📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 214 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10306)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
Why shared responsibility models confuse SMEs.
Shared responsibility looks clean in a diagram. Continue reading on aneo Security Insights »

Medium · Cybersecurity
4h ago
Transition from IPv4 Exhaustion to IPv6: The Future of the Internet
The rapid exhaustion of IPv4 addresses, which form the foundation of the internet, makes the transition to a new generation protocol, IPv6… Continue reading on

Medium · Cybersecurity
4h ago
FBI Atlanta and Indonesian National Police Take Down W3LLSTORE Phishing Marketplace
Continue reading on Medium »

Medium · Cybersecurity
4h ago
GRC vs. IT Operations: Why the ISO Must Be a Bridge Builder
Bridging the gap between the 2nd and 1st Line through eye-level collaboration and common-sense pragmatism. Continue reading on Medium »

Medium · Cybersecurity
4h ago
Why I’m Building a Cyber Intelligence Project From Scratch — And What’s Coming.
This is day one. Here’s everything. Continue reading on Medium »

Medium · Cybersecurity
4h ago
Inside a Web Shell Attack: TryHackMe First Shift CTF — Task 5: Portal Drop
A SOC Threat Intelligence Investigation into Brute Force, File Upload Exploitation, and Web Shell Persistence Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6h ago
Is your security strategy reactive — or intelligently proactive?
易 Zefai Insights || Cyber Security Edition Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
6h ago
LLM Injection + Unlimited Approval + RCE: The Coinbase AgentKit Attack Chain
A prompt injection that crosses three trust boundaries — and why Coinbase called it Medium Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6h ago
Curing Detection Engineer Anxiety: Uncovering the Blind Spots in Your Rules
In our previous post, 《Detection Rule Fragility: Design Pitfalls Every Detection Engineer Must Know》,we explored why detection rules based… Continue reading on

Medium · Cybersecurity
6h ago
CISA Critical Cybersecurity Alert: Active Threats Targeting Operational Technology and…
WATCH FULL VIDEO Continue reading on Medium »

Medium · Cybersecurity
6h ago
Building Smarter & Safer Enterprises with Integrated Security Solutions | Omnilink Technology
Introduction Continue reading on Medium »
Medium · Cybersecurity
6h ago
DejOS 1.0 — A Remastered Linux System for Retail Environments
A personal journey of building a retail-focused Linux system shaped by trial, error, and real-world deployment. Continue reading on Medium »
![[Technical Audit] 2026 Mobile Architecture: Defending Against Sophisticated Banking Trojans](https://cdn-images-1.medium.com/max/821/1*9E-i-M87eUbhwqFvUN9tBA.jpeg)
Medium · Cybersecurity
6h ago
[Technical Audit] 2026 Mobile Architecture: Defending Against Sophisticated Banking Trojans
In the first half of 2026, the global shift toward “Mobile-First” banking has invited a new generation of high-level cyber threats. While… Continue reading on M

Medium · Cybersecurity
6h ago
Implementing High-Performance App Architecture for Mobile Gaming (2026 Guide)
In the software development landscape of 2026, the delta between a “standard” application and a “high-performance” ecosystem is defined by… Continue reading on

Medium · Cybersecurity
6h ago
Claude Mythos Found Thousands of Zero-Days in Weeks.
A production engineer’s breakdown of autonomous vulnerability discovery — and how to build your own lightweight version. Continue reading on Medium »

Medium · Cybersecurity
6h ago
When Cybersecurity Theory Becomes Reality: The Internship Offer That Wasn’t
When you study cybersecurity, you spend hours learning about phishing, social engineering, identity theft, and financial fraud. Continue reading on Medium »

Medium · Cybersecurity
8h ago
How AI is Transforming SOC: From Reactive Security to Autonomous Threat Detection
Introduction Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
8h ago
Mastering the ISO 22301 Lead Implementer Role: Beyond the Certification
Imagine your organization faces a sudden, catastrophic system failure or a regional disaster. The difference between a business that… Continue reading on Medium

Medium · Cybersecurity
8h ago
BankGPT | TryHackMe Writeup
TryHackMe | BankGPT Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
8h ago
You May Have Perfect Backups and Still Lose Everything
Backup Best Practices for Data You Cannot Afford to Lose Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
8h ago
Malloc Privacy Weekly
We bring you the most recent mobile cybersecurity updates in the newest edition of Malloc Weekly Privacy. This week, we cover the surge in… Continue reading on
Medium · Cybersecurity
8h ago
IDS vs IPS:Intrusion Detection vs Prevention Systems
CORE IDEA Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
8h ago
Bug Bounty Hunting — Ethical Hacking for Profit
What if hacking could be legal, respected, and even highly profitable? Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
8h ago
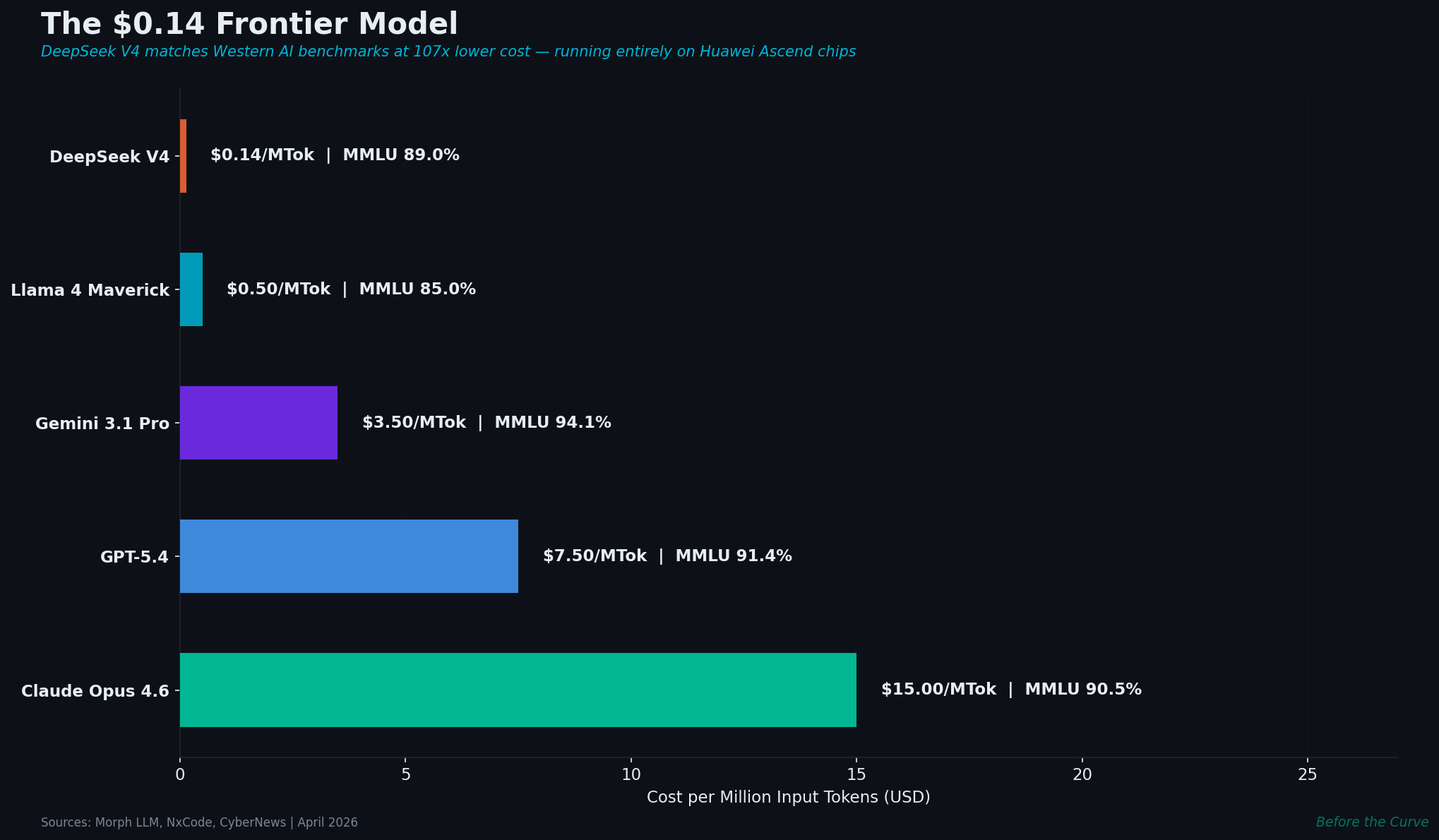
DeepSeek V4: 1 Trillion Parameters, $0.14/M Tokens, No NVIDIA
China’s latest frontier model costs 107× less than Western alternatives and runs entirely on Huawei chips. With 175,000 open-source AI… Continue reading on Medi
 DeepCamp AI
DeepCamp AI