📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 758 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13658)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsMedium · Programming
Medium · Cybersecurity
5d ago
5 Brutal Lessons I Learned After Failing My First OSCP Attempt (And How They Helped Me Pass the…
5 Brutal Lessons I Learned After Failing My First OSCP Attempt (And How They Helped Me Pass the Second) Continue reading on Medium »
Medium · Cybersecurity
5d ago
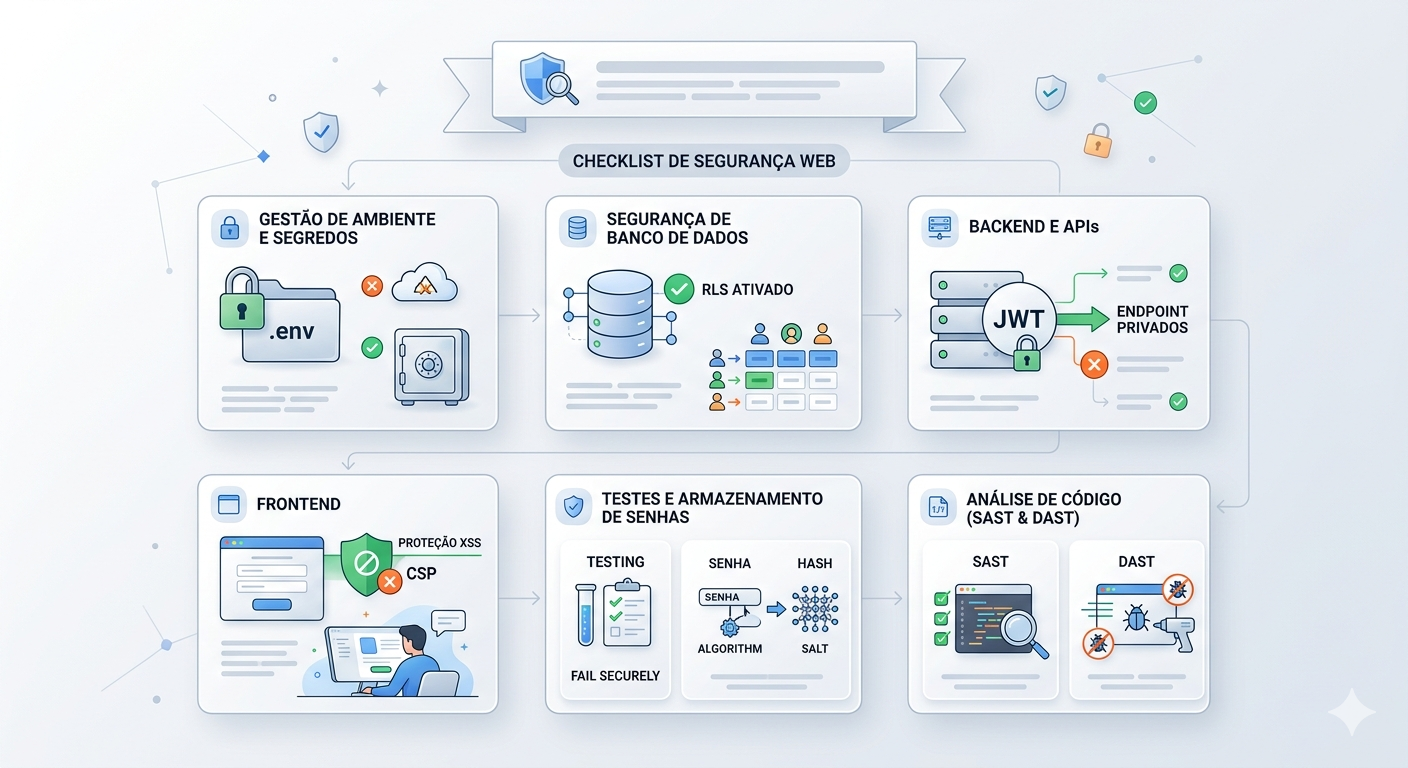
Não seja o próximo alvo: O Checklist mínimo de Segurança para aplicações Web
Na era da geração acelerada de código por IA, falhas de segurança básicas estão se tornando mais comuns do que nunca. Este guia prático… Continue reading on Med

Medium · Cybersecurity
5d ago
Mythos Found Bugs That 50 Million Security Tests Missed. Nobody Asked It To.
What Claude Mythos Preview reveals about the agentic coding era, and why the software we trust most may already be compromised. Continue reading on Data Science

Medium · Cybersecurity
5d ago
TryHackMe | AI Models & Data | WriteUp
Explore how data is fundamental to AI security, and the models which power it. Continue reading on T3CH »
Medium · Cybersecurity
5d ago
I Tried Every Major Cybersecurity Learning Platform. Here’s Why I Built Cybrixen Instead.
A founder’s honest take on what’s broken in cybersecurity education, and what we’re doing differently. Continue reading on Medium »

Medium · Cybersecurity
5d ago
RST TI Report Digest: 13 Apr 2026
Last week we processed 62 threat intelligence reports. Sharing a short summary of top10 of them with IoCs. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Police tracking 500M devices using AD
Citizen Lab reported that Hungarian law enforcement used ad data to track hundreds of millions of devices globally. Not backdoor. Just ad… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Let’s Defend: SOC287 — Arbitrary File Read On Checkpoint Security Gateway(CVE-2024–24919)
In this blog, we will analyze a critical alert generated in the Let’s Defend SOC environment(SOC287), triggered by activity associated… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
“Bug Bounty Bootcamp #33: IDOR Hunting — When Changing a Single Number Grants You Everyone’s…
You log in as user #1001. You change the URL to user #1000. Suddenly, you’re looking at someone else’s invoices, emails, and phone numbers… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Sudo Buffer Overflow: TryHackMe walkthrough
A tutorial room exploring CVE-2019–18634 in the Unix Sudo Program. Room Two in the SudoVulns Series. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
The Cyber Threat Triangle
A conceptual model for understanding cyber risk Continue reading on Medium »

Medium · Cybersecurity
5d ago
Oh My WebServer (THM) Tryhackme WriteUp Answer
Description : Can you root me? Continue reading on Medium »

Medium · Cybersecurity
5d ago
From Architect to Sentinel: Defending Your Python Applications Against Path Traversal
We’ve spent years building. We mastered data structures, engineered scalable systems, and deployed robust applications. We were the… Continue reading on Level U

Medium · Cybersecurity
5d ago
IAM Risks and Threat Detection: Why identity is the real attack surface in AWS
Most cloud attacks don’t start with exploitation. Continue reading on Medium »
Medium · Cybersecurity
5d ago
Got it You want a professional version of the article so it feels polished, credible, and ready…
Continue reading on Medium »

Medium · Cybersecurity
5d ago
Splunk: Complete set-up guide
This is a full step by step guide on how to set up the complete Splunk architecture (performed via the TryHackMe SOC lab room) Continue reading on Medium »

Medium · Cybersecurity
5d ago
AI Experience: o que o encontro da Nova8 Cybersecurity, Cequence e CISO’s Club mostrou sobre…
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Smart Cameras, Smarter Decisions: How Meraki MV Turns Video Into Actio
Security cameras have traditionally been passive devices — recording footage that sits untouched until an incident forces someone to scrub… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
This $100 Instagram Bug Proves Bug Bounty Is About Thinking, Not Complexity
Before I break this down — if you are trying to get into bug bounty hunting and want something actually useful, go check out hackthrough… Continue reading on Me

Medium · Cybersecurity
5d ago
Why Employee Security Failures Lead to Lawsuits: A Business Cybersecurity Risk Guide
You’re probably thinking your IT guy’s got this handled. He doesn’t. Continue reading on Medium »

Medium · Cybersecurity
5d ago
APT28 Just Turned Your Router Into a Spy — And OT Networks Are Next
The FrostArmada campaign is live, the FBI already moved, and your MikroTik or TP-Link router might already be compromised Continue reading on Medium »

Medium · Cybersecurity
5d ago
Mythic C2 Server — 105
Mythic Agents Overview Continue reading on Medium »

Medium · Cybersecurity
5d ago
We Tricked an AI Agent Into Sending Messages It Was Never Told To Send
How a simple Slack message exposed a dangerous flaw in how we trust AI agents with our digital identity Continue reading on Medium »

Medium · Cybersecurity
5d ago
CCDL2, CDSA and you
if you are reading this then that means i passed CCDL2 so i just wanted to share my story, exam experience, pros and cons of each exam and… Continue reading on
 DeepCamp AI
DeepCamp AI