📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 766 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (13687)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsMedium · Programming

Medium · Cybersecurity
5d ago
How Raw Alerts Become Analyst-Ready Jira Tickets — Automatically | SOC Project — Phase 4
While there are many open-source case management platforms, many enterprises use Jira for tracking security incidents. For this lab, we… Continue reading on Med
Medium · Cybersecurity
5d ago
I Automated My Entire Tier-1 Alert Pipeline With n8n and Gemini | SOC Project — Phase 3
In this phase, we will deploy n8n to handle our security orchestration and automated response (SOAR) workflows. Continue reading on Medium »

Medium · Cybersecurity
📰 AI News & Updates
⚡ AI Lesson
5d ago
Do AI Impact ASIA Company? A 2026 Macroeconomic Technical Audit
The year 2026 marks a decisive pivot point for the Asian corporate landscape. As the “Digital Silk Road” matures, the integration of… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
The 2026 Guide to Web Integrity: Understanding the Role of SSL in Modern App Ecosystems
In the current digital landscape of 2026, the internet is no longer a luxury; it is the backbone of global commerce and entertainment… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Attackers don’t hack systems — they hack decisions
The real vulnerability isn’t your software. It’s the three seconds before you click. Continue reading on Medium »

Medium · Cybersecurity
5d ago
Authentication Bypass — How Attackers Become Anyone
✍️ Introduction Continue reading on Bug Bounty Hunting: A Comprehensive Guide in English and french »

Medium · Cybersecurity
5d ago
SOC Automation Lab Series 3
Now since we have our Wazuh and TheHive ready letsconfigure our wazuh to windows 11 agent Continue reading on Medium »

Medium · Cybersecurity
5d ago
Cybersecurity 2026: Resilience, AI Governance, and the Global Challenge
From fintech ransomware to global compliance, lessons in resilience and trust. Continue reading on Medium »

Medium · Cybersecurity
5d ago
This Week in Tech: Unpatched, Unleashed, and Unstoppable
TL;DR Continue reading on Medium »

Medium · Cybersecurity
5d ago
Monitoring DNS Traffic for Suspicious Activity using Wireshark
The goal was to isolate DNS traffic and capture packets for analysis. Continue reading on Medium »

Medium · Cybersecurity
5d ago
My Bug Bounty Journey #10: Start Your Bug Bounty Journey Today
The End Continue reading on Medium »

Medium · Cybersecurity
5d ago
Verification Without Exposure: Proving Without Revealing
Introduction Continue reading on Medium »

Medium · Cybersecurity
5d ago
Trust Is Not a State: It’s a Continuous Verification Process
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
What Scale-Up CISOs Actually Need: The Politics Nobody Prepares You For
The Scale-Up CISO series by John Rouffas Continue reading on Medium »
Medium · Cybersecurity
5d ago
⚙️ 09. — Insecure Direct Object References (IDOR)
Continue reading on Medium »
Medium · Cybersecurity
5d ago
⚙️ 08. — User ID controlled by request parameter with password disclosure
Continue reading on Medium »

Medium · Cybersecurity
5d ago
Investigating Windows Event Logs: A Practical Digital Forensics Walkthrough
Introduction Continue reading on Medium »

Medium · Cybersecurity
5d ago
FortiGate Dashboard (Status) Ekranı: Temel Bileşenlerin İncelenmesi
Genel Bakış Continue reading on Medium »

Medium · Cybersecurity
📣 Digital Marketing & Growth
⚡ AI Lesson
5d ago
My Medium Partner Program Suddenly Turned “Inactive” And I Still Don’t Know Why
My Medium Partner Program Turned Inactive — Even After Following All Rules Continue reading on OSINT Team »

Medium · Cybersecurity
5d ago
Vibe Hacking: How AI Is Helping Hackers
The Hoodie Is Gone. Now All You Need Is a Chat Window and Good Vibes Continue reading on OSINT Team »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
I Found a Broken Login System in a Fintech App — Here’s How I Did It
A real bug hunt story with JWT tokens, Burp Suite, and a fintech website that trusted too much Continue reading on OSINT Team »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
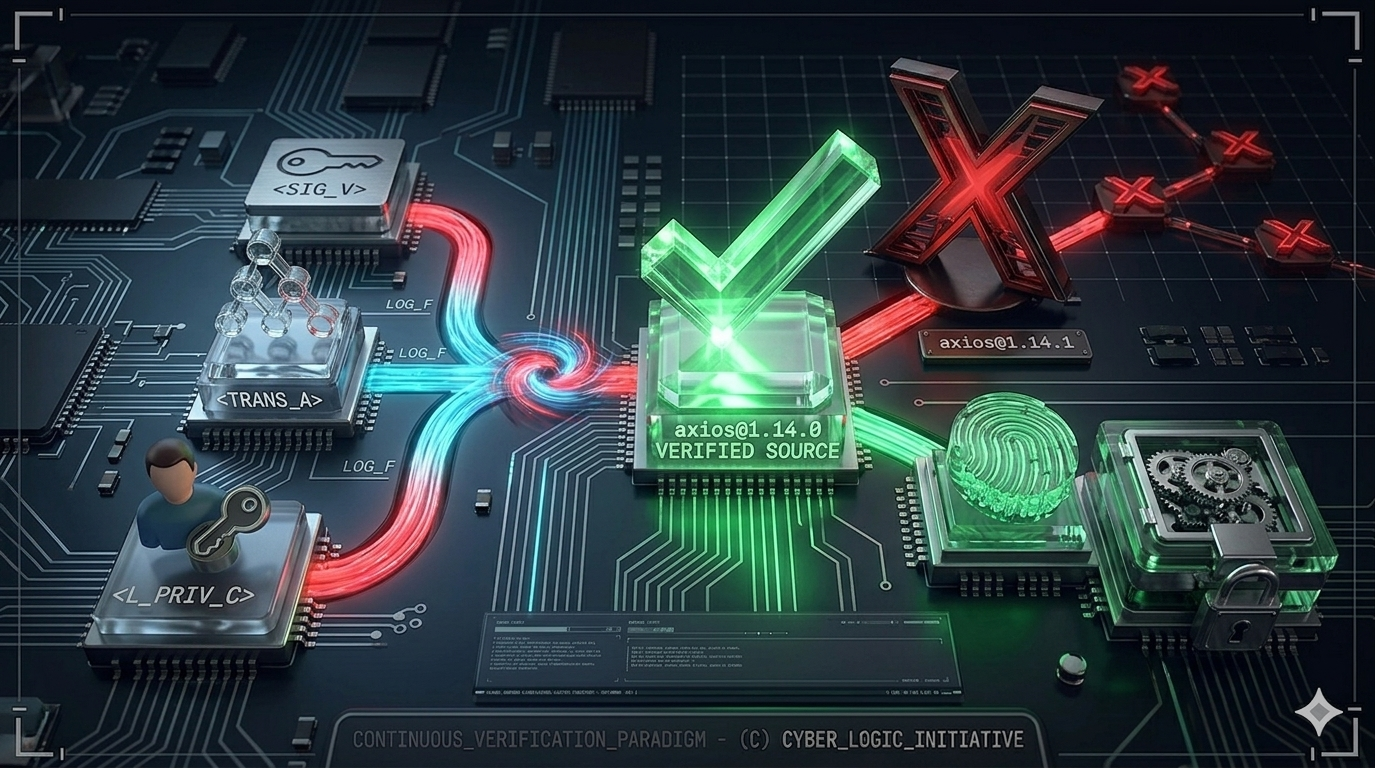
One npm install Away
What the Axios Supply Chain Attack Teaches Us About Zero Trust in Software Development Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Análisis de un dropper, que se disfraza como herramienta de hacking
¿Y bueno gente como les va?, yo por mi lado estoy bastante bien y emocionado por contarles que encontré algo interesante para explicar… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
LetsDefend: Obfuscated JavaScript Challenge Walkthrough
Malicious JavaScript Analysis: Identifying Obfuscation, WMI Usage, and Network-Based Payload Staging Continue reading on Medium »
 DeepCamp AI
DeepCamp AI