Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,381 reads from curated sources

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Microsoft Edge Password Exposure: How a Memory Dump Reveals Your Credentials
By: Kavin Jindal (@Klevr) Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
CVE-2026–31431 Explained: Detecting and Mitigating the Linux Copy Fail Vulnerability — Chandra Home…
A newly disclosed Linux kernel vulnerability known as “Copy Fail” (CVE-2026–31431) allows local attackers to escalate privileges to root… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Manual Lies: 7 Things Flipper Can Actually Do
The box says “multi-tool for geeks.” The manual shows you how to emulate your TV remote and copy an Amiibo. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
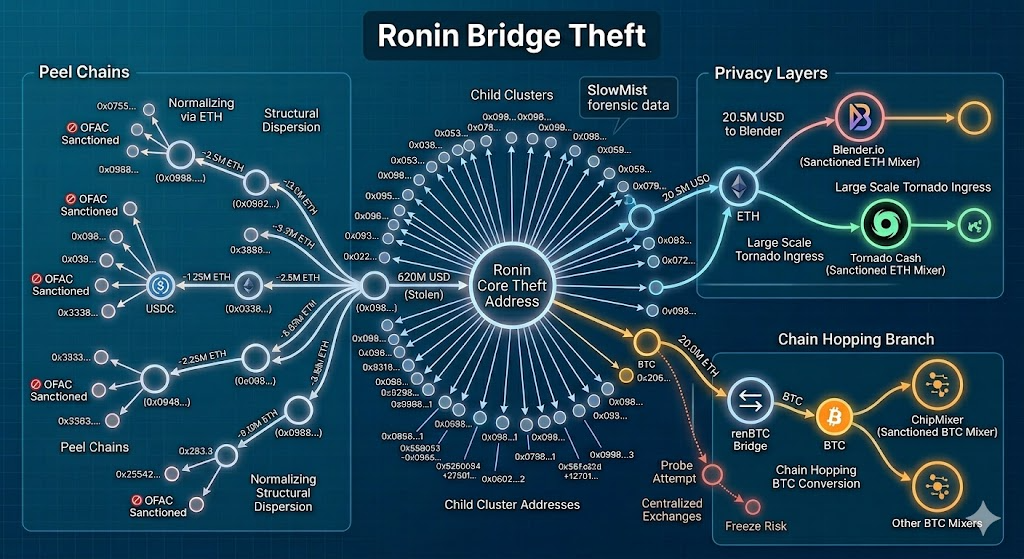
Why the Same Name Keeps Appearing at the End of Every Major Crypto Hack
The Lazarus Group’s Laundering Architecture: Lessons from Ronin, Harmony Horizon, and Atomic Wallet Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Continuous Verification: Why Future Systems May Never Fully Trust Anything
Trust Was Originally Temporary Continue reading on Medium »
Medium · Python
🔐 Cybersecurity
⚡ AI Lesson
1w ago
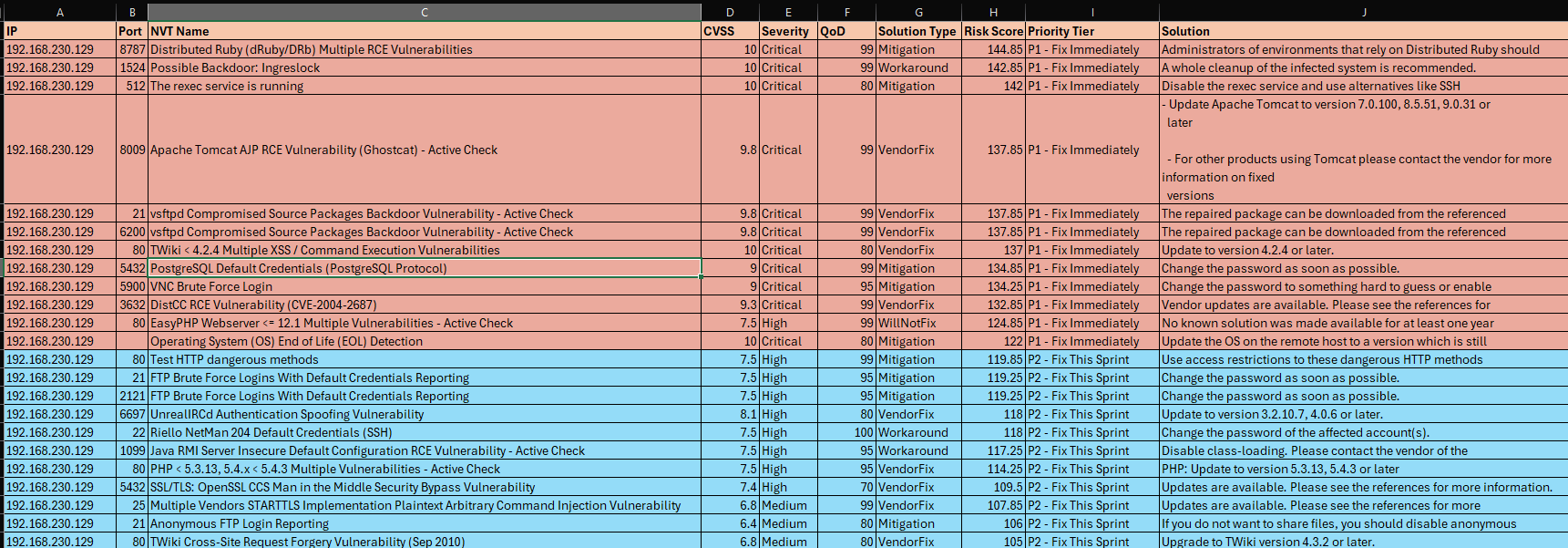
I Built a Home Vulnerability Management Lab for $0 — Here’s What I Actually Learned
Most cybersecurity beginners stop at running a scan. I went further and it changed how I think about risk. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Your Phone Knows More Than You Think — Here’s How New Tech Is Fighting Back
Your phone quietly tracks where you go, who you talk to, and what you search. While this data powers modern apps, it also raises serious… Continue reading on Me

Dev.to · Oluwagbade Odimayo
🔐 Cybersecurity
⚡ AI Lesson
1w ago
I Built a Real-Time DDoS Detection Engine from Scratch - Here's Every Decision I Made
No Fail2Ban. No rate-limiting libraries. No shortcuts. Just Python, a deque, and...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The $450,000 Email That Looked Exactly Right
On a Monday in Ohio , a vendor email rerouted half a million dollars out of a country treasury. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
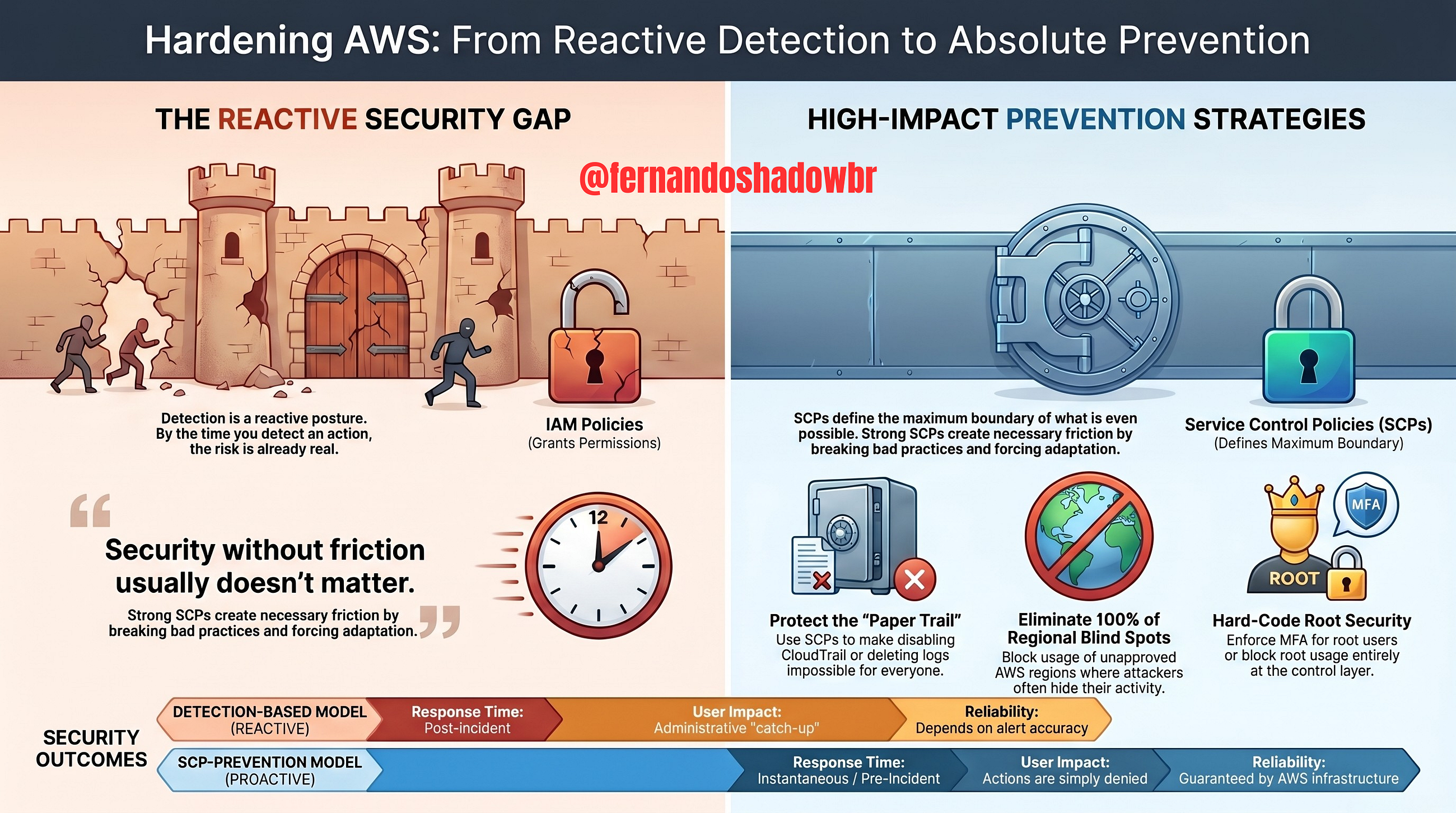
Why most AWS environments are one SCP away from being compromised
If your SCP strategy is weak, you’re not controlling risk; you’re just hoping your detections catch it in time. Continue reading on Medium »
Dev.to AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Travel Scammer's Playbook: How to Protect Your Data Abroad
The Travel Scammer's Playbook: How to Protect Your Data Abroad Quick Answer (TL;DR) Always use a reputable Virtual Private Network (VPN) on public Wi-Fi to encr

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why Your MDR Looks Healthy While Detections Are Quietly Breaking
Four silent failure modes in MDR detection, and the observability layer most teams aren’t watching. Continue reading on Medium »

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The $442 Billion Siege: Why Your Banking App Is the Most Dangerous App on Your Phone
A silent war is already underway Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The $442 Billion Siege: Why Your Banking App Is the Most Dangerous App on Your Phone
A silent war is already underway Continue reading on Medium »

Hackernoon
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Vibe-coded Mac apps are arriving fast — here is what gets lost in the process
AI-powered “vibe-coded” Mac apps are flooding GitHub, promising free alternatives to tools like CleanMyMac. But many lack reliability, proper permissions handli
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Active Reconnaissance: TryHackMe Walkthrough
Task 2: Web Browser: Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
RAM Is Lying to You — and Rowhammer Is the Proof
Your RAM is supposed to be one of the safest parts of your computer. It doesn’t have persistent storage. It can’t be “infected” the way a… Continue reading on M
ZDNet
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why Edge stores your passwords in plaintext, according to Microsoft
The behavior is by design, says Microsoft. But is this still a security risk?

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
TryHackMe: Bounty Hacker WriteUp
TryHackMe: Bounty Hacker Write-Up Continue reading on Medium »
Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1w ago
usefulness of Ipv4
IPv4 has been around for decades, and here are some of its advantages: -: IPv4 is widely supported by devices, networks, and applications… Continue reading on M
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
usefulness of Ipv4
IPv4 has been around for decades, and here are some of its advantages: -: IPv4 is widely supported by devices, networks, and applications… Continue reading on M

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
1w ago
The Future of Connectivity: Why Precision Fiber Testing is Non-Negotiable
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Why FC-10–0040F-247–02–12 is the Essential SMB License for the 2026 Threat Landscape
Navigating the 2026 threat landscape: A deep dive into why the FC-10–0040F-247–02–12 SKU is the ultimate insurance policy for your network. Continue reading on

Medium · AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
AI Just Made Kernel Zero-Days Cheap. Your Patch Process Is Not Ready.
Theori’s AI tool found a 9-year-old root-escalation bug in the Linux kernel in about an hour. Continue reading on That Infrastructure Guy »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
1w ago
AI Just Made Kernel Zero-Days Cheap. Your Patch Process Is Not Ready.
Theori’s AI tool found a 9-year-old root-escalation bug in the Linux kernel in about an hour. Continue reading on That Infrastructure Guy »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Someone Cloned My Startup. I Spent the Morning Taking It Down.
It was 8:47 AM and I was going through Ahrefs over coffee when I noticed something odd. A domain I’d never heard of was showing up in my… Continue reading on Me
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Zero Trust: The Newest Old Idea Everyone Just Discovered
I am still perseverating on Zero Trust. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
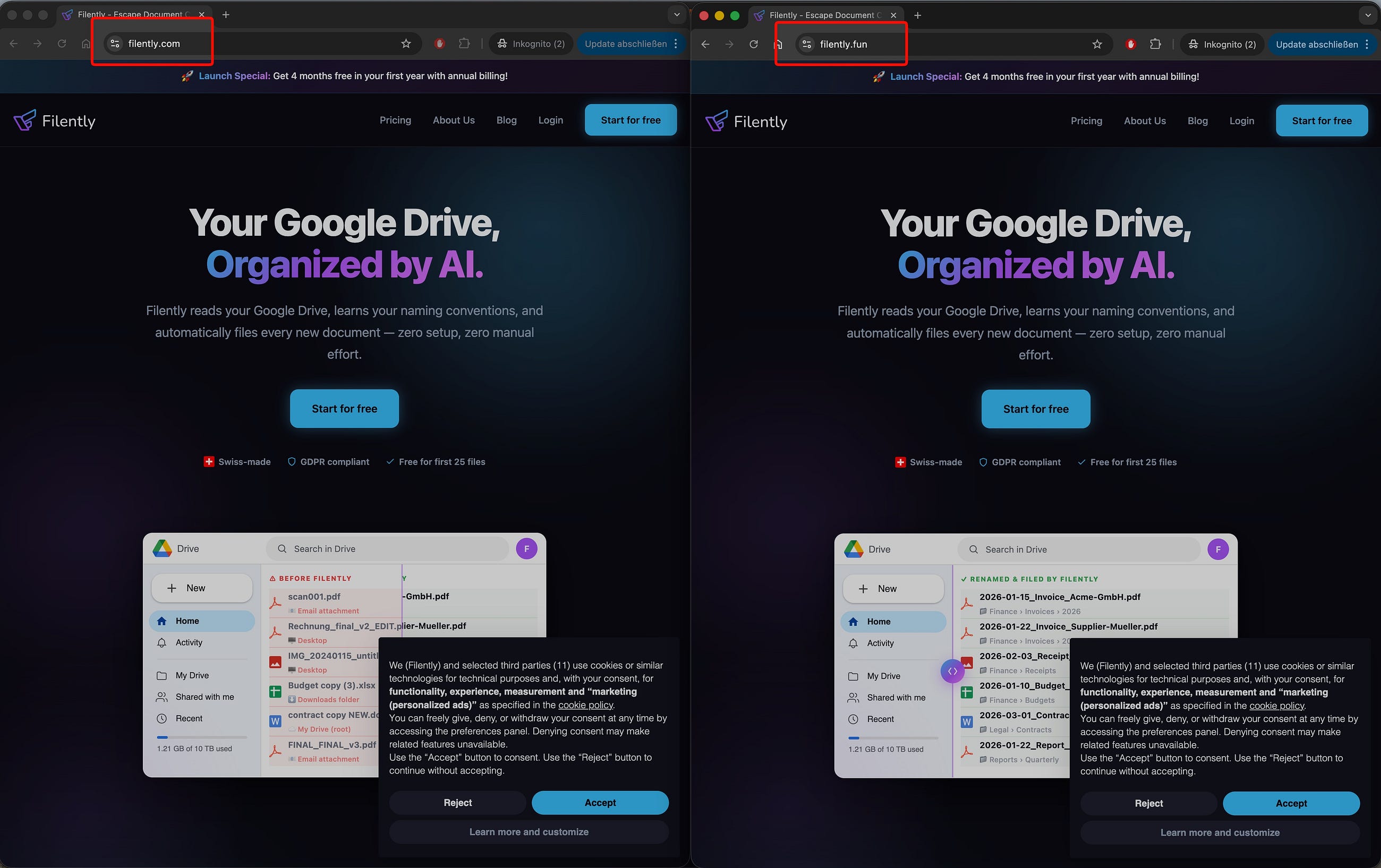
How AI is Turning Cyber Note into Actionable Intelligence
Inside CenTinel 3.1 — a pipeline that transforms raw security logs into real-world threat insights Continue reading on Coffee☕ And Code »

Dev.to · Quantum Sequrity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Lattice-Based Cryptography: Foundation of PQC
Learn how lattice-based cryptography works, why the Learning With Errors problem is quantum-resistant, and how ML-KEM and ML-DSA use it.
The Next Web AI
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Chinese chamber of commerce puts a $432bn price tag on the EU’s cybersecurity overhaul
A KPMG-conducted study commissioned by the CCCEU estimates that phasing Chinese suppliers out of 18 critical EU sectors between 2026 and 2030 would cost €367.8b

Dev.to · Dwayne McDaniel
🔐 Cybersecurity
⚡ AI Lesson
1w ago
No Off Season: Three Supply Chain Campaigns Hit npm, PyPI, and Docker Hub in 48 Hours
After a few quieter weeks, three supply chain attacks put secrets back in the spotlight. Between...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Is Cyber Security Certification Worth the Cost in India?
Cyber security has become an important part of today’s world as more people and businesses depend on online systems. From banking to… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
J’ai arrêté de faire des screenshots : comment l’automatisation a sauvé mon audit SOC 2 type 2.
C’est officiel : chez AssessFirst, nous avons lancé l’audit SOC 2 Type 2 !Après avoir consolidé notre ISO 27001, cette nouvelle étape… Continue reading on Mediu
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
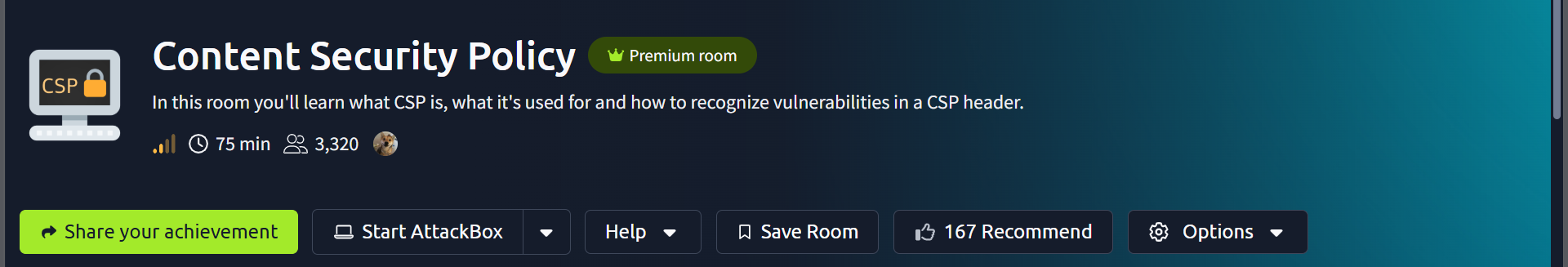
Content Security Policy | TryHackMe
In this room you’ll learn what CSP is, what it’s used for and how to recognize vulnerabilities in a CSP header. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Banking 3.0 | The Bankpocalypse Horror Story
How to Avoid the Doomsday Triggered by Mythos-Like AI Models and safeguard billions of banking customers! Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
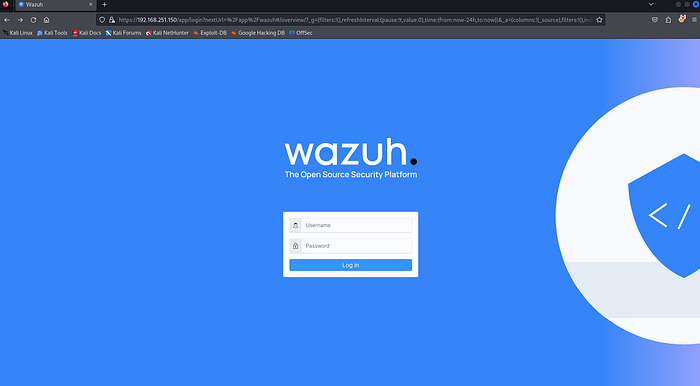
Step-by-step setup of Wazuh SIEM
Ubuntu server setup. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
CYBERDUDEBIVASH ENTERPRISE SECURITY ARCHITECTURE
Author: CyberDudeBivash Powered by: CyberDudeBivash Brand | cyberdudebivash.com Related: cyberbivash.blogspot.com… Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
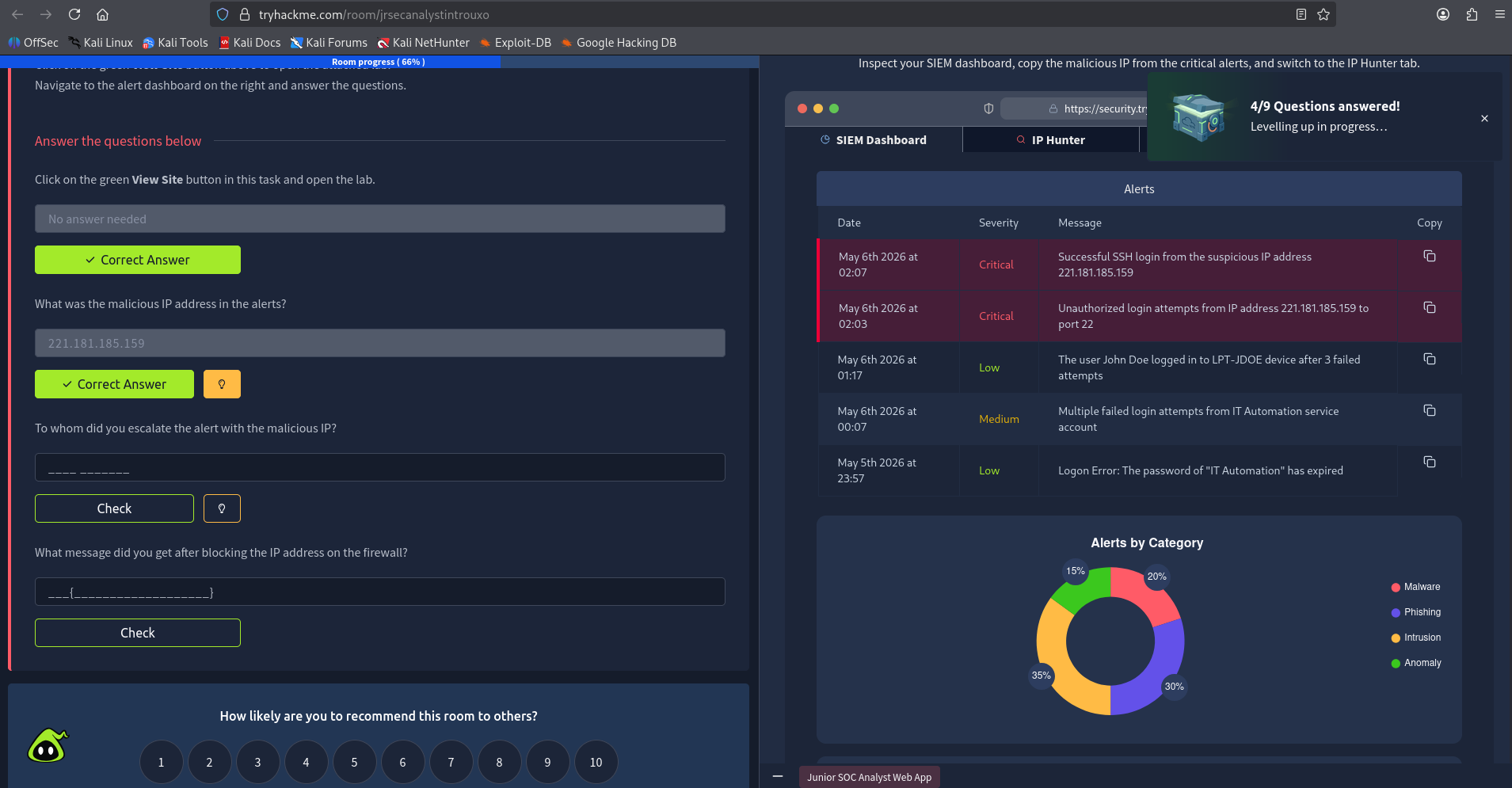
TryHackMe — Junior Security Analyst Walkthrough
SOC | Blue Teaming | Incident Response — Investigated malicious alerts, escalated incidents within a simulated SOC environment, and… Continue reading on InfoSec
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Building a Tier-1 Firewall Troubleshooting Runbook: A Practical Framework for IT Support Teams
By Ahamd Alassadi— Network Security Engineer Reading time: 7 minutes Continue reading on Medium »

Dev.to · CVE Reports
🔐 Cybersecurity
⚡ AI Lesson
1w ago
CVE-2026-6970: CVE-2026-6970: Local Privilege Escalation via Improper GID Assignment in Canonical authd
CVE-2026-6970: Local Privilege Escalation via Improper GID Assignment in Canonical...

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Urgensi Keamanan Berbasis Identitas: Mengatasi Kerentanan Autentikasi di Infrastruktur Digital
Di balik sistem keamanan yang paling kompleks sekalipun, identitas pengguna tetap menjadi salah satu target utama bagi para peretas… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Tether, Binance, and Others Freeze $41.5M of Stolen Funds
Stablecoin issuer Tether, alongside Binance, OKX, US law enforcement, and independent security agents, has frozen over $41.5 million tied… Continue reading on M

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
1w ago
“Bisnis Kecil Nggak Bakal Kena Hack” Mitos yang Bisa Membunuh Usahamu
43% serangan siber di Indonesia menyasar usaha kecil. Bukan perusahaan besar. Bukan bank. Tapi bisnis seperti punyamu. Continue reading on Medium »

Medium · JavaScript
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Reflected XSS into a JavaScript string with HTML-encoded angle brackets (<,>)
Input is reflected immediately inside a JavaScript string, where angle brackets ( ) are HTML-encoded Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Waspada Malware! Mengenal Jenis-Jenisnya, Cara Mengatasi, dan Mencegahnya
HP tiba-tiba lemot, data hilang, atau tiba-tiba ada tagihan aneh? Bisa jadi perangkatmu sudah terinfeksi malware. Yuk kenali musuhnya… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
An AI Deleted Another Database. The Real Story Isn’t the AI.
PocketOS, Replit, and the three architectural control gaps behind agent-driven production failures. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
Learning Fortinet Firewall — LESSON 8: Software Switch / Layer 2
Welcome to my Fortinet Firewall (FortiGate) learning journey! Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
1w ago
See You Space Cowboy: Bounty Hunting Threats with Splunk
Spike Spiegel didn’t wait for bounties to come to him. He hunted them down. Continue reading on Medium »
 DeepCamp AI
DeepCamp AI