Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,379 reads from curated sources

Dev.to · Dylan Gan
🔐 Cybersecurity
⚡ AI Lesson
6d ago
How SPF Pushes Scam Defence Toward Shared Intelligence
Australia’s Scams Prevention Framework is not only a regulatory development. It is a signal that scam...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
1 Million AI Services Were Exposed. The Security Disaster Is Worse Than Anyone Thought
A recent investigation into more than 1 million exposed AI services uncovered something deeply unsettling: public chatbots leaking… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Waspada Risiko Insider Threat dalam Perusahaan, Apa yang Harus Dilakukan?
Dalam menghadapi ancaman siber, banyak organisasi cenderung memfokuskan pertahanan mereka pada serangan dari pihak luar, seperti peretas… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
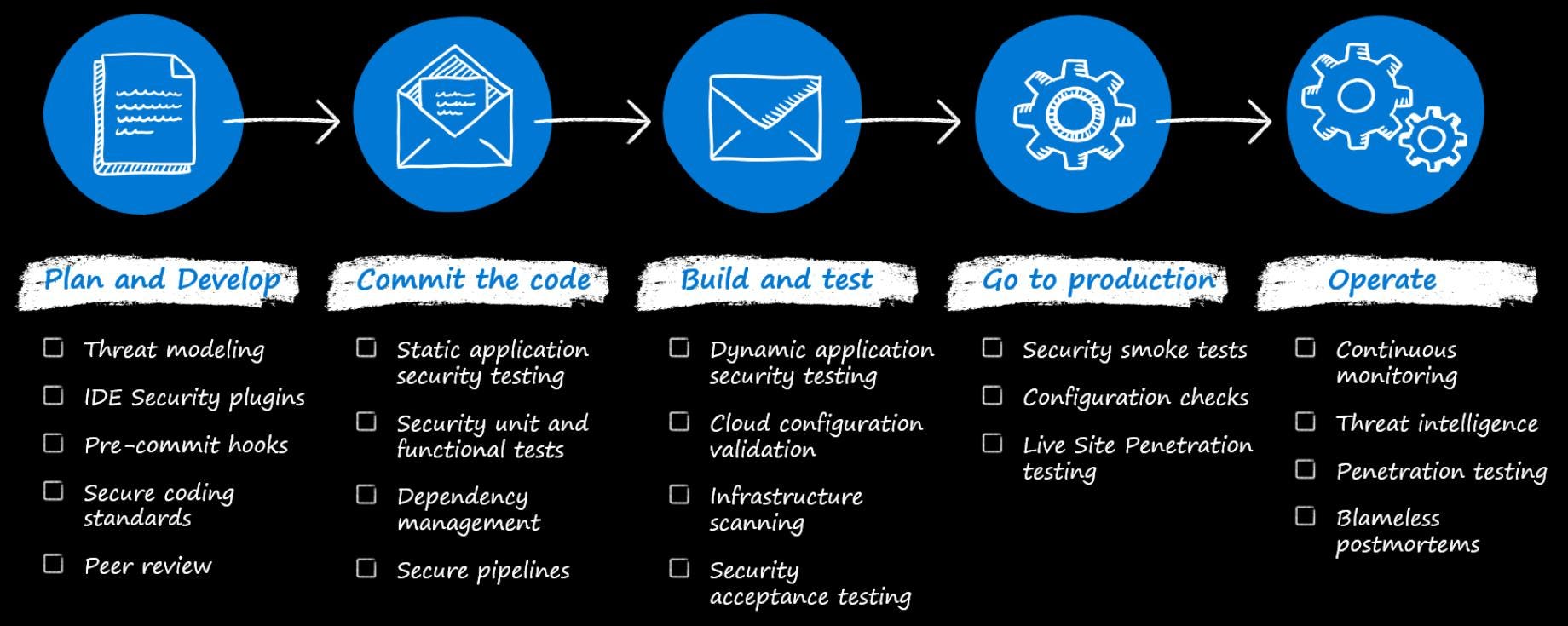
DevOps Is No Longer About Speed — It’s About Control
From rapid deployment pipelines to full-scale risk, security, and compliance engines shaping modern digital warfare Continue reading on DevSecOps & AI »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Privacy-first journaling: what it actually means in code
The five choices that turn “we take privacy seriously” from boilerplate into something you can verify. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
VAPT Services Explained, What Every Company Should Know
Cyberattacks are no longer limited to large corporations. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Breaking Infinity
Anatomy of Lock-Free Ring Buffer Vulnerabilities and Defensive Engineering Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
When Our Digital Infrastructure Goes Offline: Lessons from the Global Canvas Breach
What a real-world supply chain attack taught me about systems, security, and shared responsibility Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
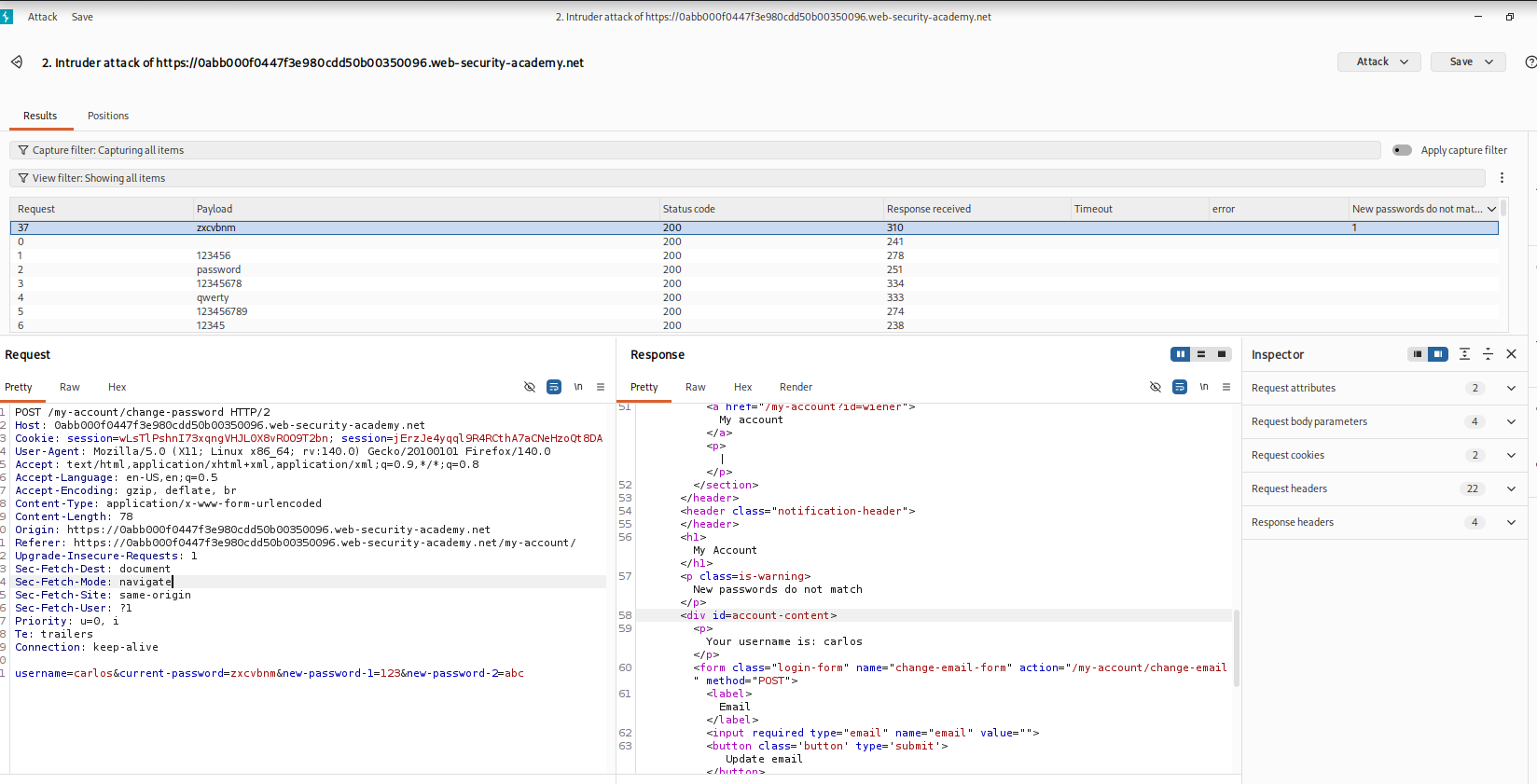
Breaking Authentication Through Password Change Logic Flaws — PortSwigger Lab Walkthrough
Authentication mechanisms are often heavily protected against brute-force attacks on the main login page. However, developers sometimes… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
AWS Elastic Beanstalk Pentesting with AWS CLI
Disclaimer: This walkthrough was performed in a controlled lab environment for educational and authorized security testing purposes only. Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Open Source Firewall for Small Business: What You Actually Need to Know
Most small businesses don’t struggle with firewall technology because it’s unavailable — they struggle because it’s either too complex… Continue reading on Medi
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
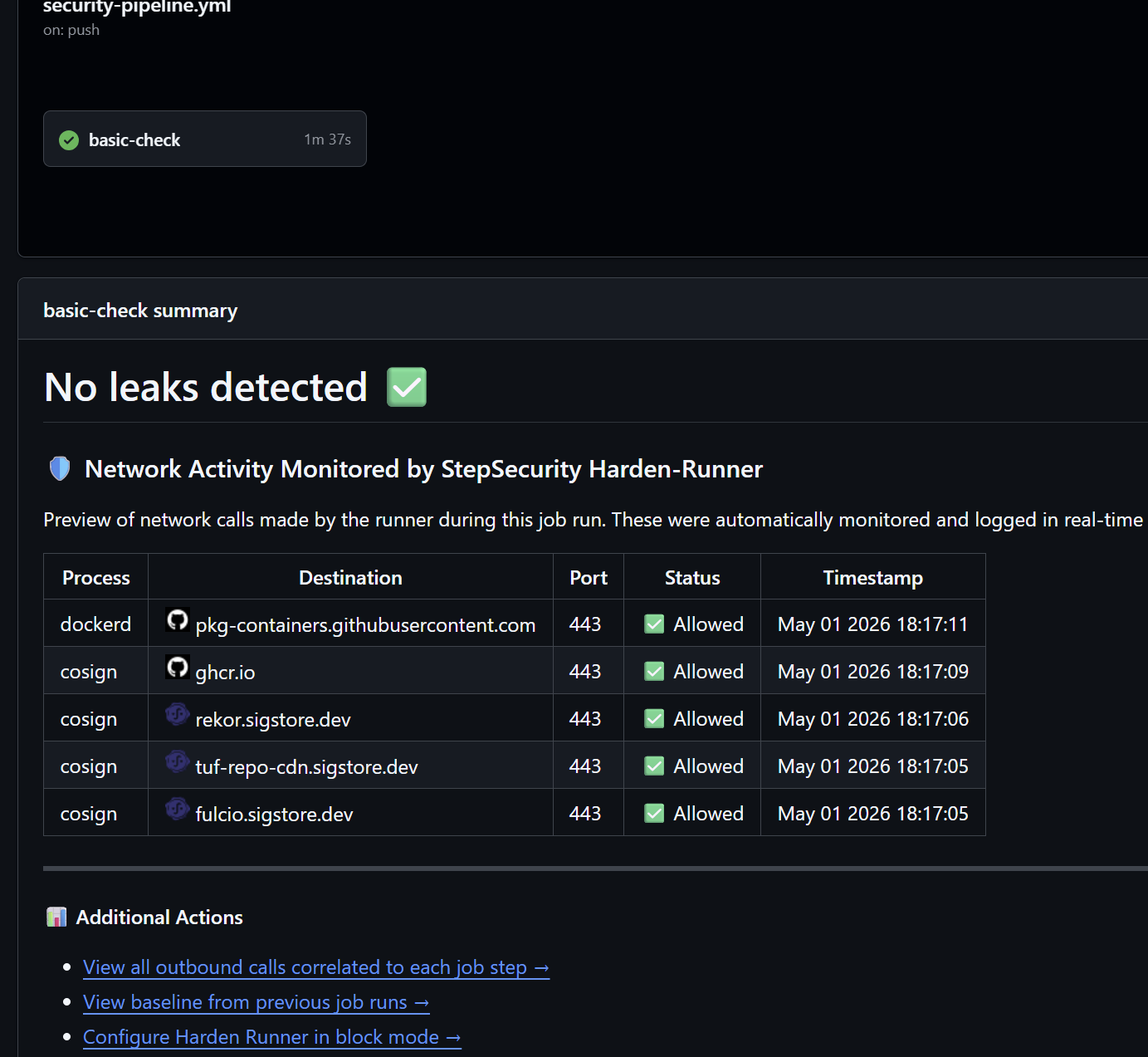
Advancing the Project of Secure CI/CD pipeline -3
If you have followed the previous series -2 then you would have understood what we are following in this project Continue reading on Medium »

Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Securing the Pipeline: Implementing Automated Security Scanning in Python CI/CD
The DevSecOps Workflow: Securing Python SaaS applications through automated vulnerability scanning. Continue reading on Medium »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Securing the Pipeline: Implementing Automated Security Scanning in Python CI/CD
The DevSecOps Workflow: Securing Python SaaS applications through automated vulnerability scanning. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Move to Proton Without Breaking Your Workflow — A Practical Migration and Adoption Guide
Part X of our Proton series: email, calendar, files, passwords, and the human work that makes privacy stick Continue reading on Cleave Security »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Hidden Security Problem in Flannel Kubernetes Clusters
Flannel has almost become the default answer to Kubernetes networking. It ships with k3s, appears in a huge number of kubeadm tutorials… Continue reading on Med
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Cryptourrency Tracing & Investigation Firms Based-in UK Consult ZEUS CRYPTO RECOVERY SERVICES
Finding a specialized team to navigate the complex world of blockchain forensics is essential for anyone who has lost digital assets. Below is the reimagined pr

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
6d ago
WhatsApp Just Fixed Two Security Bugs—Here's What They Were
Meta published a security advisory on May 1 disclosing two vulnerabilities in WhatsApp that were caught through its bug bounty program. Continue reading on Pred

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Day 1 — Awakening the Hacker Within
“You’re tired of half‑finished scripts, lines of code lost in the void, aren’t you?” “Says the voice that keeps me up at 3 a.m., insisting… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Watchers Are Getting Smarter: AI, Claude, and the Future of Threat Hunting in Datacenters
There’s an old saying in cybersecurity: attackers only need to be right once, defenders need to be right every time. For decades, that… Continue reading on Medi
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Cloud Forensics: A Meta-Study of Challenges, Approaches, and Open Problems

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
From Slack Reaction to Threat Summary: Automated Threat Intel with Slack and Gemini
Hello Everyone, As a Security Analyst, we usually read threat intel news with a flood of tabs: CISA alerts, BleepingComputer articles, and… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Why AI-Powered Phishing Is Becoming the Biggest Cybersecurity Threat in 2026
A few years ago, phishing emails were easy to spot. Bad grammar, suspicious links, strange formatting — most people could recognize them… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Apple Charged You $1399 for an iPhone That Couldn’t Delete a Notification Properly
Apple dropped iOS 26.4.2 on April 22, 2026, and the release notes said, basically, nothing. “This update provides bug fixes for your… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
How Anthropic’s Mythos Is Reshaping Firefox’s Cybersecurity Landscape
Cybersecurity is entering a new phase where artificial intelligence is no longer just defending systems. It is actively discovering… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
TryHackMe RootMe CTF Writeup — Beginner Friendly
Hi everyone! As someone exploring cybersecurity through CTFs and hands-on labs, I wanted to share my beginner’s approach to solving the… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
SSH - Festung oder Low Hanging Fruit?
Im heutigen WriteUp werden wir das Thema SSH als Initial Access Vektor besprechen. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Hope Is Not a Security Strategy
Say it with me now: “Hope is not a security strategy.” Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why Cyber Governance Will Define The Next Generation Of Market Leader
Cyber governance is not the agenda item you work through before the real conversation starts. It is the real conversation.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Bounty Hacker — TryHackMe CTF
Today I tried Bounty Hacker — a linux machine with a few interesting open ports to investigate and ultimately get root access to the… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Sonu Kumar: Navigating the Shifting Sands of Cybersecurity in 2025 — Insights from Nepal
## Sonu Kumar: Navigating the Shifting Sands of Cybersecurity in 2025 — Insights from Nepal Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Network Services 2 — THM
NFS (Network File System) Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Sonu Kumar: Critical Insights into Modern Cybersecurity Challenges & IT Trends 2025
## Sonu Kumar: Critical Insights into Modern Cybersecurity Challenges & IT Trends 2025 Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1w ago
AI Or Human, Data Is Still King: Visibility As The Real Security Advantage
Without this shared visibility, security teams risk operating with fragmented intelligence.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Not Everything Technical Is Engineering , And Zero Trust Proves the Problem
Cybersecurity keeps confusing implementation with assurance. That matters when slogans, tools, and architectures are mistaken for… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Signs Your WordPress Site Has Been Hacked
WordPress powers a large portion of the internet, which unfortunately also makes it a frequent target for automated attacks. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
CTF Basics: Understanding SQLi Blind Injection
Learn how blind SQL injection works, how to extract data using boolean conditions and time delays, and how to automate extraction in CTF… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Cyber Security: The Digital Shield Your Business Cannot Afford to Ignore
Picture this: you walk into your office one morning, turn on your computer, and discover that all your important files have vanished —… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Three Red Flags in Any Vendor’s Security Documentation
The context Continue reading on aneo Security Insights »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The fastest way to organise all your policies logically
Most SMEs don’t have a policy problem. They have a structure problem. Continue reading on aneo Security Insights »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Chapter 1 Review Questions | Security Controls (Security+ SY0–701 Domain 1)
Test your understanding of security controls with these Chapter 1 review questions. Designed for beginners preparing for CompTIA Security+… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
(HTB)Using the Metasploit Framework
Introduction to Metasploit Framework Continue reading on Medium »
InfoQ AI/ML
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Leading Open Source Author Calls for Verification over Trust in Software Supply Chains
In a blog post published in March 2026, Daniel Stenberg, creator and lead developer of curl, makes the case that the software industry's default position of tru
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Descope vs Auth0 for B2B Auth and SSO
This post was originally published on Descope. Continue reading on Auth Thoughts »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Week 19 | The Platforms You Trust Are the Ones Being Targeted
May 1–7, 2026 · 5stories Continue reading on Cybersecurity, Translated »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Security Infrastructure that Protects Users and Treasury
Security defines how systems operate, scale, and sustain trust over time. At Finanx AI, protection of capital, data, and infrastructure is… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Microsoft Edge Password Exposure: How a Memory Dump Reveals Your Credentials
By: Kavin Jindal (@Klevr) Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
CVE-2026–31431 Explained: Detecting and Mitigating the Linux Copy Fail Vulnerability — Chandra Home…
A newly disclosed Linux kernel vulnerability known as “Copy Fail” (CVE-2026–31431) allows local attackers to escalate privileges to root… Continue reading on Me
 DeepCamp AI
DeepCamp AI