📰 Medium · Cybersecurity
Articles from Medium · Cybersecurity · 92 articles · Updated every 3 hours · View all reads
All
⚡ AI Lessons (10277)
ArXiv cs.AIDev.to · FORUM WEBDev.to AIForbes InnovationOpenAI NewsHugging Face Blog

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
49m ago
Why CISSP Is the Most Valuable Cybersecurity Certification for Senior Professionals in 2026
The cybersecurity landscape has never been more competitive — or more rewarding — for those who hold the right credentials. Among the… Continue reading on Mediu

Medium · Cybersecurity
🤖 AI Agents & Automation
⚡ AI Lesson
2h ago
AI Agents and the End of Deterministic Cybersecurity
From API workflow abuse to autonomous decision chains — the new security paradigm emerging around AI agents. Continue reading on Medium »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2h ago
The Cybersecurity Gap No One Is Talking About: Claude Mythos vs Opus 4.6
Most people think AI in cybersecurity is just getting better. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2h ago
Tek Bir Link ile Uygulamayı Ele Geçirmek: Deep Link ve WebView İstismarı
Mobil Dünyanın Arka Kapıları: WebView ve DeepLink Zafiyetleri Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
2h ago
Why shared responsibility models confuse SMEs.
Shared responsibility looks clean in a diagram. Continue reading on aneo Security Insights »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
Is your security strategy reactive — or intelligently proactive?
易 Zefai Insights || Cyber Security Edition Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
4h ago
LLM Injection + Unlimited Approval + RCE: The Coinbase AgentKit Attack Chain
A prompt injection that crosses three trust boundaries — and why Coinbase called it Medium Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
4h ago
Curing Detection Engineer Anxiety: Uncovering the Blind Spots in Your Rules
In our previous post, 《Detection Rule Fragility: Design Pitfalls Every Detection Engineer Must Know》,we explored why detection rules based… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
6h ago
Mastering the ISO 22301 Lead Implementer Role: Beyond the Certification
Imagine your organization faces a sudden, catastrophic system failure or a regional disaster. The difference between a business that… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
You May Have Perfect Backups and Still Lose Everything
Backup Best Practices for Data You Cannot Afford to Lose Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
Malloc Privacy Weekly
We bring you the most recent mobile cybersecurity updates in the newest edition of Malloc Weekly Privacy. This week, we cover the surge in… Continue reading on

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
7h ago
Bug Bounty Hunting — Ethical Hacking for Profit
What if hacking could be legal, respected, and even highly profitable? Continue reading on Medium »
Medium · Cybersecurity
🧠 Large Language Models
⚡ AI Lesson
7h ago
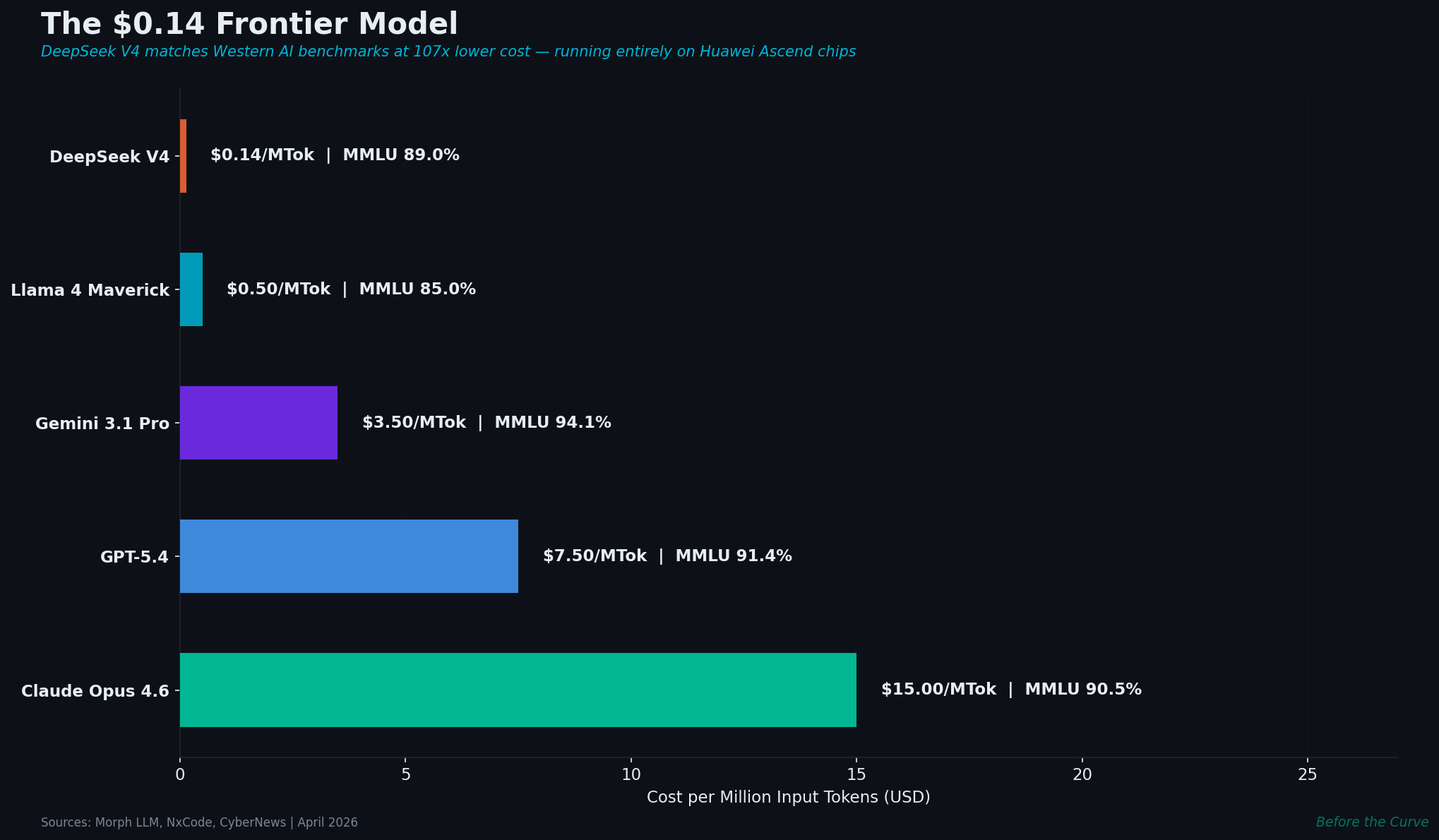
DeepSeek V4: 1 Trillion Parameters, $0.14/M Tokens, No NVIDIA
China’s latest frontier model costs 107× less than Western alternatives and runs entirely on Huawei chips. With 175,000 open-source AI… Continue reading on Medi

Medium · Cybersecurity
📰 AI News & Updates
⚡ AI Lesson
8h ago
Do AI Impact ASIA Company? A 2026 Macroeconomic Technical Audit
The year 2026 marks a decisive pivot point for the Asian corporate landscape. As the “Digital Silk Road” matures, the integration of… Continue reading on Medium

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
The 2026 Guide to Web Integrity: Understanding the Role of SSL in Modern App Ecosystems
In the current digital landscape of 2026, the internet is no longer a luxury; it is the backbone of global commerce and entertainment… Continue reading on Mediu

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
9h ago
Attackers don’t hack systems — they hack decisions
The real vulnerability isn’t your software. It’s the three seconds before you click. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
11h ago
What Scale-Up CISOs Actually Need: The Politics Nobody Prepares You For
The Scale-Up CISO series by John Rouffas Continue reading on Medium »

Medium · Cybersecurity
📣 Digital Marketing & Growth
⚡ AI Lesson
11h ago
My Medium Partner Program Suddenly Turned “Inactive” And I Still Don’t Know Why
My Medium Partner Program Turned Inactive — Even After Following All Rules Continue reading on OSINT Team »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
11h ago
I Found a Broken Login System in a Fintech App — Here’s How I Did It
A real bug hunt story with JWT tokens, Burp Suite, and a fintech website that trusted too much Continue reading on OSINT Team »
Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
12h ago
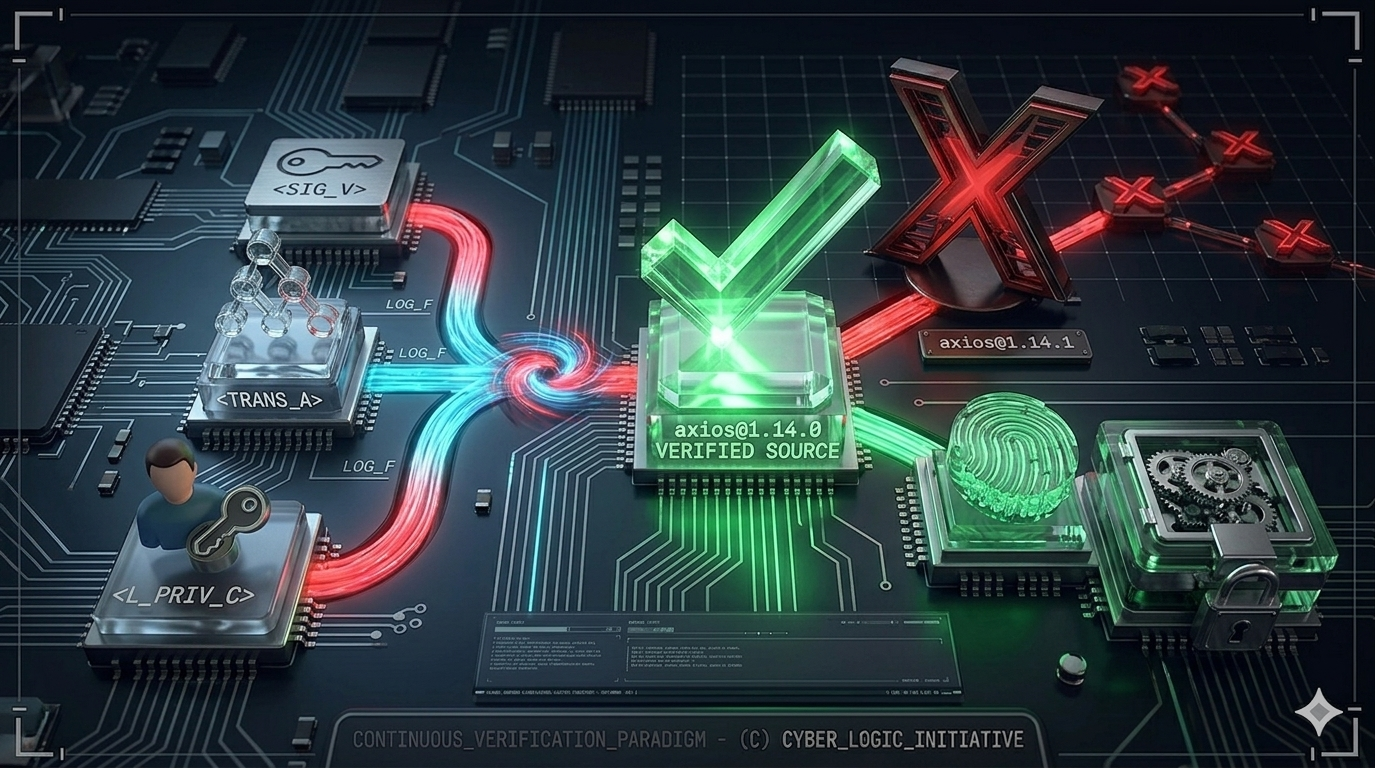
One npm install Away
What the Axios Supply Chain Attack Teaches Us About Zero Trust in Software Development Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
12h ago
Análisis de un dropper, que se disfraza como herramienta de hacking
¿Y bueno gente como les va?, yo por mi lado estoy bastante bien y emocionado por contarles que encontré algo interesante para explicar… Continue reading on Medi

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
12h ago
LetsDefend: Obfuscated JavaScript Challenge Walkthrough
Malicious JavaScript Analysis: Identifying Obfuscation, WMI Usage, and Network-Based Payload Staging Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
13h ago
The Smart Home Mistake You Are Probably Making
Why you should never share your Ring password, and how to properly share access with your family instead. Continue reading on Medium »

Medium · Cybersecurity
🔐 Cybersecurity
⚡ AI Lesson
13h ago
Instagram Hesaplarını Kapattırıp Para İsteyen Çeteler
Kod Açığı Değil, İnsan Süreçlerini Hedef Alan Yeni Nesil Bir Saldırı Modeli Continue reading on Medium »
 DeepCamp AI
DeepCamp AI