Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,379 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
HSC RTV CTF — Unknown Architect (Reversing — 200 pts)
This was an easy one. The title gives the hint of finding the right architecture in which the binary should be run on. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
THME Notes — Part 1
Cybersecurity 101 > Windows and AD fundamentals > Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
AI Hacking for Beginners: A Five-Article Series
Article 4: How to Pentest an AI System Without Getting Lost Continue reading on MeetCyber »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
AI-Powered Zero-Day Attack: A Turning Point for Cybersecurity
Keywords: Cybersecurity, Zero-Day, AI, Threat Intelligence, Zero Trust Continue reading on Medium »

Dev.to · Zil Norvilis
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Stop Leaking API Keys: Managing Secrets in Kamal 2
I see developers make a mistake that can ruin their entire month. They are building a new Rails...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
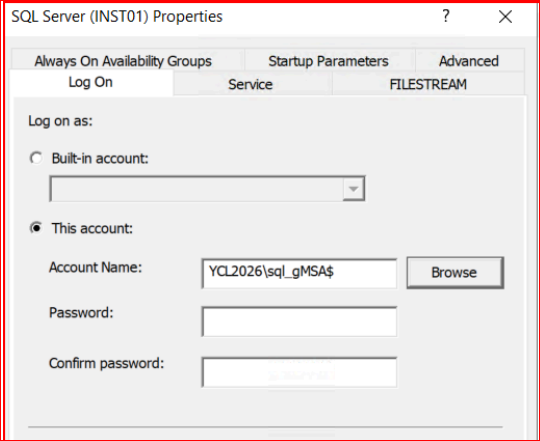
SQL Server Altyapısında gMSA Dönüşümü Nasıl Yapılır
Group Managed Service Accounts (gMSA), Windows Server 2012 ile tanıtılan, domain düzeyinde yönetilen özel bir hesap türüdür. Standart… Continue reading on Mediu
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
DeepSeek V4 Just Changed the Game Again — Here’s Why It Actually Matters
It won’t replicate the shock of R1. But what it signals is more consequential Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
2d ago
After The Canvas Hack, Here’s What Students And Colleges Should Do Next
While students change passwords and watch out for imposter scams, schools should start scrutinizing their third party providers and practice for the next hack.

Dev.to · endoflife-ai
🔐 Cybersecurity
⚡ AI Lesson
2d ago
I launched a free software end-of-life tracker — here's why it matters more than most people realize
Running legacy software isn't just a technical debt problem. It's a security emergency that most...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Windows Event Viewer Rehberi: SOC Perspektifinden Windows Log Analizi
Windows işletim sistemleri, kullanıcı aktivitelerinden sistem servislerine, güvenlik olaylarından uygulama hatalarına kadar birçok işlemi… Continue reading on M

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Your Website Is Leaking Data Right Now
Here’s How to Plug the Holes in 15 Minutes Continue reading on Webmaster Nexus »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Your Website Is Leaking Data Right Now
Here’s How to Plug the Holes in 15 Minutes Continue reading on Webmaster Nexus »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
WireGuard on macOS: Multi-Config Setup with Leak Protection
The problem: you want to use two WireGuard VPNs simultaneously on a Mac: one for work and another personal VPN for AI tools, browsing and… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
KALI LINUX SETUP IN VMWARE
A simple guide to installing Kali Linux in VMware Workstation for cybersecurity practice. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Scapy ile DeauthPacketDetector Pojesi
Etrafınızdaki bir ağda deauth saldırısı yaşanıyor olabilir — ve bunu Python ile 50 satırda tespit edebilirsiniz. Python’ın derinlemesine… Continue reading on Me

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Fragmented Cyber Risk Transfer Is Changing Board Oversight
Cyber risk transfer is fragmenting, forcing boards to rethink cyber oversight, incident response, executive liability, and insurance gaps.
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Can hackers break encrypted USB drives? I tried to find out
The Kingston IronKey Locker+50 G2 offers a high level of data security and several unique features to deter hackers.

Dev.to · CVE Reports
🔐 Cybersecurity
⚡ AI Lesson
2d ago
CVE-2026-27478: CVE-2026-27478: Authentication Bypass via Dynamic JWKS Discovery in Unity Catalog
CVE-2026-27478: Authentication Bypass via Dynamic JWKS Discovery in Unity...

Dev.to · lu1tr0n
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Langflow CVE-2026-33017: 20 horas entre el advisory y el RCE masivo
Un CVSS 9.8 en Langflow pasó del advisory a explotación masiva en honeypots en 20 horas, sin PoC público.

Dev.to · Shrijith Venkatramana
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Secure Your Go Apps Before Production Does It For You
Hello, I'm Shrijith Venkatramana. I'm building git-lrc, an AI code reviewer that runs on every...

Dev.to · CVE Reports
🔐 Cybersecurity
⚡ AI Lesson
3d ago
GHSA-MHWJ-73QX-JQXM: GHSA-MHWJ-73QX-JQXM: Prototype Pollution in @theecryptochad/merge-guard via deepMerge()
GHSA-MHWJ-73QX-JQXM: Prototype Pollution in @theecryptochad/merge-guard via...

Dev.to · Shubham Bhamare
🔐 Cybersecurity
⚡ AI Lesson
3d ago
This Is How I Could Have Reactivated Your Instagram Account Without Your Knowledge
In this write-up, I have shared the story of an Instagram bug where deactivated account could be...

Dev.to · Adrian Alexandru Stinga
🔐 Cybersecurity
⚡ AI Lesson
3d ago
FROM TOR TO TRACEABLE: WHY 90% OF 'ANONYMOUS' Threat actors ARE ONE MISTAKE AWAY FROM EXPOSURE
After spending ~15 years monitoring underground ecosystems, I've observed a pattern so consistent it...

Dev.to · CVE Reports
🔐 Cybersecurity
⚡ AI Lesson
3d ago
CVE-2026-40217: CVE-2026-40217: Remote Code Execution via Sandbox Escape in LiteLLM
CVE-2026-40217: Remote Code Execution via Sandbox Escape in LiteLLM Vulnerability ID:...
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The patching treadmill: Why traditional application security is no longer enough
Find-and-fix security once made sense, but AI-assisted development, continuous deployment, and exploding vulnerability backlogs are changing the rules. The old
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Beyond the cleanup job: Redefining application security for the modern enterprise
Secure-by-design is no longer just a developer concern. Enterprise leaders must treat application security as a board-level responsibility, with accountability,
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Stopping bugs before they ship: The shift to preventative security
Secure software starts before coding begins. Threat modeling, safer defaults, dependency hygiene, and developer workflow guardrails can help prevent vulnerabili

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The Cybersecurity Budget Nobody Approves Until the Breach
Why hospitals keep treating cybersecurity like an expense until it becomes the most expensive emergency in the building Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Ağda Ne Var? Kali ile İlk Keşif
Öğrenerek Yazıyorum #1 Continue reading on Medium »

Dev.to · taekim34
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Delete the Vercel Claude Code Plugin. Here's Why I Did.
TL;DR The Vercel Claude Code plugin creates a permanent device UUID on your machine the...
TechCabal
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Three of Nigeria’s biggest banks lost $1.56 million to fraud in 2025
Nigeria's biggest banks lost $1.56 million to fraud in 2025. While incidents fell, fraudsters are extracting more per attack as digital payments scale.

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
3d ago
‘Signifcant Threat’—Billions Of Gmail Users At Risk From Google Gaffe
New research has confirmed that almost every individual with a Gmail account is at significant risk from dangerous Google security flaw—what you need to know.

Dev.to · onyks
🔐 Cybersecurity
⚡ AI Lesson
3d ago
How I fixed network state corruption in my Linux Tor proxy
Most transparent proxy scripts share a fatal flaw: if they crash, they take your system's network...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Customer-Driven AI CTI Project Template. Part 1: Foundations
From pure CTI to hands-on detection engineering with strict validation gates Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Threat Intelligence: From Data to Decision in Cybersecurity Operations
How organizations transform raw threat data into actionable security decisions Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Moving From a Managed WAF to One We Actually Owned
A practical account of evaluating, proof-of-concepting, and migrating 100+ web assets to Imperva over four months, without taking down a… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Bypassing Stack Canaries: Your Next Step in Exploit Development (2025)
Tags: cybersecurity exploit-development stack-canary buffer-overflow format-string binary-exploitation ethical-hacking ctf infosec… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
LetsDefend: SOC141 — Phishing URL Detected | Event ID 86
Today, we will be stepping into the shoes of a SOC Analyst to investigate and contain the SOC141 — Phishing URL Detected alert on the… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The Identity Crisis: Why 2026 is the Year We Stop Trusting Our Eyes
I remember the first time I saw a deepfake that actually worked. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Defense in Depth
Introduction to Defense in Depth Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
The Illusion of Deletion: When Companies Say Your Data Is Gone, How Do You Know?
We live in an age where companies increasingly promise users more control over their personal data. Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Google And Microsoft Warn Passkeys May Not Stop Hackers
Your passkey alone is not enough — here's what you must do to secure your accounts.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
How I Found Unlimited Account Creation Vulnerability Due to Improper Access Control
A deep dive into a registration logic flaw that allowed mass account creation without email verification. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Why I’m Not Switching My VPN: A Deep Dive into Digital Sovereignty
In 2026, the internet is faster, smarter, and unfortunately, more intrusive than ever. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
HackTheBox: Campfire-1 Sherlock Walkthrough
Detecting Kerberoasting Activity: Correlating Kerberos Events, PowerShell Logs, and Prefetch Artifacts Continue reading on Medium »

Dev.to · Pedro Tolvo
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Fixing NVIDIA BadTLP PCIe Freezes on Linux - or an ASUS TUF gaming laptop odyssey
Preface Firstly, I truly hope this little article could help someone with similar problem....
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
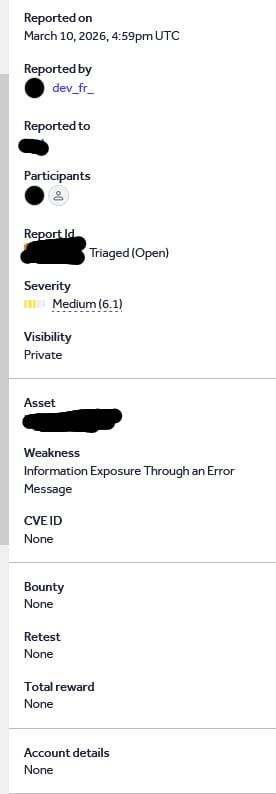
Stack Trace Exposure via Malformed Authorization Header
Weakness: Information Exposure Through an Error Message Severity:Medium (6.1) Status: Triaged (Open) — Fix Pending Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3d ago
Exposed Database Dump via Directory Listing on ETH Zurich Infrastructure
Weakness:Sensitive Information Disclosure / Improper Access Control Severity: High Status: Resolved Program: Responsible Disclosure… Continue reading on Medium
 DeepCamp AI
DeepCamp AI