Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,379 reads from curated sources
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
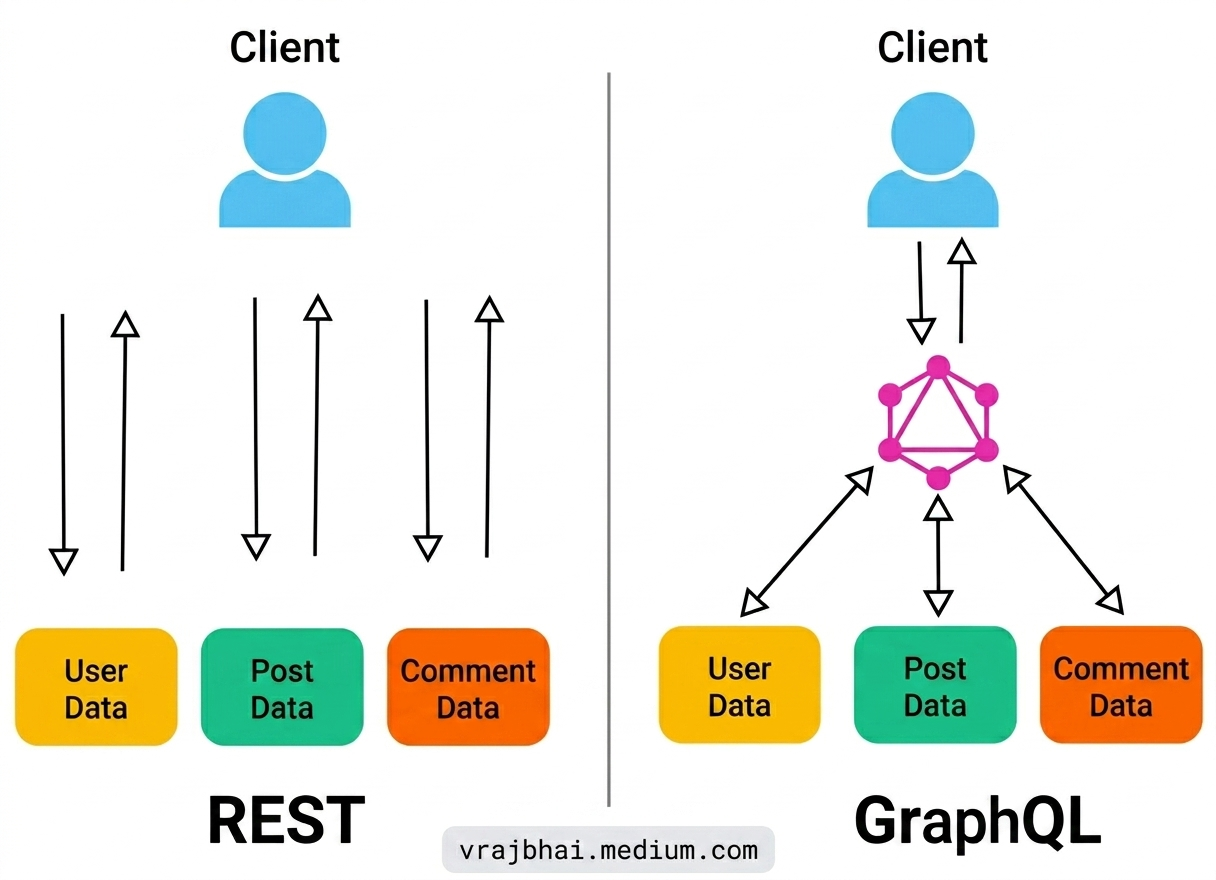
GraphQL API Vulnerability: From Lab Swagger to Battle-Ready
GraphQL is quickly becoming the standard for modern APIs, but as the saying goes, “with great power comes great responsibility” — or in… Continue reading on Med
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
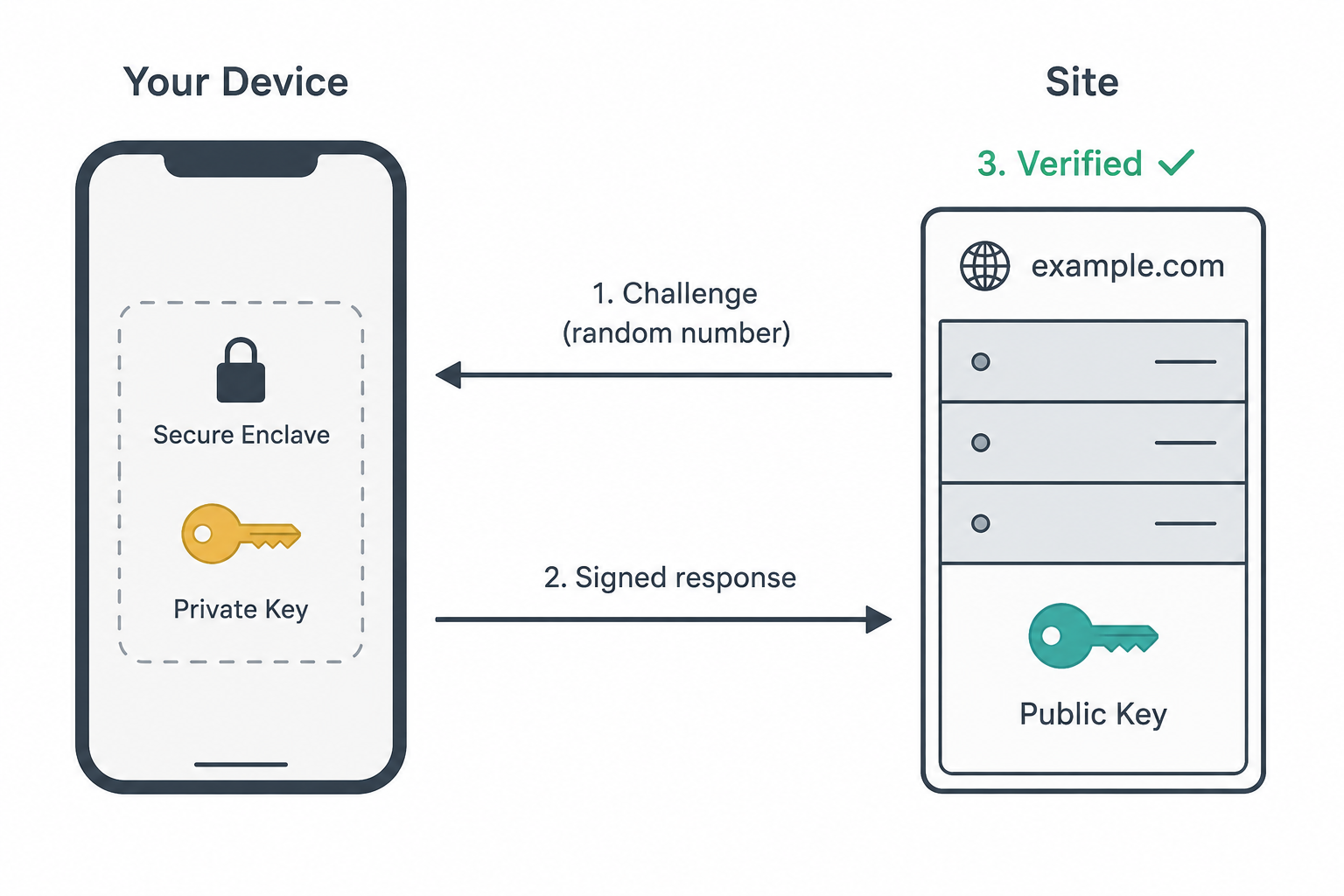
What the heck is a Passkey? (And why do they make my life so much easier?)
The actual cryptography, the actual reason phishing fails, and the rare truce between Apple, Google, and Microsoft. Continue reading on Medium »

Dev.to · Raju Dandigam
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Your AI Agent Dockerfile Might Be Leaking Secrets
Learn how to use Docker Build Secrets to prevent credential leaks in Node.js AI applications

Dev.to · Anonymous Security Researcher
🔐 Cybersecurity
⚡ AI Lesson
4d ago
The Browser Is Not a Security Boundary
Photo by Zulfugar Karimov on Unsplash Modern web applications increasingly push business logic...

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
4d ago
‘One Time Restart’—Microsoft Changes Windows After 15 Years
Microsoft starts expiring critical Secure Boot certificates in just 2 weeks.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
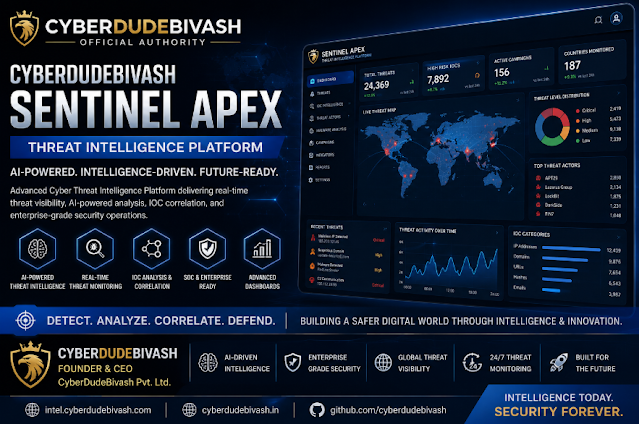
CYBERDUDEBIVASH SENTINEL APEX — AI-Powered Cyber Threat Intelligence Platform for Modern Enterprise…
Daily Threat Intel by CyberDudeBivash Zero-days, exploit breakdowns, IOCs, detection rules & mitigation playbooks. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Ubuntu Blocked One Door. Dirty Frag Found Another
A Linux kernel bug, a blocked path, and a painful reminder that attackers do not need every door open. They only need one. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
AltaySec ile Geleceğin Siber Güvenlik Ekosistemi
AltaySec; siber güvenlik eğitimleri, yapay zeka güvenliği, phishing simülasyonları ve veri koruma çözümleri geliştiren yerli ve milli bir… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
CRA Technical Documentation: Complete Checklist for Manufacturers
Everything your engineering team needs to build an Annex VII-compliant technical file before the December 2027 deadline. Continue reading on Medium »
Medium · Machine Learning
🔐 Cybersecurity
⚡ AI Lesson
4d ago
The Best Bug Bounty Skill Isn’t Hacking… It’s Pattern Recognition
How I started finding vulnerabilities faster without learning new exploits Continue reading on Level Up Coding »
Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4d ago
The Best Bug Bounty Skill Isn’t Hacking… It’s Pattern Recognition
How I started finding vulnerabilities faster without learning new exploits Continue reading on Level Up Coding »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
The Best Bug Bounty Skill Isn’t Hacking… It’s Pattern Recognition
How I started finding vulnerabilities faster without learning new exploits Continue reading on Level Up Coding »

Dev.to · Maicon Ribeiro Esteves
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Inner Warden: A Lightweight Open Source eBPF EDR for Linux that Actually Blocks Attacks
Inner Warden: an autonomous eBPF security agent that fights back Most security tools only...

Dev.to · Mahdi SHamlou | مهدی شاملو
🔐 Cybersecurity
⚡ AI Lesson
4d ago
OWASP Top 10 for Developers (2026 Edition) — How to Actually Fix the Most Dangerous Web Vulnerabilities
Hi, Mahdi Shamlou here. In my last article (What Is a Sandbox? How to Safely Run and Analyze Any...

Dev.to · Mahdi SHamlou | مهدی شاملو
🔐 Cybersecurity
⚡ AI Lesson
4d ago
What Is a Sandbox? How to Safely Run and Analyze Any Unknown .exe
Hi, Mahdi Shamlou here. In this guide, I explain how malware analysis sandboxes work — from isolating...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Practical Zero Trust: How to Secure What Actually Matters
Zero Trust is everywhere. Every vendor mentions it, and every Board deck has a slide on it. Continue reading on Medium »

Hackernoon
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Cybersecurity in 2026 and Beyond: Trends Everyone Should Know
Cyber threats are growing faster than the workforce defending against them — 78% of organizations lack the in-house skills they need. Identity and Access Manage

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Fluffy
Machine Information As is common in real life Windows pentests, you will start the Fluffy box with credentials for the following account… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
The Age of Self-Building Systems and the Rise of Self-Devouring Systems
When Enterprise Ecosystems Evolve Faster Than Governance Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Upcoming 2026 Cybersecurity Conferences & Events to Attend
Top Worldwide Cybersecurity Events to Attend in 2026. Continue reading on CodeToDeploy »
Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Why Most Bug Hunters Miss the Obvious Vulnerabilities
Because they’re too busy looking for complex ones. Continue reading on System Weakness »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Why Most Bug Hunters Miss the Obvious Vulnerabilities
Because they’re too busy looking for complex ones. Continue reading on System Weakness »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Fail2Ban — a simple tool that can improve your server security
Fail2Ban is a powerful service that helps protect your server by automatically blocking suspicious or malicious activity. It monitors logs… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Copy Fail: Ketika 732 Byte Bisa Membuat Siapa Saja Jadi Root di Linux
Copy Fail: Ketika 732 Byte Bisa Membuat Siapa Saja Jadi Root di Linux Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
# The Genesis of KYXGO TECHNOLOGY: Redefining Digital Logic and Security
By Aditya Rai, Founder & CEO Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Why Small Businesses Are Easy Targets for Scammers?
Most people think scammers only target large companies or wealthy individuals. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Dead Drop C2 Channels
How adversaries weaponize public platforms — pastebin sites, social media, even Google Docs — to hide command-and-control traffic in plain… Continue reading on

Dev.to · lu1tr0n
🔐 Cybersecurity
⚡ AI Lesson
4d ago
FreeBSD parcha CVE-2026-7270: escalada local a root vía execve()
Un bug de precedencia de operadores en el kernel de FreeBSD permite a usuarios sin privilegios obtener root vía execve(). Afecta a todas las versiones
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
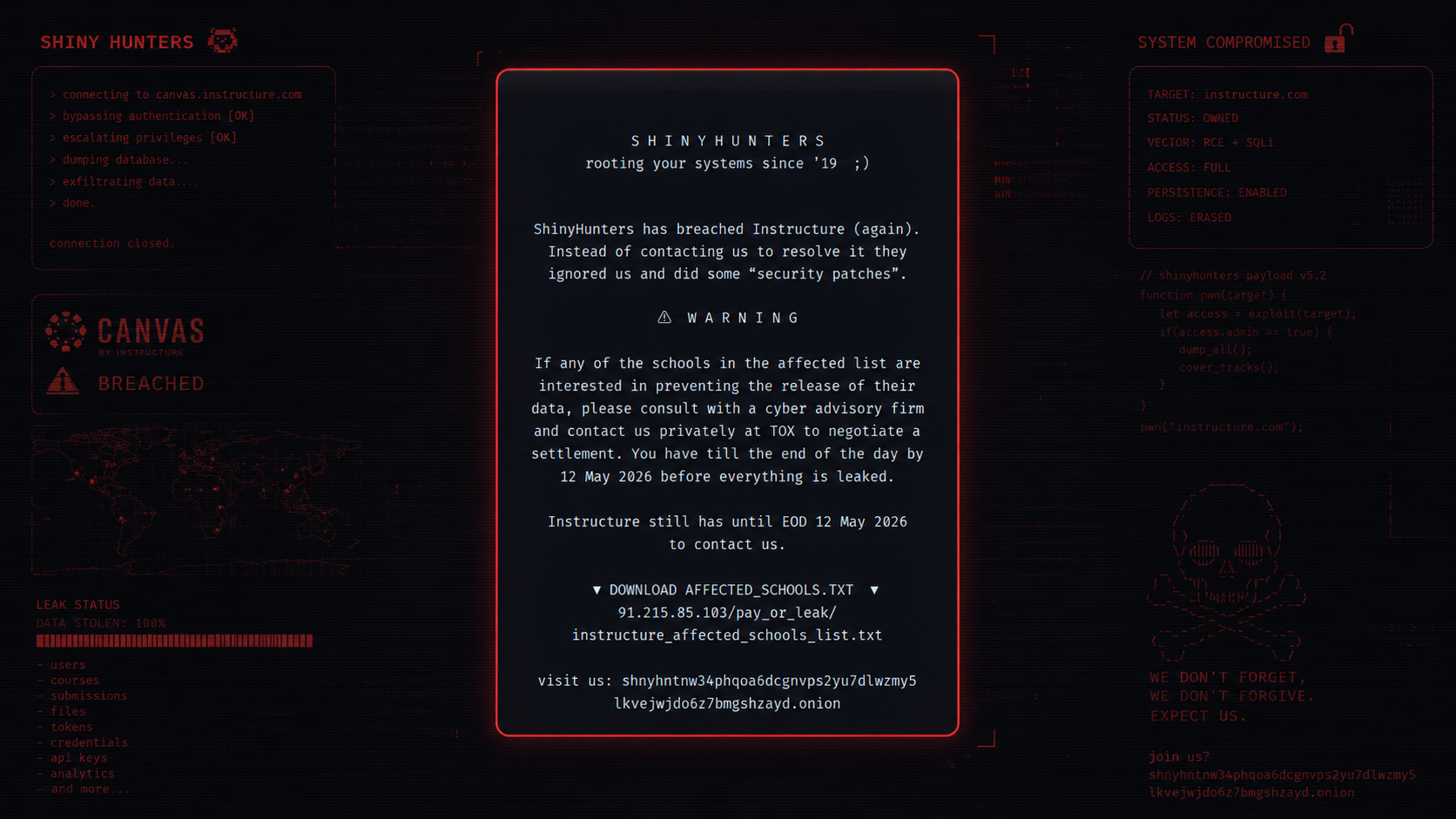
What ShinyHunters Just Did to Canvas Should Terrify Every SaaS‑Dependent Organization
Most security teams still operate as if the perimeter is their network. ShinyHunters just reminded 330 schools and every company watching… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Cyber Regulation Made Us More Auditable. Did It Make Us More Defensible?
After decades of frameworks, certifications and audits, the evidence tells a more uncomfortable story than we usually admit. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
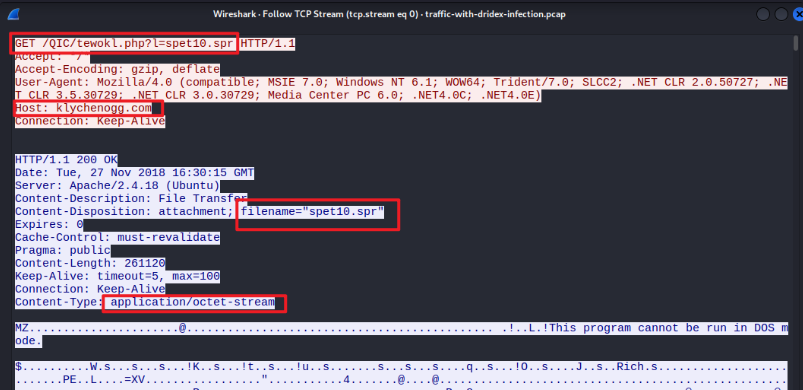
Network Analysis: Malware Compromise — BTLO Lab Writeup
From Inbox to Infection: Hunting Ursnif and Dridex in a SOC Lab (Difficulty level: Medium) Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Names Are A Security Debt We Can No Longer Afford
Why do we need to give our operating systems our name? Think about it. We give them a username and a password. Are those not sufficient… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Reducing False Positives & Building High-Fidelity Detection Engines
Threat detection has crossed an inflection point. With 86% of security teams spending over a week to ship a single detection rule, and 63%… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Cooctus Stories (THM) Tryhackme Writeup Answer
Description : This room is about the Cooctus Clan Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
DDoS Clearing House — A Dutch Model for Defense in the Digital Age
A Distributed Denial of Service (DDoS) attack is a malicious attempt to disrupt the normal traffic of a target server, service, or network… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
How Attackers Abuse Active Directory's Kerberos, By an Attacker (Part I)
This is the complete, comprehensive deep dive behind the scenes for how the Kerberos protocol is abuse by attackers in Active Directory. Continue reading on Med

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
4d ago
TCM Practical AI Pentest Associate (PAPA) Review: My Honest Experience (2026 — English Version)
My Experience with the Practical AI Pentest Associate (PAPA) Certification by TCM Security Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4d ago
Day 25: SIEM Query Basics (KQL)
Today I focused on one of the most important skills in SOC work: searching logs efficiently inside a SIEM. Whether the platform uses KQL… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
These 30+ Tools HACKERS Use Daily (Most Are FREE!)
Nmap, Burp Suite, Wireshark, Metasploit, Aircrack‑ng and 25 more. Stop hunting blindly here’s the real daily toolkit Continue reading on ILLUMINATION »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
The 30-Minute Breach: How an Attacker Went from Port Scan to Data Exfiltration on a Cloud Server
One unpatched vulnerability. Forty-five malicious workflows. Thirty minutes. Here’s how I reconstructed the whole thing. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Hackeo masivo de portales Canvas impulsa nueva campaña de extorsión del grupo ShinyHunters
Además, otra vez un zero-day en Linux permite escalar a root, hackeo al sistema ferroviario de Taiwán, Chrome descarga un modelo de IA sin… Continue reading on

Dev.to · Eric Rodríguez
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Day 78: Hunting Silent IAM Bugs & Securing DynamoDB
aws #serverless #react #webdev published: true date: "2026-05-08 21:30:00 UTC" Today was...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
What I Learned Building Azure Governance From Scratch
A few weeks ago I started a personal lab project to learn Azure Policy properly. The premise was a Wild West subscription, no tagging… Continue reading on Mediu
Medium · LLM
🔐 Cybersecurity
⚡ AI Lesson
5d ago
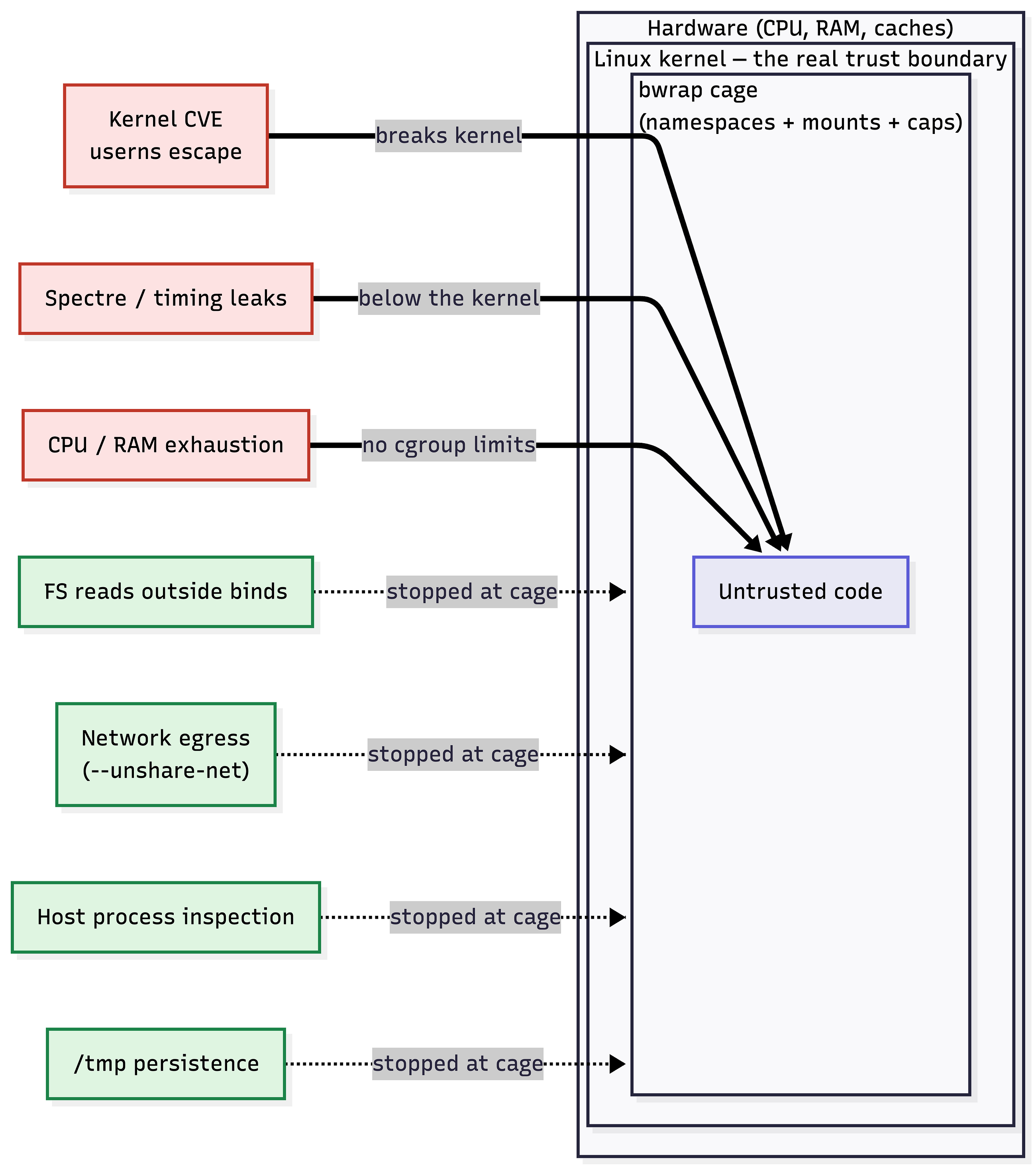
Sandboxing untrusted code with Bubblewrap
Sandboxing is about running code you don’t fully trust without giving it the run of your machine. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
WebDAV Zafiyeti ve Sudo Yanlış Yapılandırması ile Sisteme Sızma | CTF Çözümü
Bugün sizlerle çözmüş olduğum keyifli bir CTF makinesinin adımlarını paylaşacağım. Bu makinede temel bilgi toplama süreçlerinden… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
What Actually Happens When You Click “I Agree” Without Reading
Most people do it in under two seconds. A pop-up appears, something asks for permission, and you click “I agree” just to move on. It feels… Continue reading on

The Next Web AI
🔐 Cybersecurity
⚡ AI Lesson
5d ago
A manual pentest costs 50,000 dollars. Intruder built an AI that does it in minutes.
A manual penetration test costs between 10,000 and 50,000 dollars. It takes weeks to schedule, days to execute, and produces a report that is out of date before

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Responsible Disclosure Case Study: Critical Authorization, Identity and Credential-Exposure Risks…
Executive Summary Continue reading on Medium »
 DeepCamp AI
DeepCamp AI