Tech Skills
Cybersecurity
Ethical hacking, penetration testing, network security, CTFs and defensive security
Skills in this topic
8 skills — Sign in to track your progress
Security Basics
beginner
Fix OWASP top 10 vulnerabilities
AI Security
intermediate
Identify and patch prompt injection vulnerabilities
Network Security
intermediate
Configure a firewall with proper inbound/outbound rules
Ethical Hacking & Pen Testing
intermediate
Conduct a full pen test with Kali Linux
Cloud Security
intermediate
Implement IAM least-privilege policies on AWS/GCP
Incident Response
intermediate
Build an incident response playbook
Security Compliance
intermediate
Map controls for SOC 2 Type II compliance
Defensive AI
advanced
Build an AI-powered log anomaly detector
Showing 1,418 reads from curated sources

Medium · Programming
🔐 Cybersecurity
⚡ AI Lesson
3w ago
How to Investigate a Suspicious PowerShell Command
Most analysts see that alert and do one of two things: close it as a false positive because “PowerShell runs all the time,” or immediately… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
How to Investigate a Suspicious PowerShell Command
Most analysts see that alert and do one of two things: close it as a false positive because “PowerShell runs all the time,” or immediately… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Episode 2: Networking for Hackers (How Data Bleeds) (The Hacker’s Path Series)
Hook — Real-World Scenario Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
3w ago
‘Starting In April’—Microsoft Changes Windows Update After 15 Years
Security certificates on more than a billion Windows PCs expire in 8 weeks — check yours now.

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Simple Cybersecurity Tips to Protect Your Online Business
Running an online business comes with many opportunities, but it also introduces serious risks — especially when it… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Part 06 — Building a Security Operations Center Homelab (Installing Zeek on TheGateWatcher)
Hello everyone, and welcome back to the Building a Security Operation Center Series. :) Previously, in Part 05 we installed and setup… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
SQL Injection
Low Level Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
How Payment Data Leaks
Payment data often leaks through small weak points in apps, APIs, logs, storage, and human mistakes. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
My Fix Was Right. Then It Was Commented Out.
How a MongoDB type quirk turned working security code into dead code — and how a real user paid the price before we caught it. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
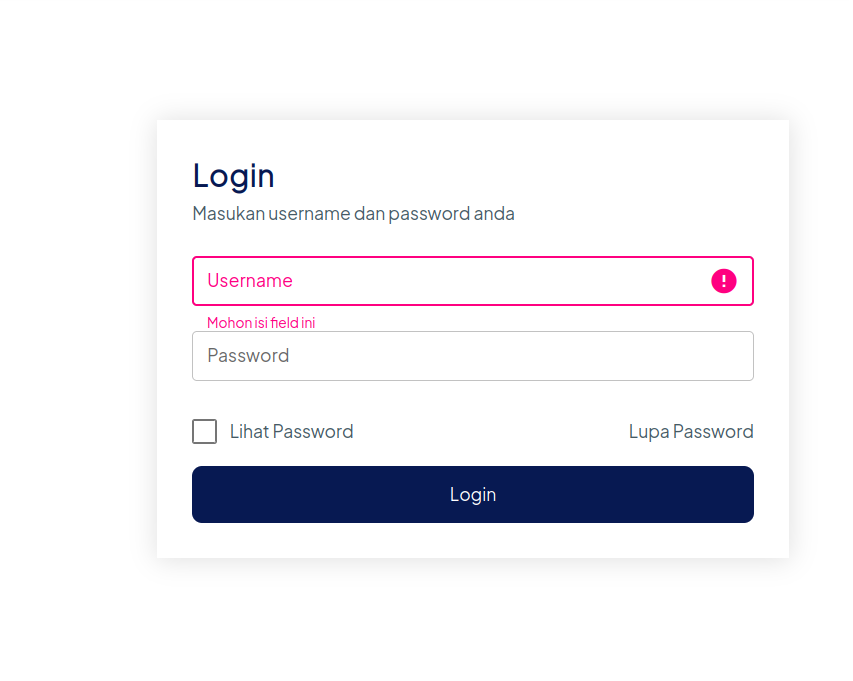
How I Found My First CVE — SQL Injection Authentication Bypass (CVE-2026-37749)
admin'-- - and i was in. The story behind CVE-2026-37749 Continue reading on Medium »

Medium · Startup
🔐 Cybersecurity
⚡ AI Lesson
3w ago
A founder's perspective on cybersecurity, machine learning, and building scalable startups in…
Why Nigerian startups must prioritise cybersecurity while building with AI and scaling in today’s fast-growing tech ecosystem Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
A founder's perspective on cybersecurity, machine learning, and building scalable startups in…
Why Nigerian startups must prioritise cybersecurity while building with AI and scaling in today’s fast-growing tech ecosystem Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Your Phone Is Listening — Here’s What I Actually Found When I Checked
I spent two weeks digging into my own data. The truth is weirder than the conspiracy. Continue reading on ILLUMINATION »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
PASETO vs JWT: 2026 Cryptographic Hardening | FmtDev
The Architectural Shift: Moving Beyond Legacy Authentication Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The end of ‘seeing is believing’
Recruiters are adding questions to video interviews that have nothing to do with the job. They’re not screening for skills; they’re… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Complete Guide to JWT Vulnerabilities: Detection, Exploitation, and WAF Bypass
Master the fundamentals of JSON Web Tokens, attack methods such as key confusion, and advanced security bypass strategies. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Penetration Testing Agreement
As part of my cybersecurity training with ParoCyber, we were tasked with drafting a professional penetration testing agreement for a… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Reentrancy Attack: Exploitation, Defense, and Audit
Thousands of smart contracts are deployed every day on the EVM (Ethereum Virtual Machine), described as “the world’s shared computer.”… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
From Zero to Hero: Building and Breaking Your First CTF Lab
Are you ready to dive into the world of ethical hacking but don’t know where to start? Most beginners get overwhelmed by complex setups… Continue reading on Med

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Threat Hunting with Splunk — C2 Communication Investigation
1. Objective Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
AS-REP Roasting: When Pre-Auth Is Off and the Hash Is Free
Kerberoasting gets most of the spotlight, but its quieter cousin AS-REP Roasting is just as dangerous — and in some ways worse, because it… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Cybersecurity Villains Lurking Around Your Business Right Now
Every business owner has had that moment. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Understand the Significance of $ITL and $ITLG in Daily Life, Allowing for Direct or Converted…
Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
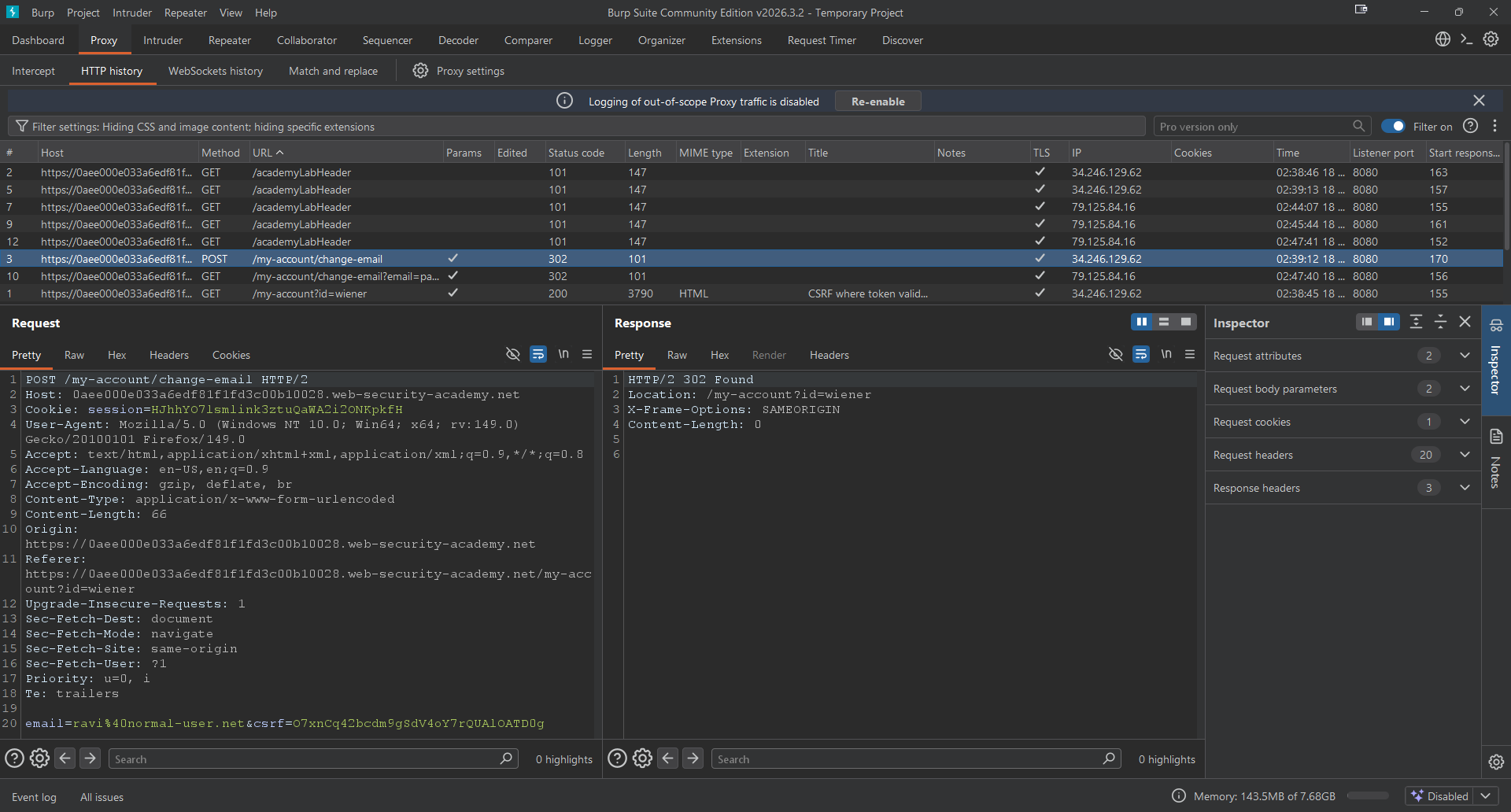
Day 5 — CSRF Token Bypass using GET Request
Hello everybody, I hope you guys are doing well. Continue reading on Medium »

Forbes Innovation
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Is Fuzzing Just AI Pen Testing?
Fuzzing finds hidden bugs in trusted systems, improving security, reliability, and resilience against real-world threats.
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Clothing Retailer Patches Website Flaw Exposing Customer Data
A clothing retailer patched a website flaw that exposed customer data via order links, highlighting risks associated with predictable URL structures. The post C
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Your Company Audits Its Vendors. But Who’s Auditing Their Vendors?
A gap I found while studying GRC that honestly surprised me Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Your Digital ID is Leaking: Here is How to Audit Your Online Privacy in 2026
Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
How Many Forgotten API Keys Are Still Spending Money in Your Name?
AI tools are getting easier for everyone to use. The real risk is no longer “the model is too weak.” It is that you may have left a paid… Continue reading on Me

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Future of Cybersecurity — Staying Ahead of Threats
Cybersecurity is not a destination. It’s a continuous battle. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Endpoint Security Risk: Why Every Device Is a Potential Entry Point
Your network is only as secure as its endpoints. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Is Your Organization Being Watched?
Learn What Cyber Threat Report Is Telling Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Securing the Backbone — Issue #18: It’s What’s Inside the Container That’ll Get You
Date: June 23, 2025 Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
From Theory to Practice: Drafting My First Pentesting Agreement
In the world of cybersecurity, the difference between a hero and a hacker often comes down to one thing: authorization. Continue reading on Medium »

Medium · DevOps
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Here’s Why You Should Disable SSH Password Login on Every VPS
You may not realize it, but bots are likely already trying to brute-force your server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
Here’s Why You Should Disable SSH Password Login on Every VPS
You may not realize it, but bots are likely already trying to brute-force your server. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
3w ago
The Silent Audience: The $448 Billion Business of Watching You
Imagine sitting in your room late at night, doors locked, curtains drawn. Continue reading on Medium »
TechRepublic
🔐 Cybersecurity
⚡ AI Lesson
3w ago
New Phishing Attack Turns n8n Into On-Demand Malware Machine
Hackers are abusing n8n workflows to deliver malware and evade detection, according to Cisco Talos, using trusted automation to bypass security defenses. The po

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Credential dumping is rarely about the tool you use and more about knowing where the OS is actually…
I was working on compromising the DC and landed on a host where I was sure I would find some clear text credentials. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Ransomware & AI-Enhanced Social Engineering: Incident Response Challenges in 2026
In 2026, the nature of cybersecurity threat will revolve around the combination of ransomware and the application of artificial… Continue reading on MeetCyber »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Perfect Crime Lies Beyond the Doorknob
~The Silent Algorithm and the Favorite Character’s Bribe~ Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Introducing SESINF SRL — Your B2B IT Integration Partner in Italy
We are SESINF SRL, a B2B IT integrator based in Rome, delivering end-to-end infrastructure, cybersecurity, and managed services to… Continue reading on Medium »
![CyberWarFare Labs — Certified Cyber Security Engineer [CCSE] — My Experience and Review](https://cdn-images-1.medium.com/max/2600/1*gQYvUXn7Ps2sbp8Q2H0CfQ.jpeg)
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
CyberWarFare Labs — Certified Cyber Security Engineer [CCSE] — My Experience and Review
Hello everyone, it’s me, Chicken0248, back again with another course and exam I just passed — the Certified Cyber Security Engineer (CCSE)… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Telegram OSINT Guide: Find User Details, Emails & Phone Numbers Legally
What is Open Source Intelligence (OSINT)? Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Authentication Testing
4.4.5 Testing for Vulnerable Remember Password Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
The Hidden Privacy Risk of Online File Converters
You’ve probably done it a hundred times. Upload a PDF, convert it, download the result. Takes 10 seconds. You move on with your day. Continue reading on Medium
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Authentication Security Audit: Testing the Resilience of Web Applications Based on the OWASP WSTG…
4.4.5 Testing for Vulnerable Remember Password Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4w ago
Tokenomics Exploits: When Design Becomes an Attack Vector
Why the most dangerous crypto vulnerabilities aren’t in the code they’re in the incentives Continue reading on Coinmonks »
 DeepCamp AI
DeepCamp AI