Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,377 reads from curated sources

Dev.to · curi0us_dev
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Best RBAC solutions: what to shortlist and why
If you are evaluating RBAC tools right now, you already know the hard part is not finding "features."...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Is Using a VPN Enough to Stay Completely Anonymous on the Internet?
Online privacy has become a major concern in today’s digital world. Many people use VPNs to protect their internet activity and hide their… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Setting Up My Mobile Application Testing Lab: What Worked, What Failed, and What I Learned
When I first started learning mobile application security testing, I honestly thought installing a few tools would be enough. I quickly… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Day 1: Why I Chose to Start Slow Before Learning to Hack
Most people beginning their cybersecurity journey hear the same advice: jump straight into tools, labs, and exploits. Install Kali Linux… Continue reading on Me

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
1d ago
‘One Time Restart’—Microsoft Changes Windows After 15 Years
Microsoft starts expiring critical Secure Boot certificates in just 2 weeks.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Soporte IT en Chile: ¿Por Qué Necesitas Pros para Proteger Tus Datos en la Era IA?
En Chile, donde ciberataques subieron 35% en 2025 (Cybersecurity Ventures), el soporte informático profesional es clave para pymes. Este… Continue reading on Me

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The Manufactured Mystery of Mythos
What does Mythos, a powerful cyber-weapon disguised as responsible AI stewardship, mean for cybersecurity professionals? Continue reading on ILLUMINATION »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
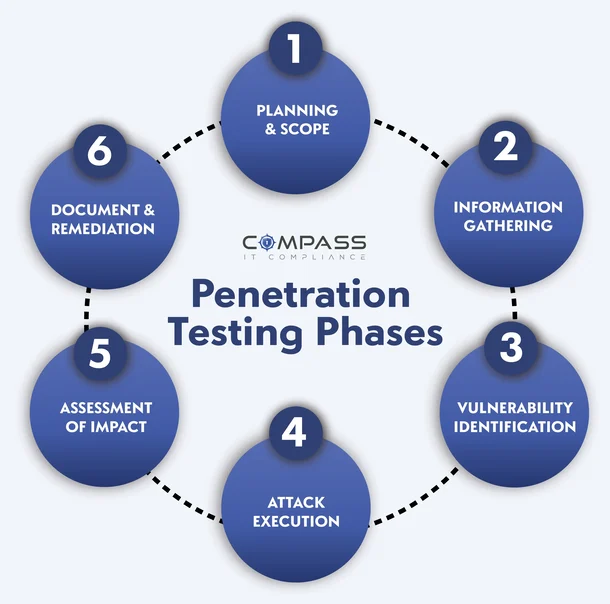
Anatomi Serangan: Membedah Metodologi Penetration Testing
Dunia keamanan siber tidak hanya soal membangun benteng yang tinggi melalui enkripsi atau kebijakan Zero Trust yang ketat. Memiliki teori… Continue reading on M
Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Here are the lessons I learnt of NMIT Hacks, 2026:
In the era of AI bots crawling the internet we must ensure the protection of our software against masquerading and spoofing. Use SMS or… Continue reading on Med

Dev.to · Freedom Coder
🔐 Cybersecurity
⚡ AI Lesson
1d ago
CVE-2026-21643: Fortinet FortiClient EMS SQL Injection Vulnerability
Fortinet FortiClient EMS contains a SQL injection vulnerability that may allow an unauthenticated attacker to execute unauthorized code or commands via specific

Medium · Data Science
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Authentication vs Authorization: Two Different Questions, Two Different Purposes
Understanding how secure systems verify identity first and then control access to actions and resources Continue reading on CodeX »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Authentication vs Authorization: Two Different Questions, Two Different Purposes
Understanding how secure systems verify identity first and then control access to actions and resources Continue reading on CodeX »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
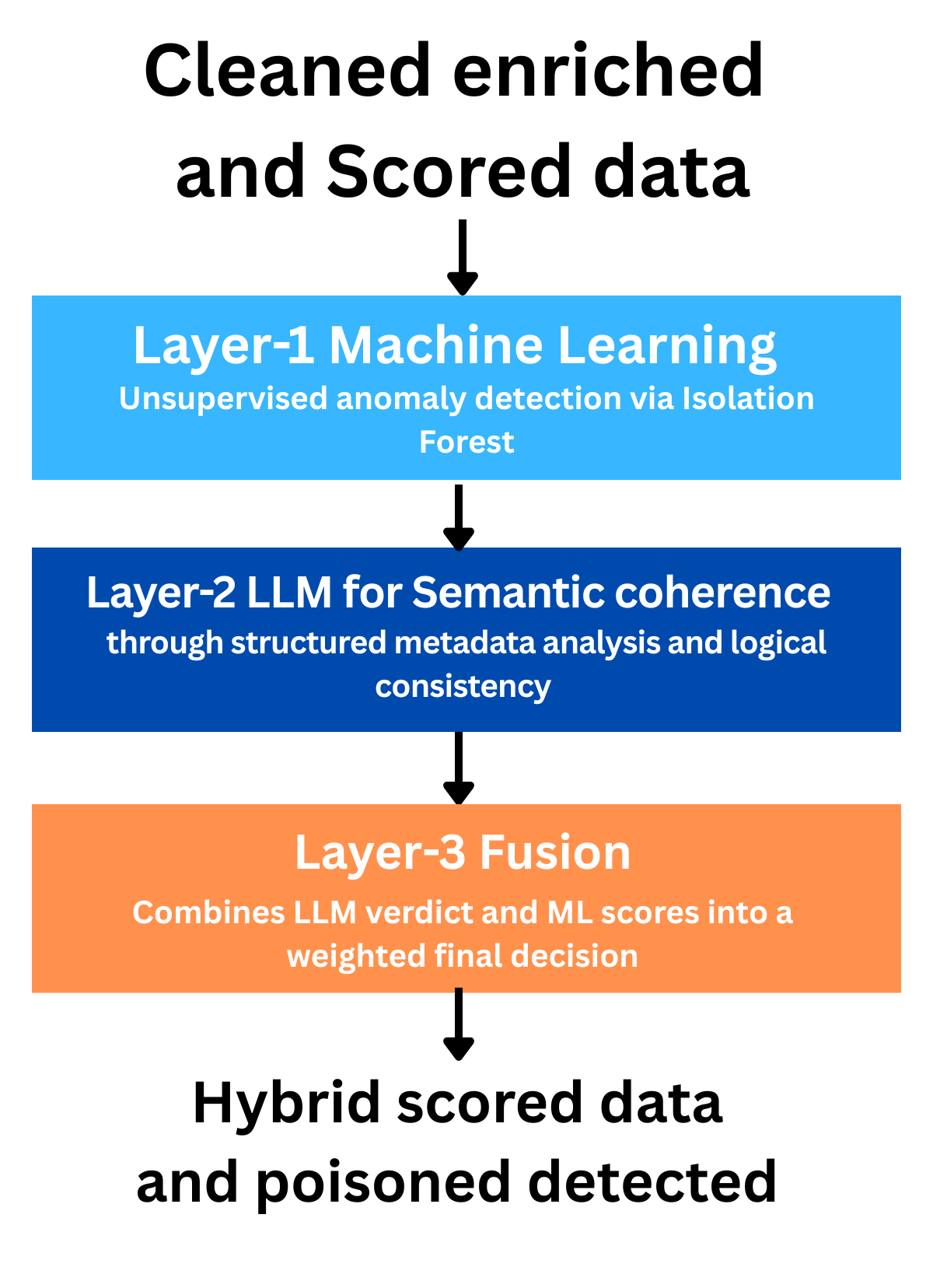
From Ingestion to Final Verdict: THREATRADAR’s Poisoning Detection Pipeline
Welcome to the fourth article in the THREATRADAR series. We recommend reading Part 1 Design and Implementation of THREATRADAR: Open-Source… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
When VirusTotal Can’t Name It: Identifying Malware Through Metadata
Two samples sitting in my honeypot had 55+ detection flags on VirusTotal but no threat label. No family name, no classification. Just… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
NoSQL Injection Guide: Fundamentals, Types, Exploitation, and Mitigation
Learn the basics of NoSQL injection, attack vectors in MongoDB, and advanced exploitation and defense strategies. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
The Authentication Debt Nobody Wants to Audit. And Attackers Know It.
Zero Trust, MFA, cloud security the conversation never stops. But underneath it all, two protocols from the 1990s still decide who gets in… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Multi-Layer Packet Processing Pipeline for DDoS Mitigation
Part of the Mirai Guard open research series on multi-layer DDoS defense architecture. Continue reading on Medium »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1d ago
4 Gigabytes You Didn’t Download
Chrome silently installed Gemini Nano on your machine. Delete it and will bedownloaded again. Continue reading on AI Advances »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Quantum-Safe, or Quantum-Scented?
Why the cybersecurity industry’s quantum discourse is long on vocabulary and short on understanding — and who profits from the gap. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
TryHackMe | Monitoring AWS Logins | WriteUp
Explore AWS authentication, common IAM threats, and SIEM detection options. Continue reading on T3CH »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Artificial Intelligence in Cybersecurity: Why Cyberattacks Are Increasing and How Users Can Defend…
By Fabian Andres Naranjo Rodríguez Master’s in Cybersecurity | PMP® | AWS Certified Cloud Practitioner Senior IT Infrastructure… Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
7deadbone labs #002 — Threat Actor Gains Initial Access. Analyst Was Watching.
TLP: CLEAR | Classification: Homelab | Date: 2026–04–01 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Deep Diving into Digital Extortion: A Comparative Malware Analysis of WannaCrypt and AsyncRAT Phase…
Unmasking the Architecture of Modern Cyber Threats: From Global Ransomware Outbreaks to Persistent Remote Access Phase 3 Continue reading on System Weakness »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Why Security Engineers Who Ignore Claude Code Will Be Obsolete by 2027
Claude Code Is Changing What “High Performance” Looks Like in Security Teams Continue reading on InfoSec Write-ups »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Where Can Someone Access Your Business? The Access Points Every Company Must Review
Most companies invest in cybersecurity tools — but still overlook one fundamental question: where can someone actually access your… Continue reading on Medium »
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Over 1 Million Baby Monitors, Security Cameras Exposed Through Meari Flaws
Meari IoT flaws reportedly exposed baby monitor images, camera activity, and device data across more than 1 million connected devices. The post Over 1 Million B

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
How to Survive the AIpocalypse & The Big Three Careers of the Future
The AI era is here. Cybersecurity, cloud engineering & marketing may become the safest careers left in the modern world of "Good Enough". Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
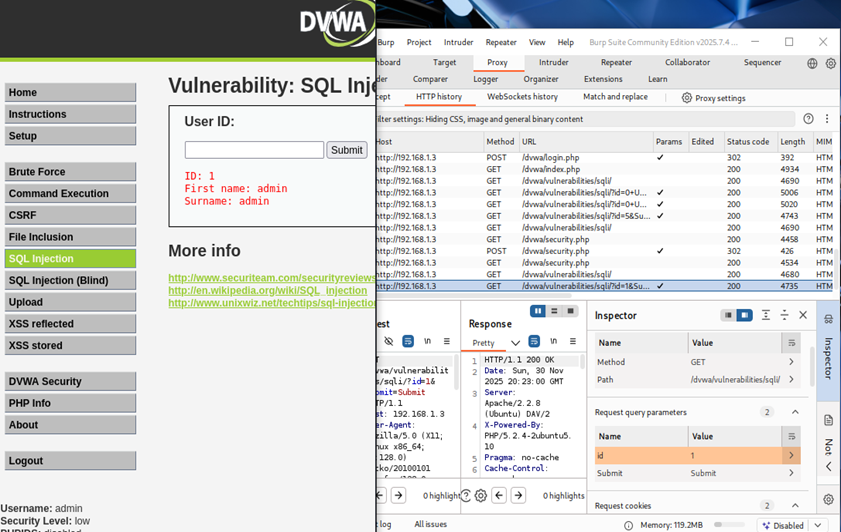
SQL Injection- Walkthrough
Vulnerability Name/Title Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1d ago
Web Application Penetration Testing: What It Is and How It Works
Your web application passed code reviews, sailed through QA, and looked clean in staging. Then someone found a SQL injection in your login… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Web Server Attacks — I | TryHackMe | practical challenge
Enumerate and identify misconfigurations across Apache, Nginx, Node.js, and Python HTTP Server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Introduction to Mark of the Web (MotW) & DLL Sideloading
แค่แปะป้ายว่ามาจาก Internet มันจะช่วยลดภัยคุกคาม Cybersecurity ได้มากแค่ไหนกัน Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
DNS Pentesting: What a Professional Bug Bounty Hunter Actually Checks When Port 53 is Open
When beginners start learning reconnaissance and bug bounty hunting, they usually focus on things like: Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Yggdrasil Network: A Decentralized, Privacy-Focused Mesh
The Yggdrasil Network is an experimental, end-to-end encrypted IPv6 overlay that connects nodes into a self-healing, decentralized mesh… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Metamorphosis (THM) Tryhackme WriteUp Answer
Description : Part of Incognito CTF Continue reading on Medium »
InfoQ AI/ML
🔐 Cybersecurity
⚡ AI Lesson
2d ago
GitHub Expands Secret Scanning with General Availability of MCP Server Integration
GitHub has announced the general availability of secret scanning support through its MCP Server, extending automated credential detection and remediation capabi

Dev.to · Jonathan Pimperton
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Open Directory Listings: The WordPress Security Hole You Forgot
Open Directory Listings: The WordPress Security Hole You Forgot Many web developers and...

Dev.to · Saleem Yousaf
🔐 Cybersecurity
⚡ AI Lesson
2d ago
OT Network Segmentation: The Foundation of Industrial Cybersecurity by Saleem Yousaf
Most OT cyber incidents become major business disruptions because attackers can move laterally...
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Debuggix vs. Snyk: Why "Identifying" Vulnerabilities Isn't Enough Anymore
In DevSecOps, Snyk has been the default. It's great at scanning dependencies. But it's a smoke detector — it tells you the house is on fire, but doesn't hand yo
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Saleem Yousaf insight: Understanding MITRE ATT&CK and MITRE ATLAS for Modern Cloud Security
Security isn’t just about firewalls anymore. Modern attacks target: • Cloud identities • SaaS apps • APIs • Containers • AI systems • Hybrid infrastructure To d

Dev.to · pickuma
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Mythos AI Found a Real Curl Vulnerability — What It Signals for Security Audits
Daniel Stenberg confirmed Mythos surfaced a real bug in curl, one of the most-reviewed codebases on the planet. Here's what that means for AI-assisted security

Dev.to · Vladimir Levchenko
🔐 Cybersecurity
⚡ AI Lesson
2d ago
HIPAA Compliant Software Development: Step-by-Step Guide for Healthtech Founders
Step Two: Conduct a Risk Analysis Before Writing Any Code The HIPAA Security Rule explicitly requires...

Dev.to · Guy Gontar
🔐 Cybersecurity
⚡ AI Lesson
2d ago
When the Pentest Wins: Hardening a Legacy API Without Breaking the Business
The report was a disaster. During a scheduled Penetration Test, the security firm didn’t just find...

Dev.to · Perufitlife
🔐 Cybersecurity
⚡ AI Lesson
2d ago
I shipped a public Apify actor that scans Supabase projects for RLS leaks (took 90 min, found a 895-record leak on the first real test run)
Just shipped a new public Apify actor: Supabase RLS Security Scanner. What it does: paste your...

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
2d ago
What Building an AWS Security Audit Tool Taught Me That Tutorials Never Could
Most cloud security tutorials give you a dangerous illusion. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
DNS Security Misconfigurations: 12 Real-World Cases Every Pentester Should Master
Did you know that a single misconfigured DNS record can open your entire organization to malware, phishing, or even full system compromise… Continue reading on

Dev.to · LayerZero
🔐 Cybersecurity
⚡ AI Lesson
2d ago
Your next supply-chain attack will come from a package you've never heard of
The TanStack npm compromise wasn't sophisticated — one maintainer's token was enough. Here are the three changes that actually shrink your blast radius.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
HSC RTV CTF — Unknown Architect (Reversing — 200 pts)
This was an easy one. The title gives the hint of finding the right architecture in which the binary should be run on. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2d ago
THME Notes — Part 1
Cybersecurity 101 > Windows and AD fundamentals > Continue reading on Medium »
 DeepCamp AI
DeepCamp AI