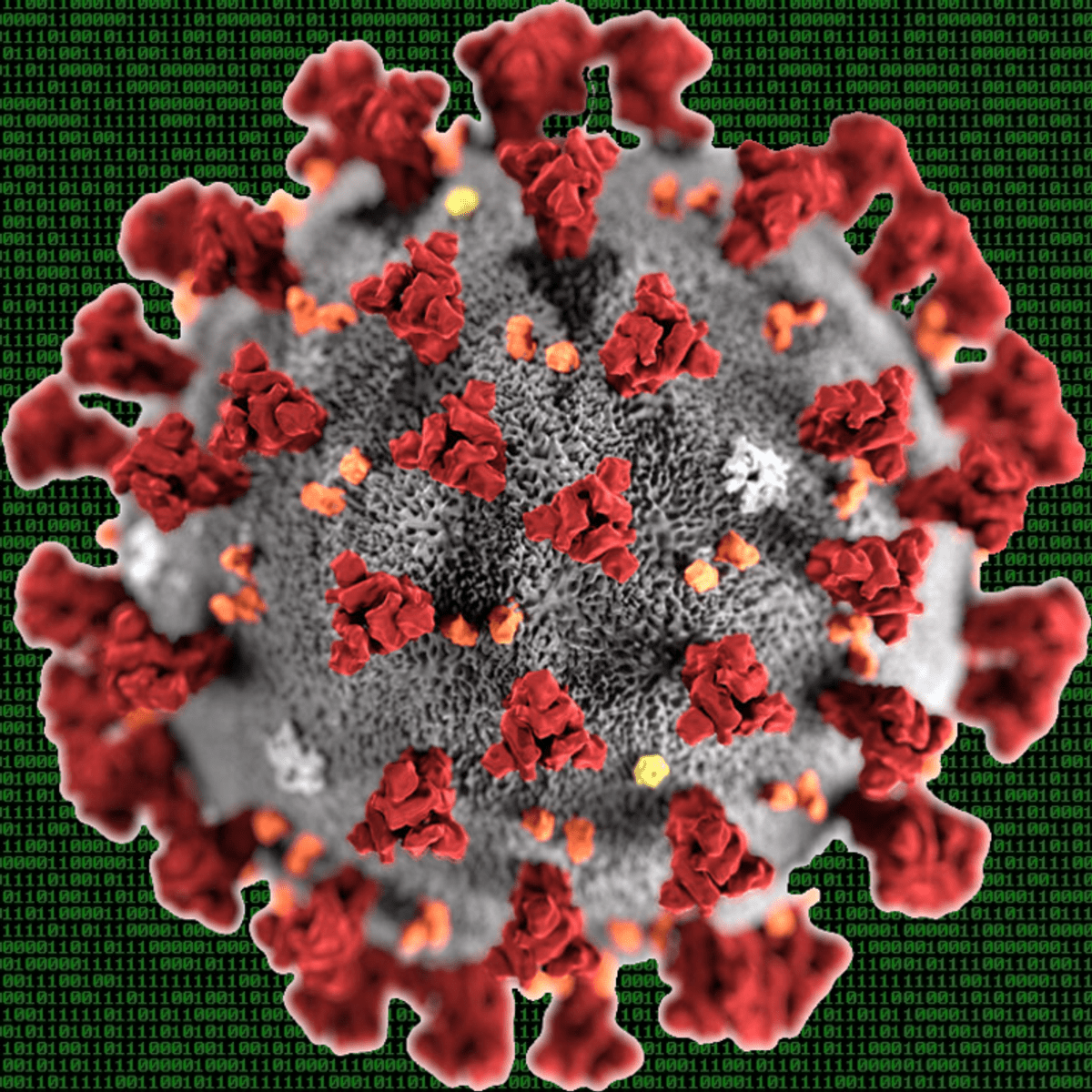
Hacking COVID-19: Metabolic Pathway Analysis Yields SARS-CoV-2 Drug Targets
Pathway Bioinformatics is a subfield of Bioinformatics that is concerned with computationally deriving functional insights from genomic data through analysis of molecular networks. This course will present principles and techniques from Pathway Bioinformatics, and will apply these methodologies to the search for drug targets for SARS-CoV-2. The course will begin by discussing motivations for Pathway Bioinformatics, and by presenting an overview of metabolism and of metabolic pathways. Next it will discuss machine representation of pathway data, and methods for pathway visualization. The course will describe how the metabolic pathways of an organism can be inferred from genome data, and how pathways can be used to interpret high-throughput data such as transcriptomics data. It will show how to predict the essential genes of an organism via reachability analysis, and then present a metabolic analysis of human metabolism when interacting with SARS-CoV-2 to predict SARS-CoV-2 drug targets.
Watch on Coursera ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
Related AI Lessons
⚡
⚡
⚡
⚡
Stop trusting your agent skills with vibes. Eliminate the context security risk.
Dev.to · Tessl
Investigating a Command Injection Attack — SOC168: Whoami Command Detected in Request Body |…
Medium · Cybersecurity
pwning Facts
Medium · Cybersecurity
Detecting Dangerous Shell Commands in Rust — Building a Safety Layer
Dev.to · hiyoyo
🎓
Tutor Explanation

 DeepCamp AI
DeepCamp AI