Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,422 reads from curated sources
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
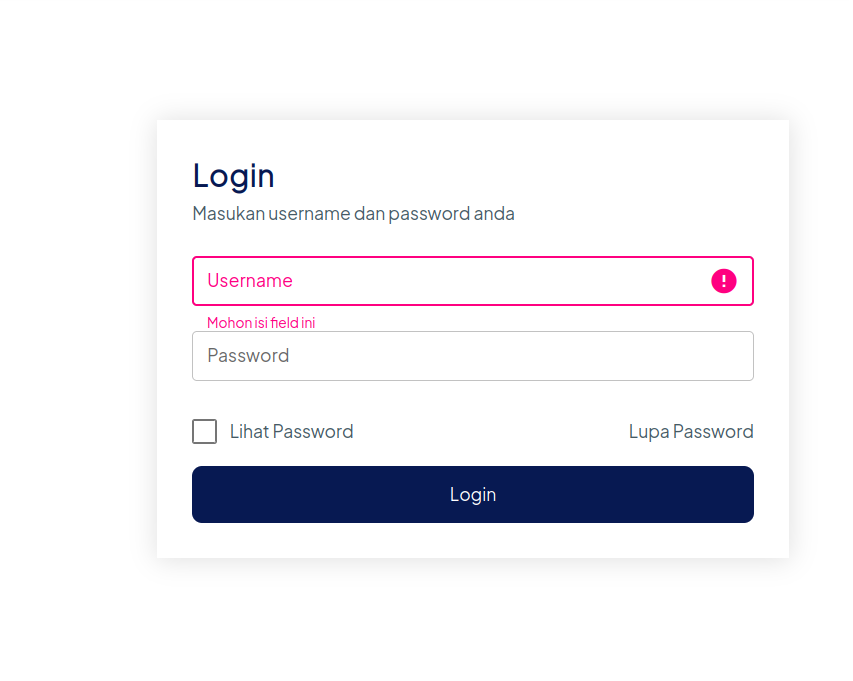
Authentication Testing
4.4.5 Testing for Vulnerable Remember Password Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Hidden Privacy Risk of Online File Converters
You’ve probably done it a hundred times. Upload a PDF, convert it, download the result. Takes 10 seconds. You move on with your day. Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Authentication Security Audit: Testing the Resilience of Web Applications Based on the OWASP WSTG…
4.4.5 Testing for Vulnerable Remember Password Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Tokenomics Exploits: When Design Becomes an Attack Vector
Why the most dangerous crypto vulnerabilities aren’t in the code they’re in the incentives Continue reading on Coinmonks »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Cisco Notes Networking basics — Module 5:Communication principles.
Communication Protocols — Communication in our daily lives takes many forms and occur in many environments. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Hidden Art of Speedrunning Reality: Where Glitches Become Skill
Speedrunners do not play games the way they were designed. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Axios CVE-2025–62718: The Silent SSRF Bug That Could Be Hiding in Your Node.js App Right Now
How a simple hostname comparison flaw in Axios can let attackers bypass your proxy protection entirely and what to do about it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Ethical Hacking Summer Internship for Freshers with Live Projects
What is Ethical Hacking? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
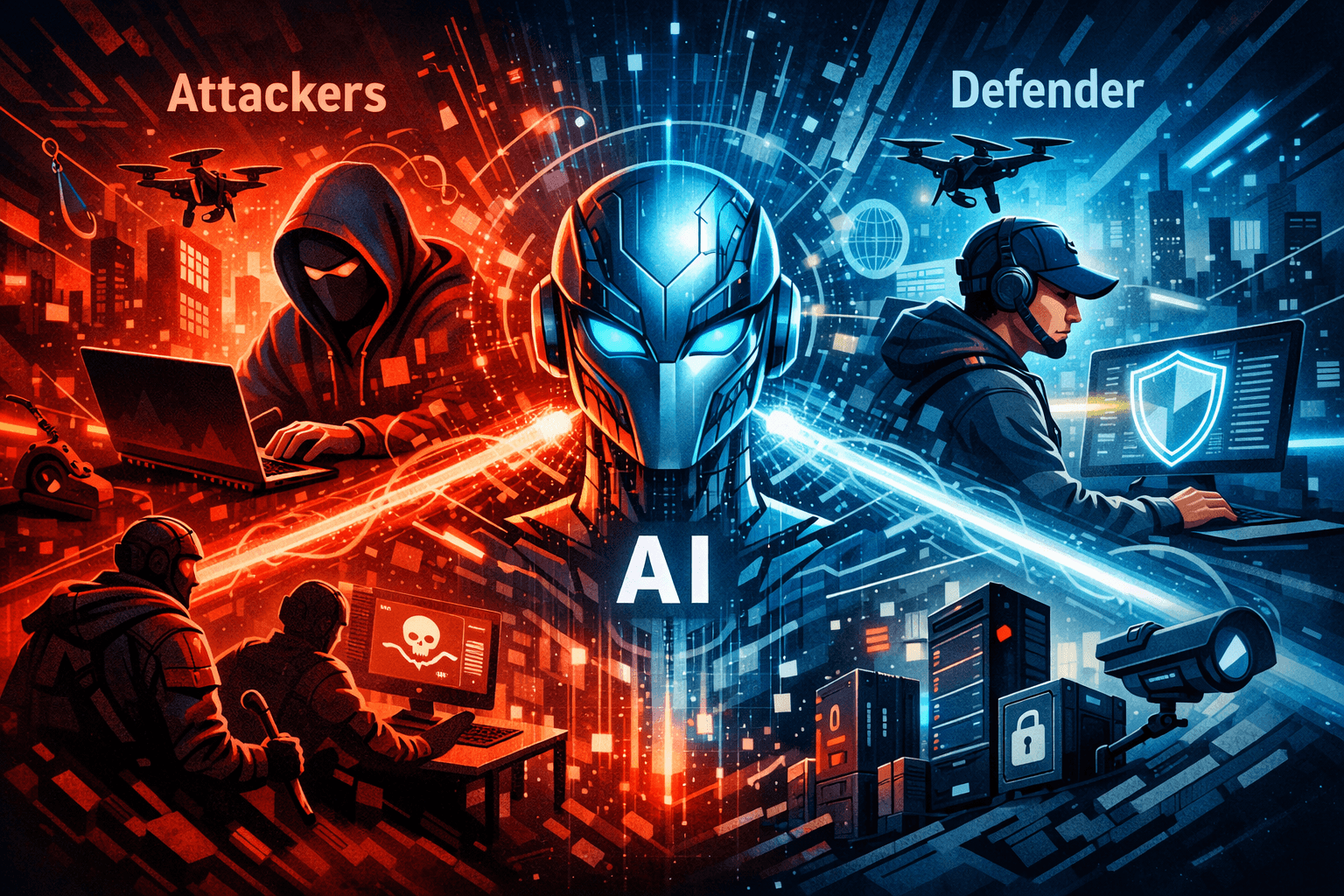
AI Powered Cybersecurity in 2026: Defending Against Next Generation Threats
As cyber threats become more advanced and frequent, traditional security methods are no longer enough to protect modern digital systems. Continue reading on Med

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Anthropic Built an AI That Can Hack Every Major Operating System. Then They Called the White House.
The Mythos model found thousands of zero-day vulnerabilities with an 80% exploit rate. Now JPMorgan, Goldman Sachs, and the federal… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Anthropic Built an AI That Can Hack Every Major Operating System. Then They Called the White House.
The Mythos model found thousands of zero-day vulnerabilities with an 80% exploit rate. Now JPMorgan, Goldman Sachs, and the federal… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
How AWS Security Hub Improves Cloud Security for Indian Businesses
In today’s digital world, cloud security is not optional, it is essential. Businesses in India are rapidly moving to cloud platforms like… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Non-Human Identity Attacks: When APIs, Bots, and Service Accounts Become the New Target
Introduction: The Expanding Identity Landscape Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Dark Side of Generative AI in Cybercrime
The Dark Side of Generative AI in Cybercrime How ChatGPT, Deepfakes, and AI Tools Are Revolutionizing Digital Crime We hear a lot… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Dark Side of Generative AI in Cybercrime
The Dark Side of Generative AI in Cybercrime How ChatGPT, Deepfakes, and AI Tools Are Revolutionizing Digital Crime We hear a lot… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Stop Hackers Before They Start: A Complete Guide to Modern Web Security
The internet is an inherently hostile environment. Every web application — whether a simple landing page or a distributed microservices… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Elastic: Setting up a SOC Lab | TryHackMe | Elastic
Set up a SOC lab with Elasticsearch, Kibana, and Fleet Server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Weekly Threat Intelligence Report 13 Apr 2026
This document summarizes key cyber threats identified between Apr 6 and Apr 12, 2026, including related threat events Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Every time you drop a pin in Accra, someone is watching
Think about last week. How many times did you share your location? You dropped a pin for a Bolt driver. You sent your address to a Glovo… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
OS Level Age Verification: Is Your Child Using Linux?
On October 13th of yesteryear, a bill has passed vote in California which will require age verification on the OS (Operating System) level… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Compliance Is a Baseline, Not a Security Strategy
Compliance does not equal security, and that distinction matters more than many organizations want to admit. Continue reading on T3CH »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Saving A Medical Facility Part 1
The reality here is that medical facilities and healthcare businesses need to be compliant with a magical federal act known as H.I.P.A.A… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Cyber guerra: il conflitto invisibile che sta già cambiando tutto
Non ha carri armati né confini visibili, ma ha effetti reali ogni giorno Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
OT/ICS: Introduction · TryHackMe Walkthrough
Learn what Operational Technology (OT) and Industrial Control Systems (ICS) are, and how they function. Continue reading on Medium »

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Safari Broke Our Authentication — Here’s What We Missed
(Cookies, tokens, and the cross-domain issue that nearly broke our login system) Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Claude Mythos Preview Is Not Just a Better Claude. It Changes the Economics of Cybersecurity.
Why Anthropic’s newest unreleased model matters, what most coverage misses, and why its biggest value and biggest risk come from the same… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Attackers Actively Exploiting Critical Vulnerability in Ninja Forms — File Upload Plugin
Attackers Actively Exploiting Critical Vulnerability in Ninja Forms — File Upload Plugin Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Reverse Engineering on CyberTalents: Solving All MEDIUM Challenges Part 5
Challenge 1 (They are many) : Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
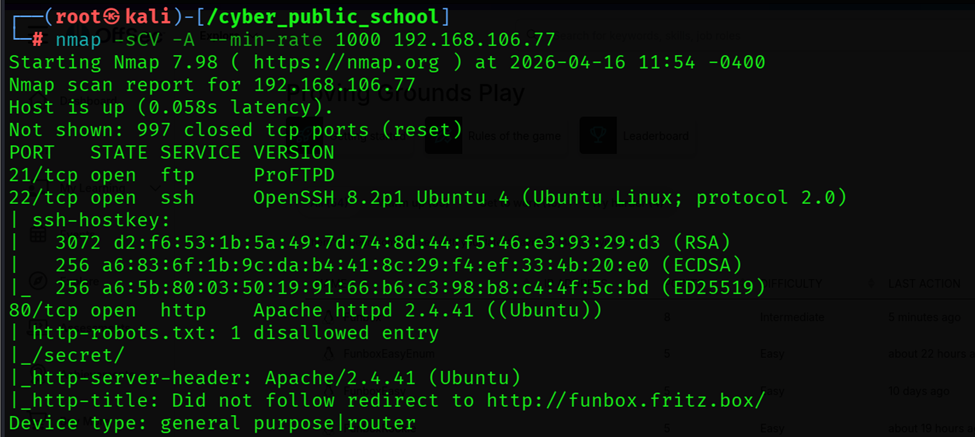
Funbox Walkthrough (Proving ground-play-OSCP)
By cyber_public_school | Cyber Security Researcher Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Netwalker Configuration Extraction via Malcat
Introduction Continue reading on Medium »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
4w ago
AWS Community Day Bay Area 2026 (Security Edition): A Volunteer’s Recap and Your Guide to Every…
The cloud security community showed up. Here’s what went down and where you can watch all of it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
AWS Community Day Bay Area 2026 (Security Edition): A Volunteer’s Recap and Your Guide to Every…
The cloud security community showed up. Here’s what went down and where you can watch all of it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
I’ve Been in Cybersecurity 20+ Years… The Next Two Years are a wake up call
The Future Is Not What You Think Continue reading on InfoSec Write-ups »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Expiration Date of Secrecy: Why the Quantum Threat Has Already Begun
Your bank details, private emails, and crypto wallets might be secure today. But the "Harvest Now, Decrypt Later" reality means they are… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Why Choosing the Right Cybersecurity Services Provider in Dubai is Crucial for Business Growth
In today’s digital-first world, businesses are more connected than ever, but this connectivity also brings increased exposure to cyber… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Try Hack Me- Blue Walkthrough
Hello, stranger — let’s begin. Continue reading on Medium »
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Malicious WordPress Plugins with Backdoors Compromise Thousands of Websites
More than 30 WordPress plugins were shut down after a supply-chain backdoor compromised thousands of sites through the Essential Plugin portfolio. The post Mali
Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Rethinking How to Learn Cybersecurity in the Age of AI
I’ve always had an interest in cybersecurity. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
IAM Engineer Salary in UAE: What Most Job Listings Don’t Tell You
When people research IAM Engineer salaries in the UAE, they usually expect a straightforward answer — a number based on years of… Continue reading on Medium »

Engineering at Meta
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Post-Quantum Cryptography Migration at Meta: Framework, Lessons, and Takeaways
We’re sharing lessons learned from Meta’s post-quantum cryptography (PQC) migration to help other organizations strengthen their resilience as industry transiti

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Building a $40 Stingray Detector That Fits in an Altoids Tin
The tin clicks shut with that thin metallic snap. You toss it into a bag next to a half-dead USB cable and a notebook that smells faintly… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Over 100 Chrome extensions caught stealing your personal data
Security researchers uncover a coordinated campaign hidden inside games, Telegram clients, and browser tools. Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
4w ago
800 Google Android Apps Targeted By PIN-Stealing Hackers
More than 800 Google Android apps have been targeted by a surge in PIN-stealing hack attacks. What you need to know.
TechCabal
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Kenya’s LOLC Microfinance Bank directors risk prosecution in data enforcement case
The decision signals a sharper enforcement stance in Kenya’s data protection regime.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Cross-site WebSocket Hijacking ; Lab Write-up
this challenge was part of the PortSwigger web security academy. Continue reading on Medium »

MIT Technology Review
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Download: cyberscammers’ banking bypasses, and carbon removal troubles
This is today’s edition of The Download, our weekday newsletter that provides a daily dose of what’s going on in the world of technology. Cyberscammers are bypa

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Investigating GotoHTTP on Windows: Behavior, Forensic Artifacts & Detection
Deep dive into GotoHTTP RMM and how to detect it if it ever lands on your corporate Windows workstation Continue reading on Medium »
Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Retry Storm: How a Small Slowdown Can Take Down Your JVM
JVM Internals -Scenario 6 Continue reading on Medium »
 DeepCamp AI
DeepCamp AI