Pentesting
Many beginners focus on exploits professionals focus on information. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Sonu Kumar: Navigating the 2025 Cybersecurity Landscape — Insights from Nepal’s Cloud Security…
As Sonu Kumar, a cybersecurity specialist deeply rooted in Nepal and passionate about securing digital frontiers, I’ve witnessed firsthand… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Secret Language of Search: Google Dorking
Imagine you are standing in the world’s largest library. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Polymorphic & Metamorphic Malware: The Shape-Shifting Threat Your Antivirus Can’t See
A deep dive into how modern malware evolves, evades, and why the old playbook of signature detection is quietly losing the war. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
I Wrote a Techno-Thriller About My Own Technology. Then I Gave It Away for Free.
Every piece of technology in “Trust No Agent” is real. The platform exists. The attacks are plausible. The book is free. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
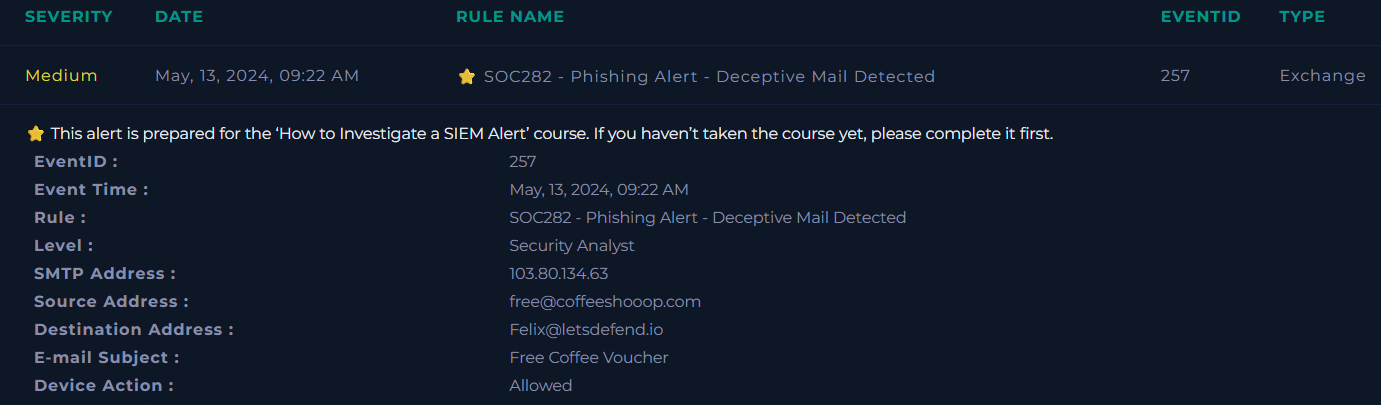
How I Investigated a Real Phishing Attack That Led to Malware Execution and C2 Communication
As a SOC Analyst , I recently investigated a phishing case on the LetsDefend platform that turned out to be far more serious than a simple… Continue reading on

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Swiss Chip in Russia’s Stealth Drone: How a $47 STMicroelectronics Controller Blew Open the…
A forensic autopsy of the October 2024 S-70 Okhotnik-B wreckage, the Western silicon inside it, and why Russia’s drone dominance was a… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why Data Privacy Is a Daily Commitment Not Just a Policy
As we step into a new month, it’s easy for businesses to focus on growth, targets, and new opportunities. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Liveness Detection Technology in Remote Identity Verification
The digital landscape has undergone a seismic shift, moving from physical handshakes to encrypted handshakes in less than a decade. As we… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
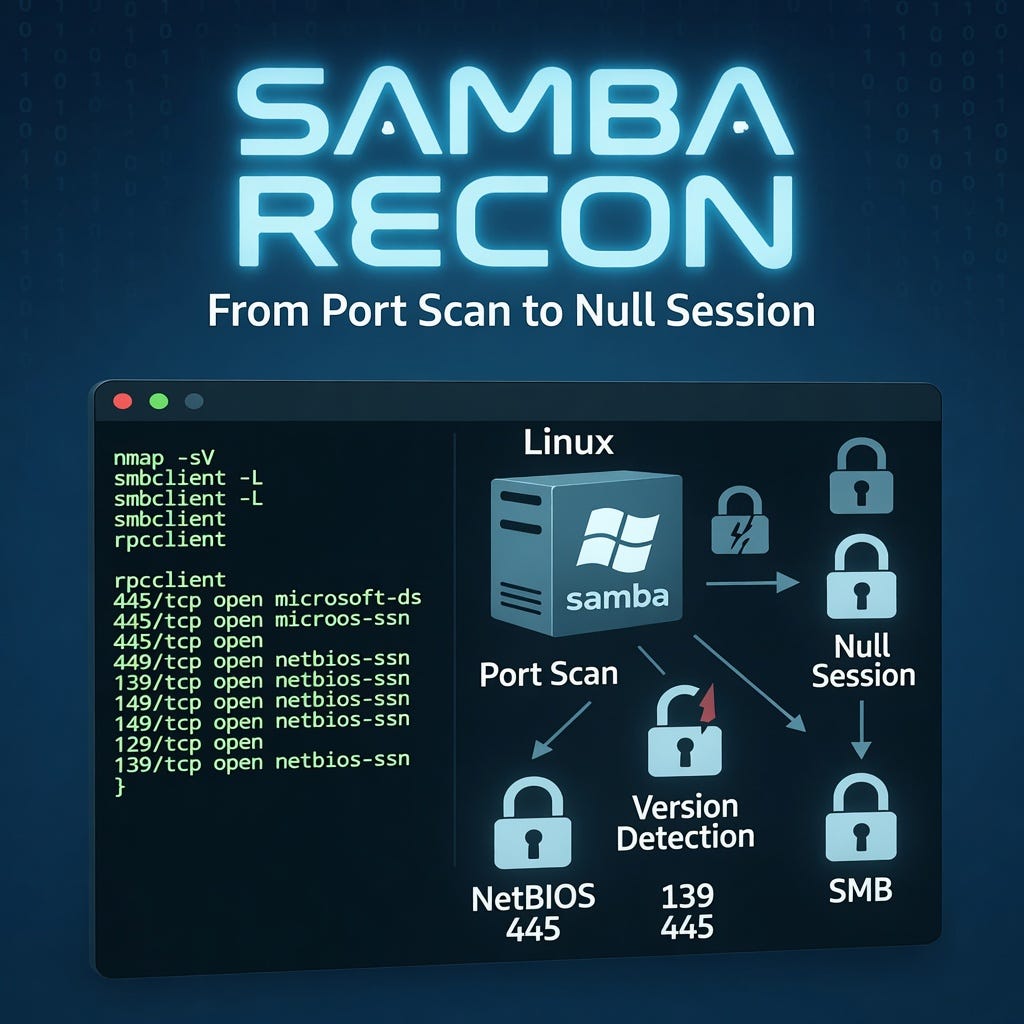
Exposing Hidden Server Secrets: A Practical Guide to Samba Reconnaissance
If you are diving into network security, ethical hacking, or system administration, you will inevitably run into Samba. It is the backbone… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Setting Up Snort 3 as an IDS
Intrusion Detection System (IDS) watches your actual traffic, matches it against known attack patterns, and alerts you when something… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Deepfake Çağında Kırmızı Tehdit
Red Team’ler İçin Aldatma, Kimlik Taklidi ve Yetki Aşımı Operasyonları Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Ethics of Pixel Tracking: Where Useful Analytics Become Digital Surveillance — Joseph Sides
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
TryHackMe | Detecting AD Credential Attacks | WriteUp
Detect Kerberoasting, AS-REP Roasting, LSASS dumping, DCSync, and NTDS.dit extraction in Splunk. Continue reading on T3CH »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
CyberDefenders — Insider Walkthrough
Olay İnceleme Raporu: İç Tehdit (Insider Threat) Vakası — “Karen” Analizi (CyberDefenders) Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
“Copy Fail”: The Most Alarming Linux Bug in a Decade
Intro Continue reading on Medium »
 DeepCamp AI
DeepCamp AI