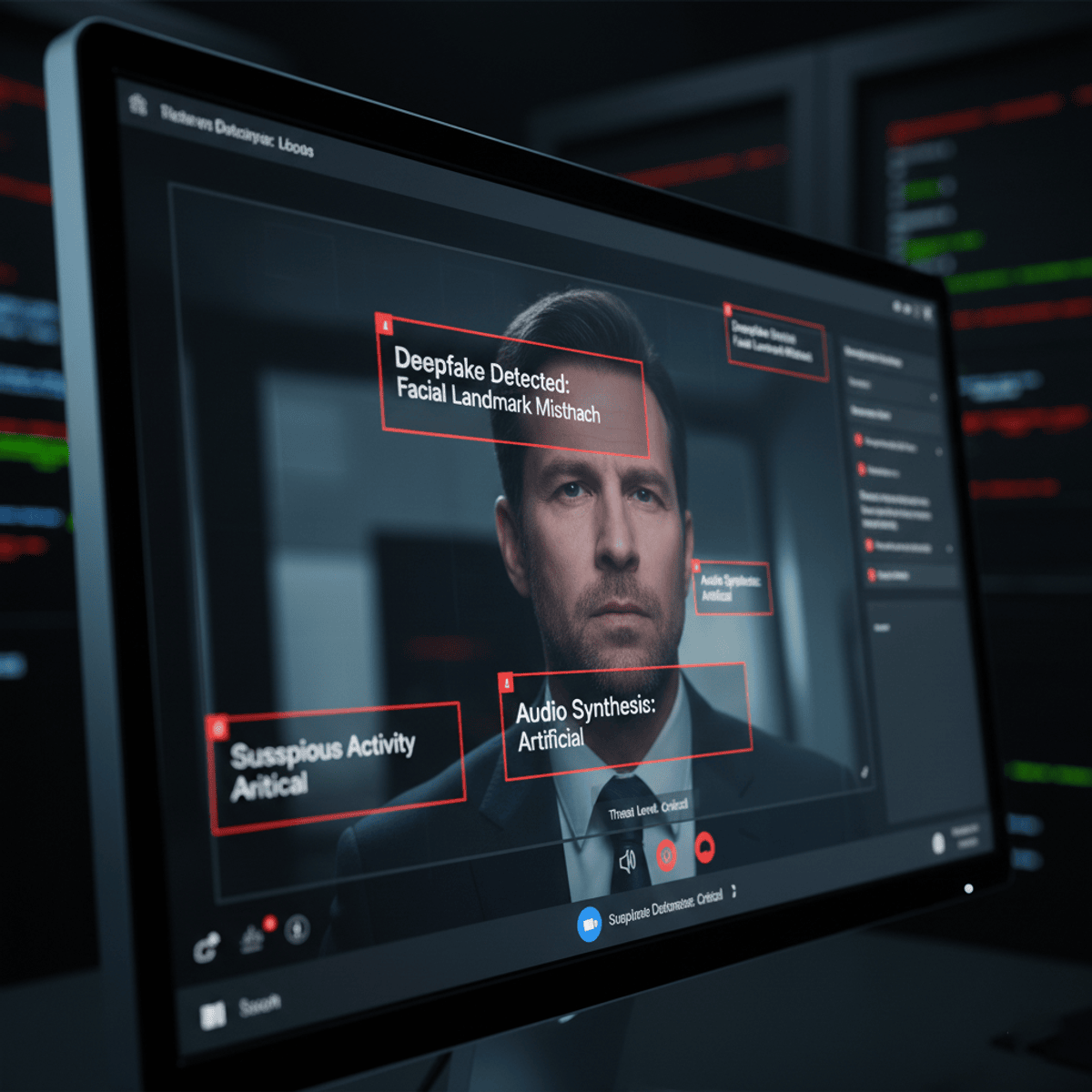
Analyze and Defend Against GenAI Social Engineering Attacks
Skills:
AI Security90%
Learners will be able to analyze Generative AI–driven social engineering techniques, evaluate emerging human-centric cyber threats, and apply effective defensive strategies to recognize and respond to AI-enabled manipulation. This course equips learners with the knowledge and critical thinking skills required to understand how Generative AI is transforming phishing, vishing, deepfakes, SMS-based scams, and large-scale disinformation attacks.
Through structured modules and real-world scenarios, learners gain insight into how attackers exploit trust, authority, urgency, and familiarity using AI-generated content that closely mimics legitimate communication. The course emphasizes not only how these attacks work, but why they are effective, enabling learners to anticipate and identify subtle manipulation techniques that traditional security training often overlooks.
What makes this course unique is its strong focus on the human layer of cybersecurity in the age of Generative AI. Rather than centering solely on tools or technology, the course develops learner awareness, judgment, and decision-making skills that complement technical defenses. By completing this course, learners strengthen their ability to detect deception, reduce organizational risk, and contribute to resilient, AI-aware security cultures across personal and professional environments.
Watch on Coursera ↗
(saves to browser)
Sign in to unlock AI tutor explanation · ⚡30
More on: AI Security
View skill →Related AI Lessons
⚡
⚡
⚡
⚡
Twitter OSINT & Threat Intelligence: Toolkit for Ethical Hackers & Security Analysts
Medium · Startup
Twitter OSINT & Threat Intelligence: Toolkit for Ethical Hackers & Security Analysts
Medium · Cybersecurity
Your Encrypted Laptop Isn’t as Safe as You Think
Medium · Cybersecurity
TCP, Firewalls, Port Forwarding & VPNs — How Data Is Sent and Secured
Medium · Cybersecurity
🎓
Tutor Explanation











 DeepCamp AI
DeepCamp AI