Hash Functions(Turning Data Into Fingerprints)
Hashing transforms any given input—whether small or large—into a fixed-length string known as a hash. A strong hash function ensures that it’s extremely difficult for two different inputs to produce the same output, minimizing collisions and boosting reliability. Because of this security and efficiency, hashing is widely used in password storage, data indexing in hash maps, and the integrity checks that power blockchain technology.......#hashing, #security, #datastructures
Watch on YouTube ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
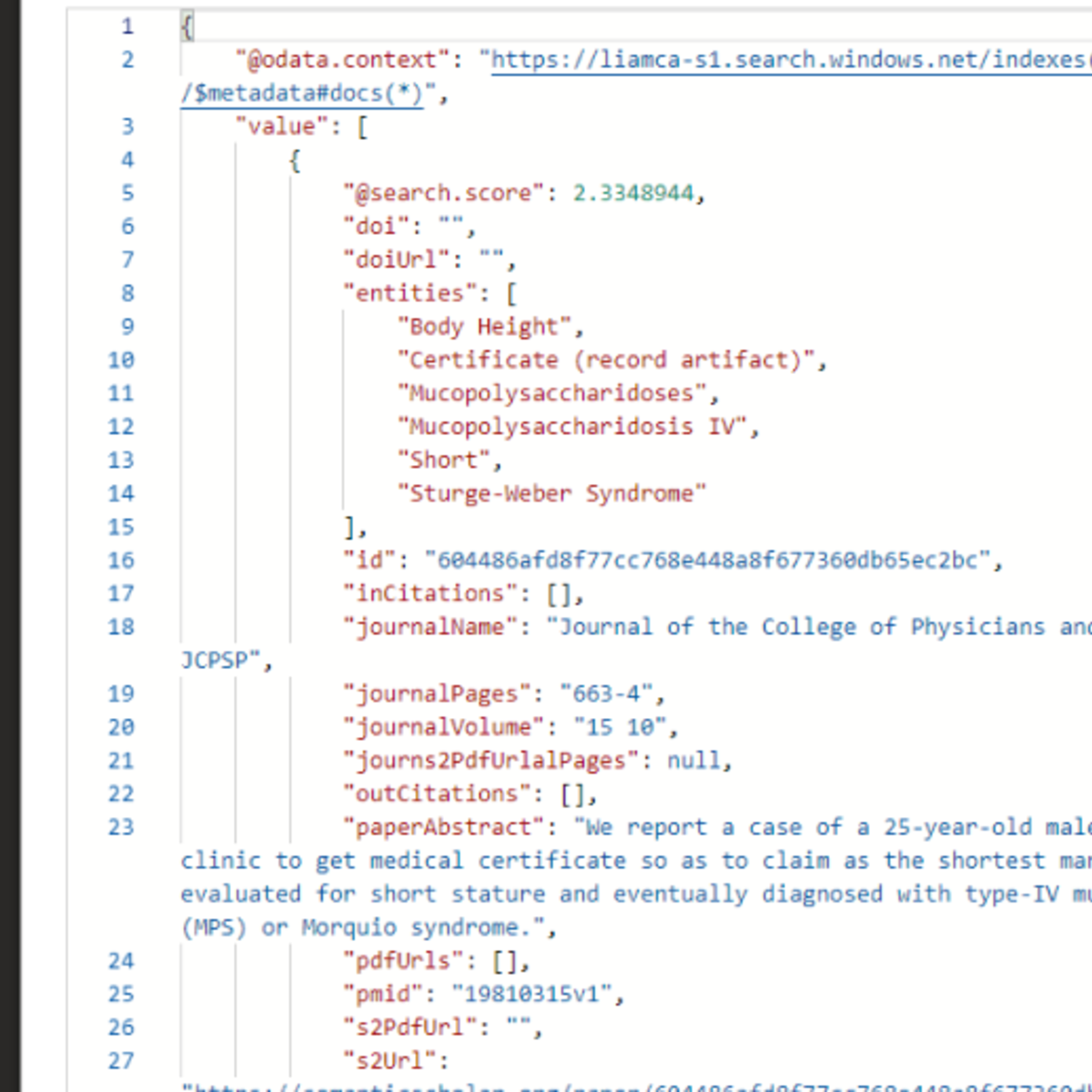
More on: RAG Basics
View skill →Related AI Lessons
⚡
⚡
⚡
⚡
The Future of RAG: Dead, Evolving… or Becoming the Brain of AI?
Medium · Machine Learning
Smart Routing, Transfer Family Ingestion, and Voice Chat — Permission-Aware RAG v4.2
Dev.to · Yoshiki Fujiwara(藤原 善基)@AWS Community Builder
Most Companies Doing GenAI Are Really Just Doing RAG: RAGOps Explained for analysts
Medium · RAG
RAG - Sliding Window, Token Based Chunking and PDF Chunking Packages
Dev.to AI
🎓
Tutor Explanation







 DeepCamp AI
DeepCamp AI