Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,390 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
It’s Becoming Easier to Sell Cybersecurity Than to Do It
Cybersecurity is everywhere right now. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Authentication Vulnerabilities Lab 06
The Brute-Force Block That Reset Itself Every Time I Logged In Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The 404 That Leaked a Live JWT and Sentry Keys
I requested a URL that didn’t exist. The server handed me an access token, a refresh token, and internal monitoring credentials. Bug… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
What are the best certs in demand 2026?
The job market this year is brutal for generalists but incredibly rewarding for specialists who hold the right credentials. If you want to… Continue reading on

Dev.to · SimpleDrop-Free&Secure File Sharing
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Why End-to-End Encryption Should Be the Default for File Sharing, Not a Premium Feature
As a developer, I've spent a lot of time thinking about how we handle file sharing — and one thing...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Quiet Signal — Hunt Forward Lab #001: C2 Beaconing Detection
Lab Difficulty: Beginner — Estimated Time: 60–90 minutes Continue reading on InfoSec Write-ups »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
2w ago
You Don’t Need Another Certification. You Need Proof You Can Actually Hunt.
Introducing Hunt Forward — the practice platform built for threat hunters who want real experience, not just another badge. Continue reading on InfoSec Write-up

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
You Don’t Need Another Certification. You Need Proof You Can Actually Hunt.
Introducing Hunt Forward — the practice platform built for threat hunters who want real experience, not just another badge. Continue reading on InfoSec Write-up
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
TryHackMe: Overpass 2 — Reading an Attack From a PCAP and Hacking Back In
Why This Room Is Different Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Introduction to Linux for Cybersecurity Beginners
Linux is one of the most widely used operating systems in cybersecurity. Continue reading on Medium »
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Nearly half of cybersecurity pros want to quit - here's why
Research suggests security specialists around the globe are unhappy, but there is hope.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Sinyal Jauh, Risiko Nyata: Pelajaran Keamanan dari Membangun Sistem Gate Ticketing Berbasis LoRa
Ketika sebuah proyek sederhana mengubah gelang QR menjadi RFID dengan transmisi LoRa, pertanyaan tentang keamanan data menjadi tidak bisa… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
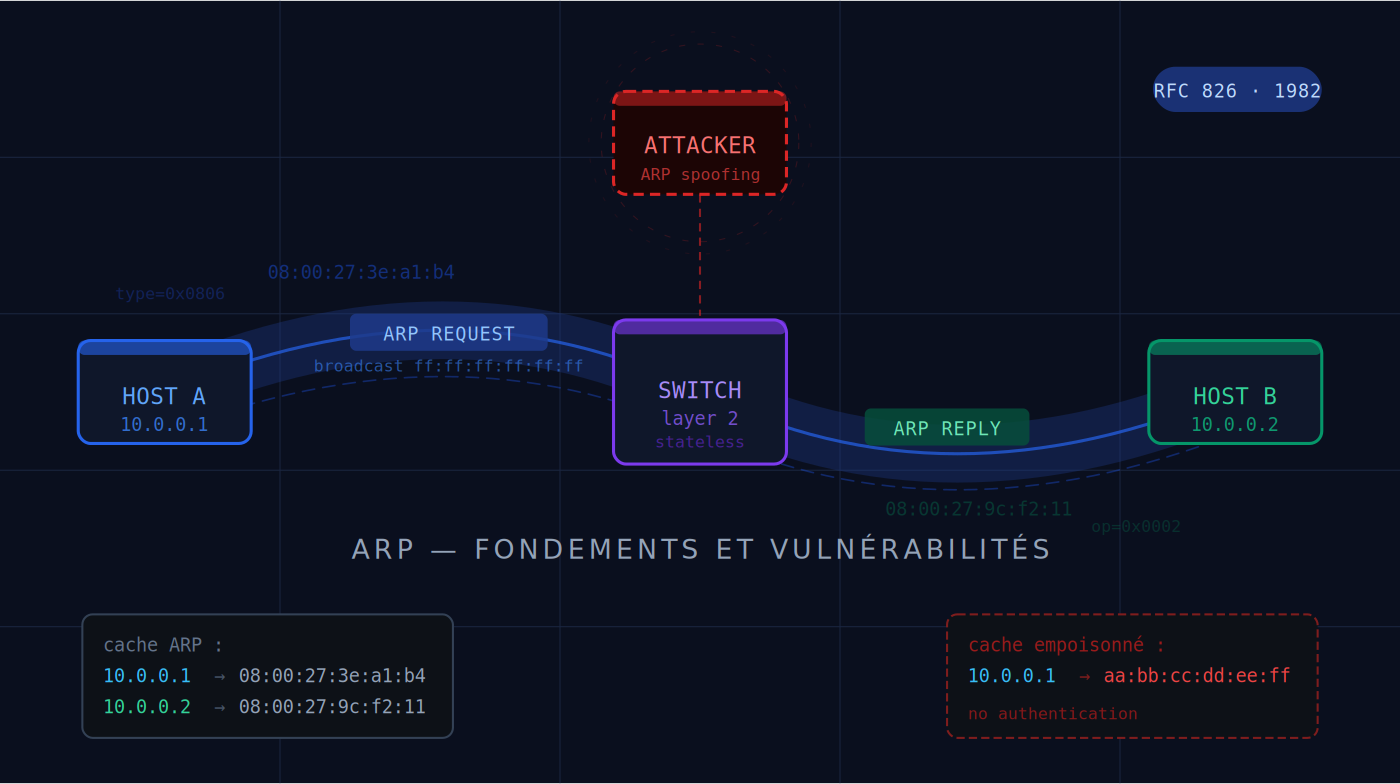
ARP : le protocole silencieux au cœur de chaque réseau — et sa faille fondamentale
Avant de comprendre comment un réseau peut être attaqué à la couche 2, il faut comprendre pourquoi ARP a été conçu ainsi — et ce que cette… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
X’s Head of Product Says iMessage, Gmail, and Phone Calls Will Collapse Within 90 Days.
He’s the Engineer Who Fights Bots for a Living. When He Panics, We Should Pay Attention. Continue reading on Predict »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
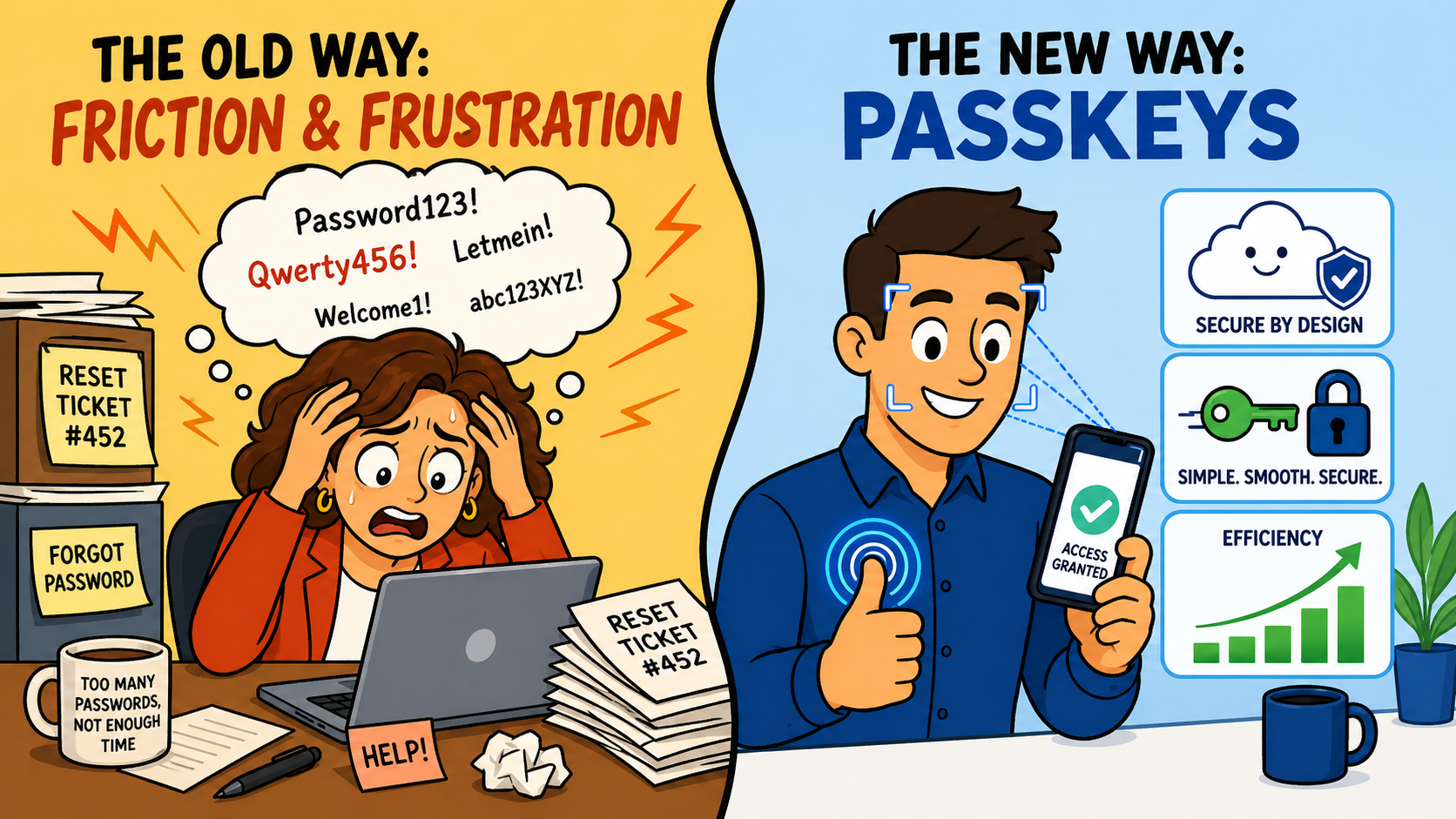
Passwords to Passkeys…
Why Moving Beyond Passwords Is a Leadership Issue, Not Just an IT One Continue reading on Medium »
Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
2w ago
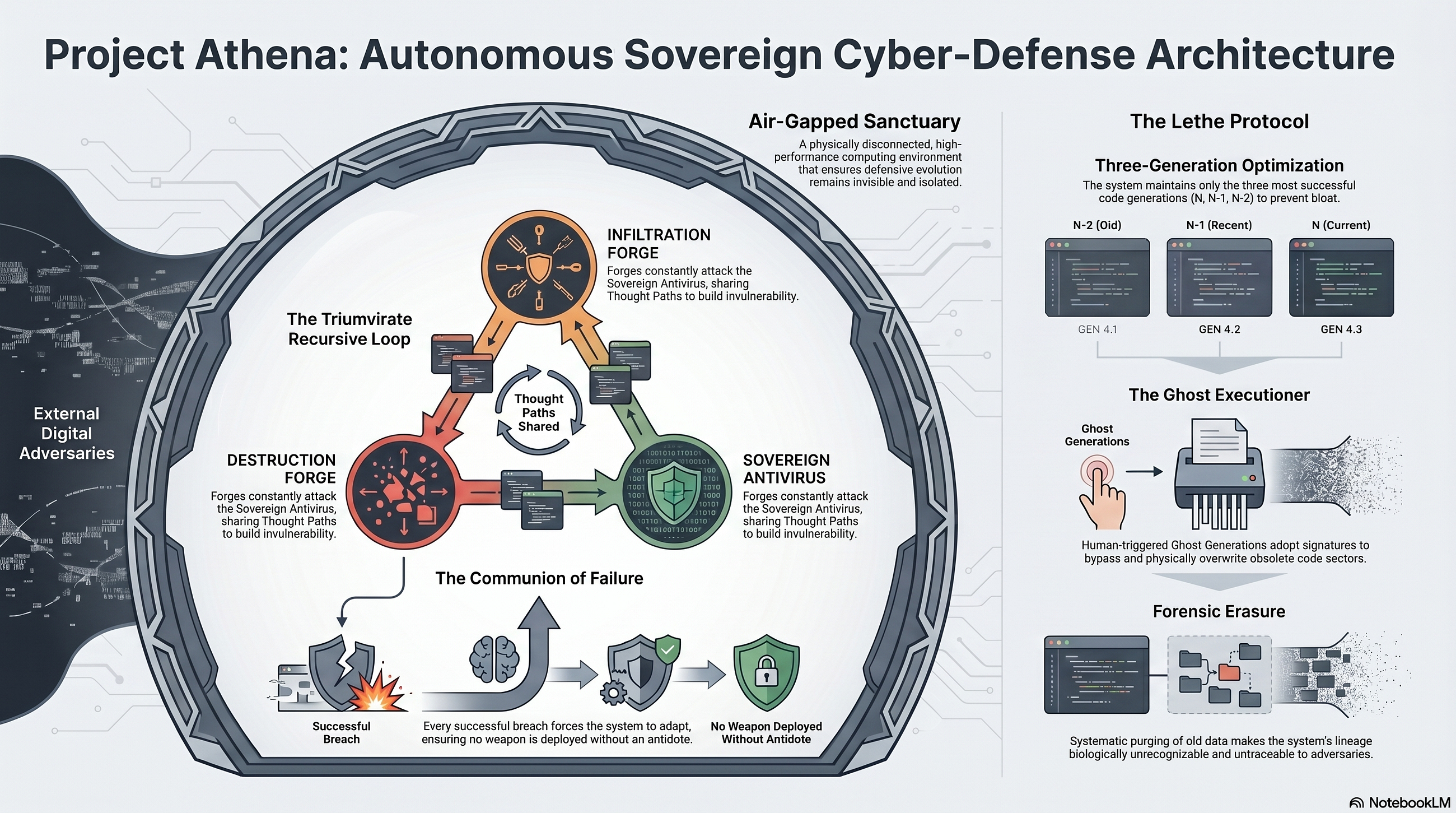
Project Athena: A Deep Dive into Autonomous Sovereign Cyber-Defense Architectures
The modern cyber-defense landscape is fundamentally flawed due to its reactive nature. Conventional Security Operations Centers (SOCs)… Continue reading on Med

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Why Your SPA Shouldn’t Handle Authentication
XSS, CSRF, OAuth 2.0, JWTs, the BFF Pattern, and are you ready for Mythos? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Browser That Knew Too Much
XSS, CSRF, OAuth 2.0, JWTs, the BFF Pattern, and are you ready for Mythos? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Demystifying Hong Kong’s New Cybersecurity Law: A Deep Dive for SMEs (Plus Your Free Compliance…
A few days ago, I wrote about what Hong Kong’s new Protection of Critical Infrastructure (Computer System) Bill (CI Bill) means for your… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Supply Chain Attacks: Exploiting Trust in Modern Digital Ecosystems
Supply chain attacks have emerged as a primary threat vector in modern cybersecurity, not because they rely on entirely new exploitation… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Active Directory Pentesting 101 — Pt1.
# The Basic Definitions Continue reading on Medium »
Hacker News (AI)
🔐 Cybersecurity
⚡ AI Lesson
2w ago
GoDaddy Gave a Domain to a Stranger Without Any Documentation
Comments

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Understanding Cloud Computing Security: Necessity, Risks, and Best Practices
Cloud computing offers “immense benefits — scalability, flexibility, cost-efficiency,” but it also introduces new cybersecurity challenges… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Meet Trestan "Romeo" Renzetti: The 25-Year-Old Paid to Hack the Human Mind
By Roman Zuniga Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
From LinkedIn to Root Access: How a Phone Number, an Old Password Dump, and a Cache Poisoning Bug…
Free Link Continue reading on InfoSec Write-ups »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Social Engineering: The Most Powerful Hacking Technique
Social Engineering: The Most Powerful Hacking Technique Why Hackers Don’t Need to Break In—They Just Ask Let me tell you something… Continue reading on Me

Hackernoon
🔐 Cybersecurity
⚡ AI Lesson
2w ago
How to Secure Accurate Measurements in a Decentralized System Without Oracles
O Coin needs two kinds of truth in code: (1) local water price in each fiat lane where we can observe it, and (2) a connected graph of cross-country references
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Critical SQL Injection in Sourcecodester Complaint Management System (CVE-2020–24932)
How an unauthenticated cid parameter exposed complete databases — what went wrong, how it was fixed, and how to avoid it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
What Scarlet Goldfinch shows us about detection at scale
A year of paste-and-run evolution, the disclosure paradox, and why behavioral chain detection potentially survives the arms race Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
ColdBoxEasy Walkthrough (Proving Ground-play-OSCP)
By cyber_public_school | Cyber Security Researcher Continue reading on Medium »

Dev.to · Haruki Kondo
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Building a Full-Stack ZK-Privacy App on Midnight: A Step-by-Step Guide
Introduction Hello everyone! 🚀 In this post, we are diving deep into Midnight, the...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
“Bug Bounty Bootcamp #36: SSRF Hands-On — Confirming the Server Makes the Request and Reading Local…
You think you found an SSRF. But how do you prove the request came from the server and not your browser? And once confirmed, how do you… Continue reading on Med
Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
2w ago
I Ran 60 Cryptanalysis Experiments on SHA-256. Here’s What I Found.
R0-2: 100% deterministic R3: carry breaks control (→22%) R4: nonce enters R6-7: 26 trackable channels R8: ALL 26 destroyed — 17× drop… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Stop Treating AI Like a Cure. It’s Often Just a Mask.
Sharpening Both Sides: When AI Security Fixes Create New Bugs Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Your Scanner Found Nothing. I Found 3 Bugs — With Just My Brain.
Stop hoarding tools. Start developing the one skill that actually makes you dangerous. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
They Already Know Where You Slept Last Night
Trying to live anonymously in 2026 isn’t paranoia. It’s a full-time job — and you’re probably already losing. Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Update Your Safari Browser —1Password Users Warned
1Password for Safari users have been warned that they must update their browser before May 24, or app security improvements will no longer be available.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
You Don’t Have a Coverage Problem — You Have a Confidence Problem
Most security leaders believe they have coverage. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
What Bug Bounty Culture Isn’t Telling You
The security community has a copy-paste problem. AI is making it worse. And the job market is about to make it matter. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
CROSS-SITE SCRIPTING A HACKERS GUIDE
WHAT IS CROSS SITE SCRIPTING?? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Mahalleden Dünyaya: Bir Veri Paketinin LAN’dan WAN’a Büyük Göçü (Bölüm 6)
Yerel ağın (LAN) tüm sırlarını çözdük; verinin mahalle içindeki o mikroskobik el sıkışmalarını ve dijital zırhlanma süreçlerini en ince… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
The Journey of a Click: How the Internet Actually Works
Most of us treat the internet like magic. You click a link, and a millisecond later, a cat video appears. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
What Threat‑Informed IAM Actually Means (And Why It Matters)
Most identity and access management (IAM) programmes fail quietly. They pass audits, hit delivery milestones, and implement modern tooling… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
Dark Web Myths vs. Reality: A Computer Science Student’s Breakdown
Separating Hollywood fiction from technical fact — because understanding the dark web matters more than fearing it. Every time "dark web"… Continue reading on M

Dev.to · Philippe Quattrociocchi
🔐 Cybersecurity
⚡ AI Lesson
2w ago
# How MemoraEU Cannot Read Your Memories — Even If We Wanted To
How MemoraEU Cannot Read Your Memories — Even If We Wanted To Zero-knowledge architecture...

Medium · JavaScript
🔐 Cybersecurity
⚡ AI Lesson
2w ago
HttpOnly — Your First Line of Defense
I’ve worked on a lot of projects over the years, and some used HttpOnly cookies for auth (access tokens, refresh tokens… let’s be honest… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
HttpOnly — Your First Line of Defense
I’ve worked on a lot of projects over the years, and some used HttpOnly cookies for auth (access tokens, refresh tokens… let’s be honest… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2w ago
SMB Relay Attack Home Lab
How to use a LLMNR Poisoning to steal hashes using SMB Relay attacks Continue reading on Medium »
 DeepCamp AI
DeepCamp AI