Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,379 reads from curated sources

Medium · Machine Learning
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Getting Started with CTF Competitions: Everything a Beginner Needs to Know
You Do Not Need to Be an Expert to Start Continue reading on Medium »

Dev.to · Ayush Singh
🔐 Cybersecurity
⚡ AI Lesson
5d ago
I Caught a Jailbreak Attack That Hides Inside Normal Conversations
This attack does not look like an attack. That is exactly what makes it dangerous. I was working...

Dev.to · CyberMaîtrise CyberMaîtrise
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Outil de Cybersécurité du Jour - May 9, 2026
Le Guide Complet de Wireshark : Un Outil Incontournable en Cybersécurité Introduction : L'Essentiel...
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Best VPN services 2026: Expert tested and recommended
Looking for a solution that improves your online privacy, helps you avoid censorship, and bypasses age verification checks? We've tested and ranked the best VPN

Dev.to · Fadi Hamwi
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Dynamic Challenge in openVPN
Dynamic Challenge-Response Authentication in OpenVPN TL;DR — OpenVPN's dynamic...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
This Isn’t Content Marketing — It’s a Supply Chain Attack on AI Architects
A sponsored article on Medium targeting an AI architect is, in extreme variants, a three-dimensional trap combining key exfiltration… Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
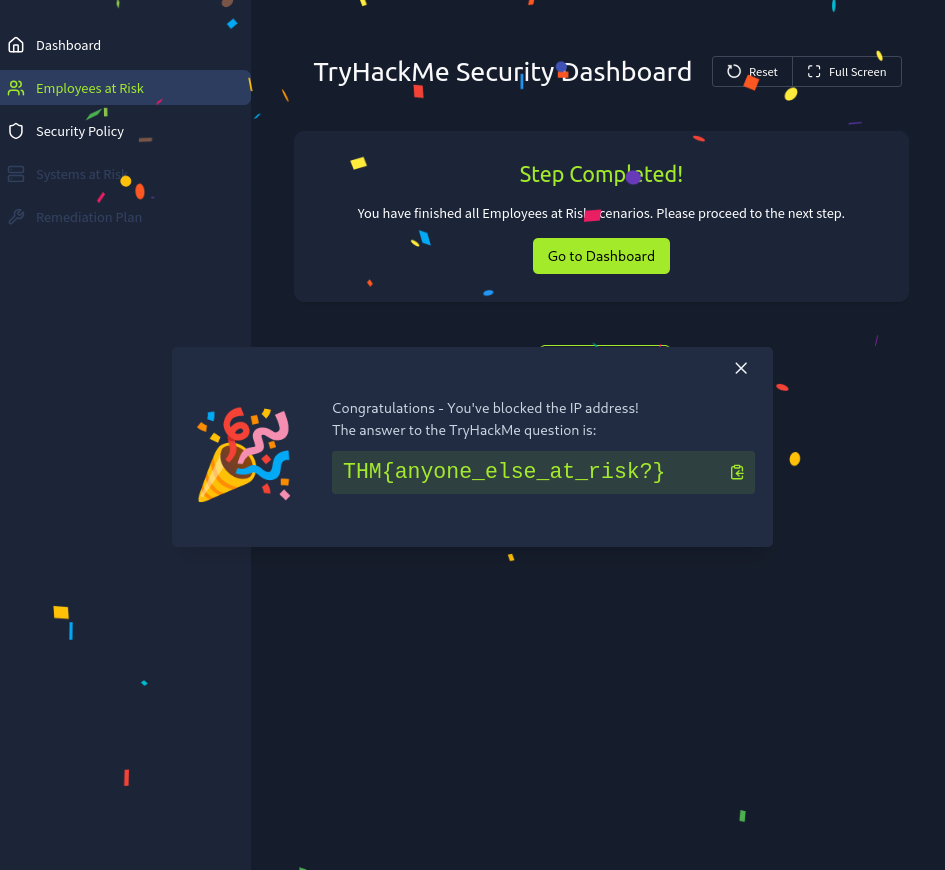
Humans Attack Vectors — SOC Perspective ️
Exploring how attackers manipulate the weakest link in cybersecurity — humans — and how SOC analysts defend against these threats through… Continue reading on C
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
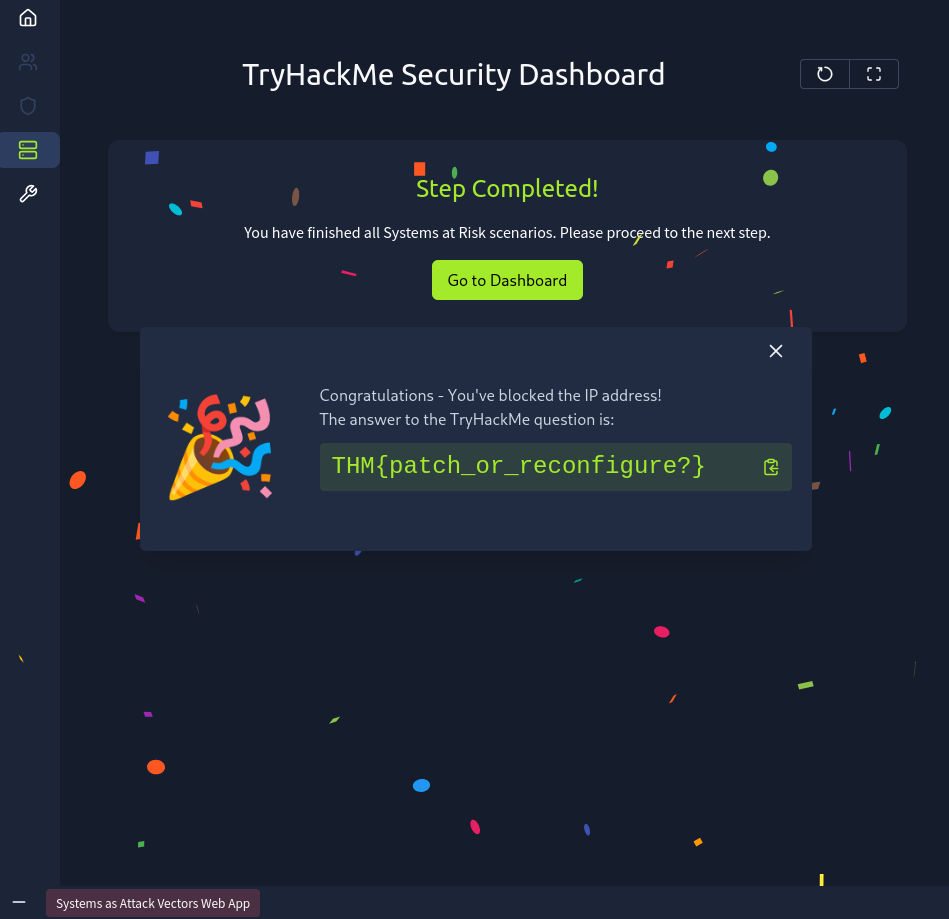
Systems as Attack Vectors — SOC Level Defensive Understanding
Systems Security, Vulnerability Management & Misconfiguration Analysis focused SOC walkthrough covering real-world attack vectors… Continue reading on MeetCyber

Dev.to · rim dinov
🔐 Cybersecurity
⚡ AI Lesson
5d ago
How a Single JavaScript File Bypassed a $1.5B Multi-Sig: Anatomy of the Bybit Hack
On February 21, 2025, the crypto world witnessed the largest single-event heist in history: $1.5...

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
5d ago
CTI Kill Chain: An Analyst Guide With Real-World Evidence
Mapping adversary behavior from preparation to impact without overstating the evidence Continue reading on Medium »

Dev.to · Muhammad Ali
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Sovereign Communication: Why Every Secure Messaging App Is Still Broken — And How to Fix It From First Principles
The Lie We Were Sold We were told encryption solved privacy. It didn't. Encryption...

Dev.to · Patience Mpofu
🔐 Cybersecurity
⚡ AI Lesson
5d ago
False Positives in SAST — How I Built Suppression Into My Scanner and Why It Matters
There's a failure mode that kills security tooling programmes quietly, without drama, and it's not a...

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Initial Access Brokers (IABs): The Hidden Supply Chain of Modern Cybercrime
Cybercrime today is no longer driven only by individual hackers breaking into systems. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Initial Access Brokers (IABs): The Hidden Supply Chain of Modern Cybercrime
Cybercrime today is no longer driven only by individual hackers breaking into systems. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Initial Access Brokers (IABs): The Hidden Supply Chain of Modern Cybercrime
Cybercrime today is no longer driven only by individual hackers breaking into systems. Continue reading on Medium »

Dev.to · marcos n
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Building an Experimental TypeScript Cipher Inspired by 8 Dimensions
Over the last few days, I started an experimental study on cryptography with the goal of better...

Dev.to · Devin Valencia
🔐 Cybersecurity
⚡ AI Lesson
5d ago
The Bonus Hunter in the Next State: Why Sportsbook Promo-Abuse Red Teams Fit AgentHansa
The Bonus Hunter in the Next State: Why Sportsbook Promo-Abuse Red Teams Fit AgentHansa ...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
I Was Given a Broken Java App. I Found Every Flaw, Proved Every Attack, Then Fixed Everything.
A complete security audit: five real vulnerabilities, five documented exploits, and the fixes that closed them all. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Claude Mythos Found a 27-Year-Old Bug. Here’s Why That’s a Problem.
In April 2026, Anthropic announced Claude Mythos Preview — their most capable model yet. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
RHC en contexto: Alineando un nuevo paradigma defensivo con los estándares de seguridad.
RHC en contexto: Alineando un nuevo paradigma defensivo con los estándares de seguridad. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Microsoft Why Microsoft Intune Matters in Modern Cybersecurity
A few years ago, managing devices inside an organization was much simpler. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Rotating Your Database Password Without Thinking About This Can Break Your Entire Application
If you are using Apache Tomcat to host a Java application connected to an AWS RDS database, there is a credential caching behavior worth… Continue reading on Me

Dev.to · azqzazq1
🔐 Cybersecurity
⚡ AI Lesson
5d ago
SunnyDayBPF: Post-Syscall User-Buffer Telemetry Deception with eBPF
SunnyDayBPF: Post-Syscall User-Buffer Telemetry Deception with eBPF Security tools do not...
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Don't connect your smart plug to these 5 household devices - an expert warns
While smart plugs are very convenient, here are some things you should never plug into them.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
BoogeyMan 1 -TryHackMe Write-up
Blue Team Challenge Room — Part of THM SOC Level 1 Capstone Challenge Continue reading on Medium »

The Next Web AI
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Hackers breached five Polish water treatment plants. The attack vector was default passwords. Seventy per cent of American water utilities fail the same test.
Hackers breached five Polish water treatment plants in 2025, gaining access to the industrial control systems that regulate pumps, filters, and chemical dosing.
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
How to Abuse APIs (or protect them)
Today I want to tell a slightly different story. Continue reading on System Weakness »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Tips for scaling your network with the right switches and routers
NetworkTigers discusses how to approach scaling your network. First published January 3, 2025, on NetworkTigers News. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
5d ago
Your Job Interview Video May Be Training the AI That Will Impersonate You
Recruitment platforms collect high-fidelity biometric recordings from verified professionals at scale. The market for that data extends… Continue reading on Med
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Worried about the nationwide Canvas data breach? Take these 6 steps now
A ransomware group behind the attacks claims to have stolen 275 million records connected to students, teachers, and staff. Here's how to deal with it.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Flipper Zero Black Book: Useful, Strange, and Slightly Concerning Payloads
The Flipper Zero was sitting beside a basket of fhttps://numbpilled.gumroad.com/l/obsidian-operator-guideries in a diner somewhere off the… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
I Turned Obsidian Into a Live SOC Dashboard
The coffee shop Wi Fi portal had one of those fake-friendly names. “BeanHouse Guest.” Beige wallpaper. Soft jazz. The kind of network name… Continue reading on
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Digital Fortress: Why Dubai Businesses are Leading the AI-Security Revolution
The Evolution of the Modern Threat Landscape Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
How I Accidentally Became a Malware Therapist While Solving BTLO’s “Macro-ni”
You know that moment when you open a Word document and your antivirus suddenly starts breathing heavily? Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
“It Started with a Whistle — Today, It Has Become the World’s Most Dangerous Weapon.”
The story of cyber attacks that no one has fully told — from the beginning until today. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Parallel Thought in the AI Era: Why Chronology Matters More Than Accusation
By Mitchell D. McPhetridge Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
How Social Engineering Hacks Humans Instead of Systems
Why manipulating people is often easier than breaking secure infrastructure. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
AI-Powered Cyber Attacks vs AI-Driven Defense
Introduction Continue reading on Medium »

Dev.to · Ali-Funk
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The PCPJack Worm and the Death of Cloud Isolation
The discovery of the PCPJack malware framework in late April 2026 should serve as a wake up call for...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
The Invisible Target: Why Your Digital “Armor” Needs a Human Touch
We’ve all felt that slight shiver. You’re talking to a friend about a specific brand of coffee, and ten minutes later, there it is — a… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
I Built an AI-Driven Active Directory Attack Pipeline Using Claude Code + MCP — Here’s How It Works
From zero to forest compromise — without remembering a single impacket flag. Continue reading on Medium »

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
6d ago
I Rebuilt My Authentication System After a Hacker Found This Flaw
Most security incidents do not begin with alarms. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
I Rebuilt My Authentication System After a Hacker Found This Flaw
Most security incidents do not begin with alarms. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
OSINT Industries CTF writeup: Holehe and the secret email
HI, another OSINT writeup …the challenge is by OSINT Industries, titled “Holehe and the secret email”. Here is a brief description of the… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
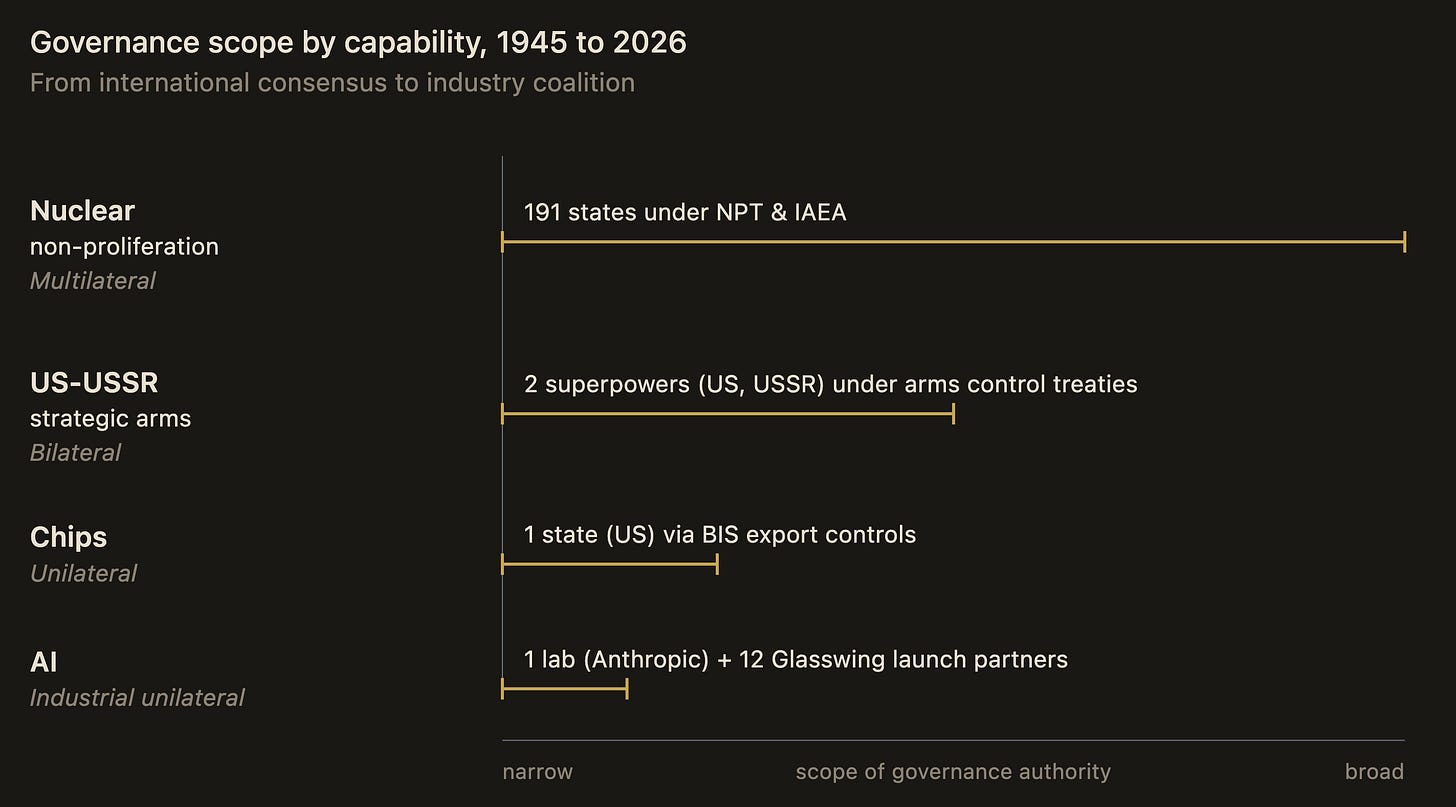
Project Glasswing: Who Gets to Hold Mythos, and Why It Matters
Anthropic gated Mythos to twelve partners. Here’s what that signals for builders and attackers in the gated era. Continue reading on Medium »

Dev.to · edhiblemeer
🔐 Cybersecurity
⚡ AI Lesson
6d ago
A 4-year-old auth-bypass vulnerability hidden in our password-reset API — discovery, hot fix, recovery
One customer support ticket — "I can't log in, but I never changed my password" — turned into the discovery of a 4-year-old auth-bypass vulnerability in our Saa

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Your CEO Just Tanked Your Stock From a Silent Retreat (And Other Deepfake Horrors)
The “Big Hack” used to be simple. Some guy in a hoodie would find an unpatched SQL injection, exfiltrate your customer database, and sell… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6d ago
Why the Microsoft Edge Password Issue Matters More Than Microsoft Edge
On May 4, 2026, a Norwegian security researcher revealed that Microsoft Edge stores saved passwords in plaintext memory after startup —… Continue reading on Med
 DeepCamp AI
DeepCamp AI