Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,404 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Reverse Engineering on CyberTalents: Solving All Easy Challenges Part 2
Challenge 3: “Pure Luck” Reverse Engineering Continue reading on Medium »

Dev.to · Mr. 0x1
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
We Ran Four Security Tools Against Express.js. They Found Each Other's Proof.
How a multi-layered analysis stack independently surfaced findings that map to real, open GitHub issues — including a 3-day-old report that the original prototy

Dev.to · soy
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Actively Exploited Adobe CVE, Supply Chain Malware, & Self-hosted Certs
Actively Exploited Adobe CVE, Supply Chain Malware, & Self-hosted Certs ...

Dev.to · RepairXpert
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Crucix: An Open OSINT Dashboard Aggregating 27 Real-Time Data Sources
Crucix: An Open OSINT Dashboard Aggregating 27 Real-Time Data Sources I built Crucix...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
How I Bypassed Premium Subscription & Escalated Privileges Using a $0 VCC (Business Logic Flaw)
Introduction : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Before MYTHOS Ships, Someone Has to Fix the World
An Op-Ed on Anthropic’s Ethical Bind Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Anthropic’s New AI Found Bugs in Every Major OS and Browser — And They’re Not Releasing It
Claude Mythos Preview just found thousands of zero-day vulnerabilities. Apple, Google, Microsoft, and AWS are already using it. You can’t. Continue reading on L

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Anthropic’s New AI Found Bugs in Every Major OS and Browser — And They’re Not Releasing It
Claude Mythos Preview just found thousands of zero-day vulnerabilities. Apple, Google, Microsoft, and AWS are already using it. You can’t. Continue reading on L

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Windows Defender Killer: Combining Registry Edits with BYOVD for Permanent Disable
In the latest update to the Windows Defender Killer repository, I added a powerful new component: a BYOVD (Bring Your Own Vulnerable… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Using AI Without Fundamentals Is the Fastest Way to Stay a Beginner
You can look like you’re learning cyber security without actually learning anything. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Lab Ortamında FortiGate Kurulumu: Adım Adım Rehber
Bu yazıda lab ortamında FortiGate firewall kurulumu adım adım anlatılacaktır. Siber güvenlik alanına ilgi duyanlar ve özellikle SOC… Continue reading on Medium

Dev.to · ComplianceLayer
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Start a scan
When was the last time you checked what the internet actually sees when it looks at your domain? Not...

Medium · JavaScript
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
How a Single npm Possibly Compromised 100 Million Weekly Downloads
The axios supply chain attack is a masterclass in everything wrong with how we trust open source packages. Continue reading on System Weakness »

Dev.to · UZYNTRA Security
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Top API Security Vulnerabilities in 2026 (Real-World Breakdown)
Most APIs are vulnerable — and attackers know it. In 2026, API breaches aren’t about complex...

Dev.to · toolbox-poster
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SPF Records Explained: Prevent Email Spoofing with Sender Policy Framework
TL;DR SPF (Sender Policy Framework) is the first line of defense against email spoofing, allowing...

Dev.to · toolbox-poster
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SSL/TLS Certificates Explained: HTTPS Security for Every Website
TL;DR SSL/TLS certificates are the backbone of encrypted web communication, authenticating server...

Dev.to · toolbox-poster
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
HTTP Security Headers: The Complete Guide to Securing Your Website
TL;DR HTTP security headers are your first line of defense against cross-site scripting (XSS),...

Dev.to · toolbox-poster
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Domain Security Audit: The Complete Checklist for 2026
TL;DR A domain security audit reviews DNS configuration, email authentication, SSL/TLS...

Dev.to · toolbox-poster
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Phishing Attacks: How to Detect, Prevent, and Respond
TL;DR Phishing remains the most common initial attack vector, responsible for over 80% of reported ...

Dev.to · toolbox-poster
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
IP Blacklists & DNSBL: How to Check and Get Delisted
TL;DR IP blacklists (DNSBLs) are real-time databases that mail servers query to block spam at the...

Dev.to · Delmar Olivier
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Nuclei vs Traditional Vulnerability Scanners in 2026
Nuclei vs Traditional Vulnerability Scanners in 2026: Why Security Teams Are...

Dev.to · Delmar Olivier
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
OWASP ZAP vs Burp Suite in 2026: Which Should Your Team Use?
OWASP ZAP vs Burp Suite in 2026: Which Web Security Tool Should Your Team Use? OWASP ZAP...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
How APTs Breach, Persist, and Devastate Networks
Advanced persistent threats (APTs) are well-funded, evasive, and determined to penetrate networks containing sensitive… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Digital Evidence is Dead.
Why AI watermarks and warning labels are a losing battle against physics and human psychology Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Beyond the CLI: Reimagining Network Recon with Cyber-Eye Mapper v4.0
The power of Nmap, the elegance of a modern web dashboard, and the security of AES-256 encryption — all in one orchestration layer. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Post-Exploitation Pivoting in a Lab Environment Using Meterpreter
Internal Network Enumeration and Service Access Through a Compromised Linux Host Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
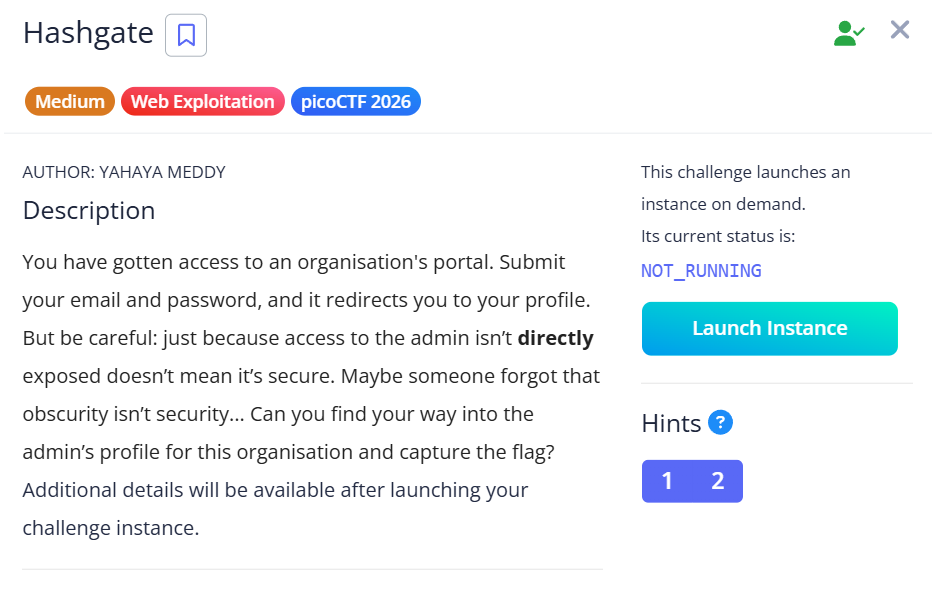
HashGate — picoCTF 2026 Writeup
Category: Web Exploitation | Difficulty: Medium Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Break-Glass Accounts in 2026
Why Passwordless Is No Longer Optional Continue reading on Medium »

Dev.to · Delmar Olivier
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The Complete Guide to Automated Penetration Testing in 2026
Why Your Security Scanner Isn't a Penetration Test AI-powered and automated pentesting in...
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Broken Access Control via Replay Attack
How a simple replay trick bypasses permission checks on a popular project management platform Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Obsession Writeup Español
La máquina Obsession se encuentra en la plataforma de Dockerlabs, creada por “El Pingüino de Mario” esta máquina está catalogada como “MUY… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Integrating VirusTotal Malware Intelligence with Wazuh — File, IP & URL Scanning
Imagine a new file appears on your system, or your machine suddenly connects to a suspicious IP address — and within seconds, you get an… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
BrowserMon Appliance Released: Enterprise Browser Security, Hardened and Ready to Deploy
A CIS Level 1 hardened OVA that ships pre-configured, pre-loaded, and ready for production Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
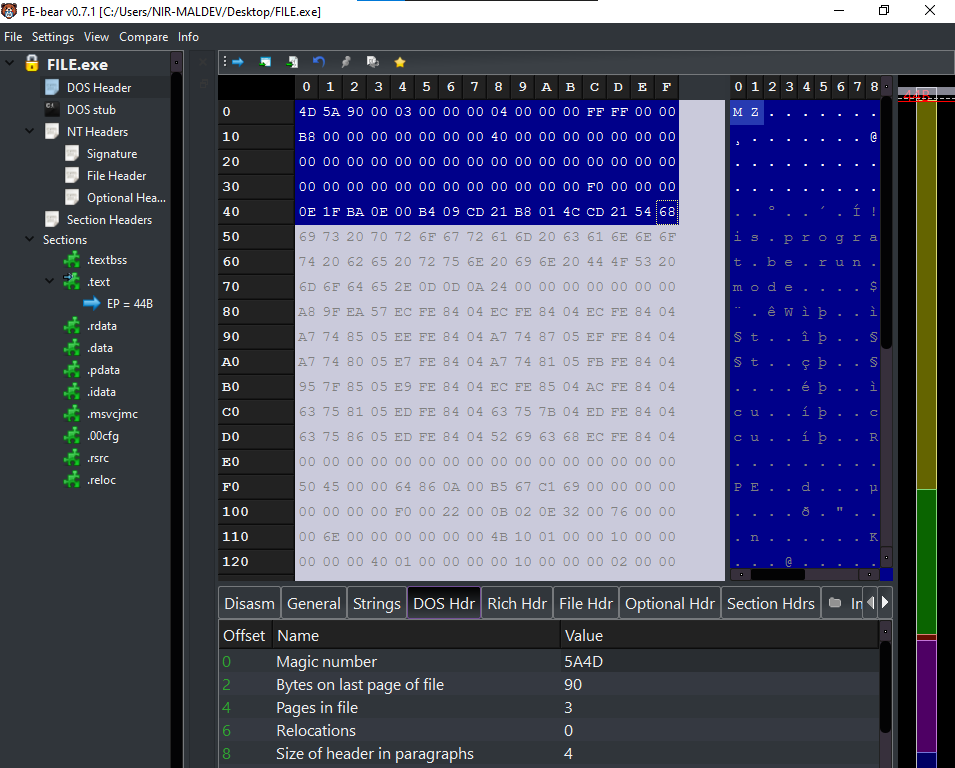
Introduction to DOS Header and DOS Stub (PE)- Nir(7)
Hello, Cybersecurity enthusiasts and white hat hackers!! Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
An AI Model Just Found a 27-Year-Old Zero-Day in OpenBSD
Anthropic’s Claude Mythos — still unreleased, currently gated to about 50 partner orgs through Project Glasswing — autonomously discovered… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Cybersecurity for Scammers
While trying to make a hotel reservation, I unexpectedly found myself in the middle of a critical security vulnerability. In this article… Continue reading on M

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Forget Hallucination: What if AI Deceives You?
Threads & Perspectives: On Mythos, Statistics, and a Very old playbook Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Hackers Give Rockstar Games Until April 14 To Pay For Stolen Data
As Rockstar Games confirms hack, ShinyHunters hackers give the GTA developer just days to pay ransom for stolen data.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Mr Robot VulnHubWalkthrough | 06/100
Introduction: The Machine That Started With a Smirk Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Analyse des risques stratégiques liés à l’intégration de l’EUDI wallet dans la gouvernance cyber…
La révolution silencieuse de l’EUDI Wallet : Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
SOC-Challenge-Day0
Episode 0: Membangun Lab SOC di Cloud Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Phishing Email Analysis SOC Analyst Guide Part-4 Email Authentication.
In this article we are going to touch our created lab a bit to understand the email security checks. Email security is used to protect… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Inside the Rockstar Games Breach: How ShinyHunters Exploited a Hidden Third-Party Weakness
A real-world breach that proves attackers don’t break in, they exploit trust. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Claude Mythos Might Break Cybersecurity. But Not in the Way You Think.
I’ll be honest with you. When I first read about Claude Mythos, my reaction wasn’t awe. It was a question I couldn’t shake. Continue reading on Medium »

Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Windows Recall Hides EVERYTHING: This Tool Exposes It All!!!
Windows Recall is one of those features that immediately triggers strong reactions. On one side, it promises a searchable timeline of what… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
The scariest AI story of the year!
Big claim, but meet Mythos the AI superhacker breaking bulletproof code. Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Aadi-Tech Vault: Personal Security Reimagined
Aadi-Tech Vault is the brainchild of Aditya Rai, who designed, coded, and architected the entire encryption system from scratch. Built on a budget PC, this proj
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1mo ago
Building a Windows Server Lab: From Zero to Active Directory Domain Services
Documentation is a key part of the learning process in cybersecurity. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI