📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 587 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (12632)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
2d ago
Tak Selamanya Web yang Aman “HTTPS” Itu Bebas Dari Serangan
Critical Review: ‘if HTTPS were secure, I wouldn’t need 2FA’ — end user and administrator mental models of HTTPS. Continue reading on Medium »
Medium · Cybersecurity
2d ago
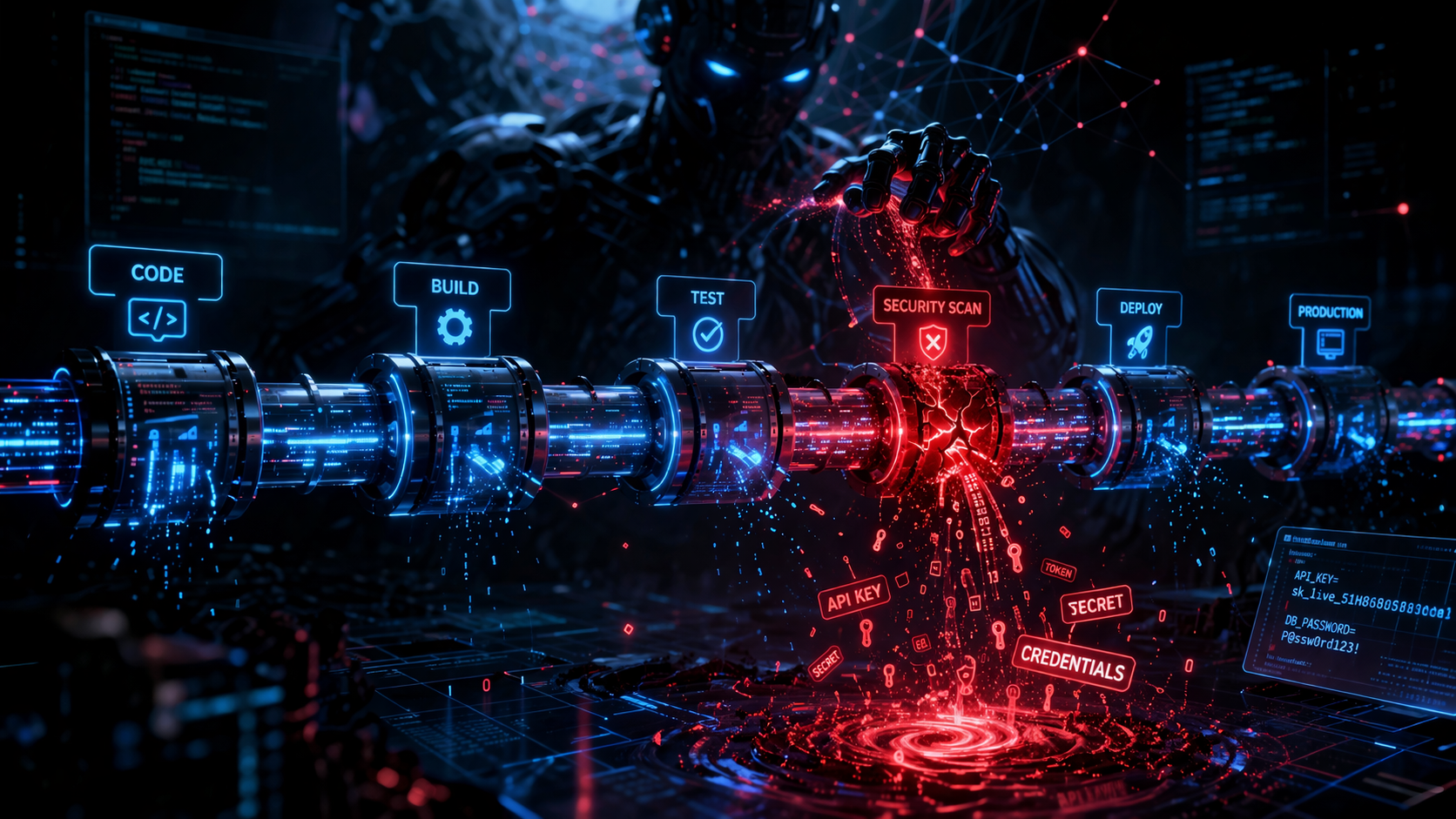
I Built an AI Agent That Pwns CI/CD Pipelines — Then Helps Fix Them
Part 2 of the prt-actions-pwn series. Read Part 1 for the threat landscape, attack chain, and vulnerability patterns. Continue reading on Medium »

Medium · Cybersecurity
2d ago
TryHackMe: Offensive Security Intro Writeup
Introduction Continue reading on Medium »

Medium · Cybersecurity
2d ago
The Assessed Enterprise: Why Operational Discipline Is the Foundation for AI-Era Security…
How operational discipline shapes AI-driven security and determines whether automation delivers assurance or false confidence. Continue reading on Harmonious Pi
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Why Hyderabad IT Professionals Are Turning to SailPoint IIQ Certification in
2026Hyderabad has emerged as India’s second-largest hub for cybersecurity and enterprise software hiring. Companies like Deloitte… Continue reading on Medium »

Medium · Cybersecurity
2d ago
Threat Hunting, Detection & Intelligence — What They Really Are
The Confusion… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Cmess — TryHackMe Walkthrough
Hosts File Configuration Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
BlueHammer Isn’t a Defender Bug — It’s a Windows Design Flaw. Here’s the Real Fix.
Why detection rules won’t save you, and what Microsoft should actually do. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Why Anthropic’s Claude Mythos Is Not Fearmongering but a Force Reshaping Cybersecurity
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Securing the Backbone — Issue #14: When Risk Feels Invisible: Bridging the Executive Disconnect in…
Date: May 5, 2025 Continue reading on Medium »

Medium · Cybersecurity
2d ago
CI/CD Pipelines Are High-Privilege Targets — And AI Just Scaled the Risk
Hello Friends! Continue reading on Medium »

Medium · Cybersecurity
2d ago
Reconnaissance With Metasploit
Welcome back, guys. As you might know me from the previous part of this series, I’m a cybersecurity student sharing my knowledge of the… Continue reading on Med

Medium · Cybersecurity
2d ago
OAuth Guide: Vulnerabilities, Attack Vectors, and Security
Master OAuth: Learn about its vulnerabilities, critical attack vectors such as JKU and account takeover, and chaining strategies. Continue reading on Medium »
Medium · Cybersecurity
2d ago
The Church of Malware Presents: The Most Braindead Python Botnet We’ve Ever Seen
┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼ ┼┼┼┼┼┼┼┼██┼┼┼┼┼┼┼┼┼┼┼┼┼┼┼██┼┼┼┼┼┼┼┼┼ ┼┼┼┼┼┼████▄┼┼┼▄▄▄▄▄▄▄┼┼┼▄████┼┼┼┼┼┼┼… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Reverse Engineering on CyberTalents: Solving All Easy Challenges Part 4
Challenge 12 : (chall ) Continue reading on Medium »
Medium · Cybersecurity
2d ago
I Built a SOC Home Lab From Scratch as a Graduate — Here’s Everything I Learned
I Built a SOC Home Lab From Scratch as a Graduate — Here’s Everything I Learned Continue reading on Medium »

Medium · Cybersecurity
2d ago
Cybersecurity in the Age of Autonomous AI: When Defense Is a Luxury Few Can Afford
If recent claims hold even partially true, cybersecurity is approaching a fundamental shift, and it’s not just about better tools. It’s… Continue reading on Med
Medium · Cybersecurity
2d ago
Scam Systems Do Not Exploit Trust; They Exploit Latency
A common but incomplete explanation of scams is that they exploit trust, emotion, or human error. While not incorrect, that framing is… Continue reading on Medi

Medium · Cybersecurity
2d ago
“Anonymous” Messaging is One Big Lie
For a long time, we’ve been sold the idea that encrypted messaging apps like Telegram and Signal make us invisible. Continue reading on Medium »
Medium · Cybersecurity
2d ago
As large language models (LLMs) are increasingly embedded into production systems,
As LLM move in to real production systems, security challenges are shifted from code-level vulnerabilities to system-level risks. Continue reading on Medium »

Medium · Cybersecurity
2d ago
The Conversation the Security Industry Keeps Having Wrong
By Joshua Moses Continue reading on Medium »
Medium · Cybersecurity
2d ago
The Silicon Chokehold: Why AI’s Silent Security Threat and Memory Drain Could Break Tech
A cyber-capable model is terrifying the government, while data centers quietly swallow the global supply chain. The math is finally… Continue reading on Medium
Medium · Cybersecurity
2d ago
The Last Locksmith
April 14, 2026 – By X. Voidwriter Continue reading on Medium »

Medium · Cybersecurity
2d ago
The Government Is Fighting Itself Over the Most Powerful Cybersecurity Tool Ever Built — And Your…
On the same week the Trump administration was fighting Anthropic in federal court, the Treasury Secretary and the Chair of the Federal… Continue reading on Beyo
 DeepCamp AI
DeepCamp AI