Analyze Cybersecurity Risks in Financial Systems
By the end of this course, learners will be able to define core cybersecurity concepts, analyze cyber risks within financial systems, evaluate regulatory and ethical requirements, and apply proactive strategies to manage emerging cyber threats using modern technologies.
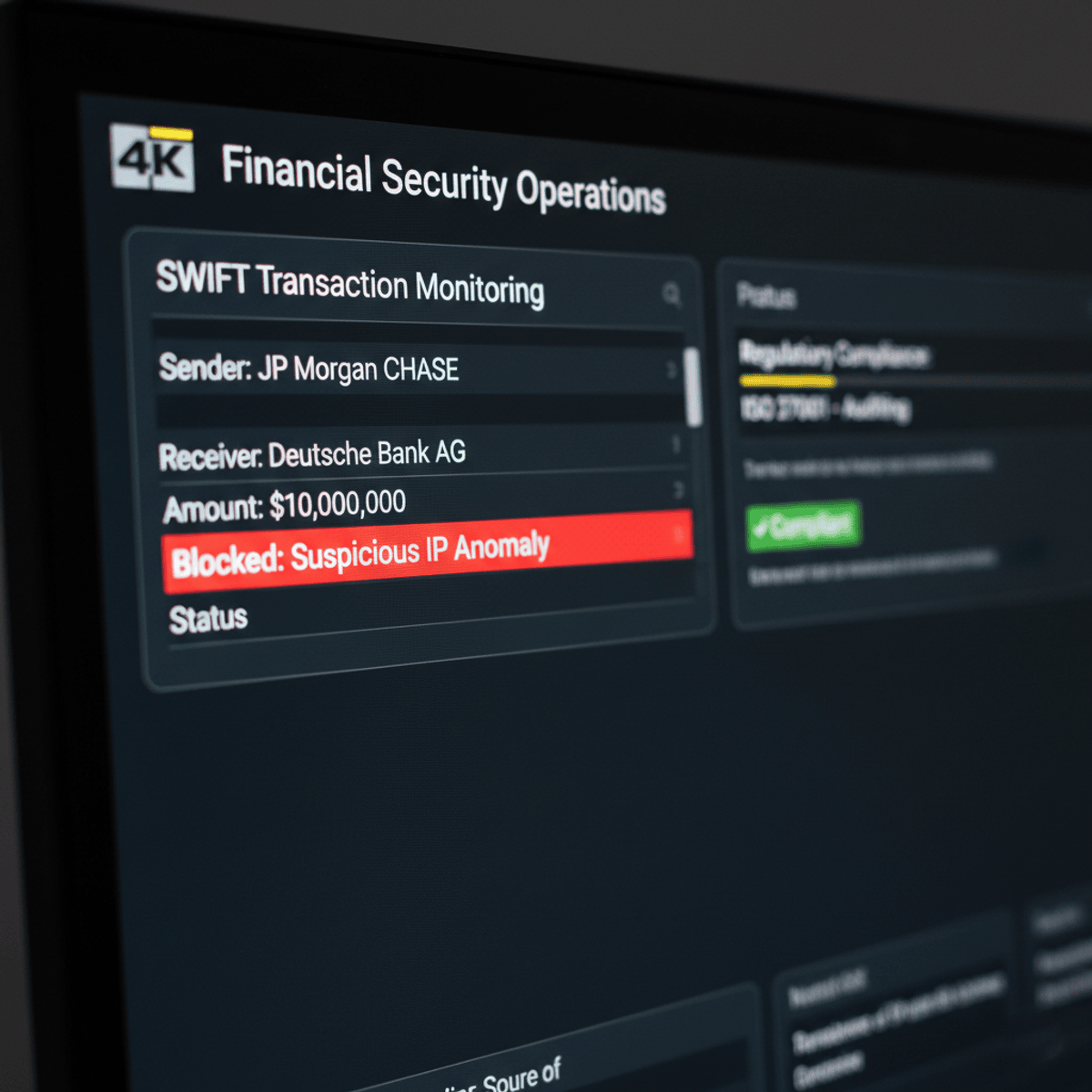
This course equips learners with a comprehensive understanding of cybersecurity tailored specifically to the financial sector. Participants will explore how cyber threats impact financial institutions, digital transactions, and customer trust, while gaining insights into the people, processes, and technologies that form effective security frameworks. Through structured modules, learners will examine governance models, compliance obligations, ethical responsibilities, and the influence of emerging technologies such as cloud computing, artificial intelligence, and blockchain.
What makes this course unique is its finance-first approach to cybersecurity, blending technical awareness with risk management, regulatory compliance, and strategic decision-making. Rather than focusing solely on tools, the course emphasizes real-world application, continuous improvement, and threat navigation strategies relevant to modern financial environments. Upon completion, learners will be better prepared to support secure financial operations, strengthen organizational resilience, and contribute meaningfully to cybersecurity initiatives in regulated industries.
Watch on Coursera ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
Related AI Lessons
⚡
⚡
⚡
⚡
How to secure your macOS games
Dev.to · GuardingPearSoftware
The Hidden Risk in Emergency Evacuation Plans Nobody Talks About
Medium · Cybersecurity
3 Key Takeaways on Why Cybersecurity Product Management Matters More Than Ever
Medium · Cybersecurity
The Coding Challenge That Came for Your development Directory: Anatomy of a Job Interview Infostealer
Dev.to · Alex Chen
🎓
Tutor Explanation

 DeepCamp AI
DeepCamp AI