📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 748 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13599)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
4d ago
Encryption Enforcement & Audit in AWS using Terraform
Overview Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Securing Autonomous Payments: Risk, Compliance, and Governance for AI Spend
Autonomous payments without governance become autonomous fraud. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Agentic Triage on Snowflake
The biggest bottleneck hitting security teams today isn’t the SIEM, it’s triage. Analysts are drowning in alerts, spending the bulk of… Continue reading on Snow
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
SOC Automation Lab Series 4
Now we will combine all of out tools and create an playbook on shuffler.io which is like an automation Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
I Investigated a Phishing Network That Has Been Running Since 2016 with 400+ Phishing Blogs and…
Before I start, just note that the full techinacal report containing all IOCs, redirect chain analysis and detection rules is available… Continue reading on Med

Medium · Cybersecurity
4d ago
Hybrid Operation: How Two “Rival” Hacking Groups Are Manufacturing a Cyberwar Against Armenia
As the June 2026 Armenian parliamentary elections approach, a sophisticated hybrid operation with the signs of cyberactivities, attacks… Continue reading on Med
Medium · Cybersecurity
4d ago
A Quick Note on Anthropic’s Project Glasswing and Claude Mythos
I missed last week’s newsletter as I was away, but Anthropic’s Project Glasswing and Claude Mythos have been impossible to ignore in the… Continue reading on Cy

Medium · Cybersecurity
4d ago
The “Mythos” of Control: Why We’re Cloaking the Network Before the AI Escapes
With the customers BlastWave talks to every day, AI threats come up periodically, raised by the OT geeks who have already embedded it into… Continue reading on
Medium · Cybersecurity
4d ago
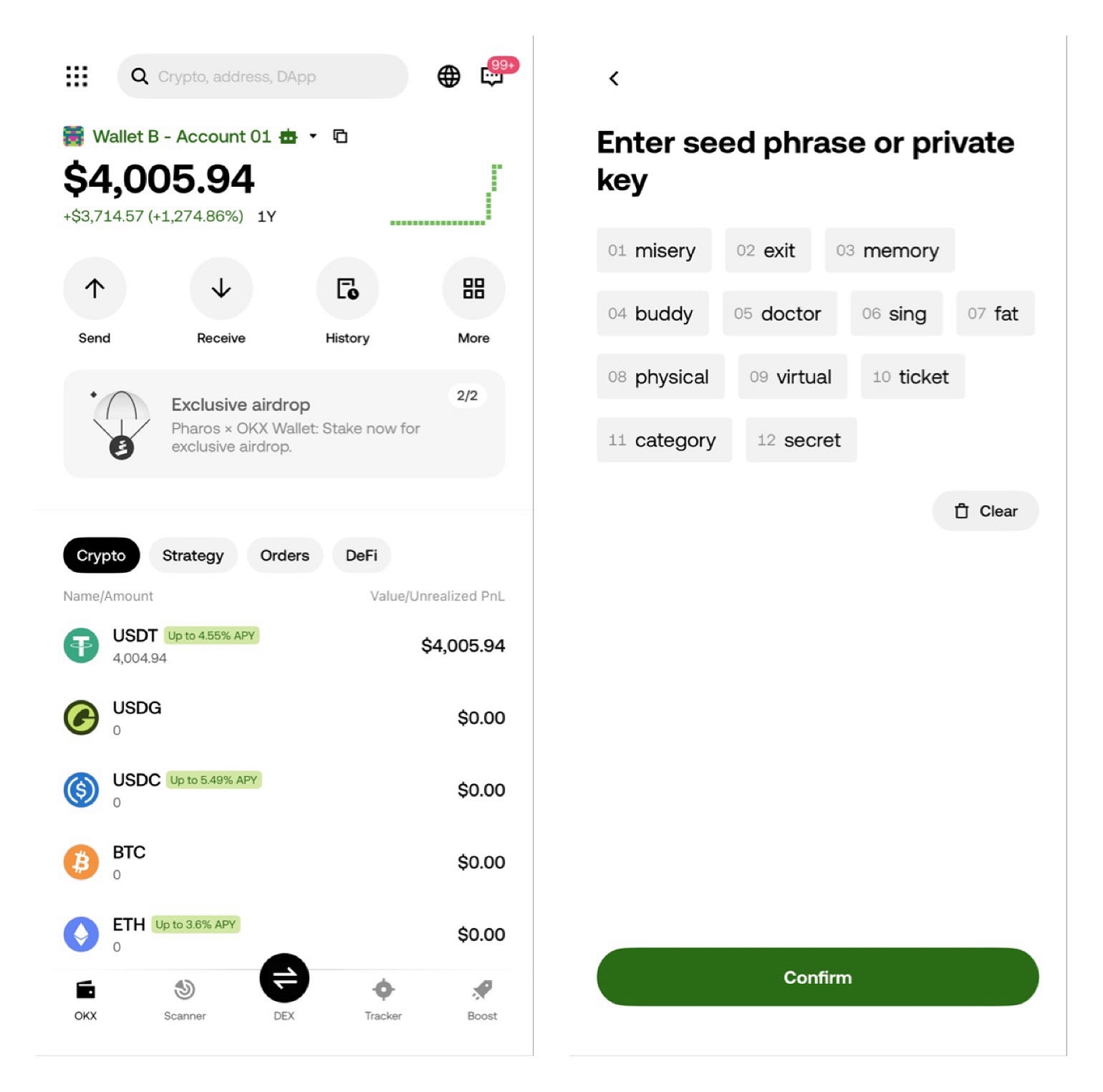
how can i withdrawing my 4,000 from Okx wallet to binance ?
12 seed phrase: misery exit memory buddy doctor sing fat physical virtual ticket category secret Continue reading on Medium »

Medium · Cybersecurity
4d ago
Best Small Business Firewalls in 2026: 7 Top Picks & Buyer’s Guide
Think of a firewall as the security guard at the entrance of your business. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
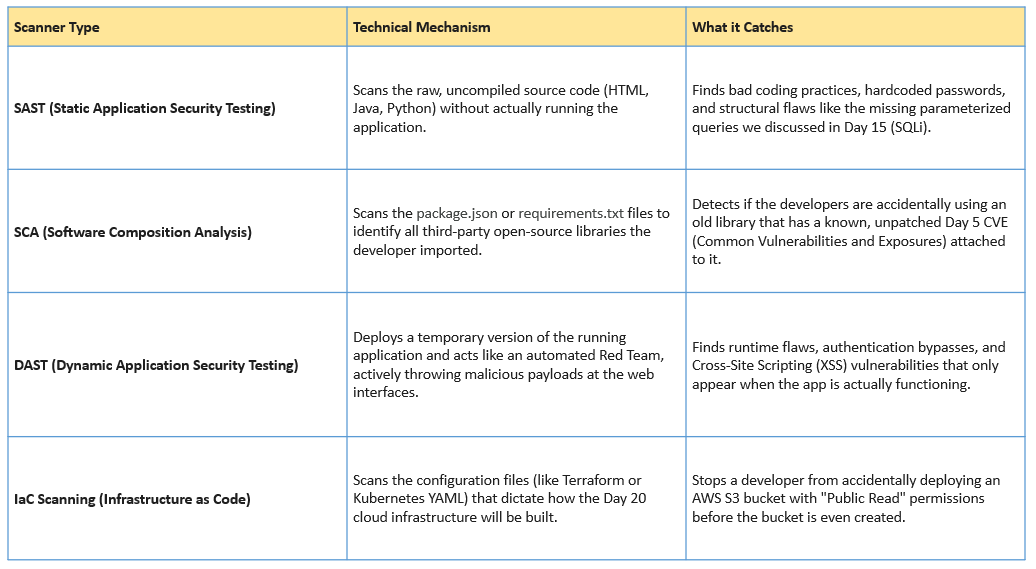
Day 21: Shifting Left — DevSecOps and the CI/CD Pipeline
Welcome to Day 21 of our 30-Day Cybersecurity Mastery series. Continue reading on Medium »

Medium · Cybersecurity
5d ago
Behind the Mask: Uncovering a Fake Amazon Security Alert Phishing Attack
Phishing Analysis Lab Questions: Continue reading on Medium »

Medium · Cybersecurity
5d ago
From Self-Doubt to eJPT: How I Found My Path in Cybersecurity
The Beginning: Self-Doubt, Curiosity, and No Direction Continue reading on Medium »

Medium · Cybersecurity
5d ago
How I poisoned an AI security assistant and built the code to prove it
A technical walkthrough of corpus poisoning and prompt injection against RAG-based SOCs, with real implementation code Continue reading on Towards AI »
Medium · Cybersecurity
5d ago
5 Brutal Lessons I Learned After Failing My First OSCP Attempt (And How They Helped Me Pass the…
5 Brutal Lessons I Learned After Failing My First OSCP Attempt (And How They Helped Me Pass the Second) Continue reading on Medium »
Medium · Cybersecurity
5d ago
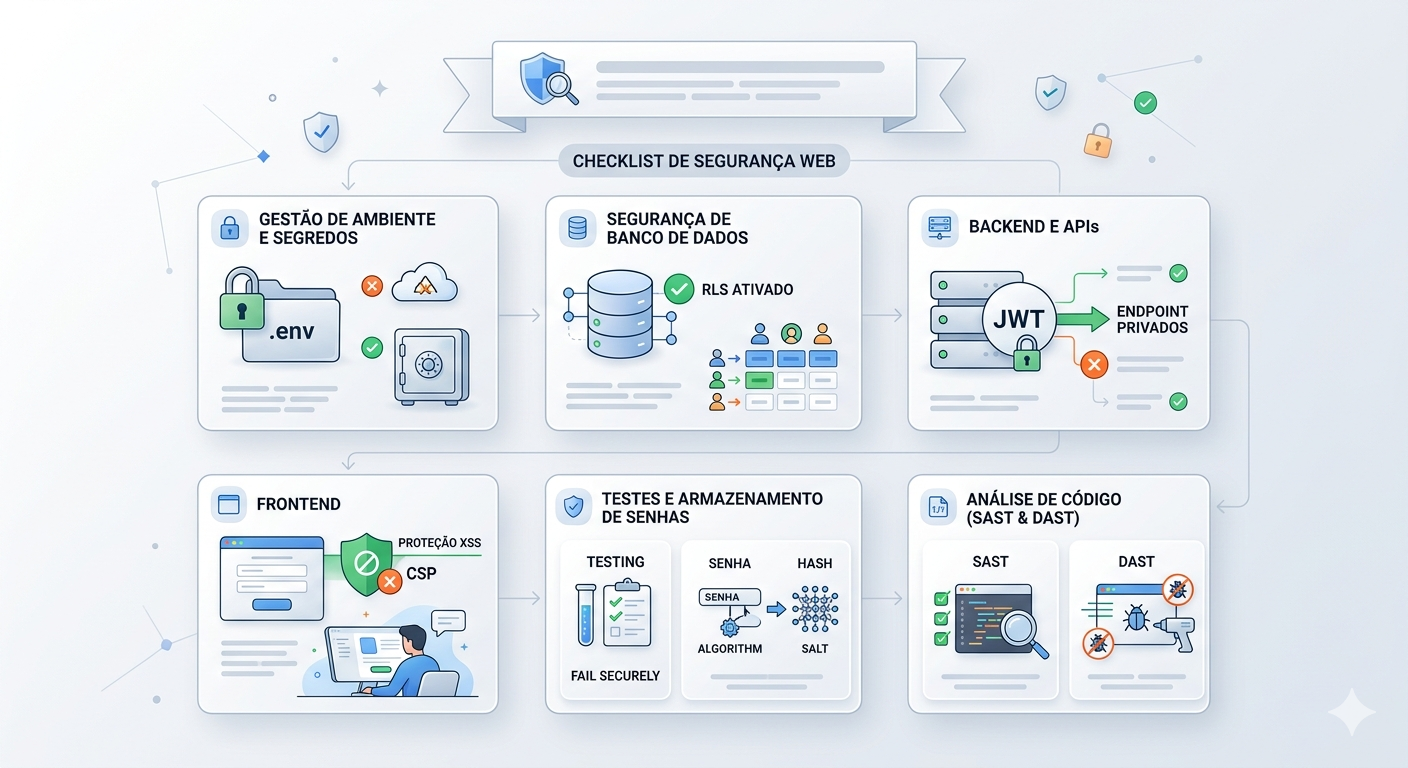
Não seja o próximo alvo: O Checklist mínimo de Segurança para aplicações Web
Na era da geração acelerada de código por IA, falhas de segurança básicas estão se tornando mais comuns do que nunca. Este guia prático… Continue reading on Med

Medium · Cybersecurity
5d ago
Mythos Found Bugs That 50 Million Security Tests Missed. Nobody Asked It To.
What Claude Mythos Preview reveals about the agentic coding era, and why the software we trust most may already be compromised. Continue reading on Data Science

Medium · Cybersecurity
5d ago
TryHackMe | AI Models & Data | WriteUp
Explore how data is fundamental to AI security, and the models which power it. Continue reading on T3CH »
Medium · Cybersecurity
5d ago
I Tried Every Major Cybersecurity Learning Platform. Here’s Why I Built Cybrixen Instead.
A founder’s honest take on what’s broken in cybersecurity education, and what we’re doing differently. Continue reading on Medium »

Medium · Cybersecurity
5d ago
RST TI Report Digest: 13 Apr 2026
Last week we processed 62 threat intelligence reports. Sharing a short summary of top10 of them with IoCs. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Police tracking 500M devices using AD
Citizen Lab reported that Hungarian law enforcement used ad data to track hundreds of millions of devices globally. Not backdoor. Just ad… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Let’s Defend: SOC287 — Arbitrary File Read On Checkpoint Security Gateway(CVE-2024–24919)
In this blog, we will analyze a critical alert generated in the Let’s Defend SOC environment(SOC287), triggered by activity associated… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
“Bug Bounty Bootcamp #33: IDOR Hunting — When Changing a Single Number Grants You Everyone’s…
You log in as user #1001. You change the URL to user #1000. Suddenly, you’re looking at someone else’s invoices, emails, and phone numbers… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Sudo Buffer Overflow: TryHackMe walkthrough
A tutorial room exploring CVE-2019–18634 in the Unix Sudo Program. Room Two in the SudoVulns Series. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI